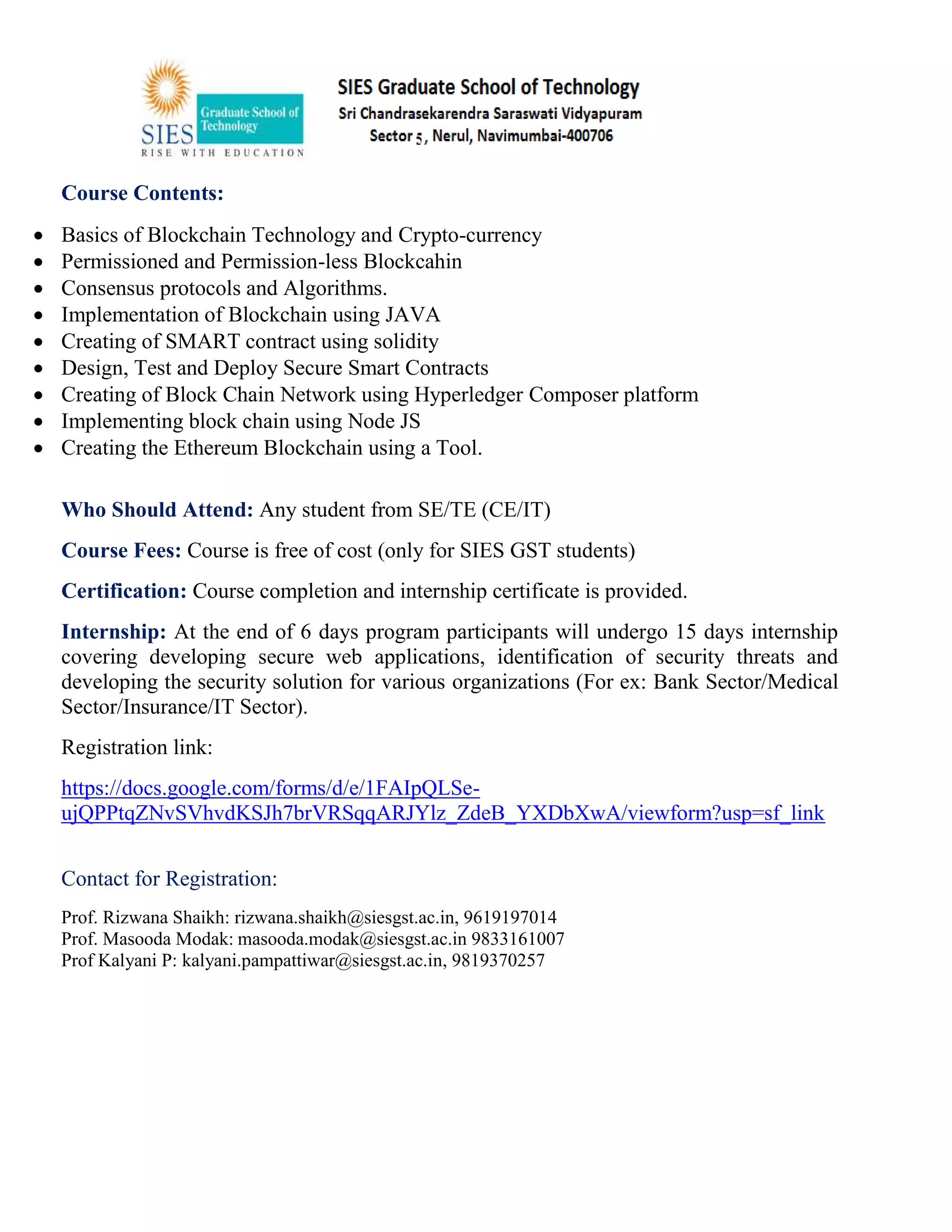
