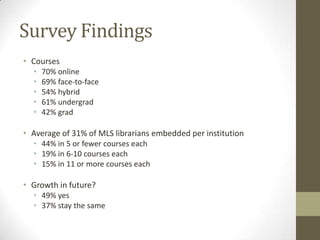
The document discusses the scalability of embedded librarianship within Learning Management Systems (LMS) and presents survey findings from various institutions about information literacy methods. It highlights barriers to implementation, collaboration with faculty, and the potential for enhanced student interactions and resource use. The data indicates a growing interest in embedded librarianship, with a substantial percentage of librarians currently working within LMS environments.