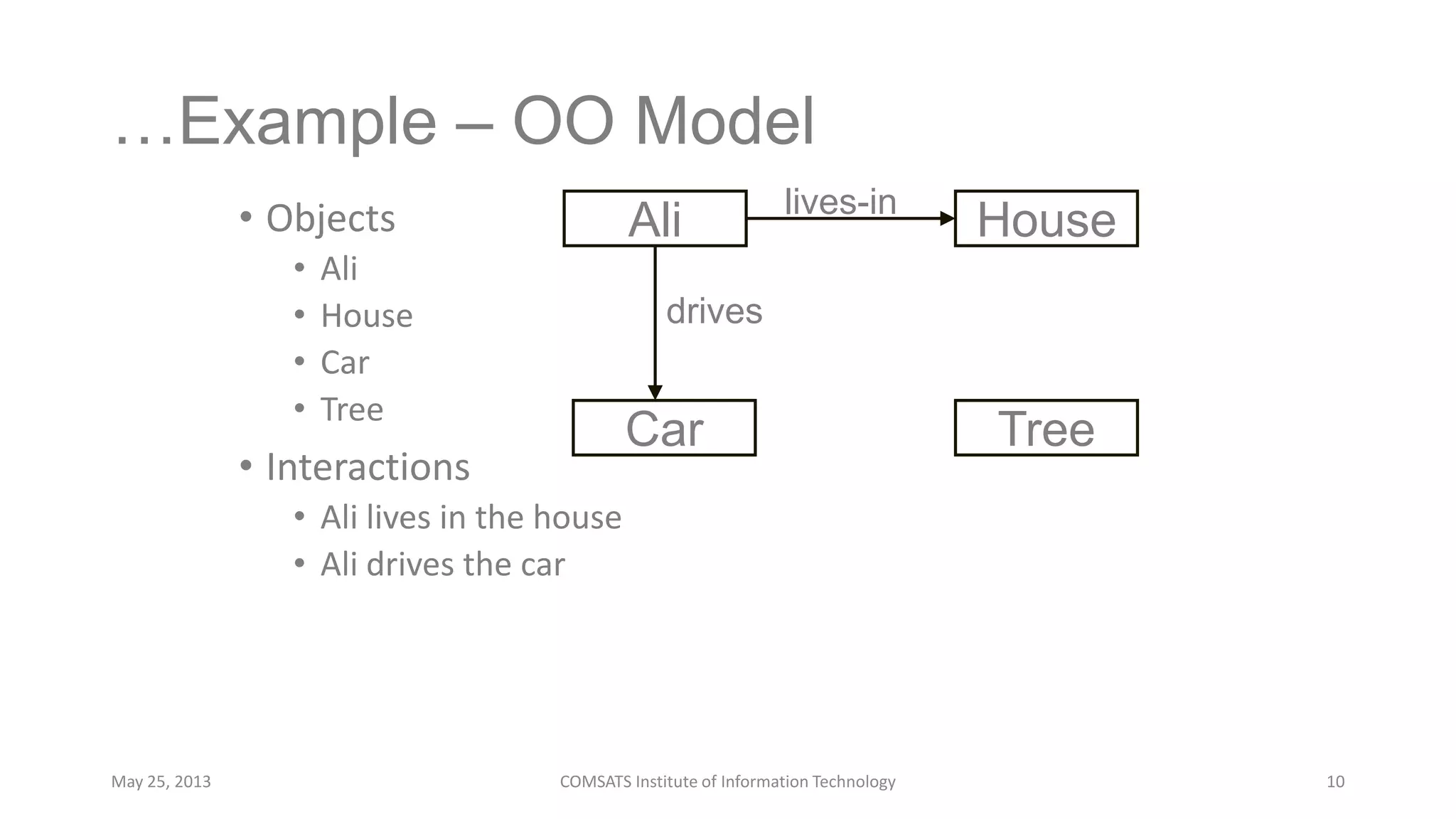
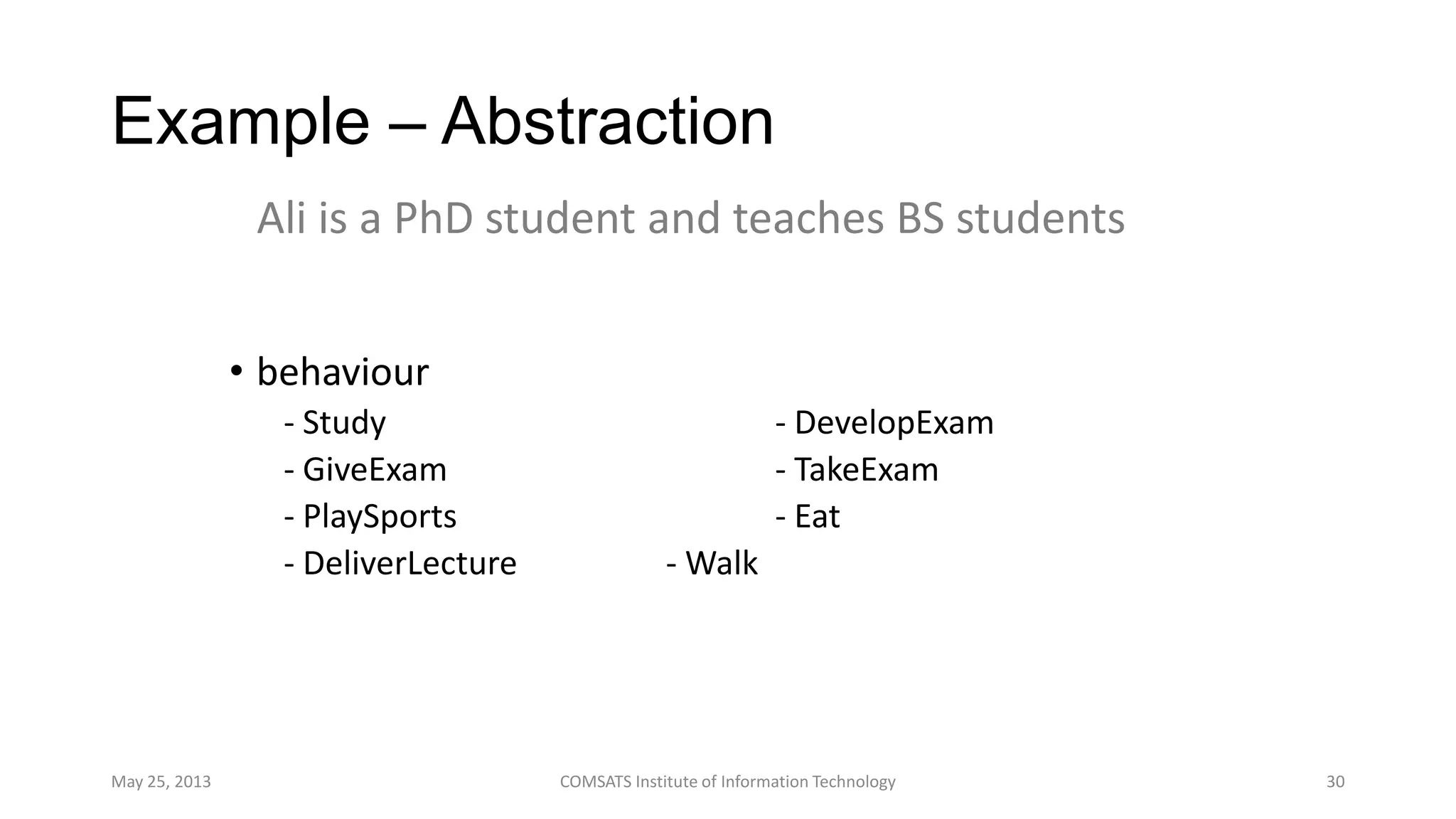
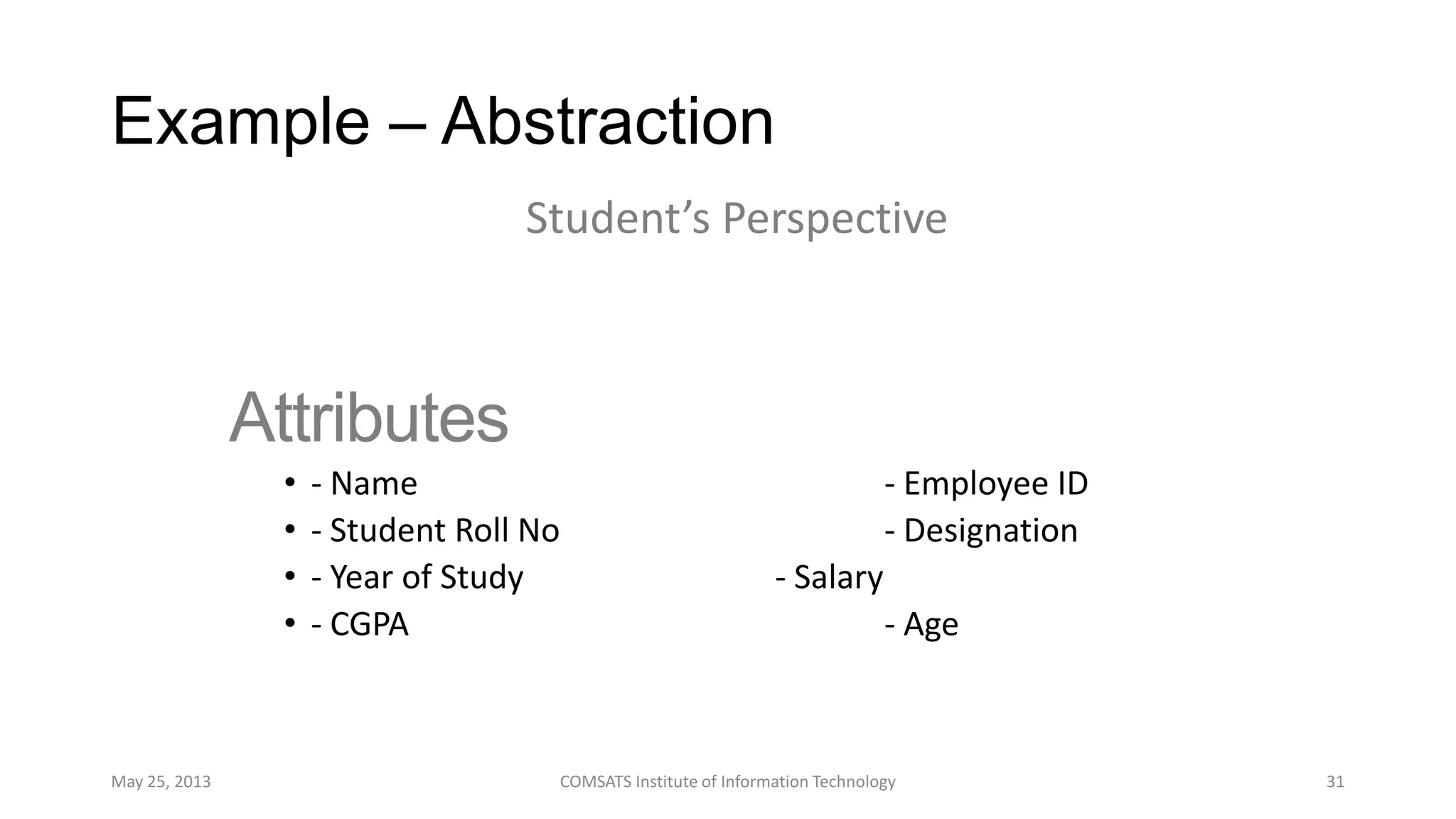
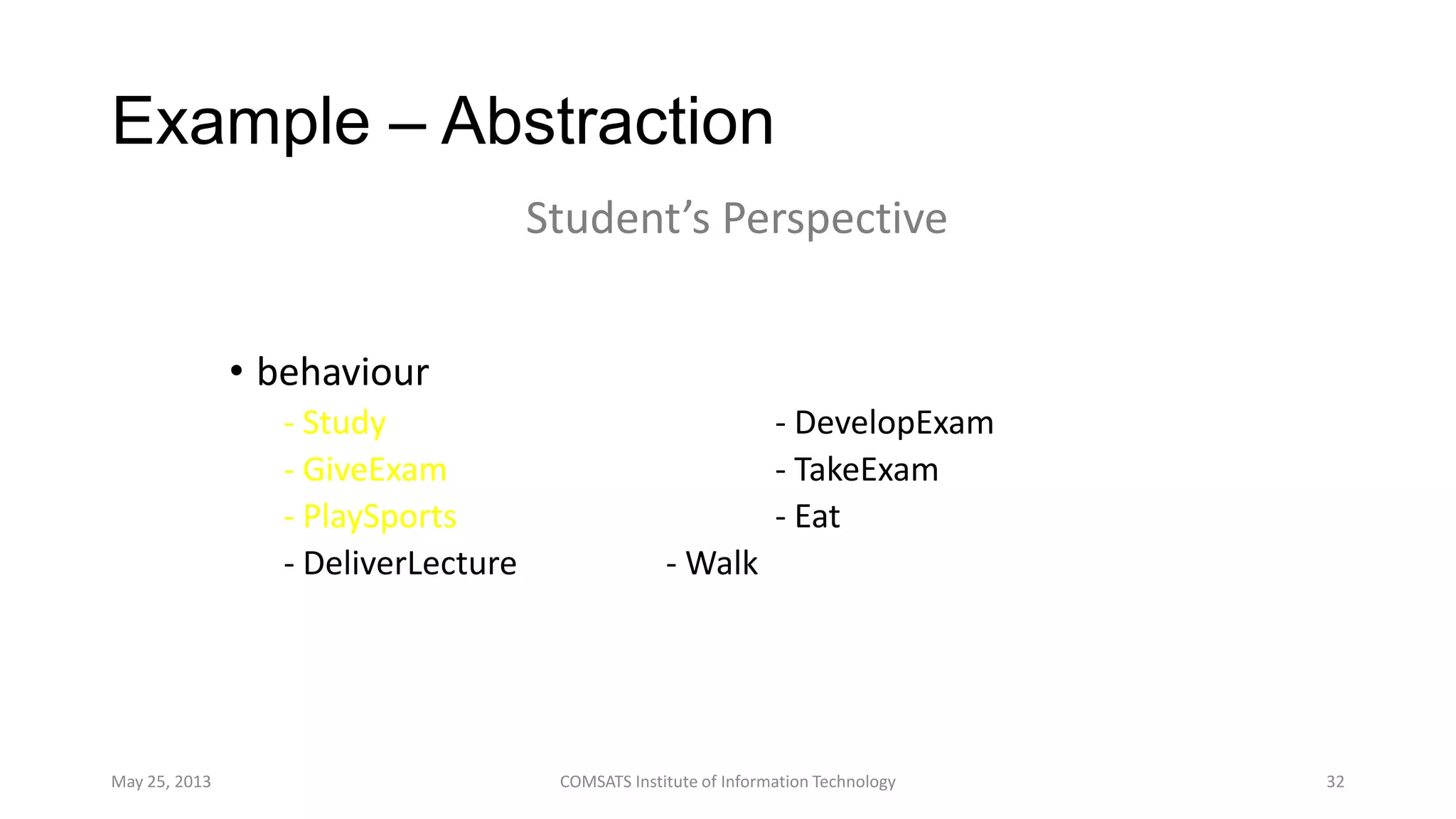
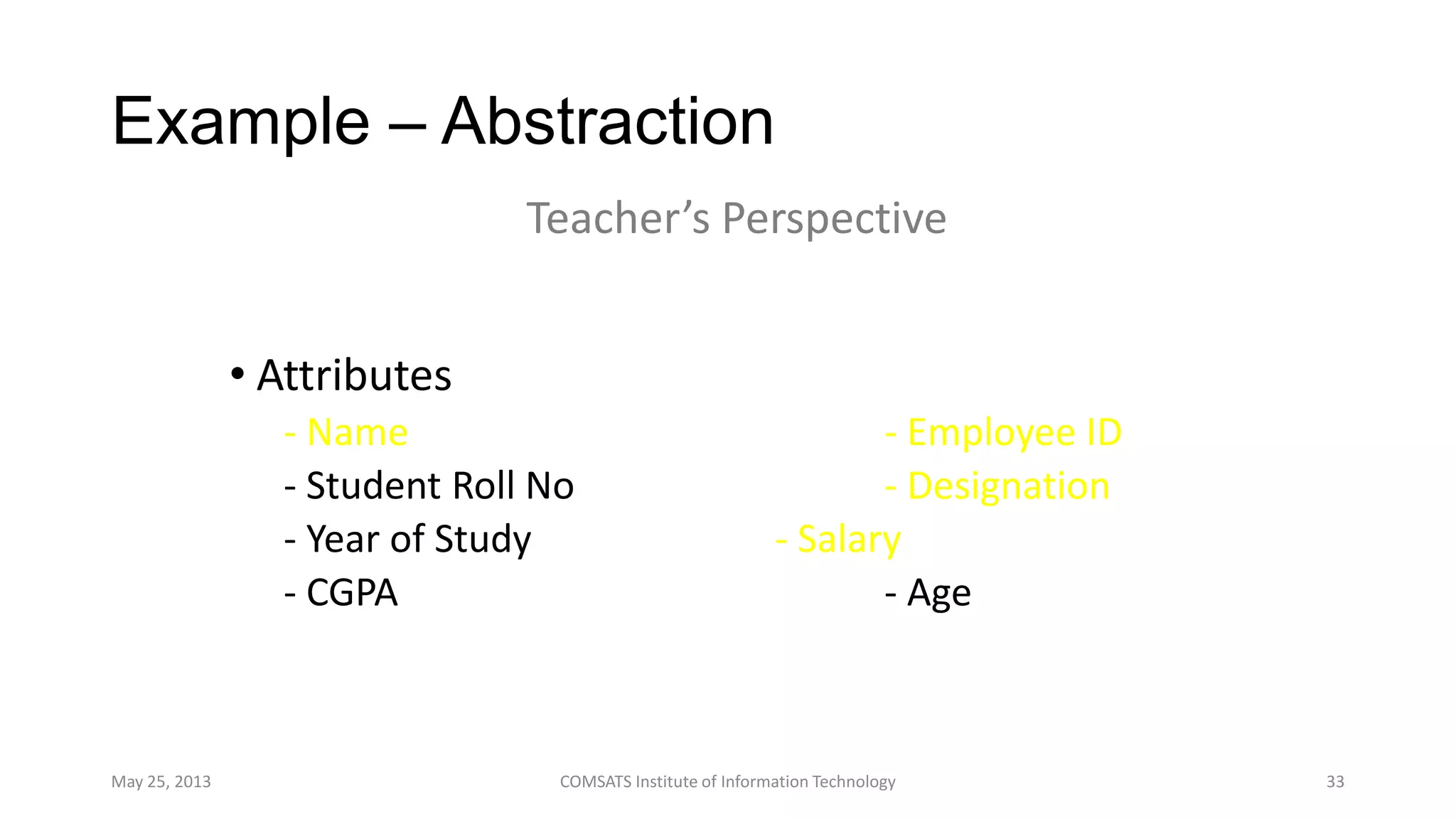
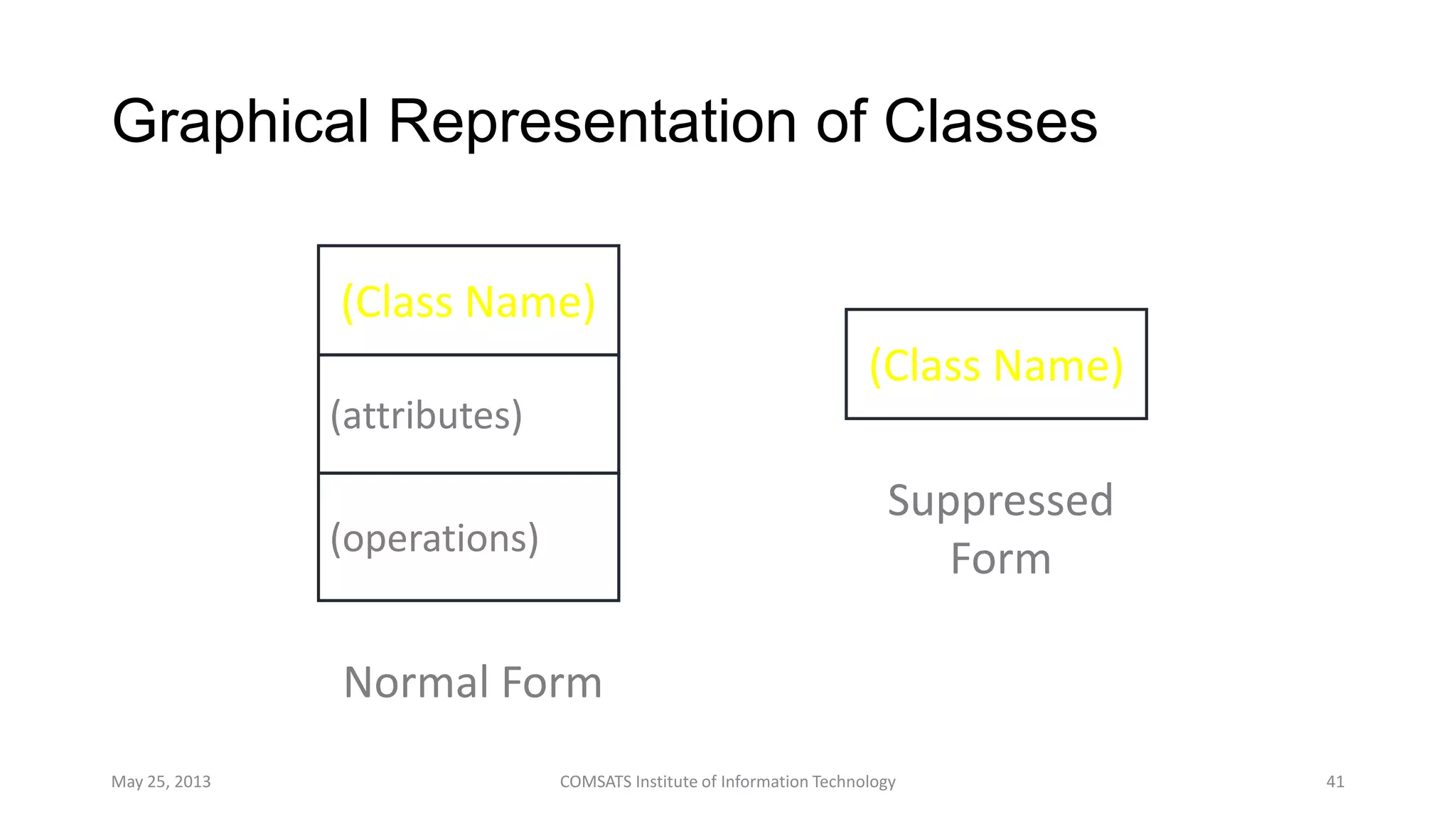
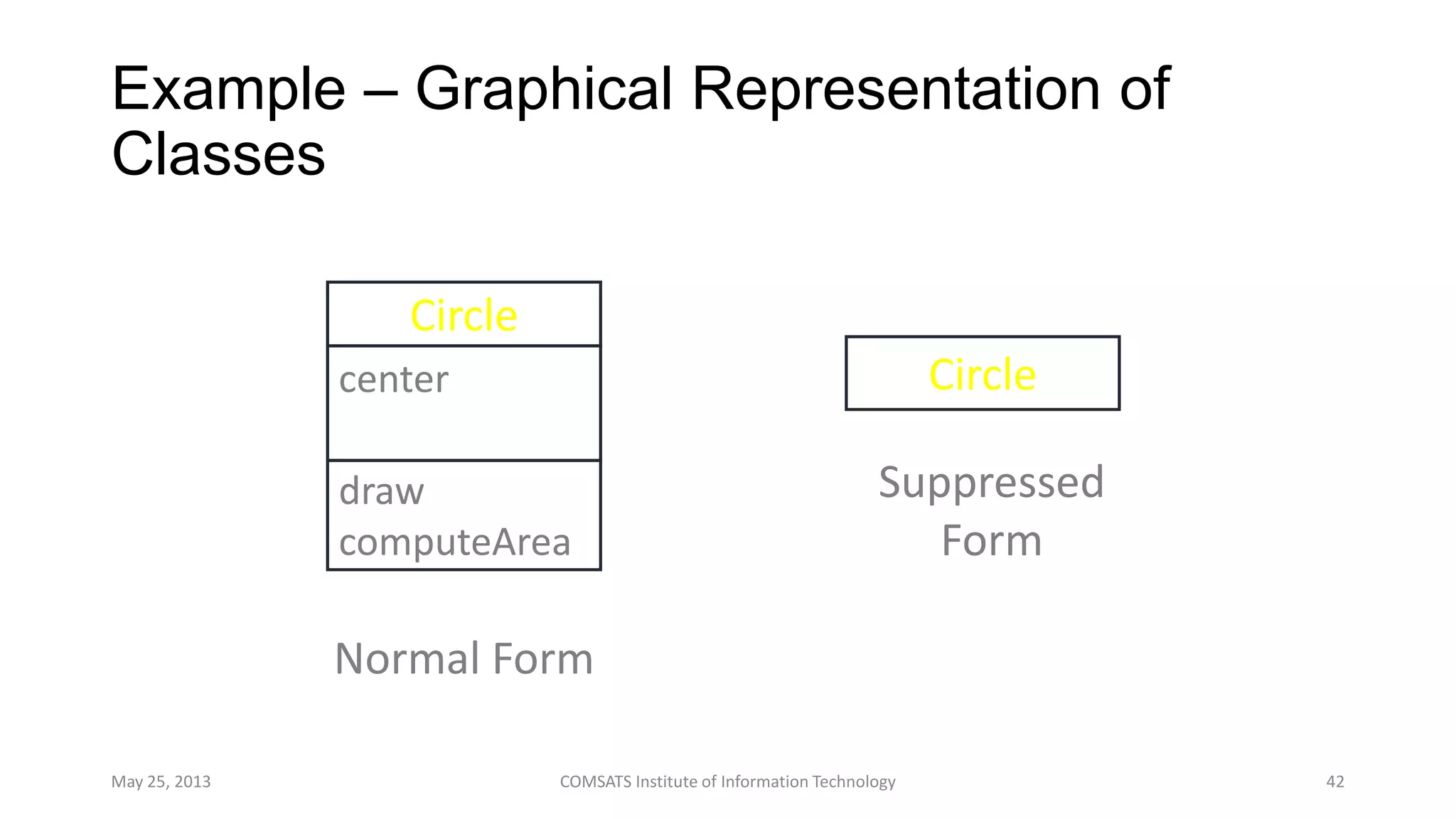
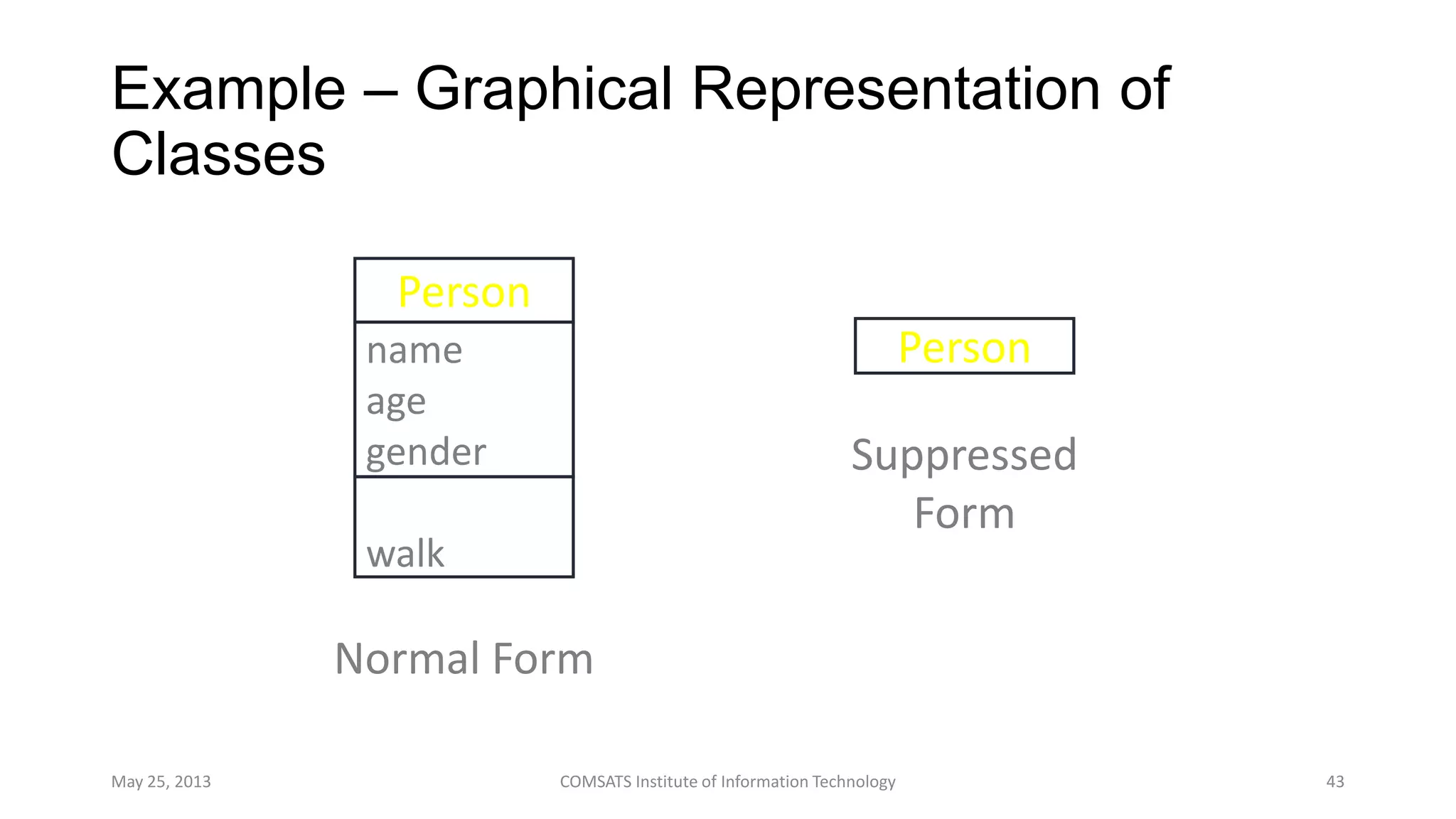