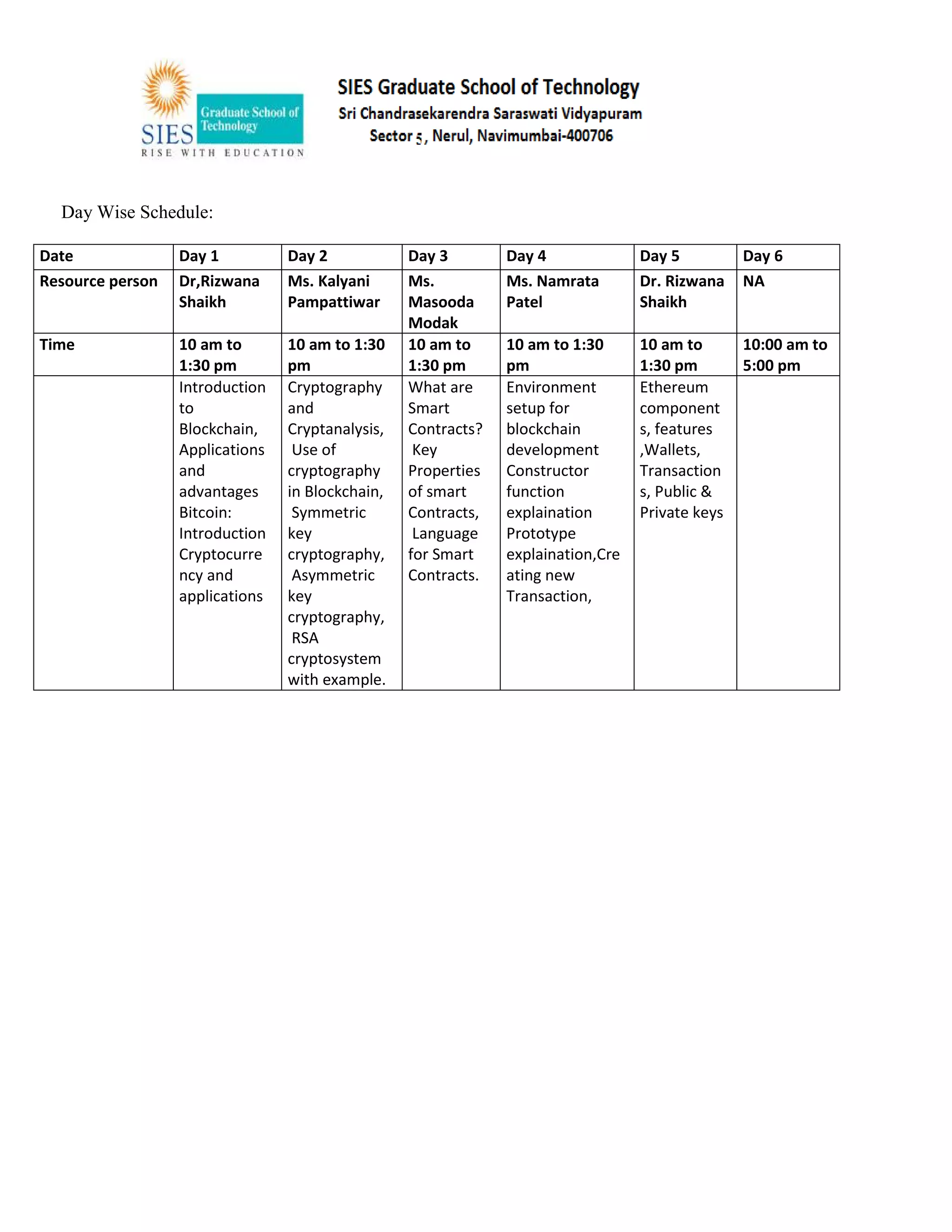
