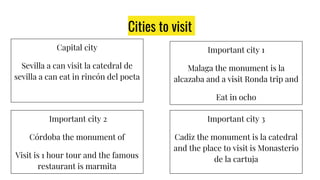
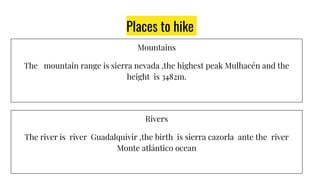
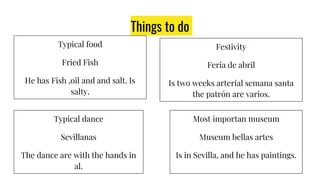
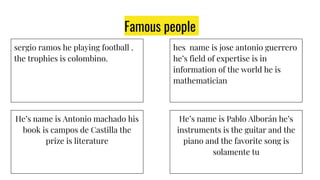
Andalucía is a region in southern Spain known for its cities, mountains, and culture. The capital city is Seville, home to the cathedral and popular for eating tapas. Other important cities include Málaga, Córdoba, and Cádiz, each with notable monuments. The Sierra Nevada mountain range offers hiking with the highest peak over 3,400 meters. Rivers like the Guadalquivir flow from the mountains to the Atlantic Ocean. Local specialties include fried fish, April fairs, Sevillana dancing, and the Museum of Fine Arts in Seville, which houses paintings. Famous people from Andalucía include footballer Sergio Ramos, poet Antonio Machado