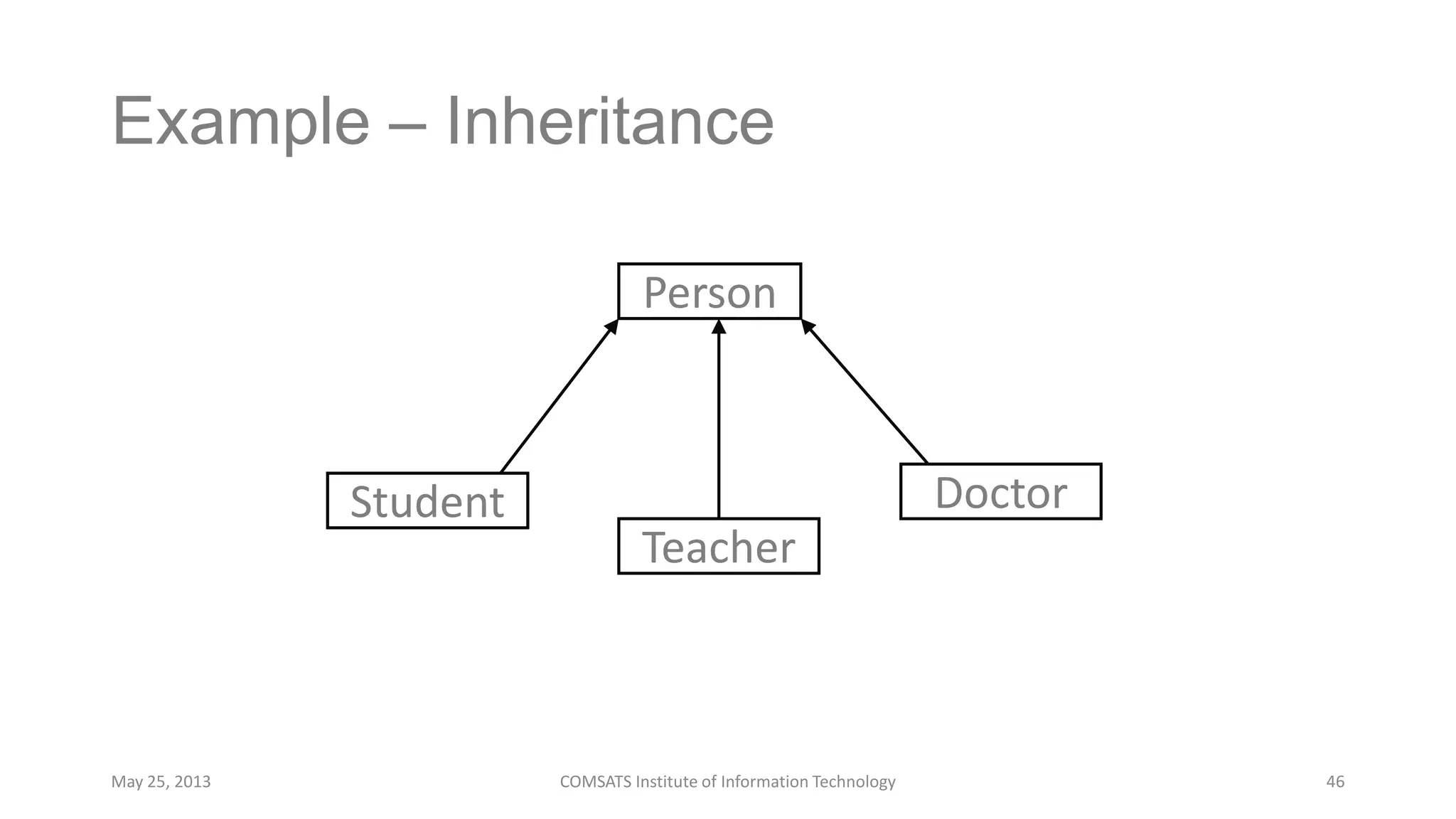
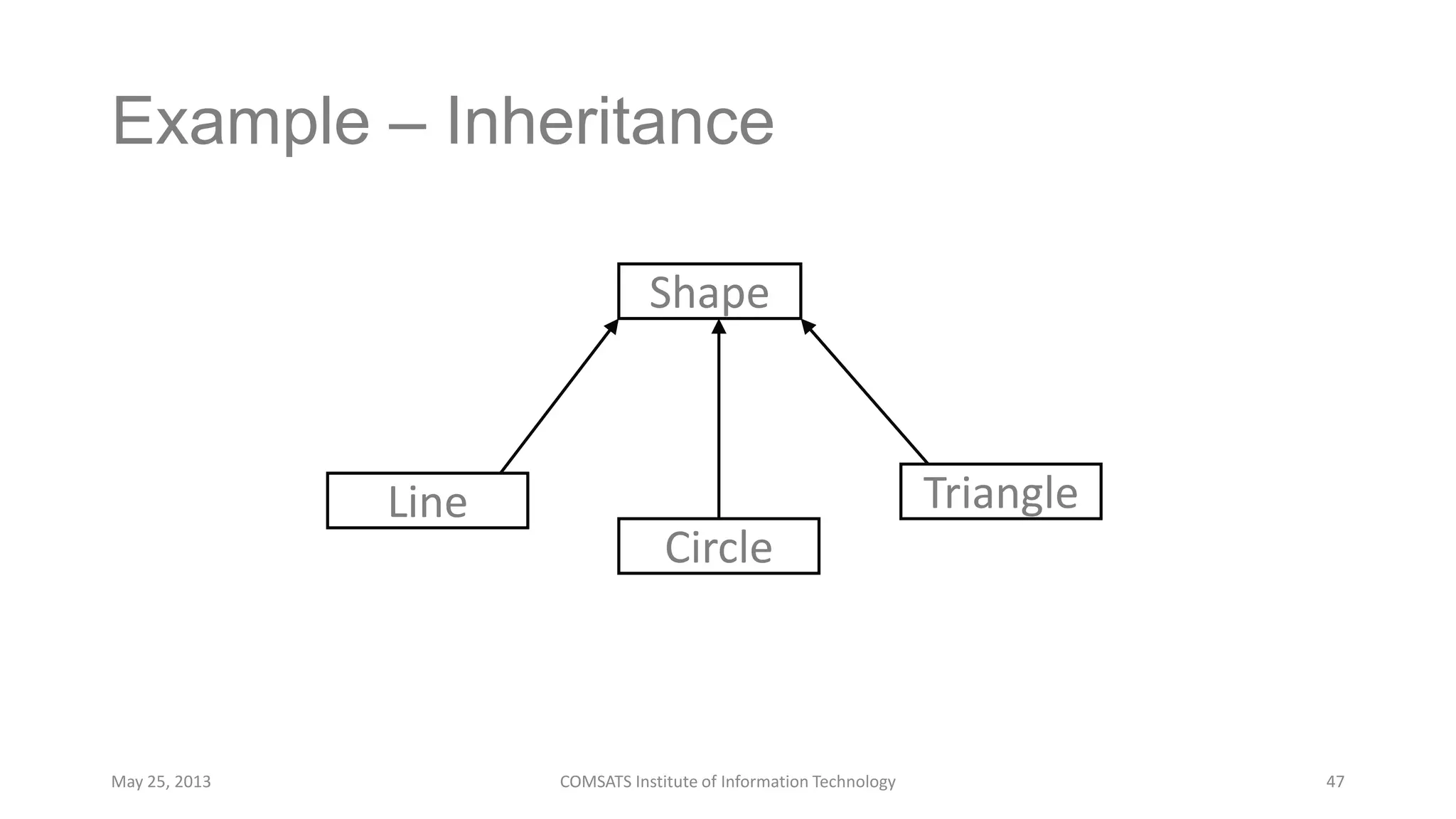
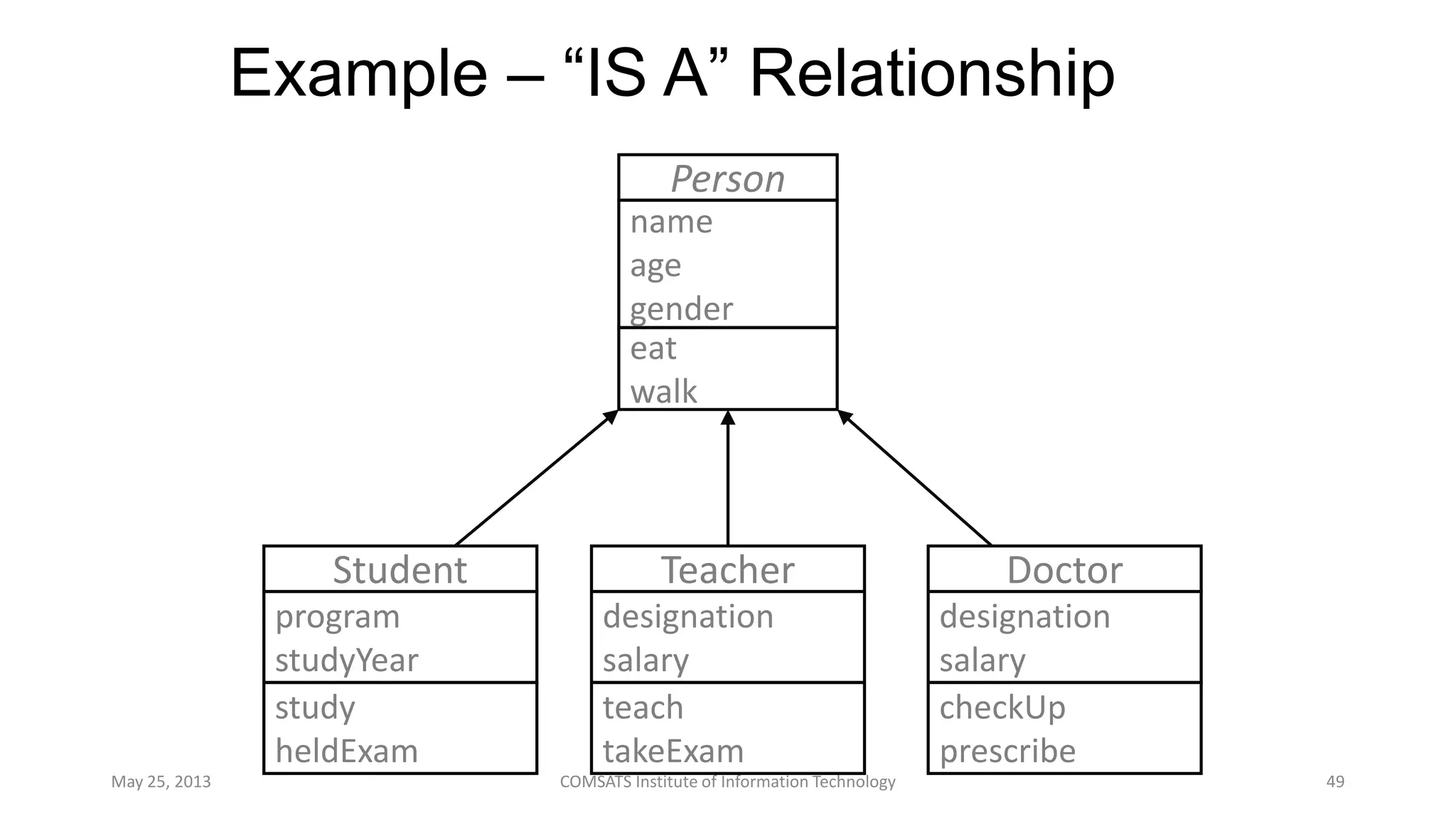
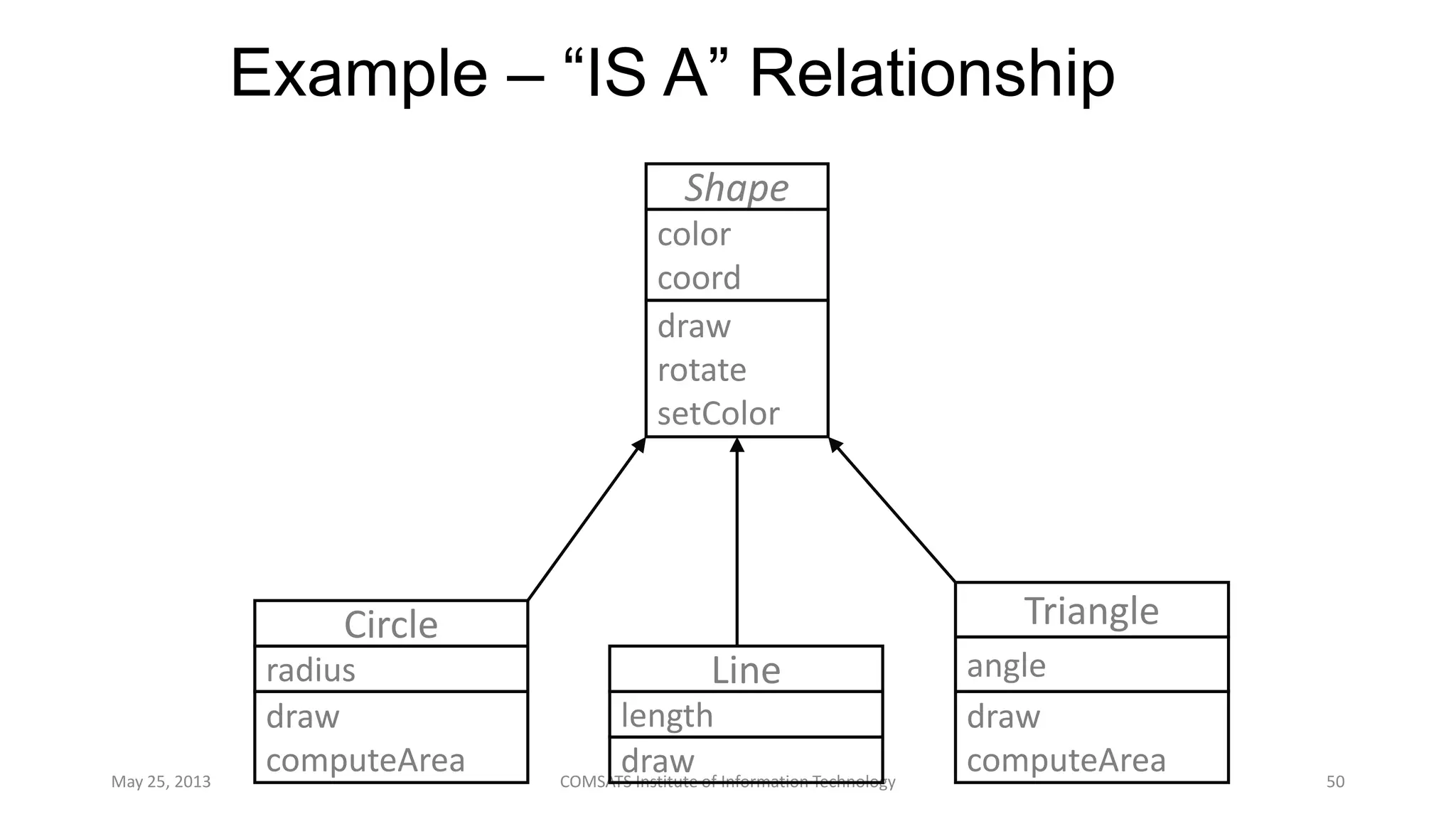
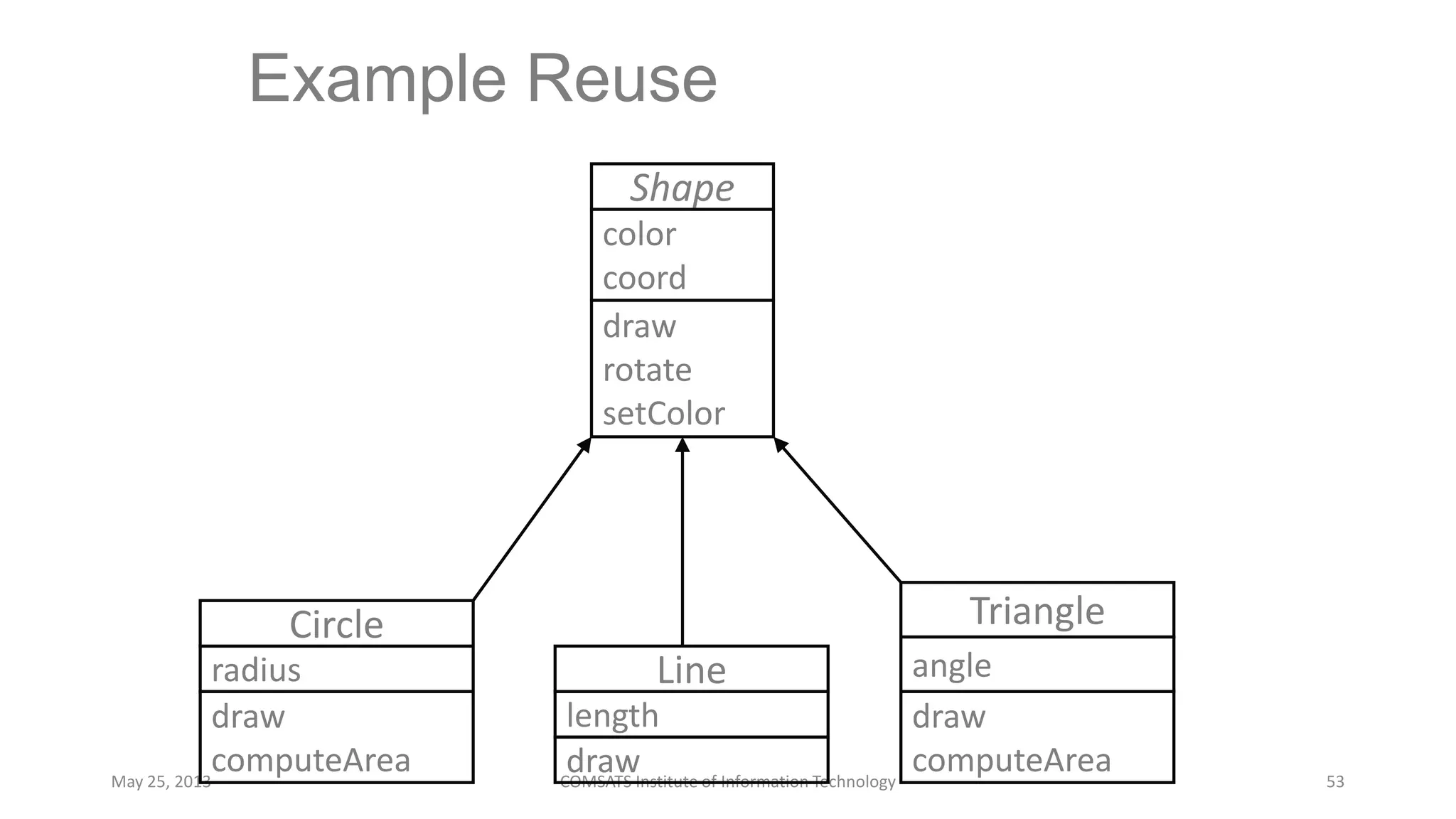
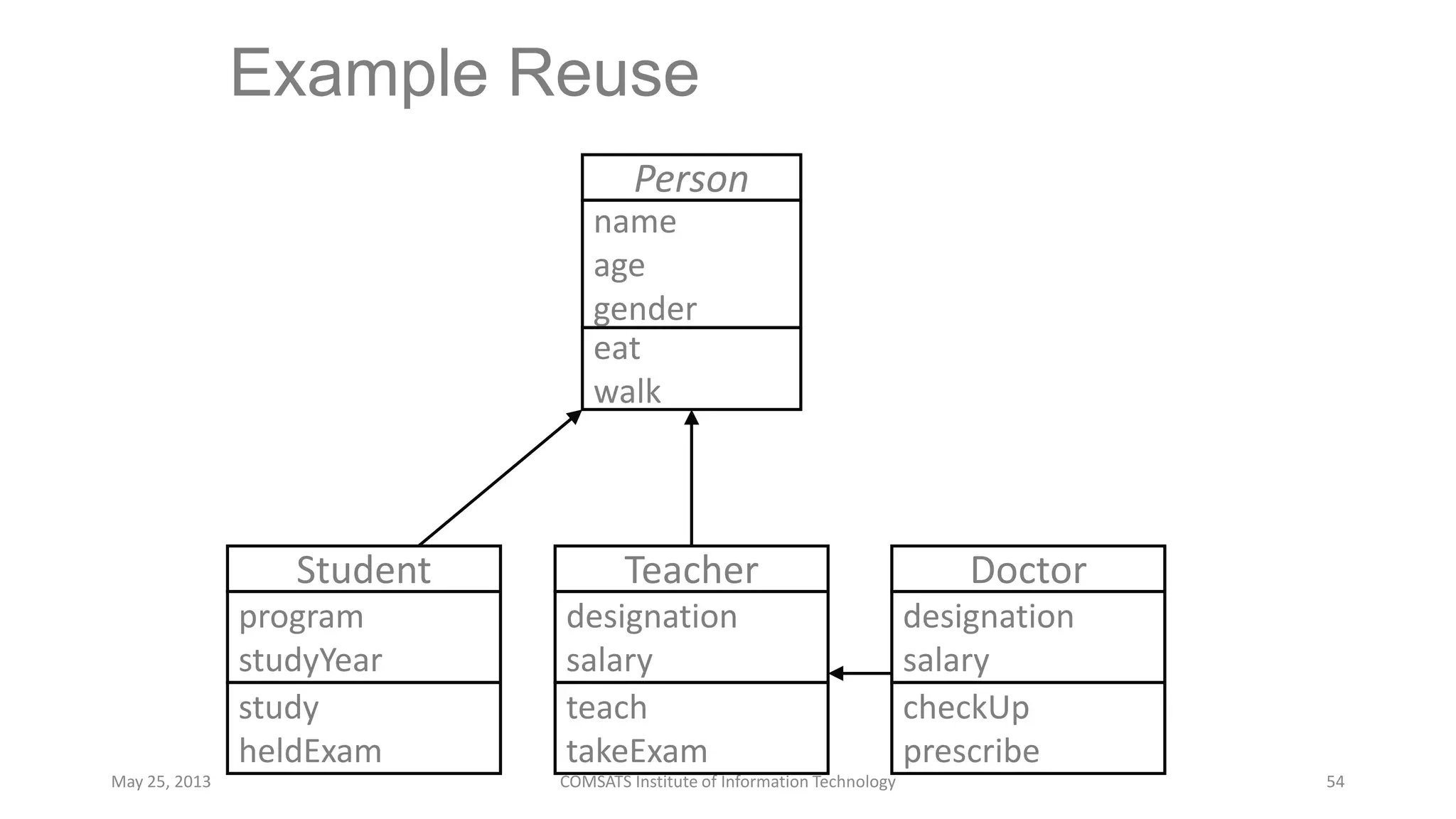
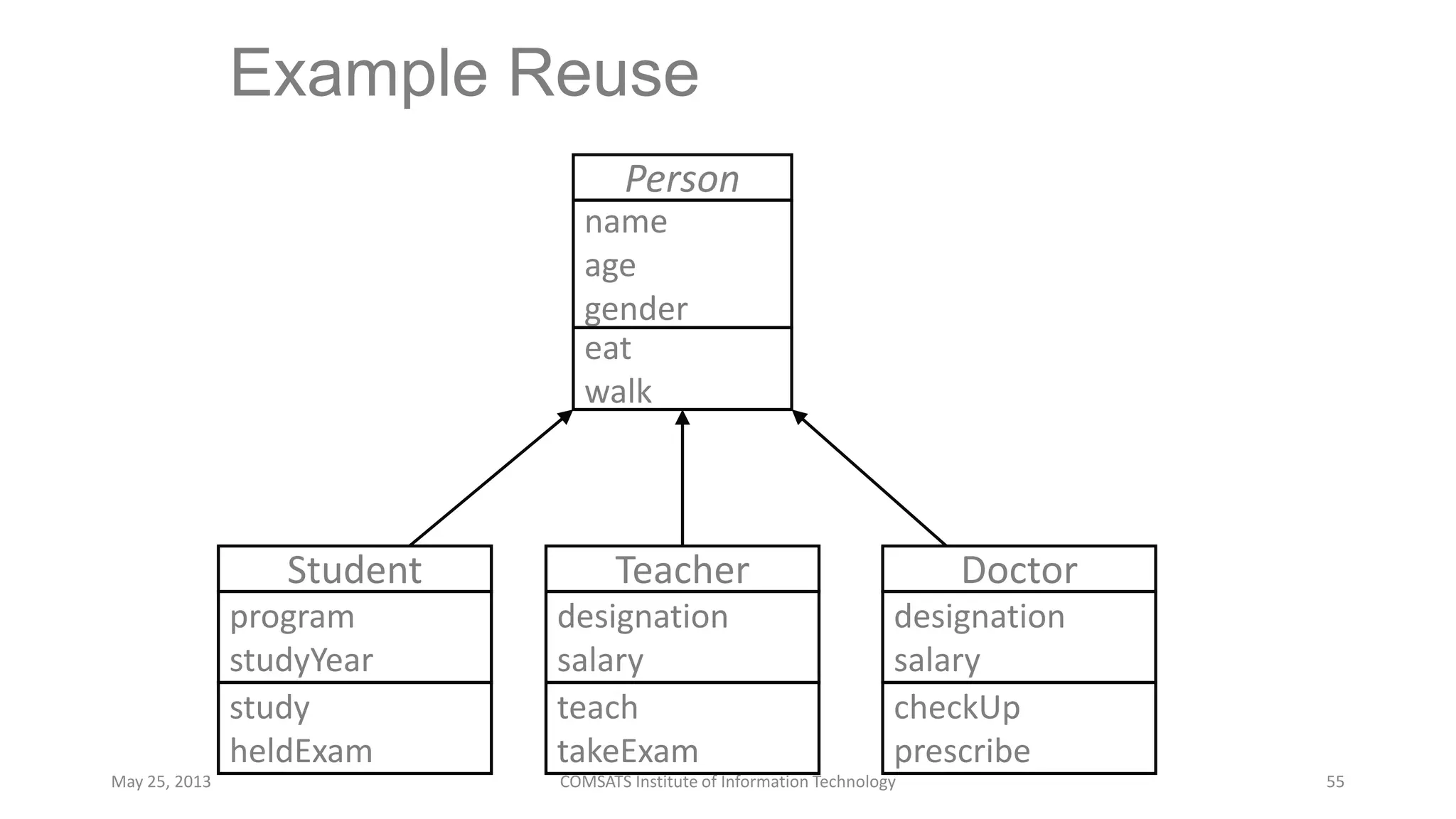