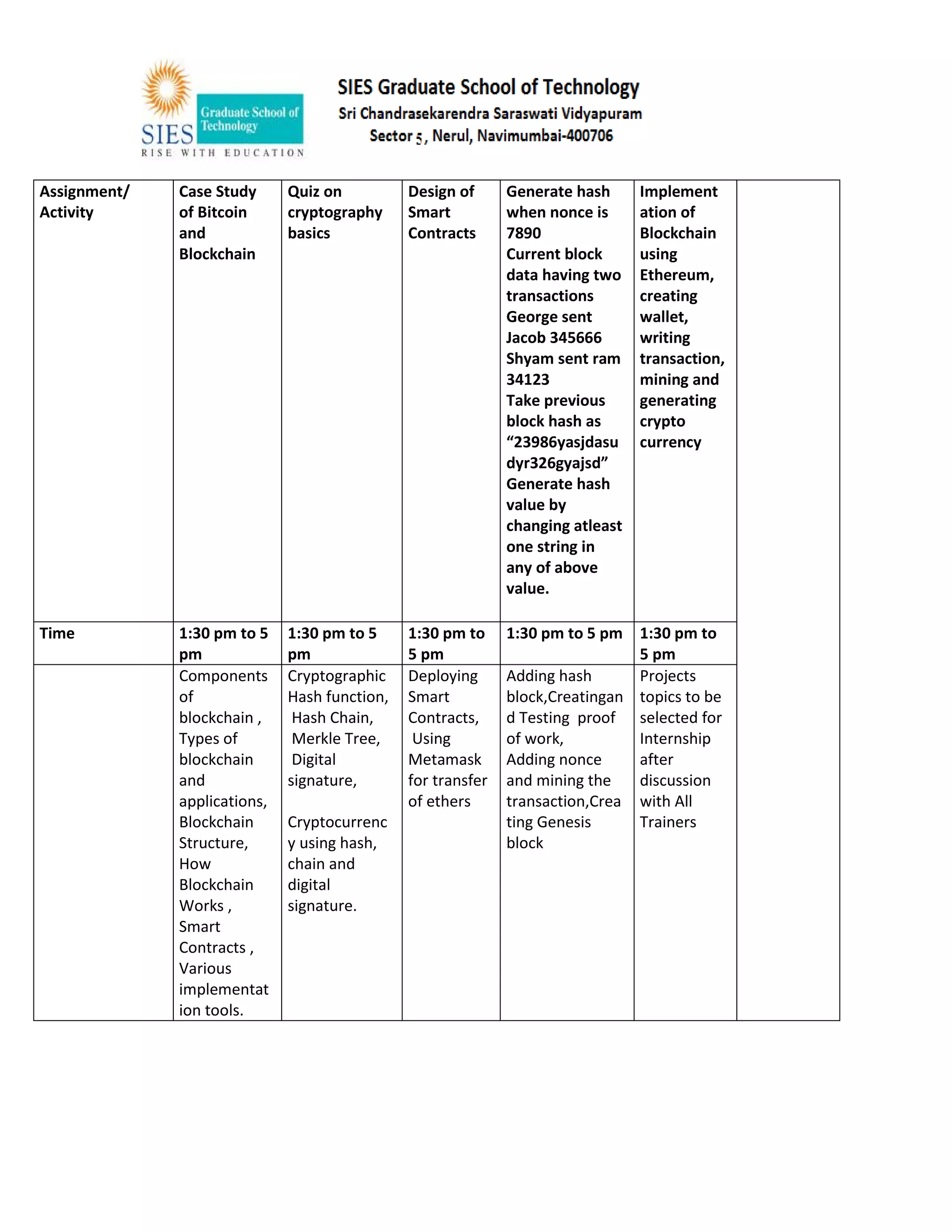
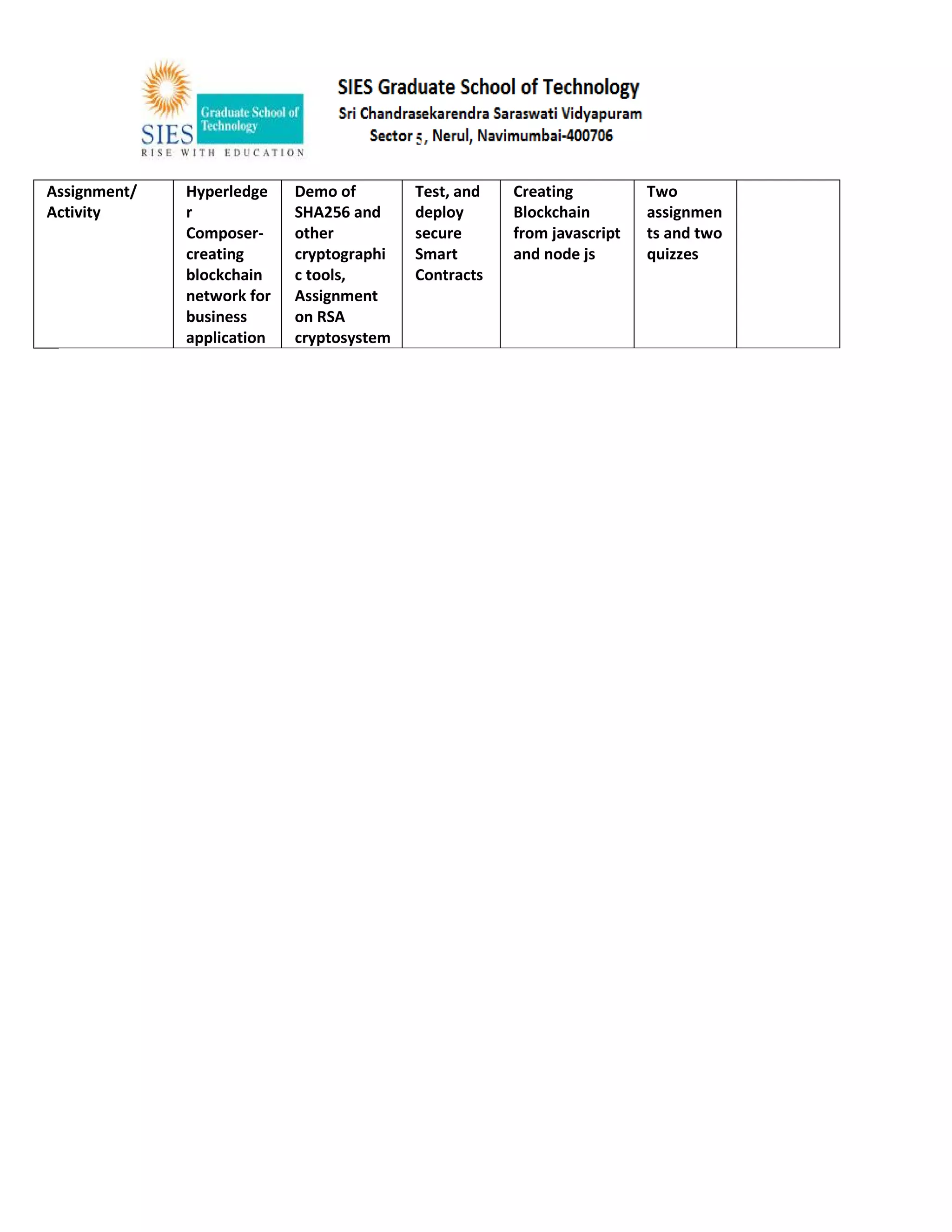
