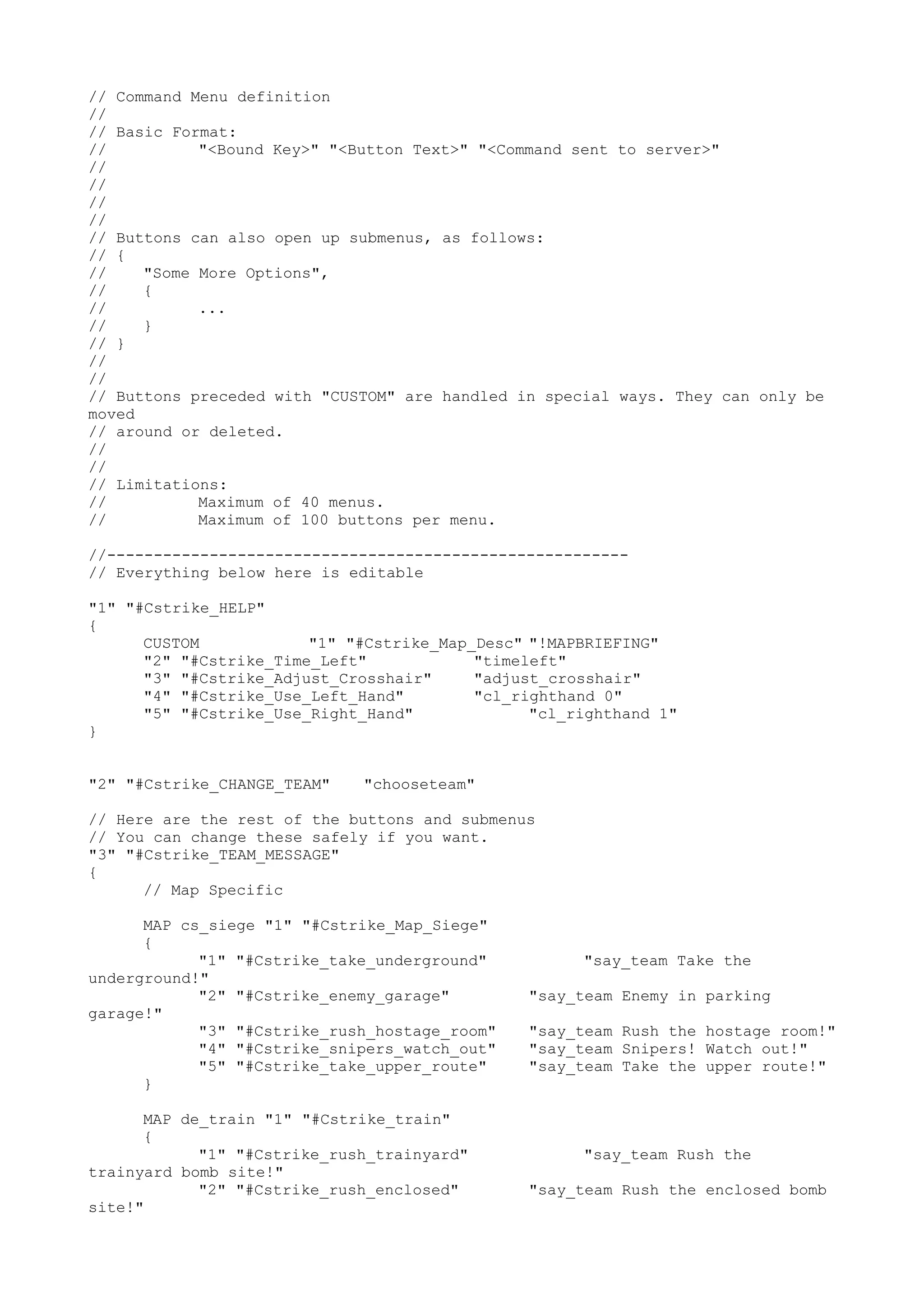
This document defines a command menu for Counter-Strike with buttons that send preset text messages to teammates when pressed. It lists the format for buttons, includes custom buttons, and sets limits of 40 menus and 100 buttons per menu. It then defines the buttons for a help menu, change team menu, and team message menu with preset messages mapped to different maps.