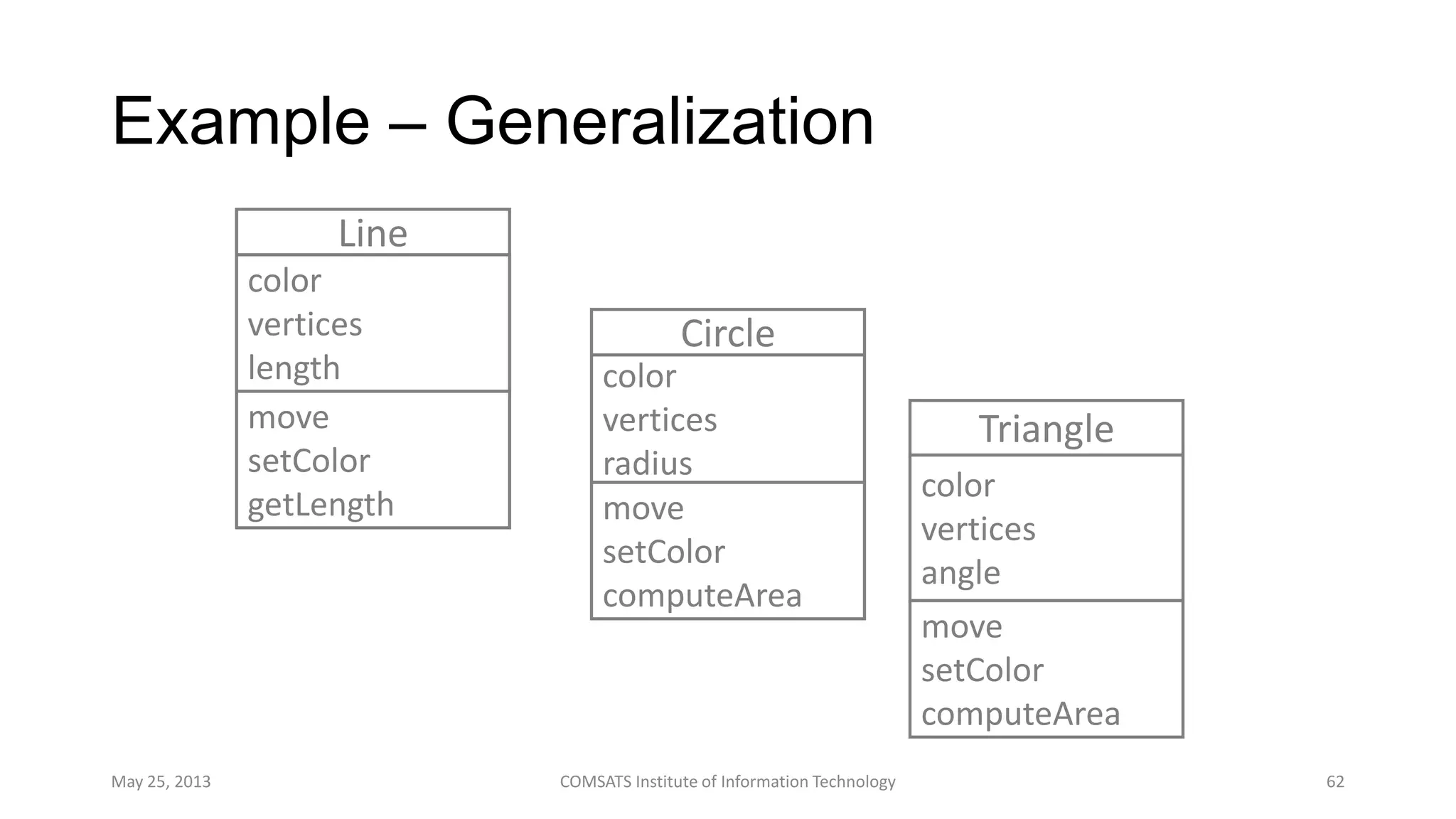
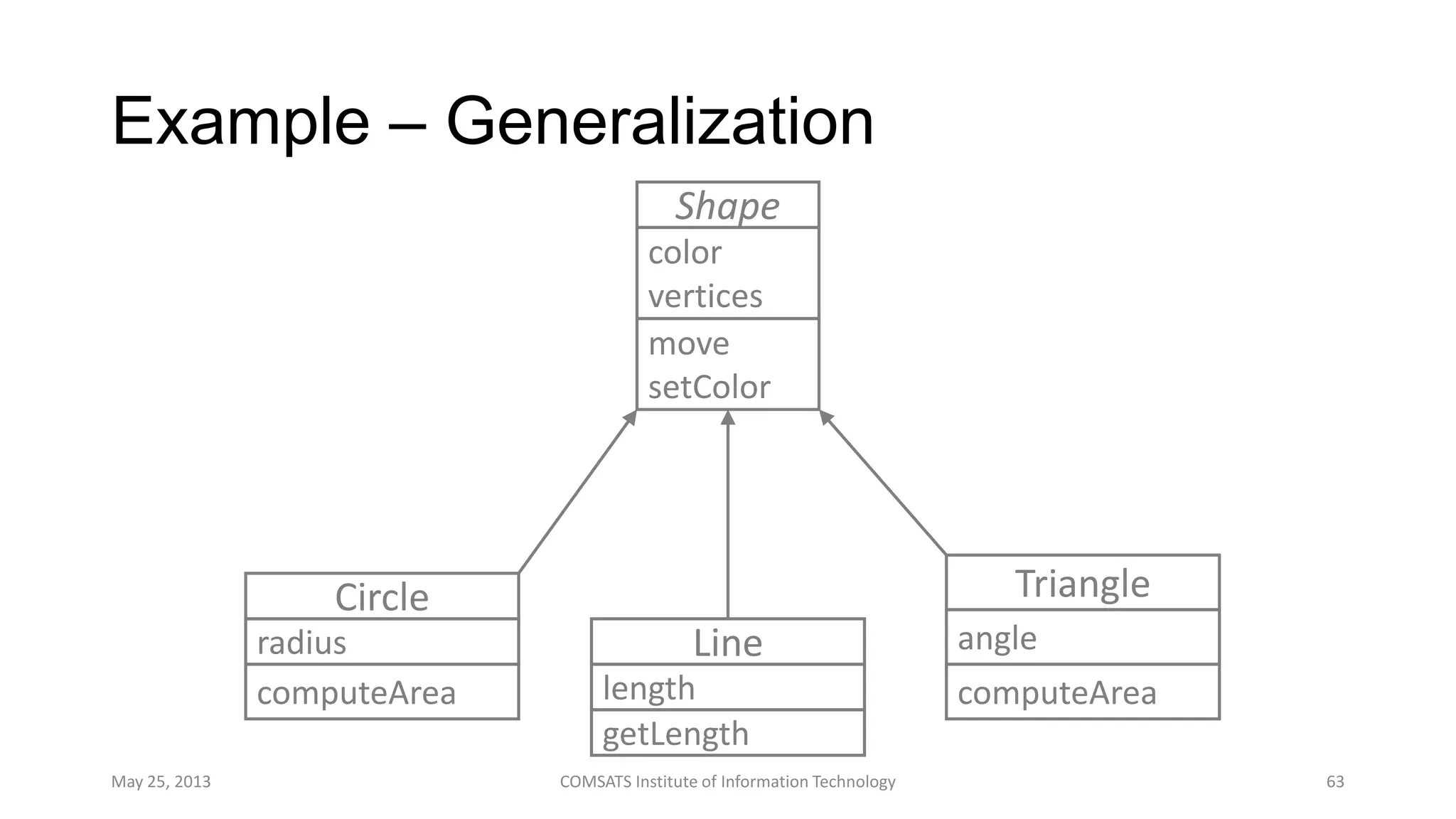
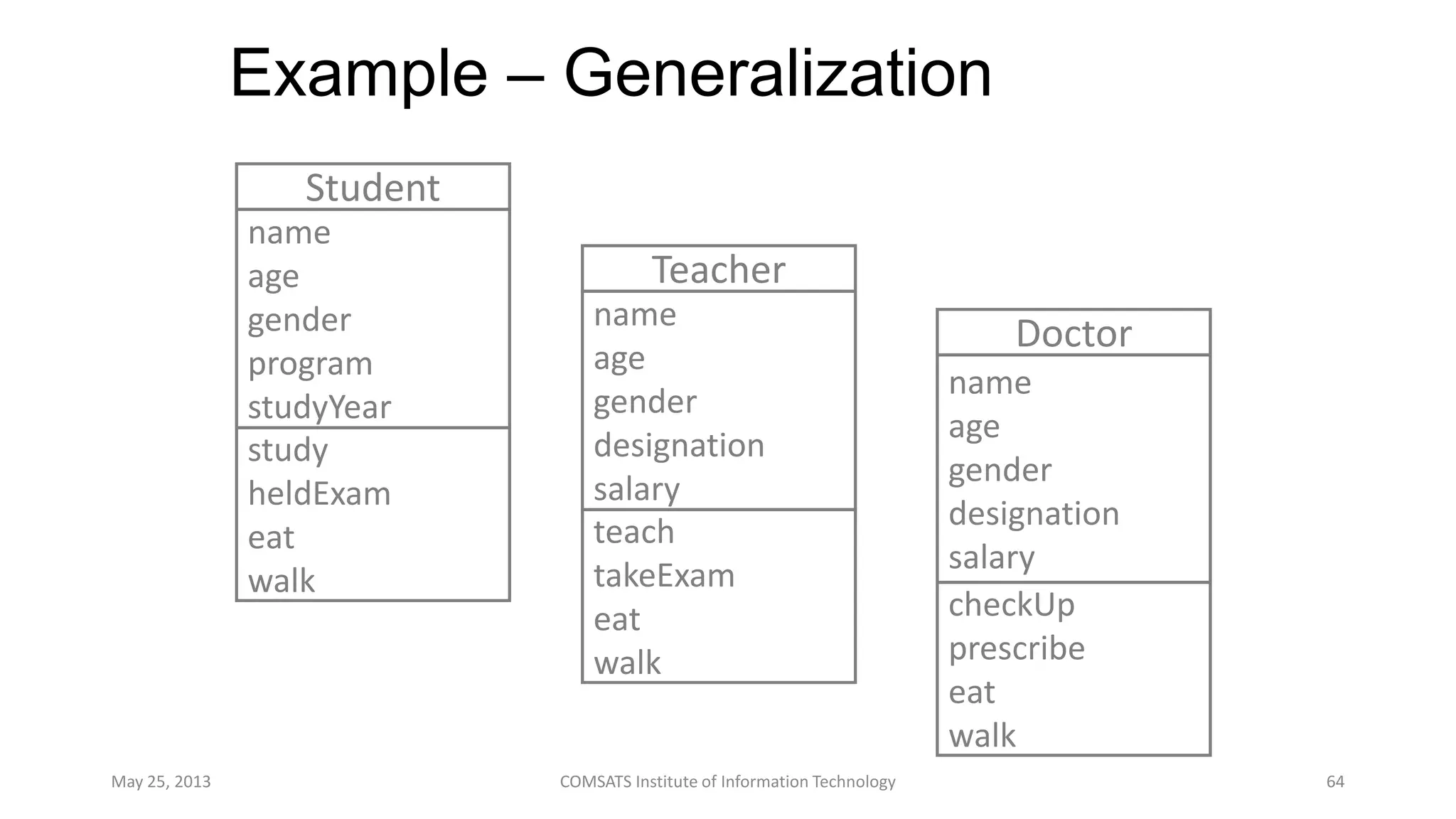
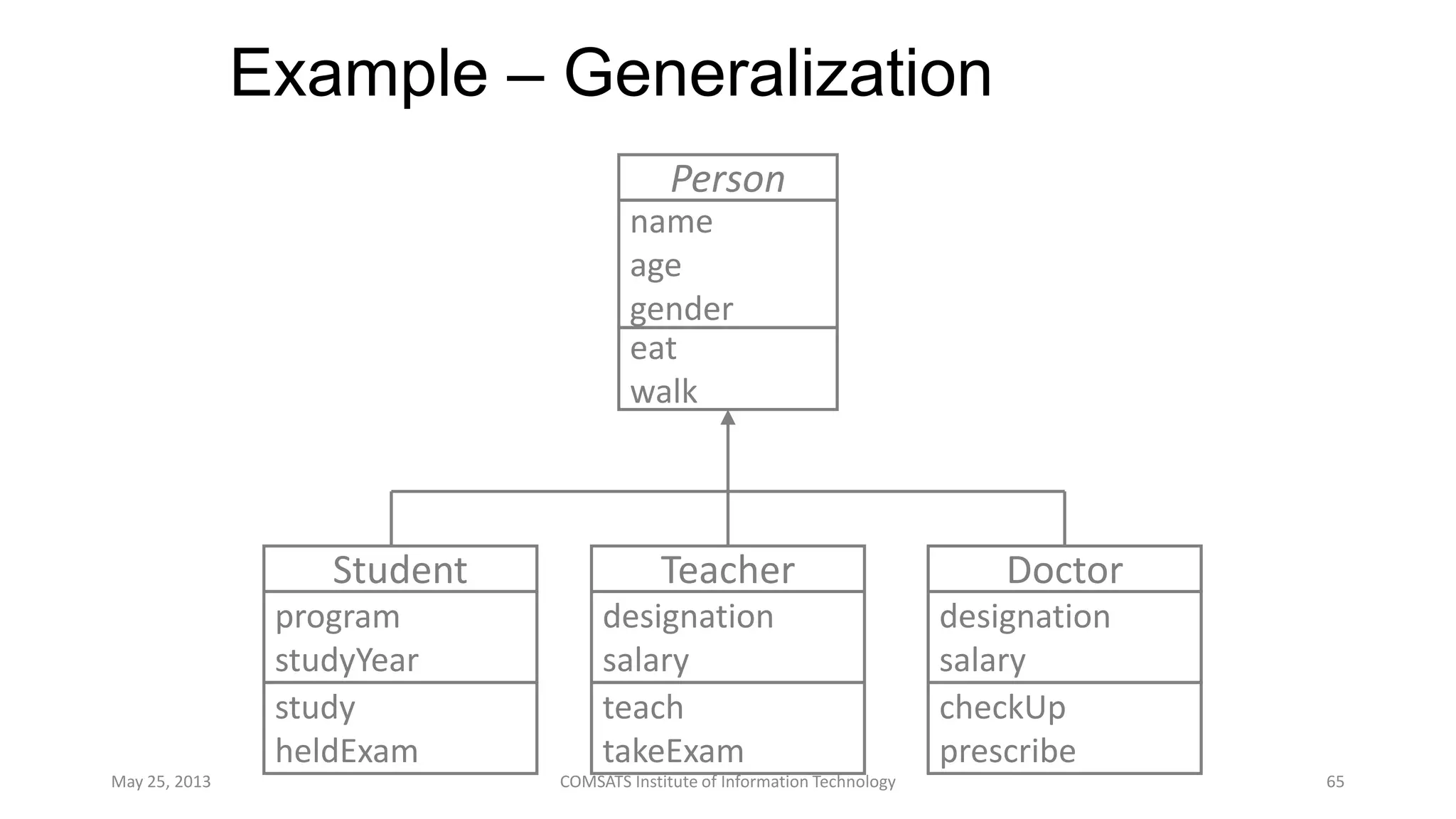
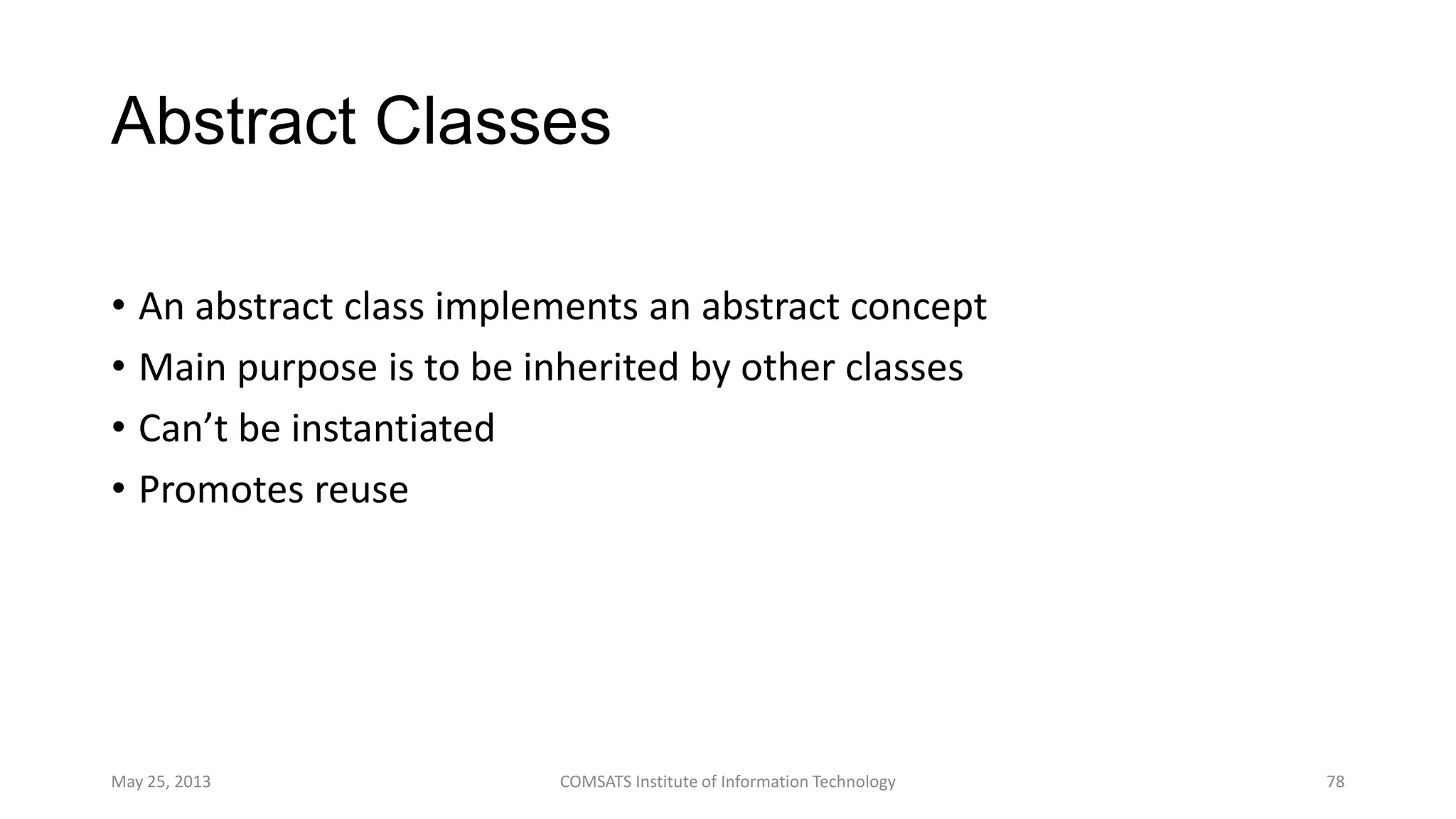
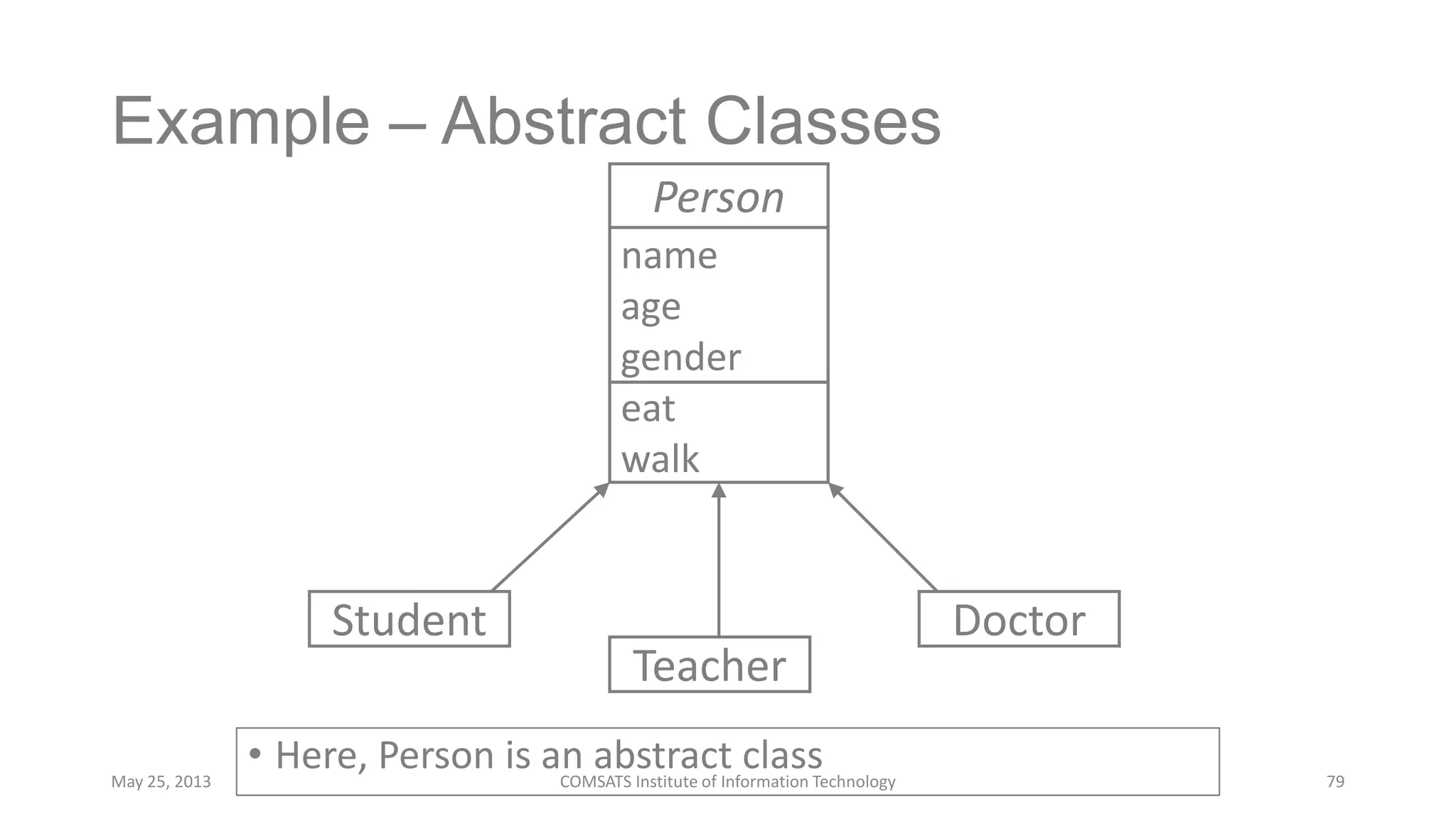
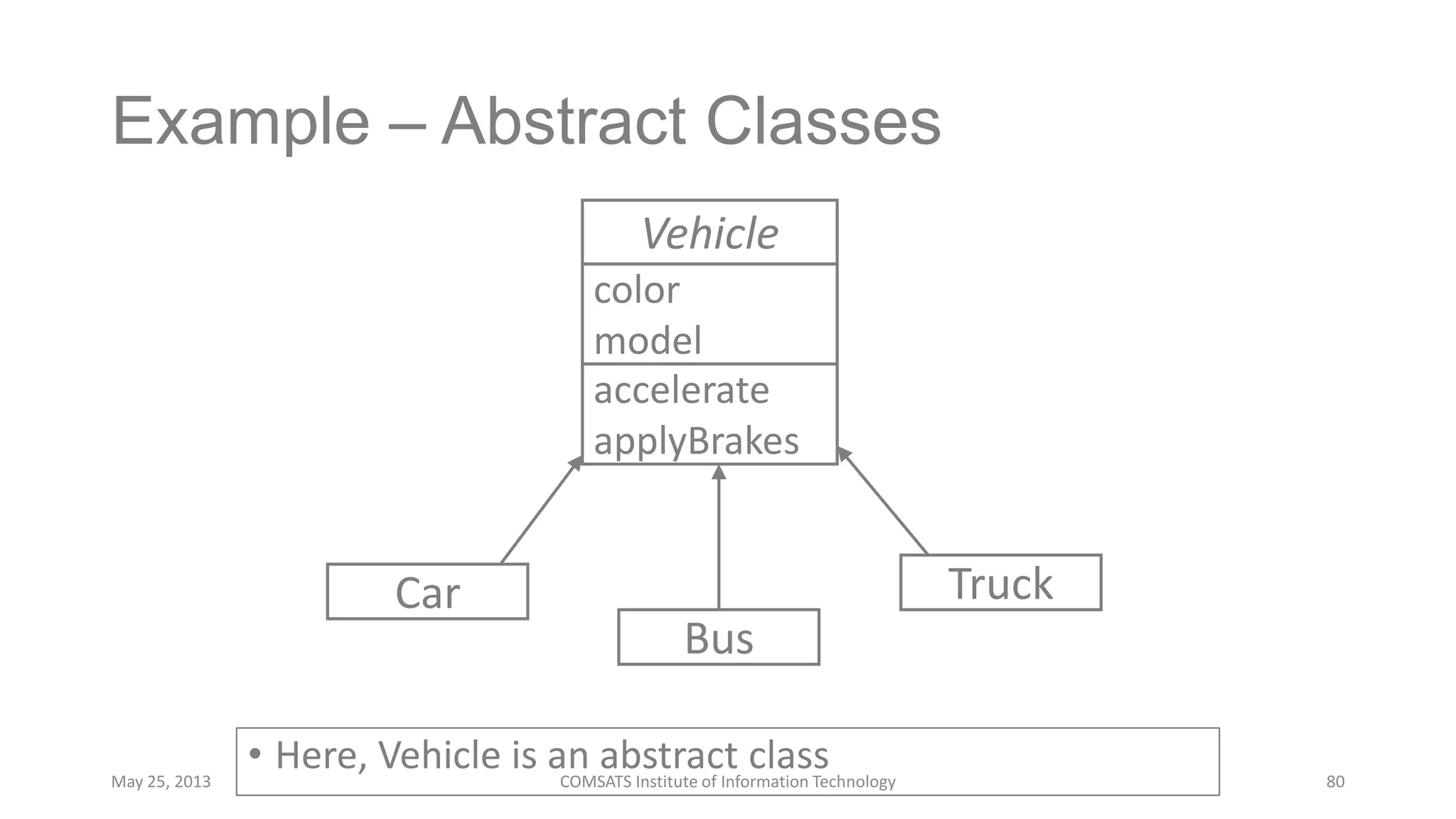
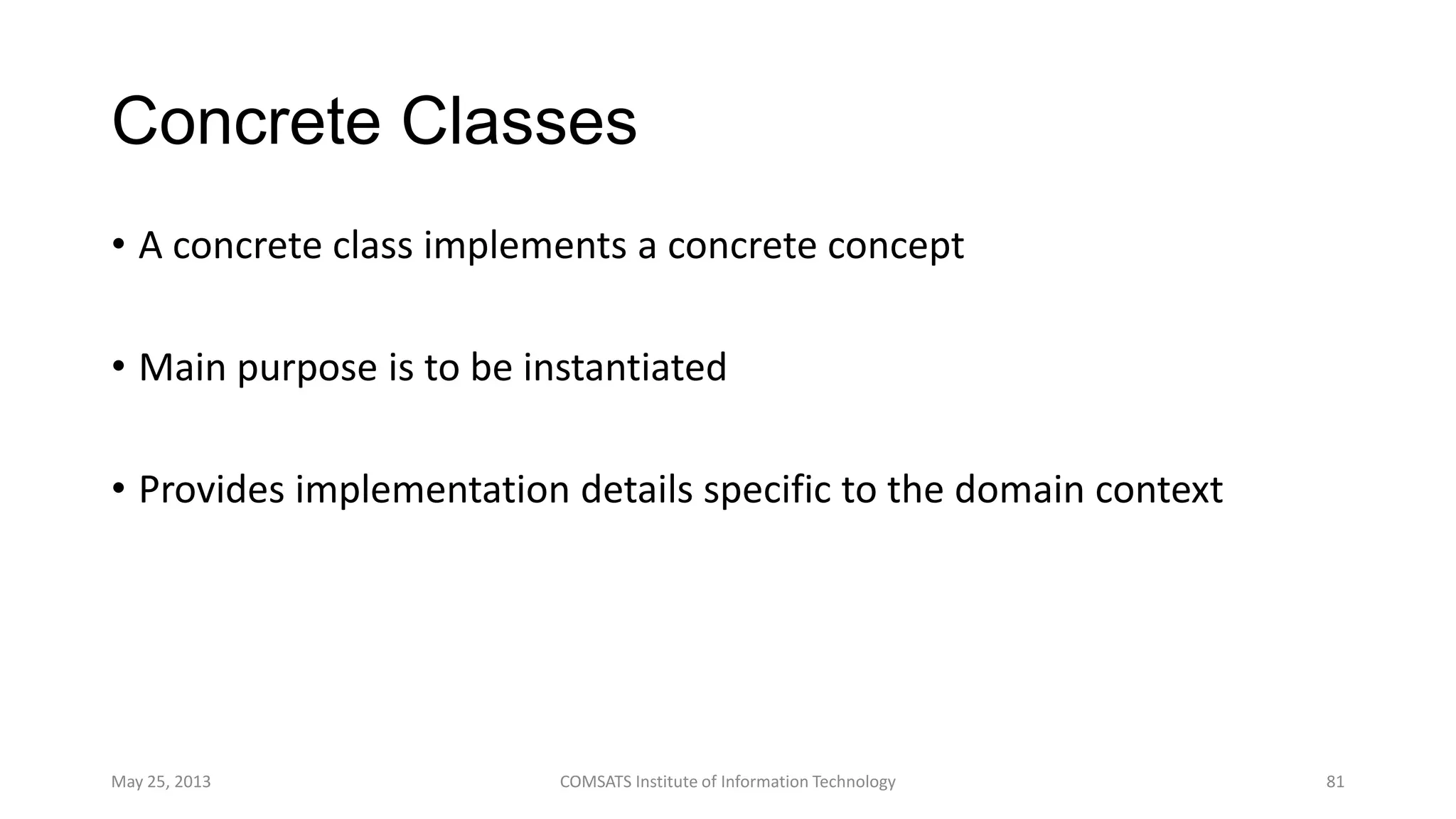