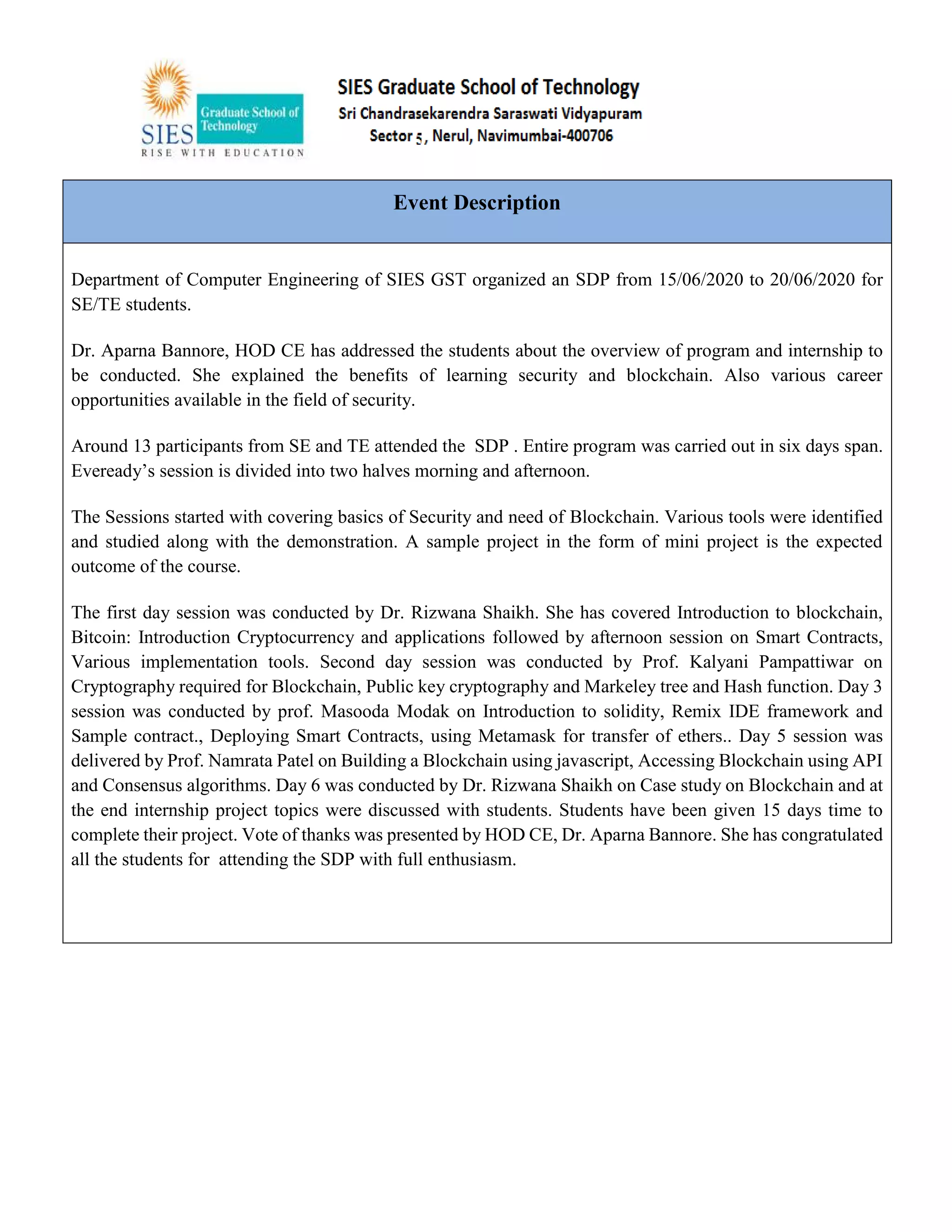
