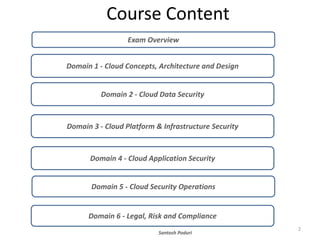
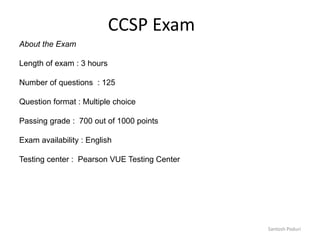
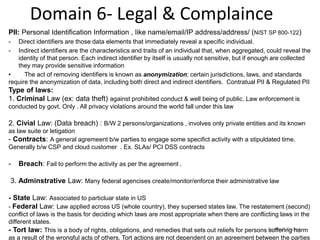
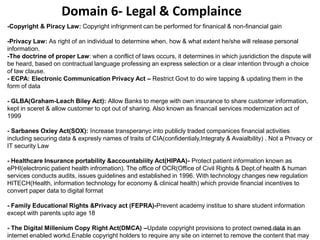
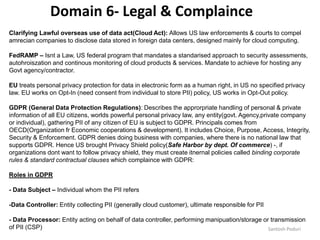
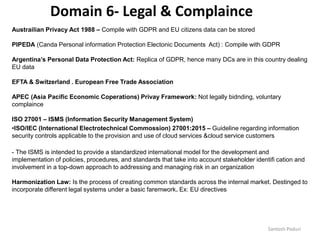
This document provides an overview of the CCSP exam, including the 6 domains covered, exam logistics, and key concepts in each domain. Domain 1 discusses cloud roles like cloud service providers, customers, and brokers. Domain 6 covers legal and compliance topics such as privacy laws, data protection regulations, and standards for eDiscovery, auditing, and nonrepudiation in cloud environments. Key frameworks referenced include GDPR, ISO 27001, FedRAMP, and privacy shield.