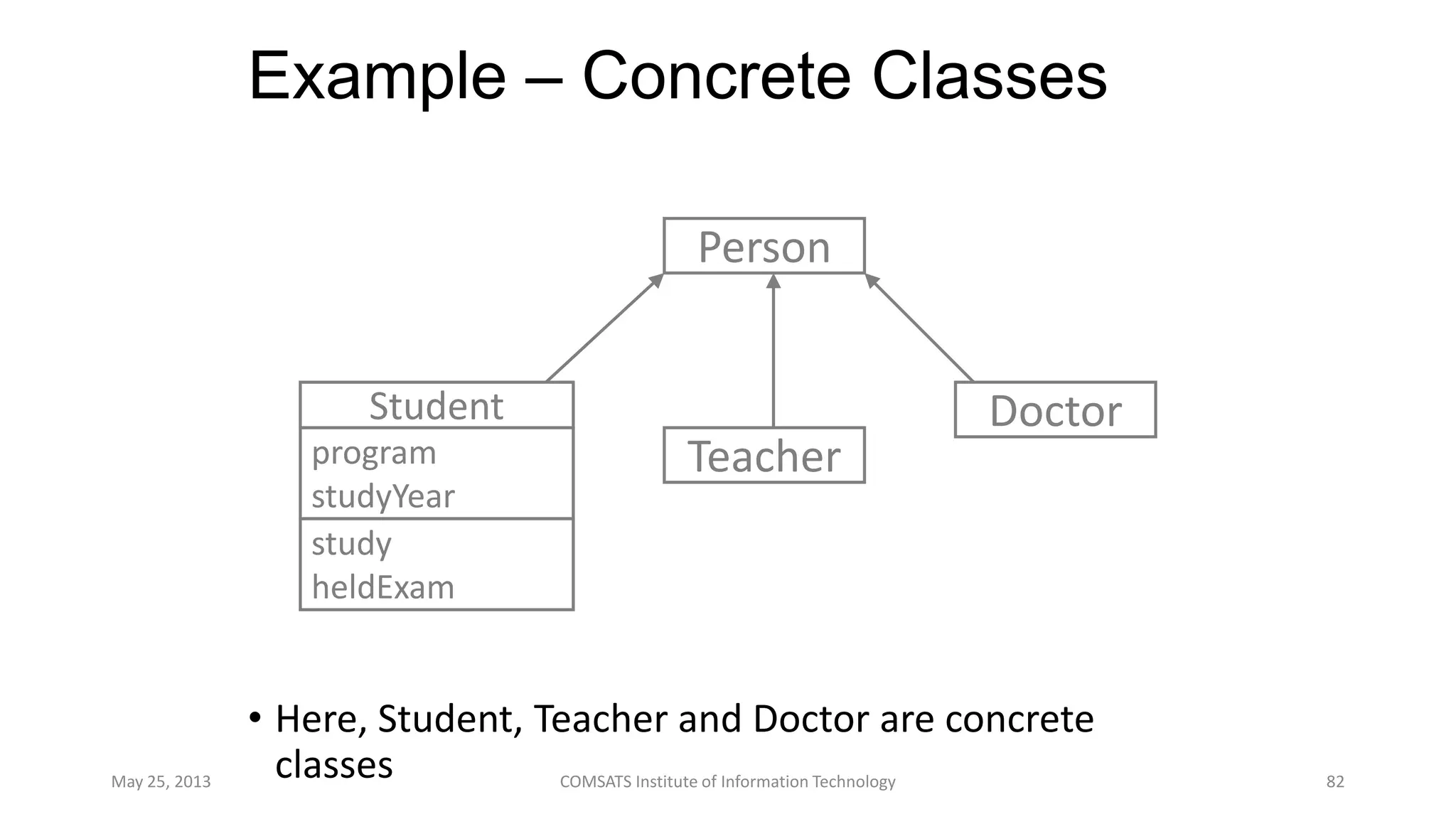
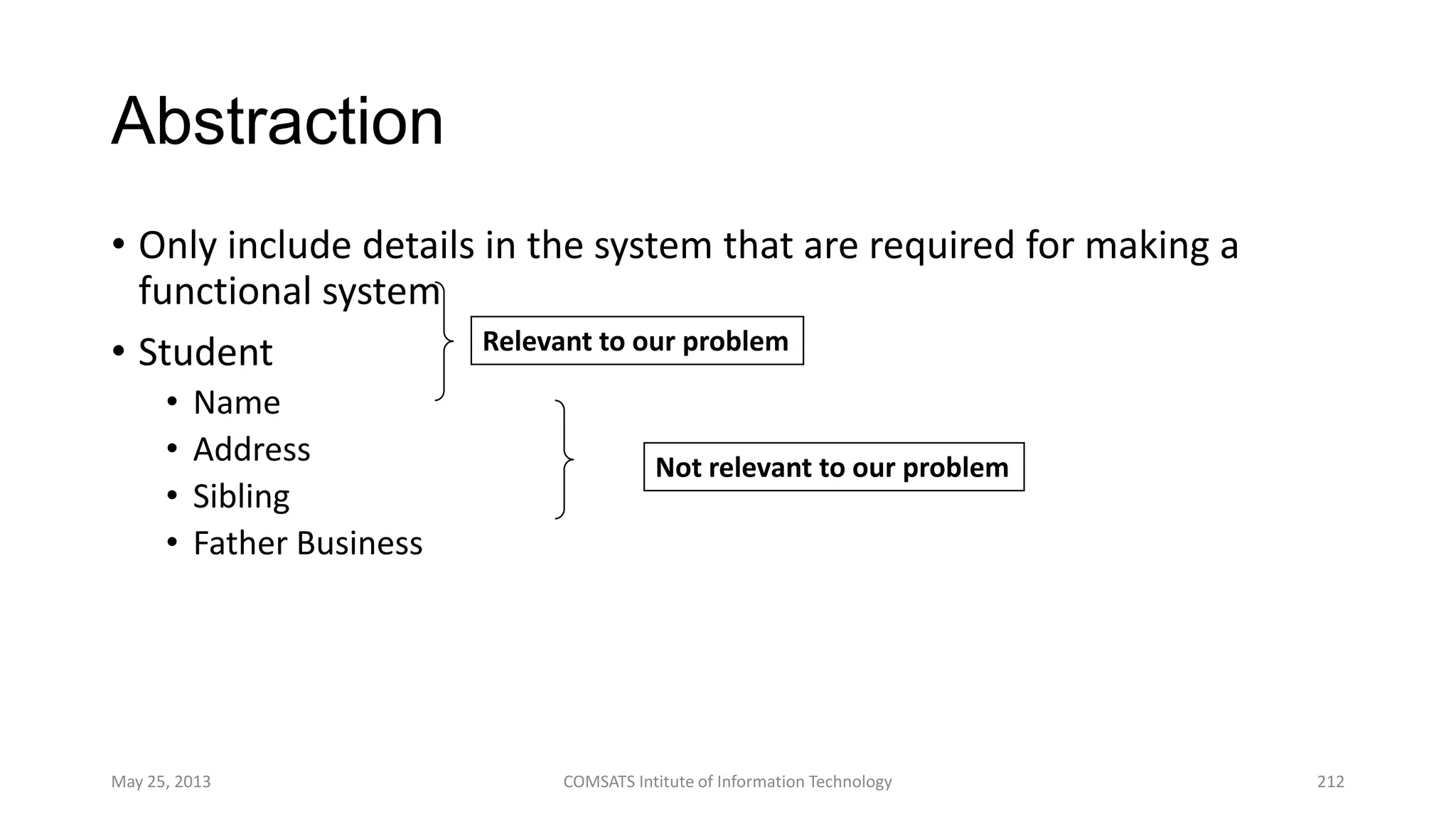
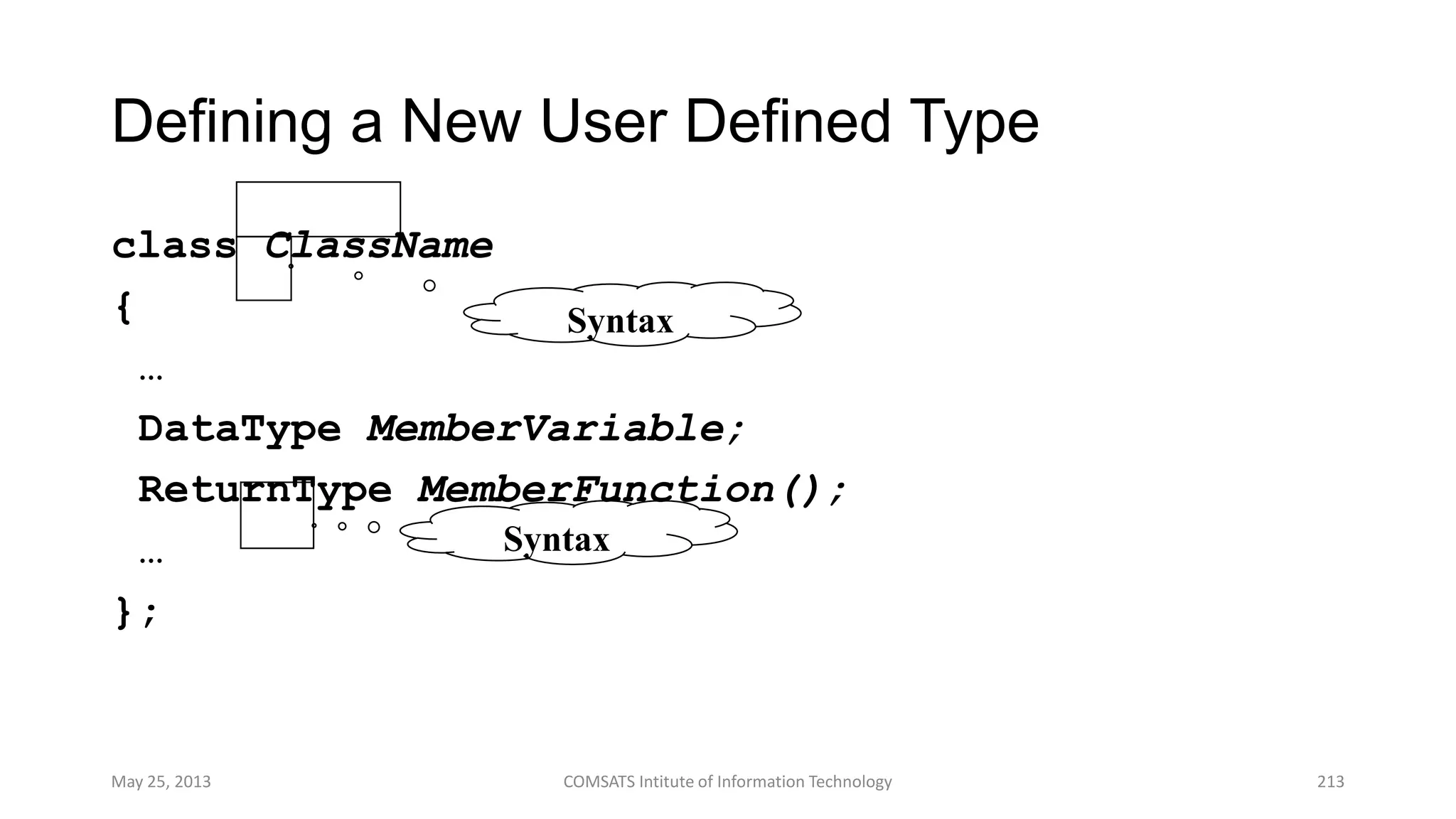
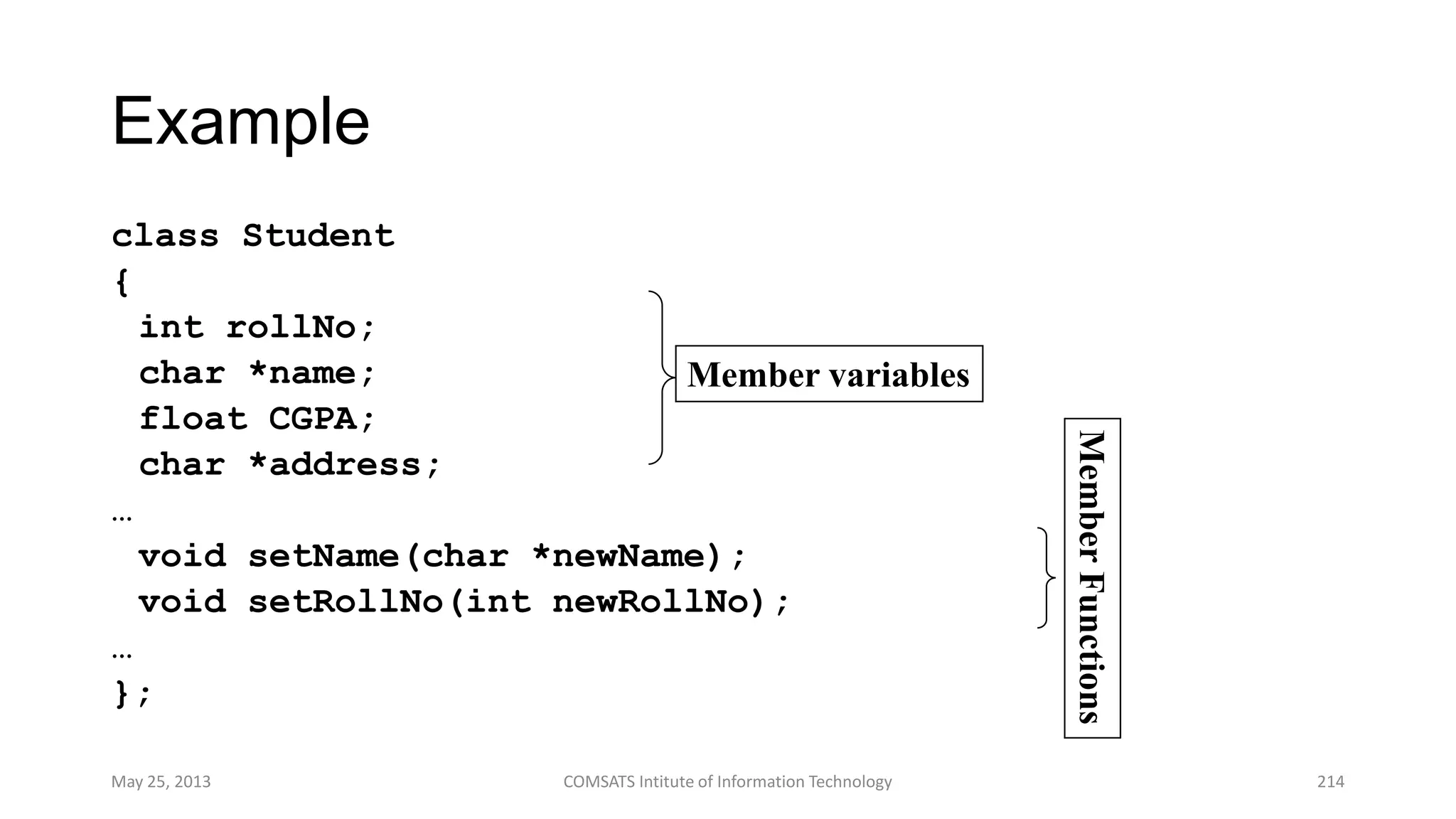
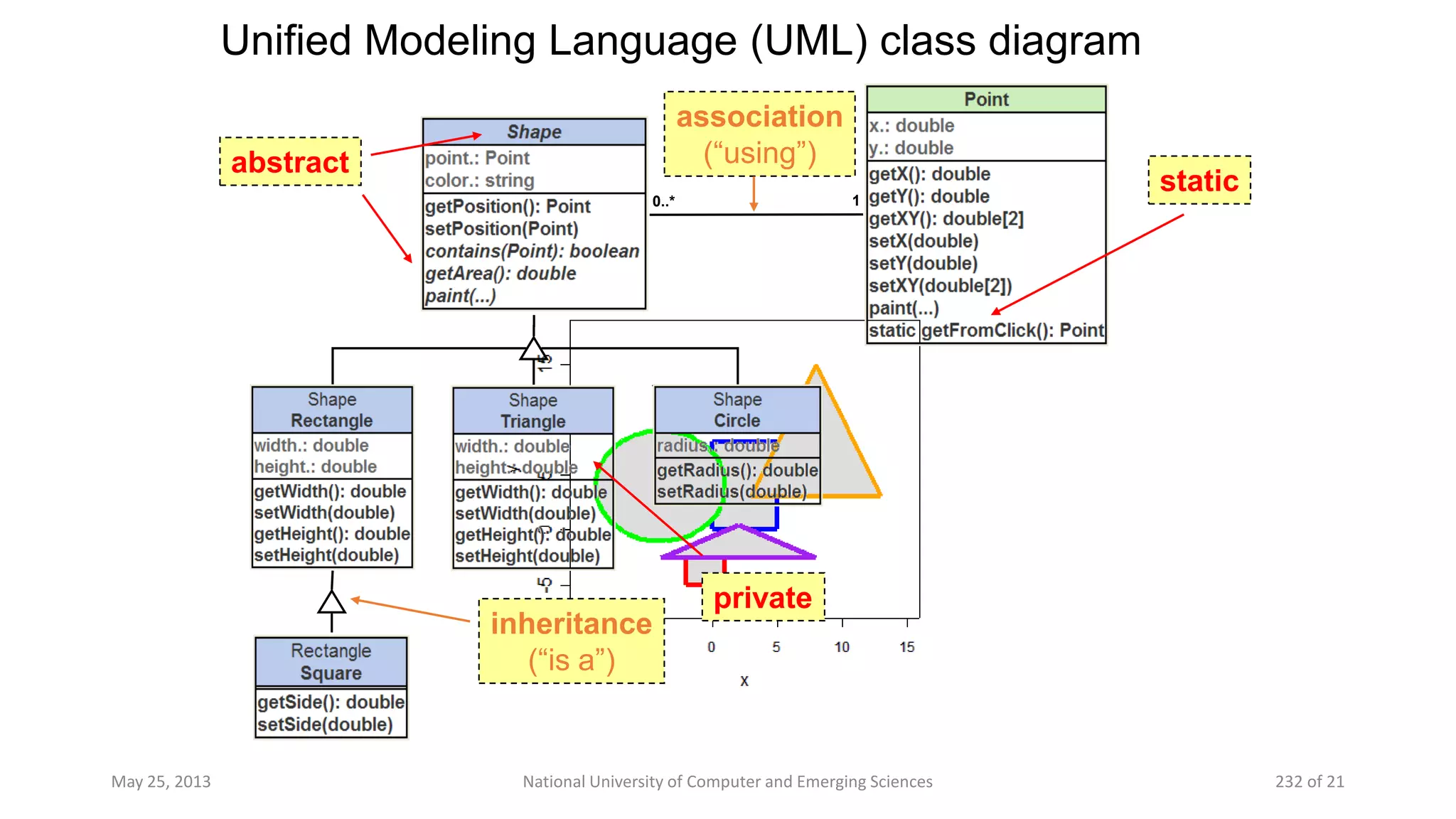
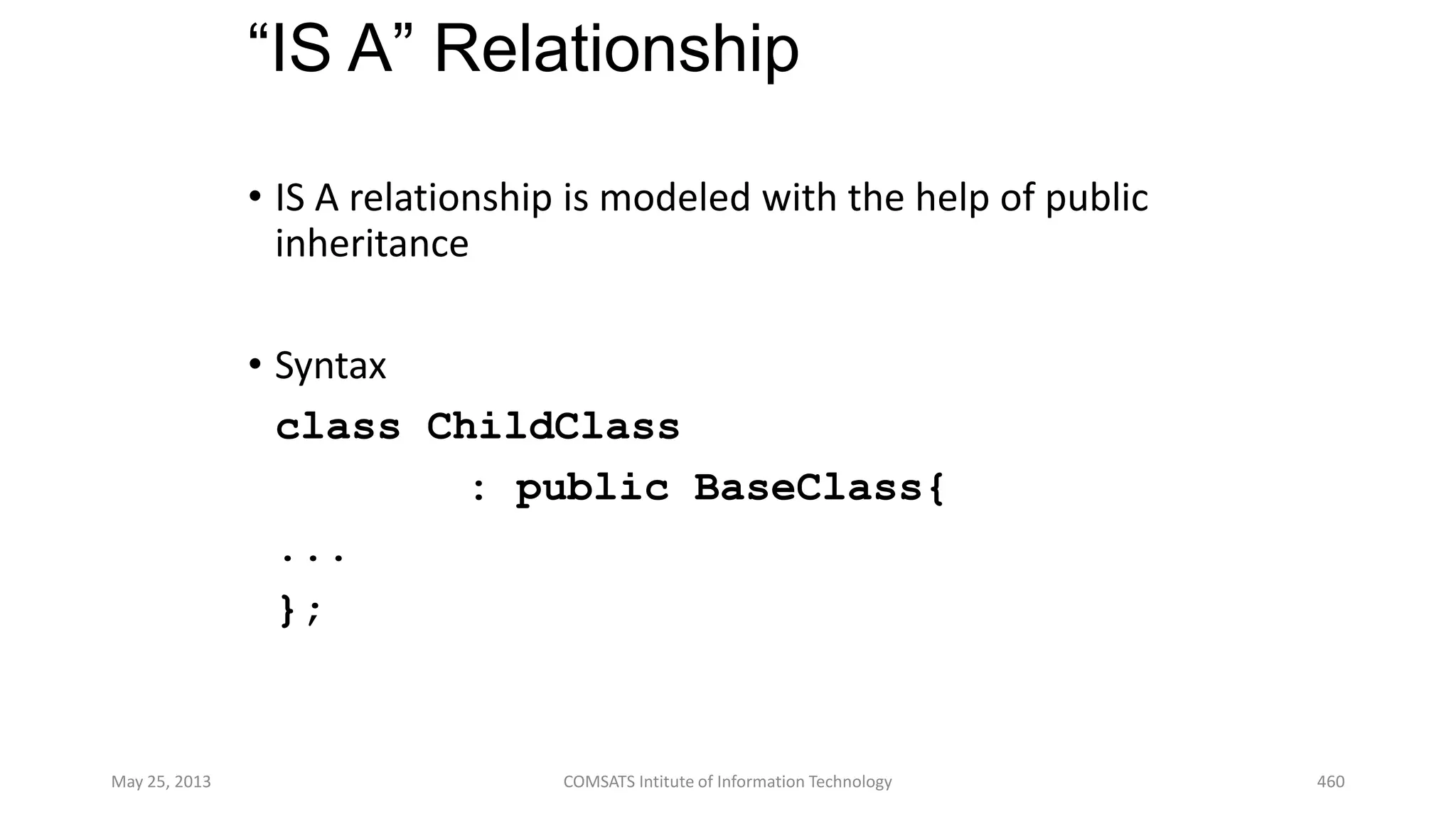
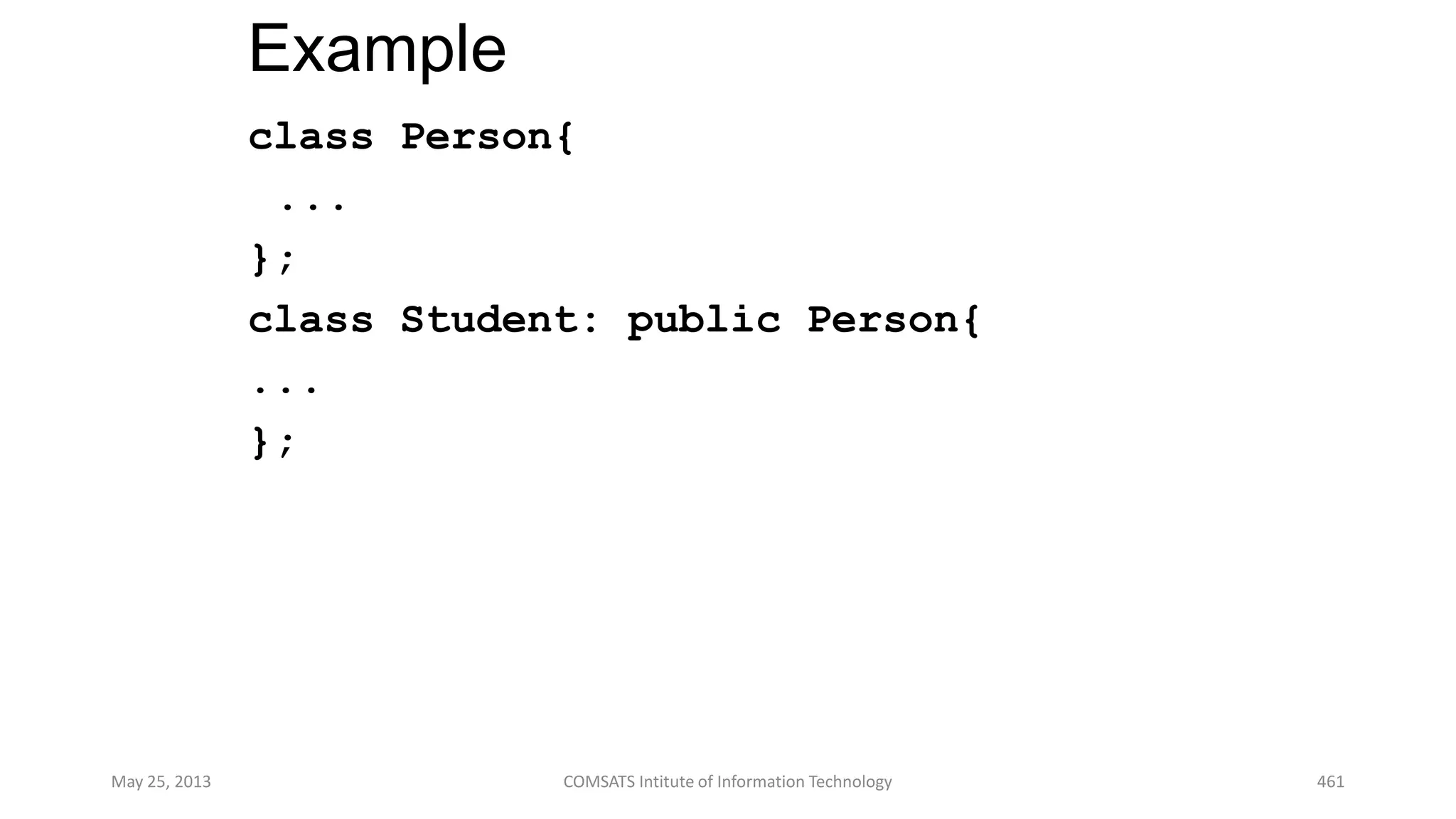