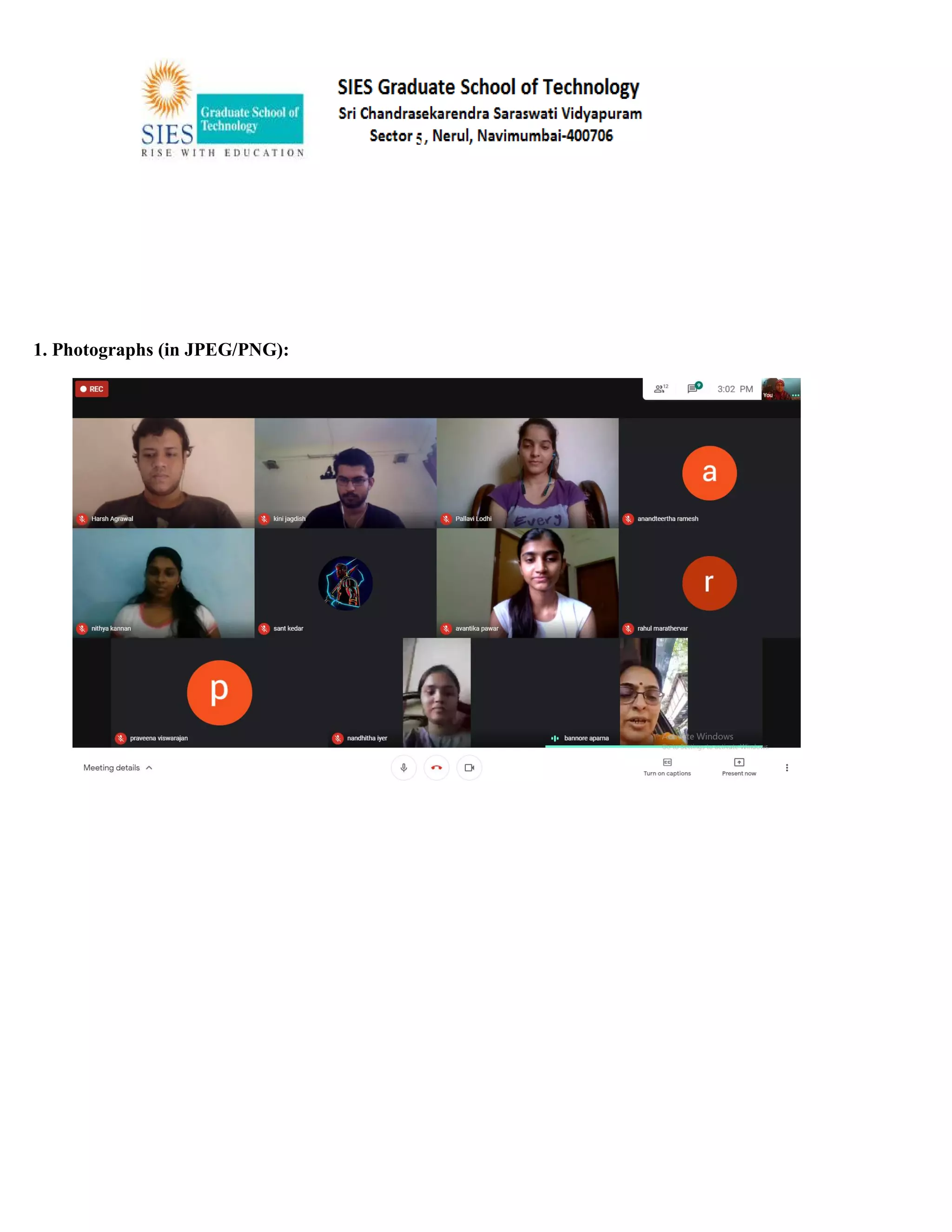
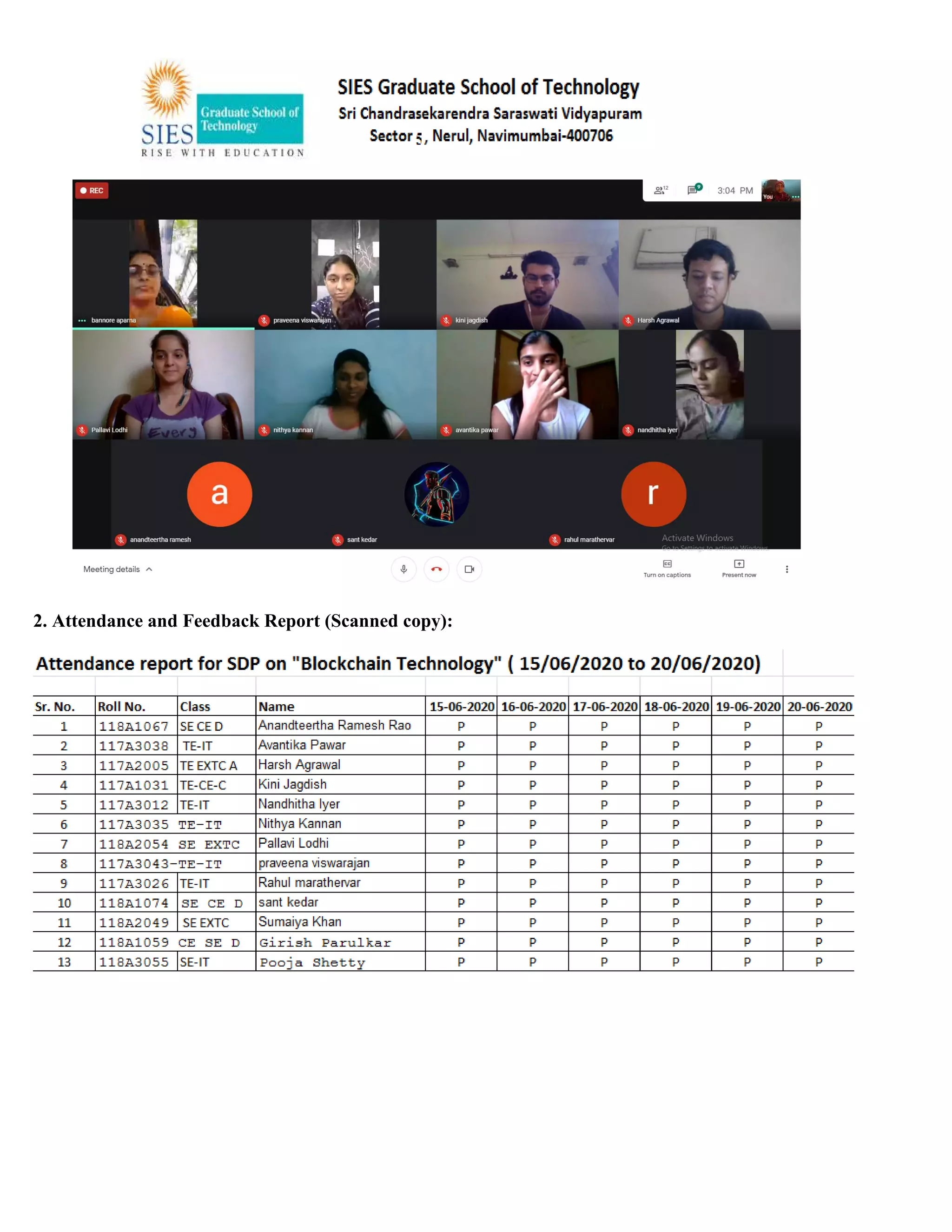
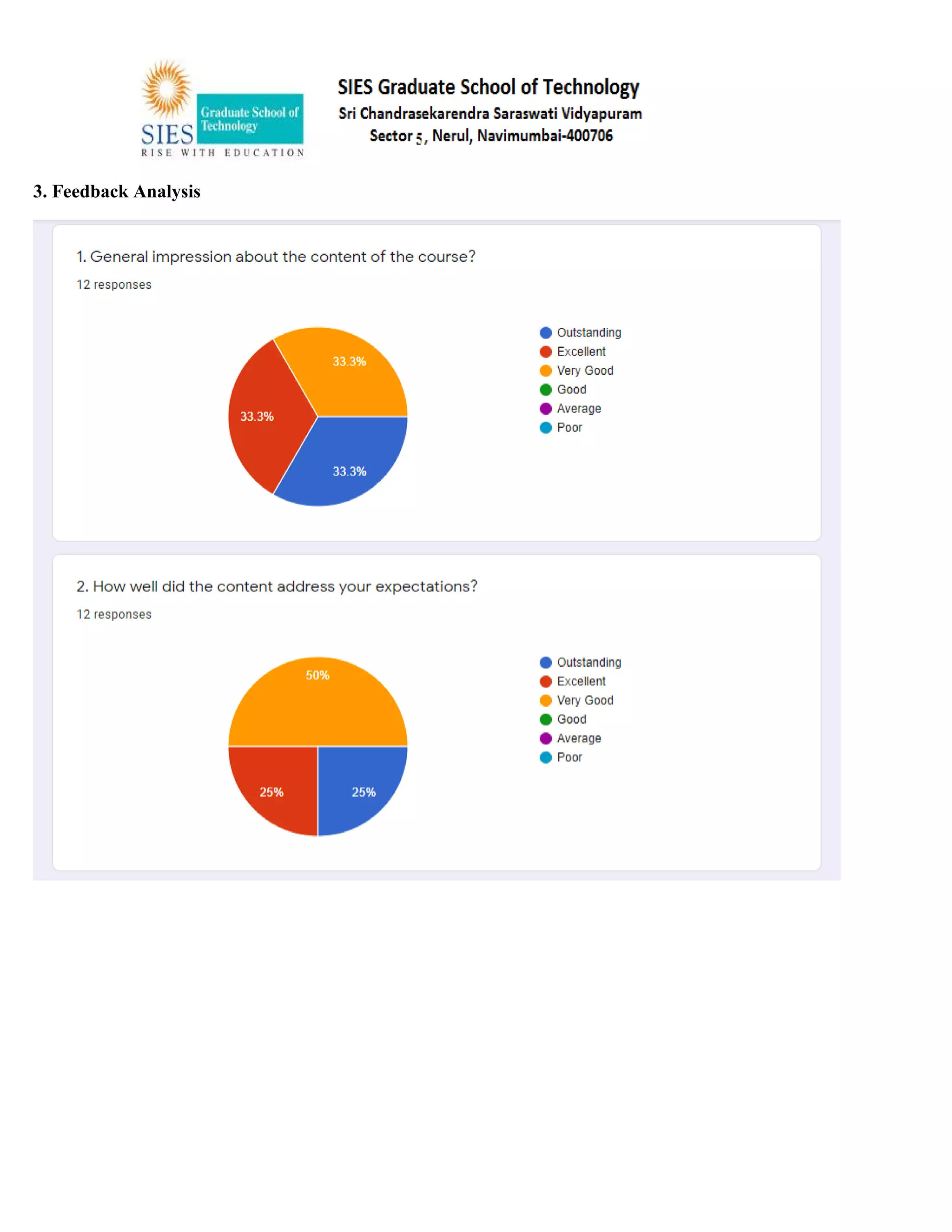