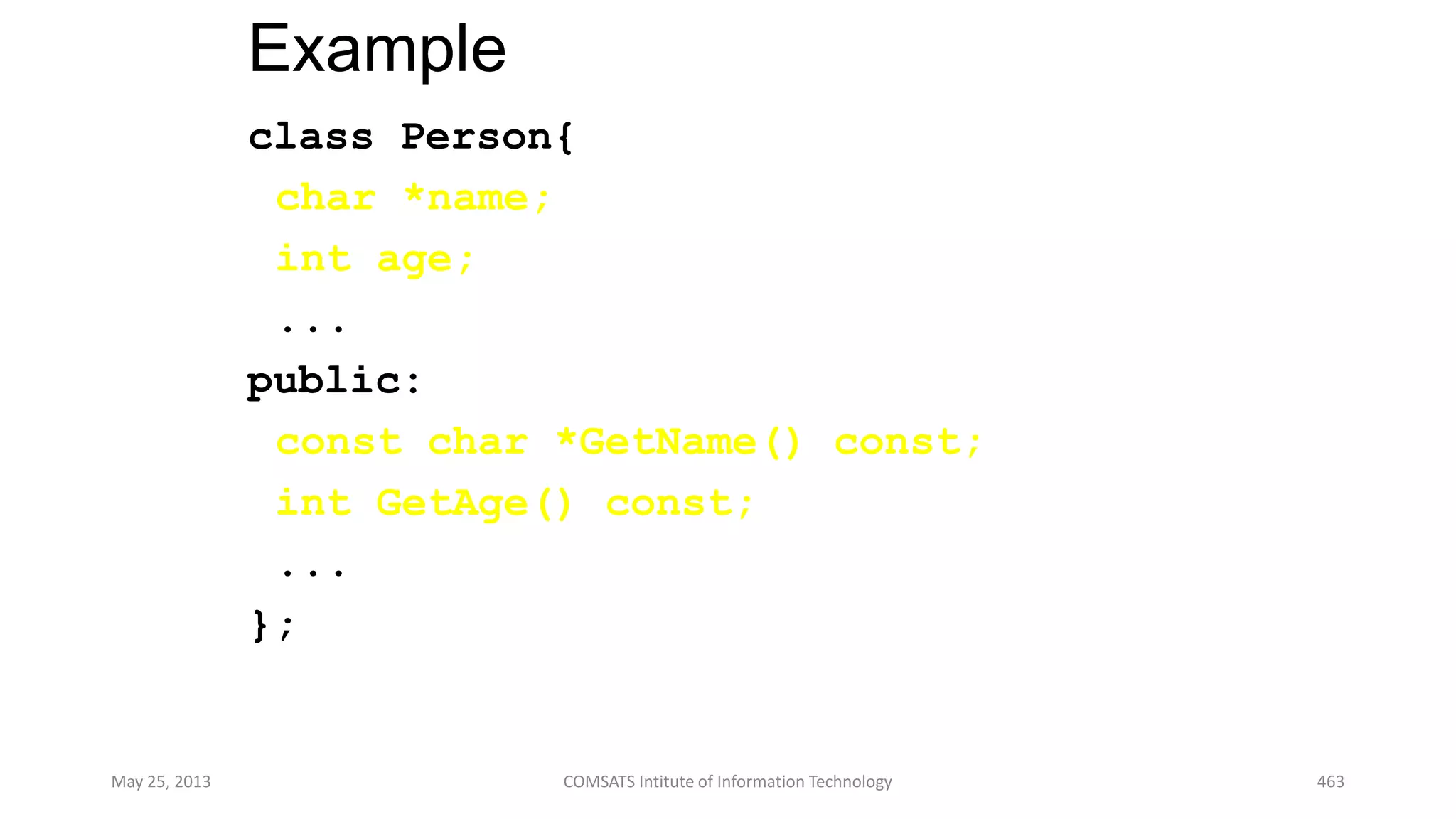
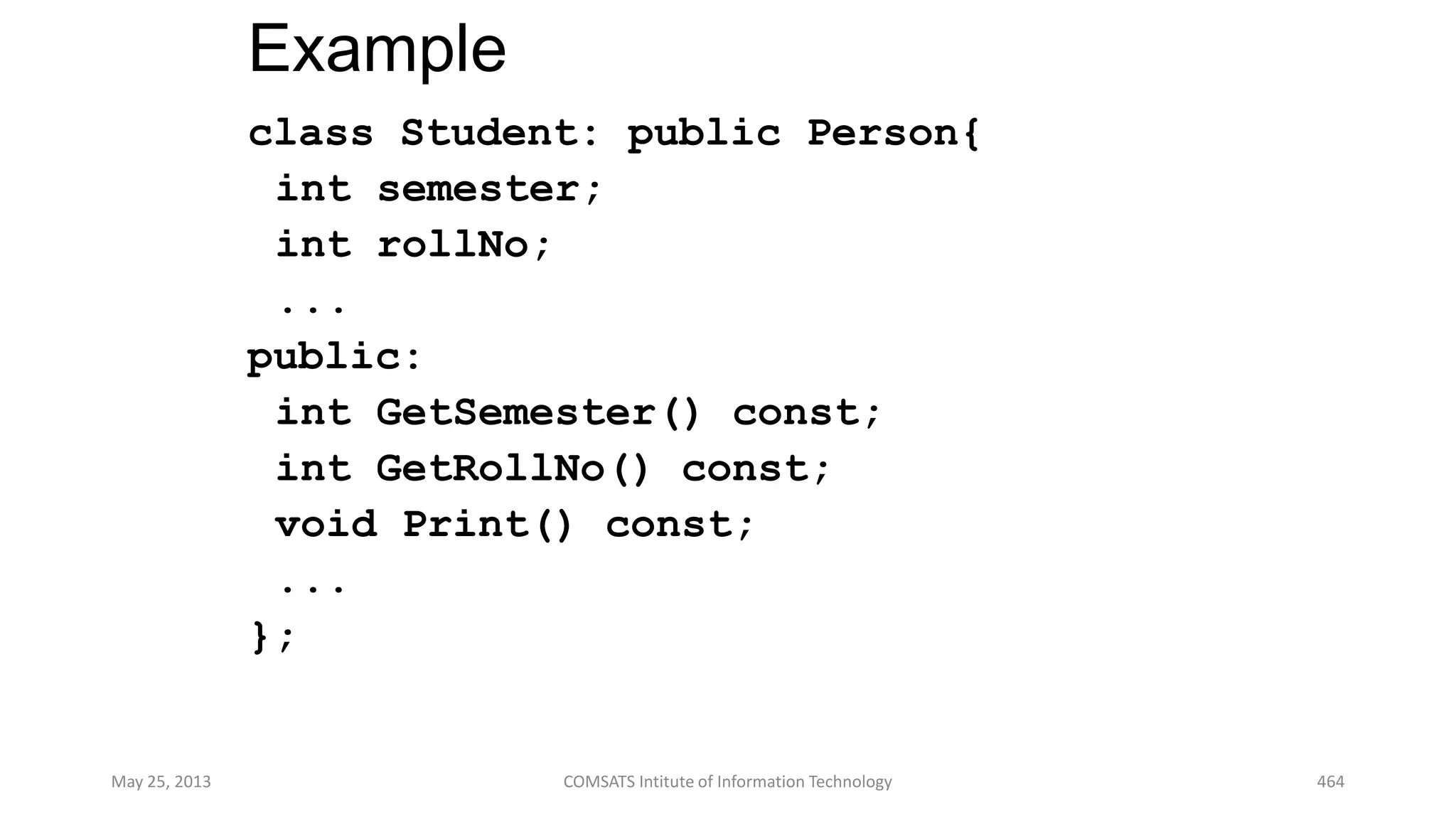
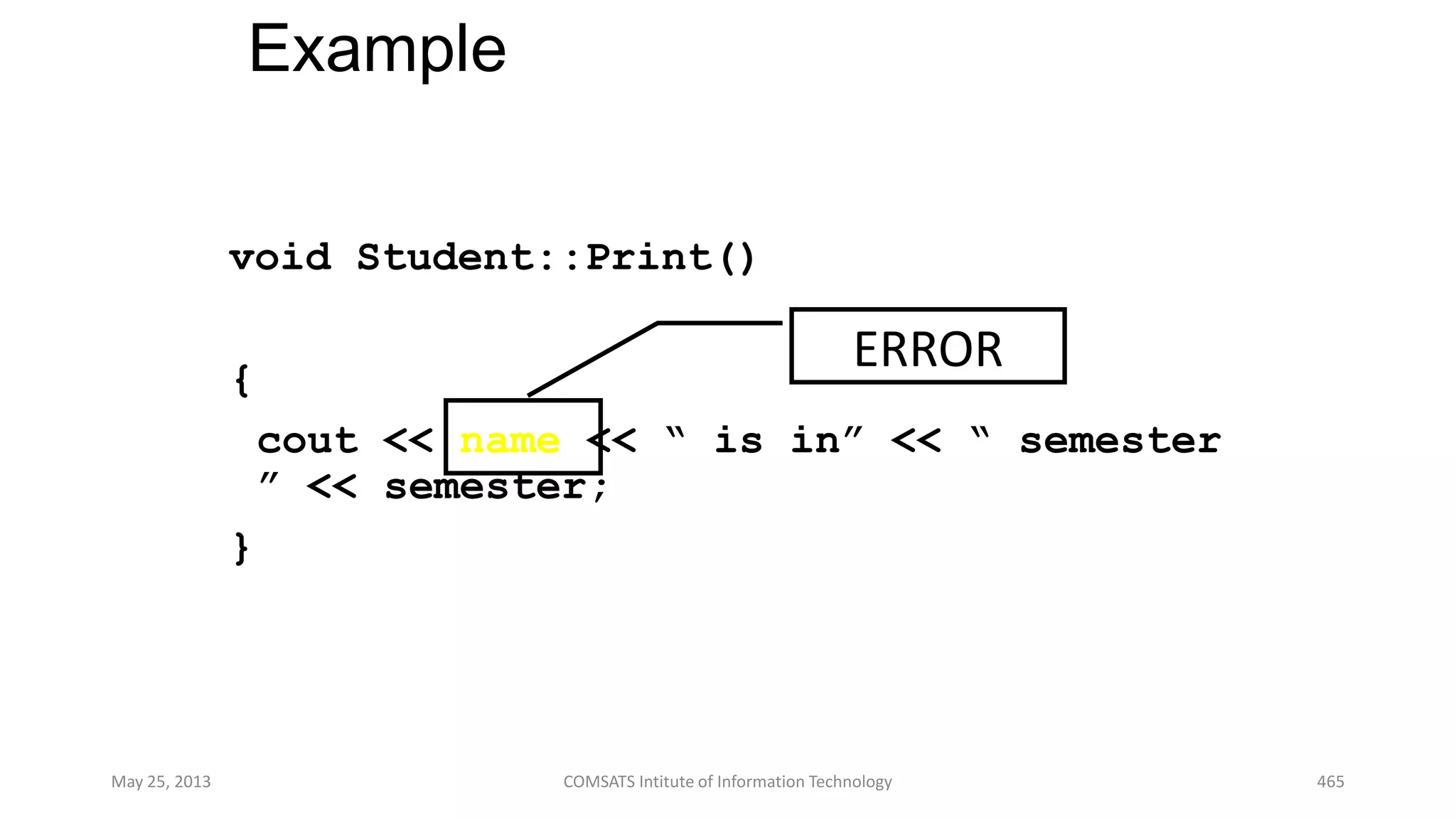
This document contains lecture notes on object-oriented programming. It discusses key OOP concepts like objects, classes, inheritance, abstraction and polymorphism. It provides examples like modeling a student, teacher and doctor as classes with common attributes and behaviors. Inheritance allows deriving more specific classes like defining a teacher or doctor class inheriting from a general person class. The notes emphasize that OOP aims to model real-world entities as interactive objects.