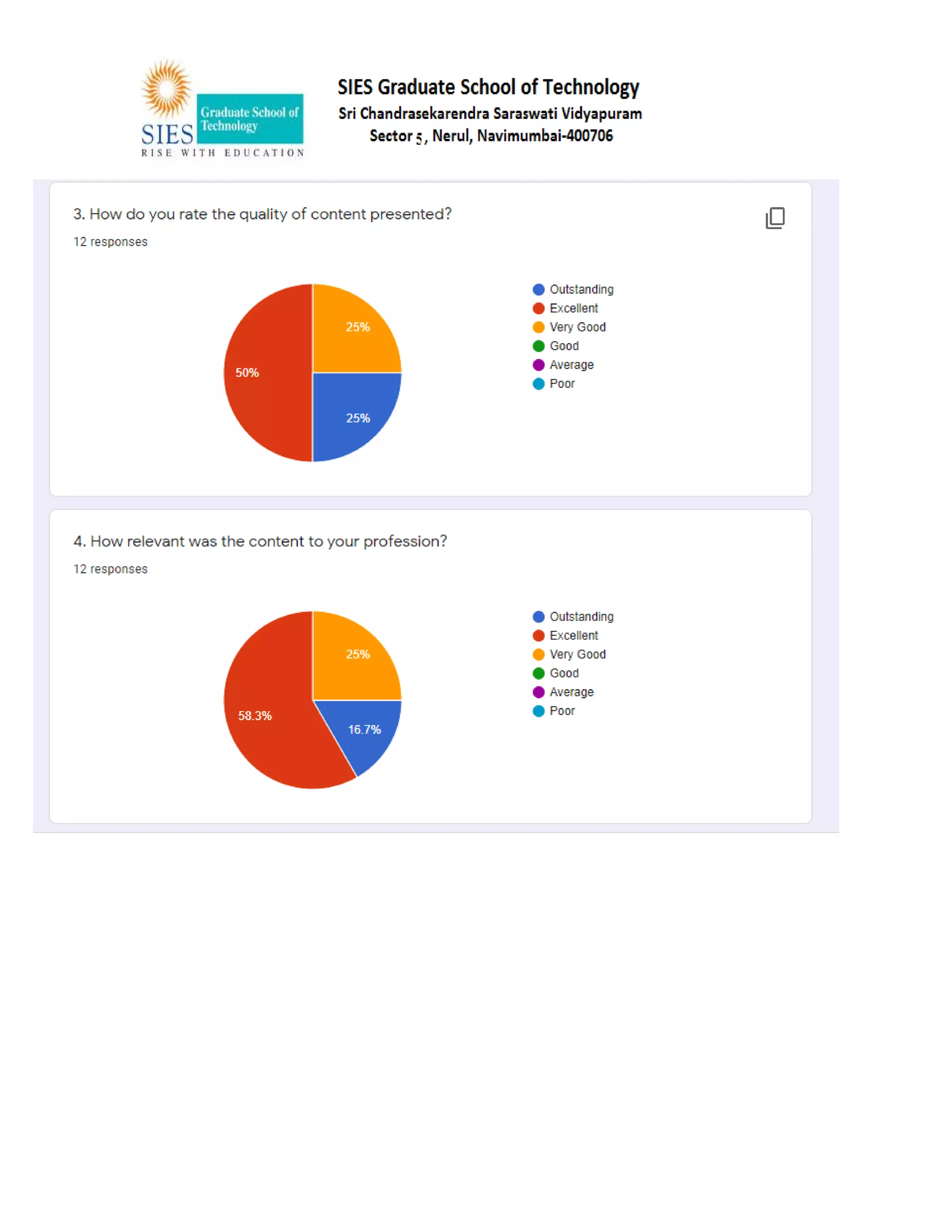