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May25,2013COMSATSInstituteofInformationTechnology
56](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-56-2048.jpg)
![Example – Specialization
(Restriction)
May 25, 2013 COMSATS Institute of Information Technology 71
Person
age : [0..100]
…
Adult
age : [18..100]
…
setAge( a )
…
setAge( a )
…
age = a
If age < 18 then
error
else
age = a](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-71-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May25,2013COMSATSInstituteofInformationTechnology
123](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-123-2048.jpg)

![More about „struct‟ …
struct stack {
int data[100];
int top;
} S;
///////////////////////////////////
void push(stack S, int a){
assert(top<100);
S.data[top]=a; S.top++;
}
May 25, 2013 COMSATS Intitute of Information Technology 163](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-162-2048.jpg)

![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 234](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-233-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 266](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-265-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 304](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-303-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 325](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-324-2048.jpg)

![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 348](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-347-2048.jpg)
![Defining, Reading and Writing Array
// gets four ages from user, displays them
#include <iostream>
using namespace std;
int main(){
int age[4], j; //array 'age' of 4 ints
for(j=0; j<4; j++){ //get 4 ages
cout << "Enter an age: ";
cin >> age[j]; //access array element
}
for(j=0; j<4; j++){ //display 4 ages
cout << "age[" << j << "] = " << age[j] << endl;
cout <<"Address " << &age[j] << " = " << age[j] <<
endl;
}
system("PAUSE"); return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-351-2048.jpg)
![Calculating Average
#include <iostream>
using namespace std;
int main(){
double avg, sum = 0 ;
int i ; int marks[10] ; /* array declaration */
for ( i = 0 ; i <= 9 ; i++ ){
cout << "nEnter marks ";
cin >> marks[i]; /* store data in array */
}
for ( i = 0 ; i <= 9 ; i++ )
sum = sum + marks[i] ; /* read data from
array*/
avg = sum / 10 ;
cout << "n Average marks = " << avg <<endl;
system("PAUSE"); return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-352-2048.jpg)
![Using Direct Access on an Array
// Using Direct Access on Array
#include <iostream>
using namespace std;
int main(){
int mem[]={50,60,70} ; // Initialize the array
cout << "mem[0] = " << mem[0] << endl;
cout << "mem[1] = " << mem[1] << endl;
cout << "mem[2] = " << mem[2] << endl;
mem[0] = 80;
mem[1] = 90;
mem[2] = 100;
cout << endl;
cout << "mem[0] = " << mem[0] << endl;
cout << "mem[1] = " << mem[1] << endl;
cout << "mem[2] = " << mem[2] << endl;
system("PAUSE"); return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-353-2048.jpg)
![Printing in Reverse Order
#include <iostream>
using namespace std;
int main(){
const int SIZE=5; // defines the size N for 5 elements
double a[SIZE]; // declares the array‟s elements as
type double
cout << "Enter " << SIZE << " numbers:t";
for (int i=0; i<SIZE; i++)
cin >> a[i];
cout << "In reverse order: ";
for (int i=SIZE-1; i>=0; i--)
cout << " " << a[i];
system("PAUSE"); return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-354-2048.jpg)
![Out of Bounds
#include <iostream>
using namespace std;
int main(){
float a[] = { 22.2,44.4, 66.6 };
float x=11.1;
cout << "I m going to Crash " << endl;
cin >> x;
a[3333] = 88.8; // ERROR: index is out of bounds!
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-355-2048.jpg)
![Passing Array to Function
#include <iostream>
using namespace std;
int sum(int[],int); // declaration
int main(){
int a[] = { 11,33, 55,77 };
int size = sizeof(a)/sizeof(int);
cout << "sum(a,size) = " << sum(a,size) << endl;
cout << endl << a[0] << endl;
system("PAUSE"); return 0;
}
int sum(int a[],int n){
int sum=0;
for (int i=0; i<n; i++)
sum += a[i];
a[0] = 100;
return sum;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-356-2048.jpg)
![n Dimensional Arrays
#include <iostream>
using namespace std;
int main(){ const int row=2, col=3; int i,j;
int ary[row][col] = {
{11,12,13},
{21,22,23}
};
for(i=0 ; i< row ; i++){
for(j=0 ; j<col; j++){ cout << ary[i][j] << " ";}
cout << endl;
}
for(i=0 ; i< row ; i++){
for(j=0 ; j<col; j++){
cout << &ary[i][j] << "="<<ary[i][j]<<"t";}
cout << endl;}
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-357-2048.jpg)
![n Dimensional Arrays
0x22ff40 = 11
0x22ff44 = 12
0x22ff48 = 13
0x22ff4C = 21
0x22ff50 = 22
0x22ff54 = 23
ary[0][0]=
ary[0][1]=
ary[0][2]=
ary[1][0]=
ary[1][1]=
ary[1][2]=
232221
131211](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-358-2048.jpg)
![2-Dimensional Arrays
#include <iostream>
using namespace std;
int main(){ const int row=3, col=3; int i,j;
int ary[row][col] = {
{11,12,13},
{21,22,23},
{31,32,33} };
for(i=0 ; i< row ; i++){
for(j=0 ; j<col; j++){ cout << ary[i][j] << " ";}
cout << endl;
}
for(i=0 ; i< row ; i++){
for(j=0 ; j<col; j++){
cout << &ary[i][j] << "="<<ary[i][j]<<"t";}
cout << endl;}
system("PAUSE"); return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-359-2048.jpg)
![3-Dimensional Arrays
0x22ff30 = 11
0x22ff34 = 12
0x22ff38 = 13
0x22ff3C = 21
0x22ff40 = 22
0x22ff44 = 23
ary[0][0]=
ary[0][1]=
ary[0][2]=
ary[1][0]=
ary[1][1]=
ary[1][2]=
0x22ff48 = 31
0x22ff4C = 32
0x22ff50 = 33
ary[2][0]=
ary[2][1]=
ary[2][2]=
333231
232221
131211](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-360-2048.jpg)
![Calculating Square of a Matrix
#include <iostream>
using namespace std;
int main(){ const int row=3, col=3; int i,j;
int A[row][col];
cout << "Square of a " <<row <<"x"<<col<<"Matrices"<<endl;
for(i=0 ; i< row ; i++){
for(j=0 ; j<col; j++){
cout << "A[" << i+1 << "][" << j+1 << "]= ";
cin >> A[i][j];
}
}
for(i=0 ; i< row ; i++)
for(j=0 ; j<col; j++)
A[i][j] = A[i][j]*A[i][j];
for(i=0 ; i< row ; i++){
for(j=0 ; j<col; j++)
cout << A[i][j] << "t";
cout << endl;
}
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-361-2048.jpg)
![Passing 2D Array to Function
#include <iostream>
using namespace std;
void get_data(float a[][3],int row, int col){
int i,j;
for (i=0; i<row; i++)
for (j=0; j<col; j++){
cout << "A["<<i+1<<"]["<<j+1<<"]:";
cin >> a[i][j];}
}
void show_data(float a[][3],int row, int col){
int i,j;
for (i=0; i<row; i++){
for (j=0; j<col; j++)
{cout << a[i][j] << "t";}
cout << endl; }
}
int main(){
float matrix[4][3]; // 4 rows and 3 columns
get_data(matrix,4,3);
show_data(matrix,4,3);
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-362-2048.jpg)
![Passing 3D Array to Function (1/2)
#include <iostream>
using namespace std;
void get_data(float a[][3][2],int row, int col,int page){
int i,j,k;
for (k=0; k<page; k++){
for (i=0; i<row; i++){
for (j=0; j<col; j++){
cout <<"A["<< i <<"]["<< j <<"]["<< k <<"]:";
cin >> a[i][j][k];
} // end of for (j=0
} // end of for (i=0
} // end of for (k=0
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-363-2048.jpg)
![Passing 3D Array to Function (2/2)
void show_data(float a[][3][2],int row, int col, int page){
int i,j,k;
for (k=0; k<page; k++){
for (i=0; i<row; i++){
for (j=0; j<col; j++){
cout << a[i][j][k] << "t";
}
cout << endl;
}
cout << endl;
}
}
int main(){
float matrix[4][3][2]; // 4 rows, 3 columns, 2 pages
get_data(matrix,4,3,2);
show_data(matrix,4,3,2);
system("PAUSE");
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-364-2048.jpg)
![Sorting Data Using Bubble Sort Algo
#include <iostream>
using namespace std;
void print( float[], int );
void sort ( float[], int );
int main(){
int i; float data[10];
cout << "Enter 10 Numbers for Sorting n";
for( i=0 ; i<10 ; i++ ){
cout << "Enter No." <<i+1<< ":" ;
cin >> data[i];
}
sort(data,10);
print(data,10);
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-365-2048.jpg)
![Sorting Data Using Bubble Sort Algo
void sort( float a[], int n ){ // bubble sort:
for (int i=1; i<n; i++) // bubble up max{a[0..n-i]}:
for (int j=0; j<n-i; j++)
if (a[j] > a[j+1]){
float temp = a[j];
a[j]=a[j+1];
a[j+1] = temp;
}
}
void print( float a[], int n ){
cout << " Sorted Data is " << endl;
for (int i=0; i<n; i++)
cout << a[i] <<" ";
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-366-2048.jpg)
![Using C-string
#include <iostream>
#include <iomanip.h>
using namespace std;
int main(){
char str[] = { 'M','.',' ','A','l','i',0,' ',
'I','I','U',0}; // char ch [] = "M. Ali";
int size = sizeof(str);
cout << "n The Character Array Size is :" <<size
<< " Bytes" << endl;
for ( int i=0 ; i<size ; i++ )
cout << "str[" << i << "]=" <<str[i] <<" =["
<< int(str[i]) << "]" << endl;
cout << endl << str << endl;
system("PAUSE");
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-367-2048.jpg)
![Reading Embedded Blanks
// blanksin.cpp reads string with embedded blanks
#include <iostream>
using namespace std;
int main(){
const int MAX = 80; // max characters in string
char str[MAX]; // string variable str
cout << "nEnter a string: ";
// cin.get() means a member function get() of the stream
// class of which cin is an object
cin.get(str, MAX); // put string in str
// first argument to get() is the array address where
the
// string being input will be placed.
// The second argument specifies the maximum size of the
// array
cout << "You entered: " << str << endl;
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-368-2048.jpg)
![Copying a String the Hard Way
// strcopy1.cpp
// copies a string using a for loop
#include <iostream>
#include <cstring> //for strlen()
using namespace std;
int main(){ //initialized string
char str1[] = "Oh, Captain, my Captain! "
"our fearful trip is done";
const int MAX = 80; int j; // MAX is size of str2 buffer
char str2[MAX]; //empty string
for( j=0; j<strlen(str1); j++) //copy strlen characters
str2[j] = str1[j]; // from str1 to str2
str2[j] = '0'; //insert NULL at end
cout << str2 << endl; //display str2
system("PAUSE"); return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-369-2048.jpg)
![Copying a String the Easy Way
// strcopy2.cpp
// copies a string using strcpy() function
#include <iostream>
#include <cstring> //for strcpy()
using namespace std;
int main(){
char str1[] = "Tiger, tiger, burning brightn"
"In the forests of the night";
const int MAX = 80; //size of str2 buffer
char str2[MAX]; //empty string
strcpy(str2, str1); //copy str1 to str2
cout << str2 << endl; //display str2
system("PAUSE"); return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-370-2048.jpg)
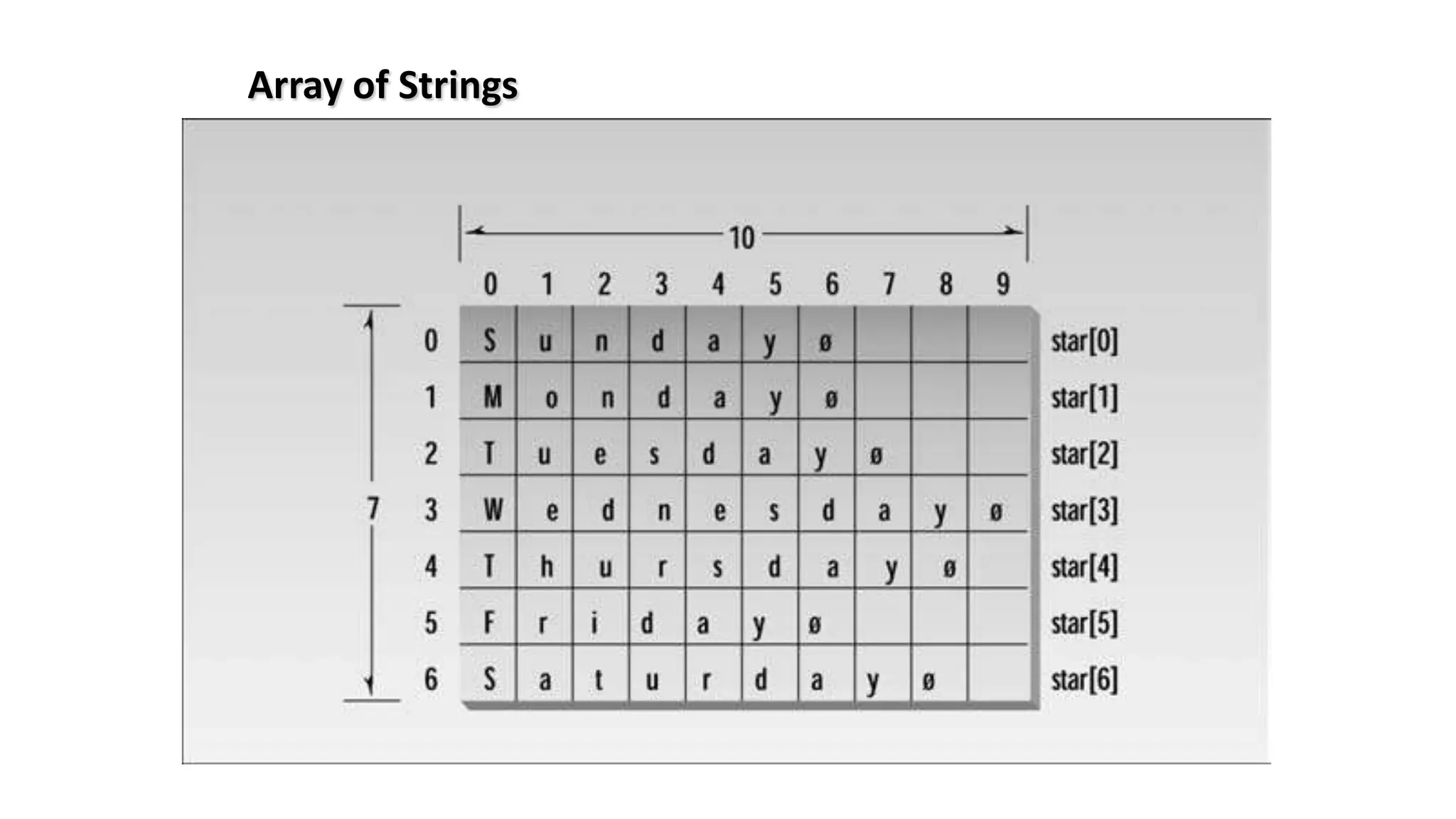
![Array of Strings
// straray.cpp
// array of strings
#include <iostream>
using namespace std;
int main(){
const int DAYS = 7; //number of strings in array
const int MAX = 10; //maximum size of each string
//An array of strings
char star[DAYS][MAX] = { "Sunday", "Monday", "Tuesday",
"Wednesday", "Thursday", "Friday" , "Saturday" };
for( int j=0 ; j<DAYS ; j++) //display every string
cout << star[j] << endl;
system("PAUSE");
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-371-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 376](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-374-2048.jpg)
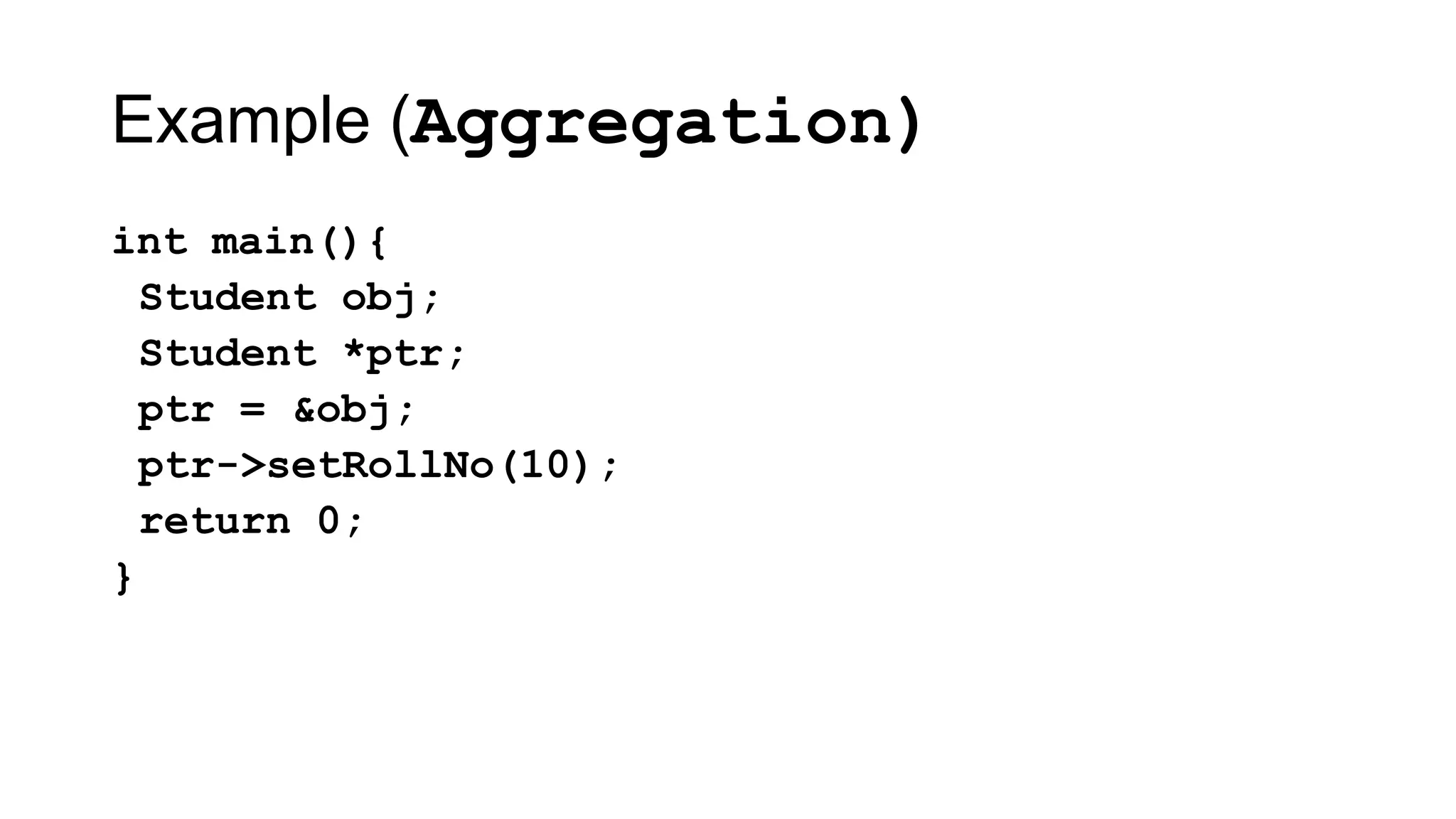
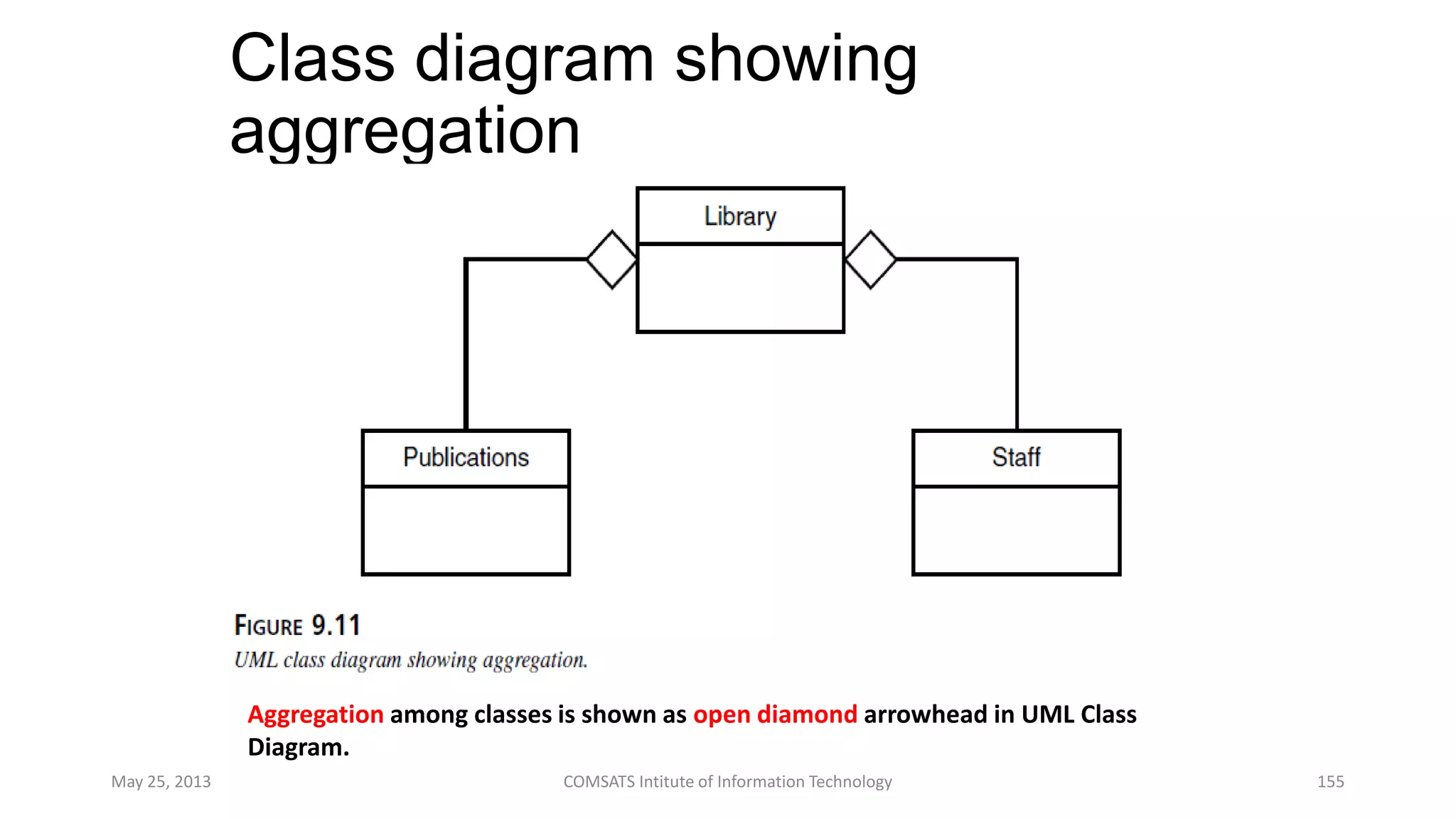
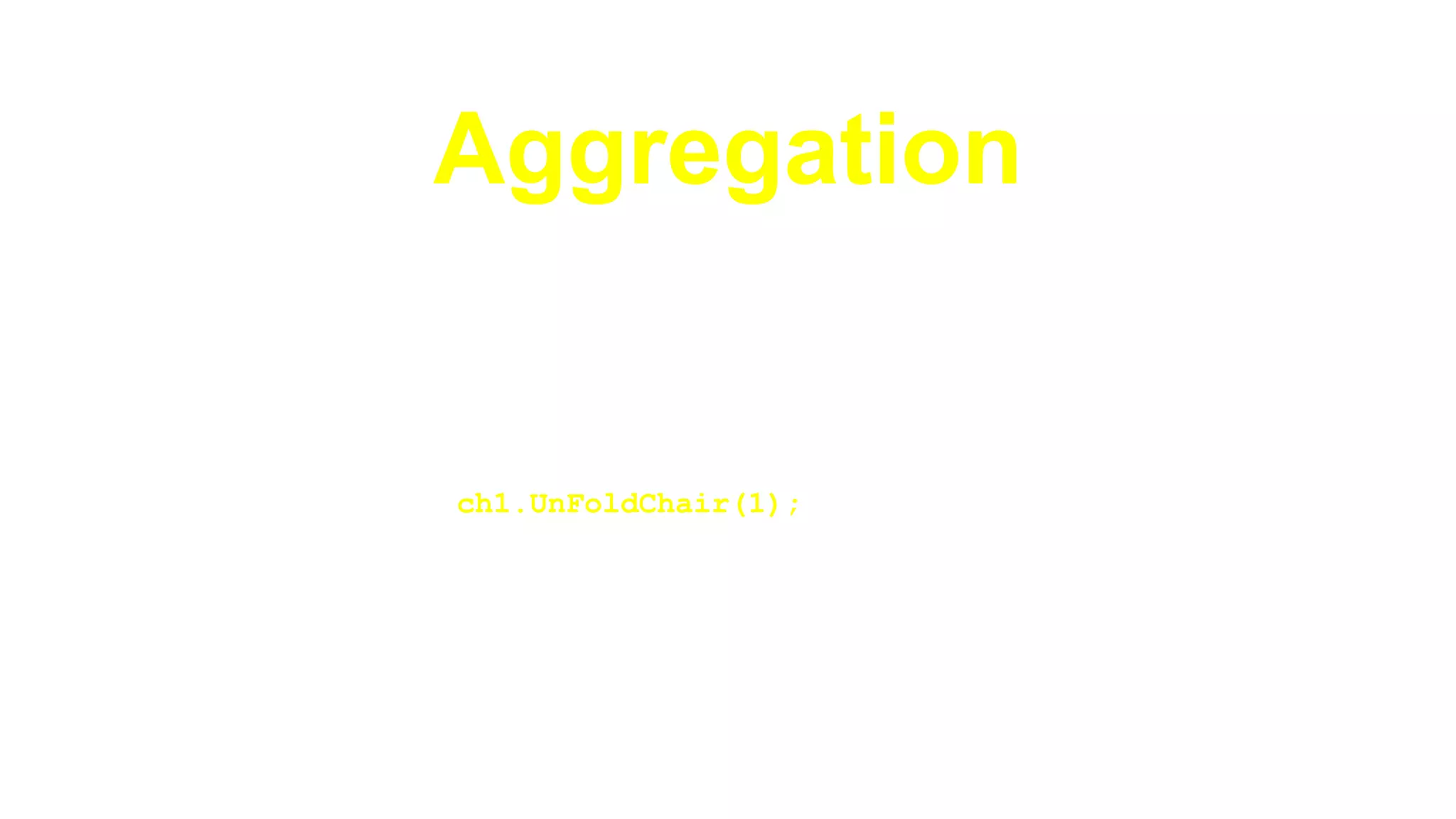
![Aggregation
Composition vs. Aggregation
►Aggregation is a weak relationship
Room(char *, int)
~Room()
FoldChair(int) : bool
…
Chair()
DoSomething() : void
FoldChair() : bool
UnFoldChair() : bool
~Chair()
…
area : float
chairs[50]:Chair *
Room
…
Chair](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-401-2048.jpg)
![Aggregation
class Room{
private:
float area;
Chair * chairs[50];
Public:
Room();
void AddChair(Chair *, int chairNo);
Chair * GetChair(int chairNo);
bool FoldChair(int chairNo);
…
};](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-403-2048.jpg)
![Aggregation
Room::Room(){
for(int i = 0; i < 50; i++)
chairs[i] = NULL;
}
void Room::AddChair(Chair *
chair1, int chairNo){
if(chairNo >= 0 && chairNo < 50)
chairs[chairNo] = chair1;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-404-2048.jpg)
![Aggregation
Chair * Room::GetChair(int chairNo){
if(chairNo >= 0 && chairNo < 50)
return chairs[chairNo];
else
return NULL;
}
bool Room::FoldChair(int chairNo){
if(chairNo >= 0 && chairNo < 50)
return chairs[chairNo]->FoldChair();
else
return false;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-405-2048.jpg)


![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 420](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-418-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 454](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-452-2048.jpg)

![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences ,FAST
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 502](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-500-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences ,FAST
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology 528](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-526-2048.jpg)
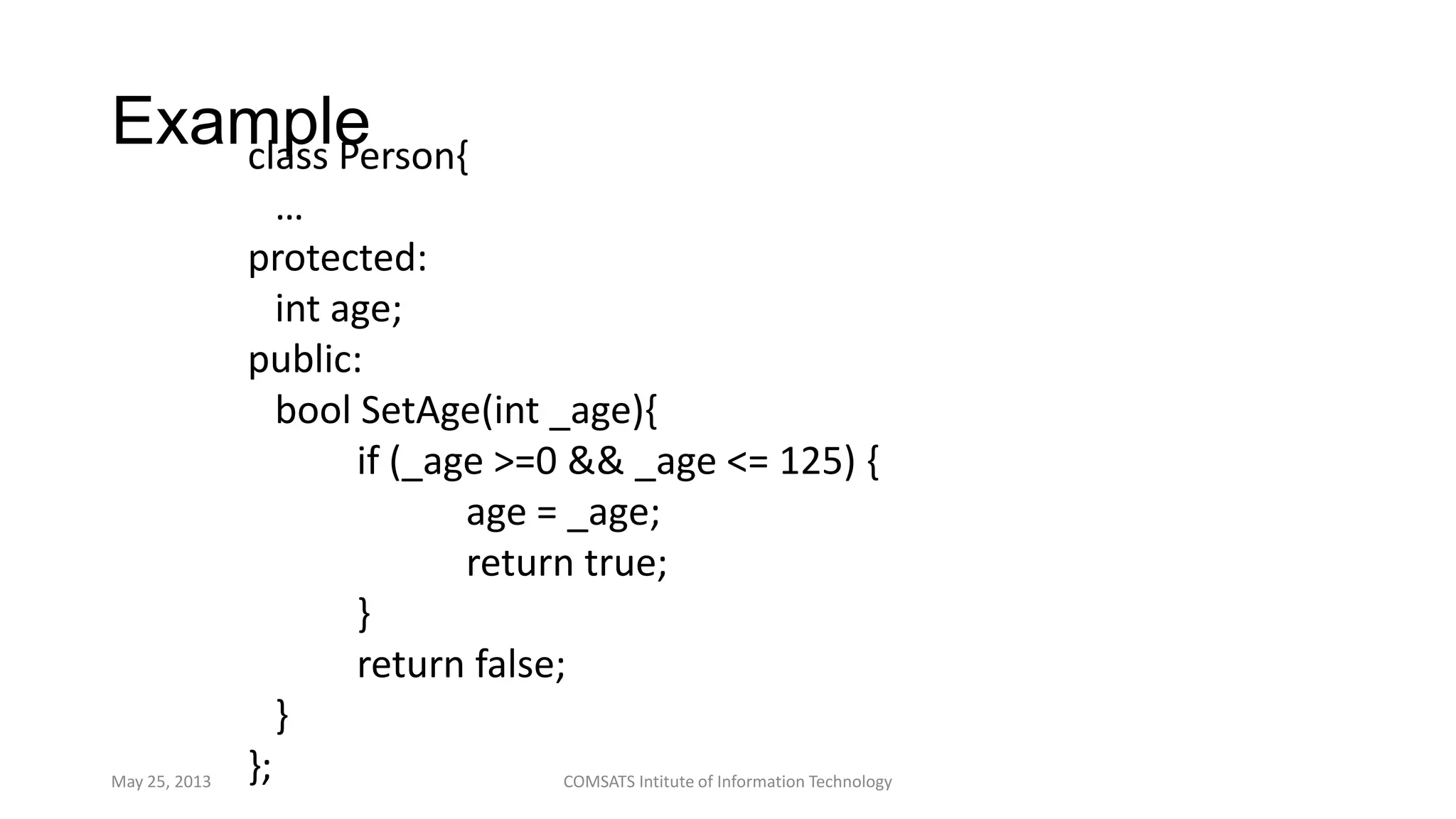
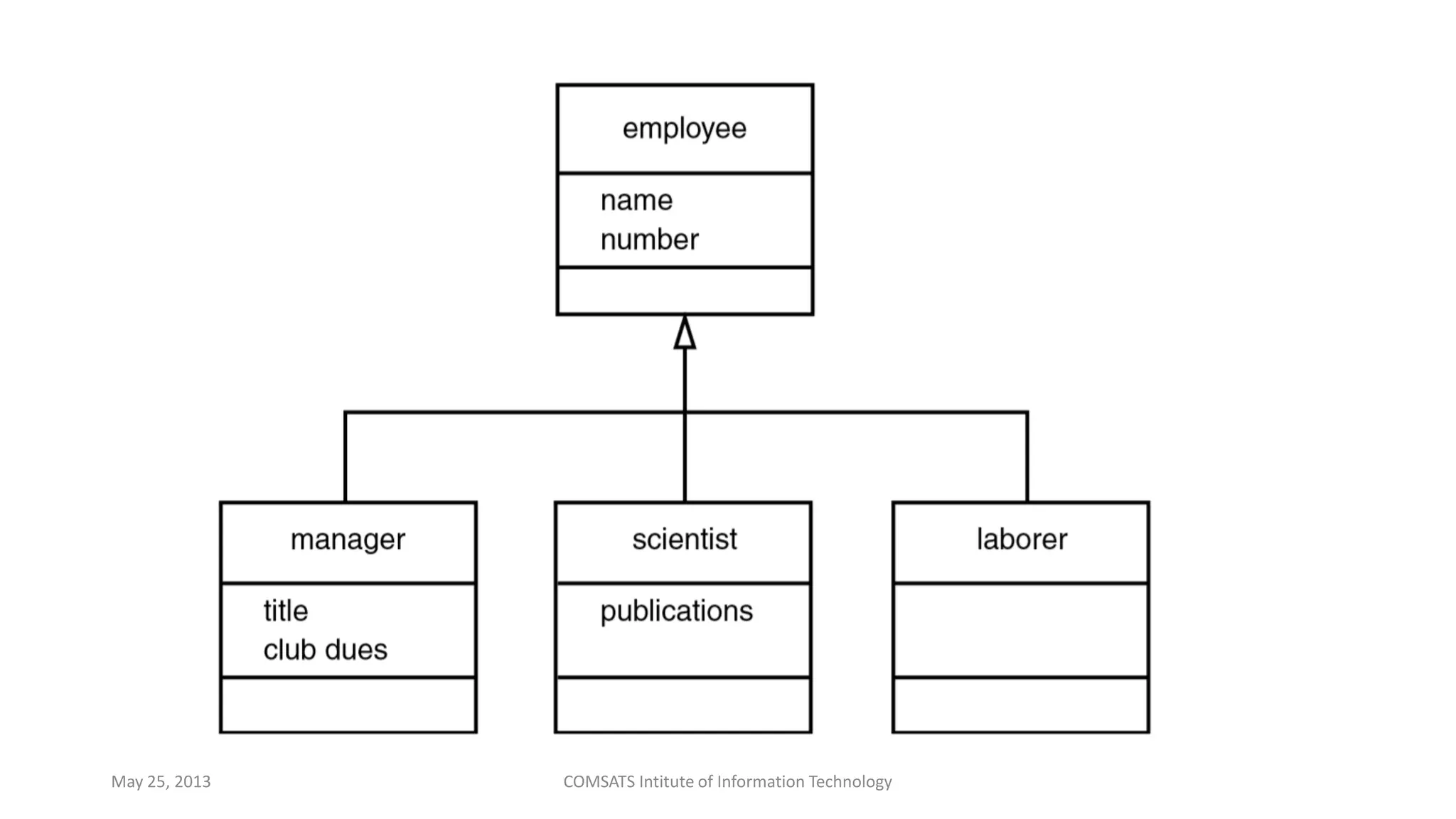
![Example – Specialization
(Restriction)
May25,2013
COMSATSIntituteofInformation
Technology
Person
age : [0..125]
Adult
age : [18..125]
setAge( a )
setAge( a )
age = a
If age < 18 then
error
else
age = a](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-537-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences ,FAST
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Intitute of Information Technology](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-546-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences ,FAST
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Institute of Information Technology 607](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-603-2048.jpg)
![Motivation
• Following function prints an array of integer elements:
void printArray(int* array, int size)
{
for ( int i = 0; i < size; i++ )
cout << array[ i ] << “, ”;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-609-2048.jpg)
![...Motivation
• What if we want to print an array of characters?
void printArray(char* array,
int size)
{
for ( int i = 0; i < size; i++ )
cout << array[ i ] << “, ”;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-610-2048.jpg)
![...Motivation
• What if we want to print an array of doubles?
void printArray(double* array,
int size)
{
for ( int i = 0; i < size; i++ )
cout << array[ i ] << “, ”;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-611-2048.jpg)
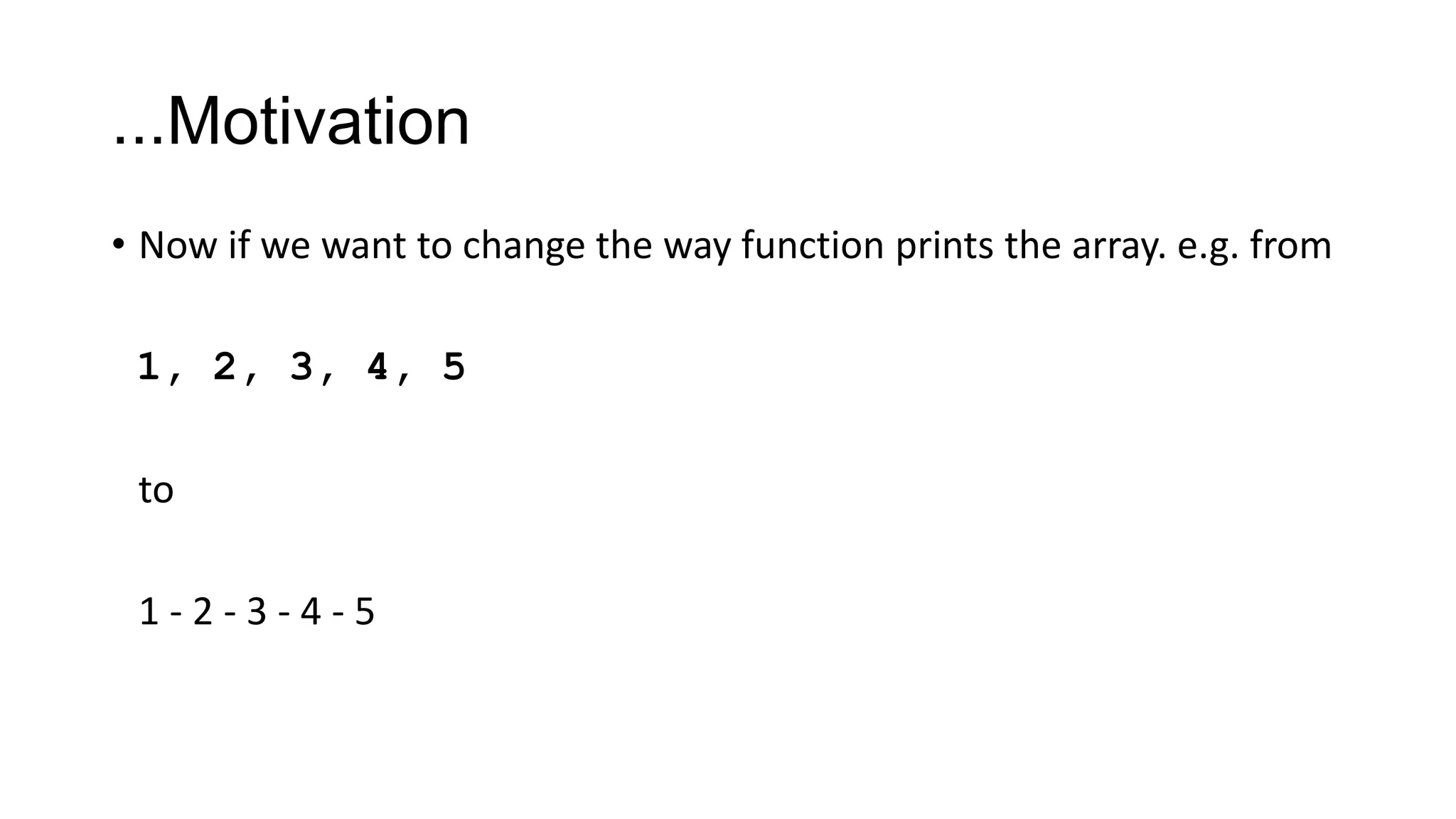

![Example – Function Templates
• Following function template prints an array having almost any type of
elements:
template< typename T >
void printArray( T* array, int size )
{
for ( int i = 0; i < size; i++ )
cout << array[ i ] << “, ”;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-623-2048.jpg)
![…Example – Function Templates
int main() {
int iArray[5] = { 1, 2, 3, 4, 5 };
void printArray( iArray, 5 );
// Instantiated for int[]
char cArray[3] = { „a‟, „b‟, „c‟ };
void printArray( cArray, 3 );
// Instantiated for char[]
return 0;
}](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-624-2048.jpg)
![References
• “Object Oriented Programming in C++”, by “Robert Lafore”, published by Sams Publishing (The
Waite Group). 4th ed. available in soft form.
• “Object Oriented Programming Using C++” by “Joyce Farrell” , published by Course Technology,
Cengage Learning. 4th ed. available in soft form
• National University of Computer & Emerging Sciences ,FAST
[www.nu.edu.pk]
• Virtual University of Pakistan [ocw.vu.edu.pk]
• Open Courseware Consortium
[http://www.ocwconsortium.org/en/courses]
May 25, 2013 COMSATS Institute of Information Technology 637](https://image.slidesharecdn.com/allin1-130526013151-phpapp01/75/All-in-1-633-2048.jpg)