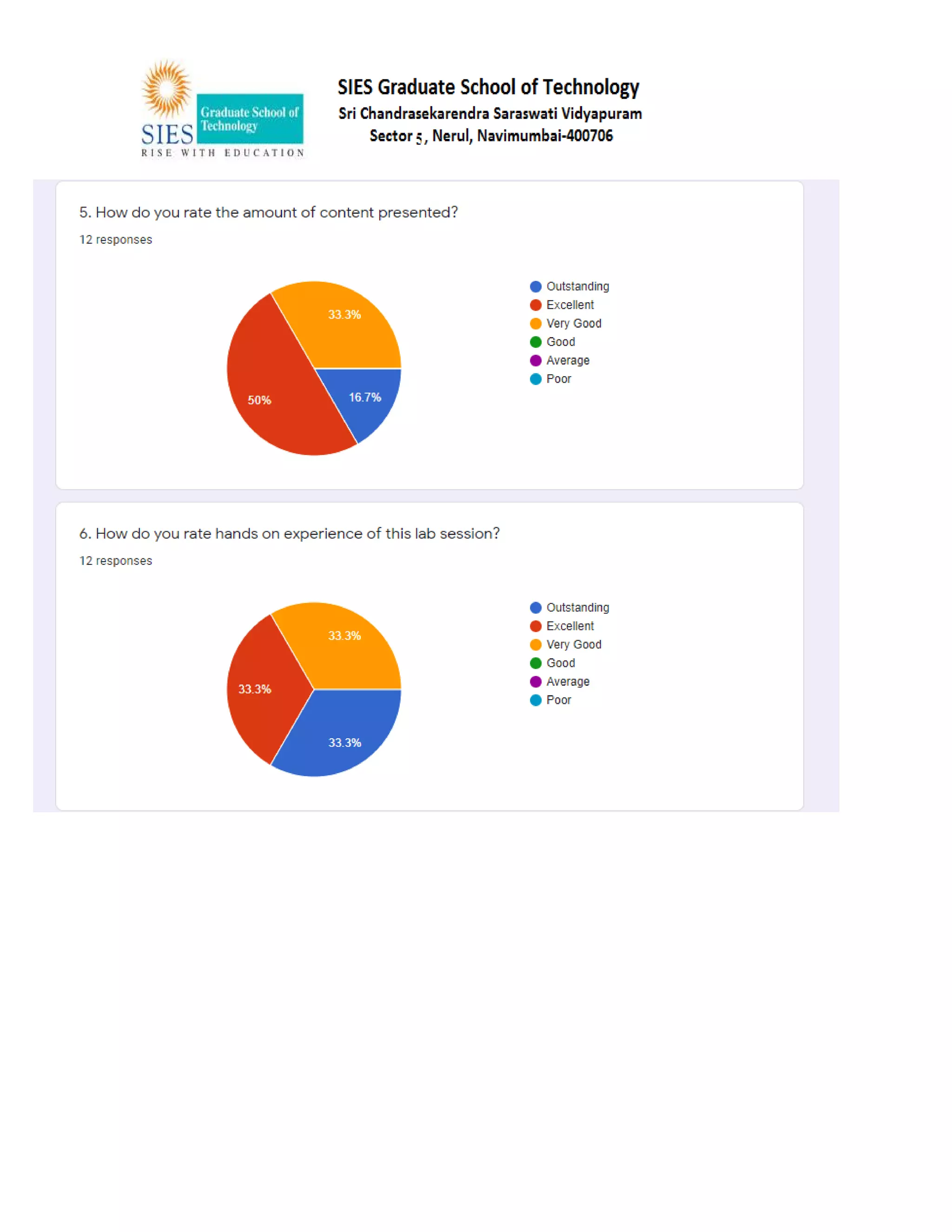
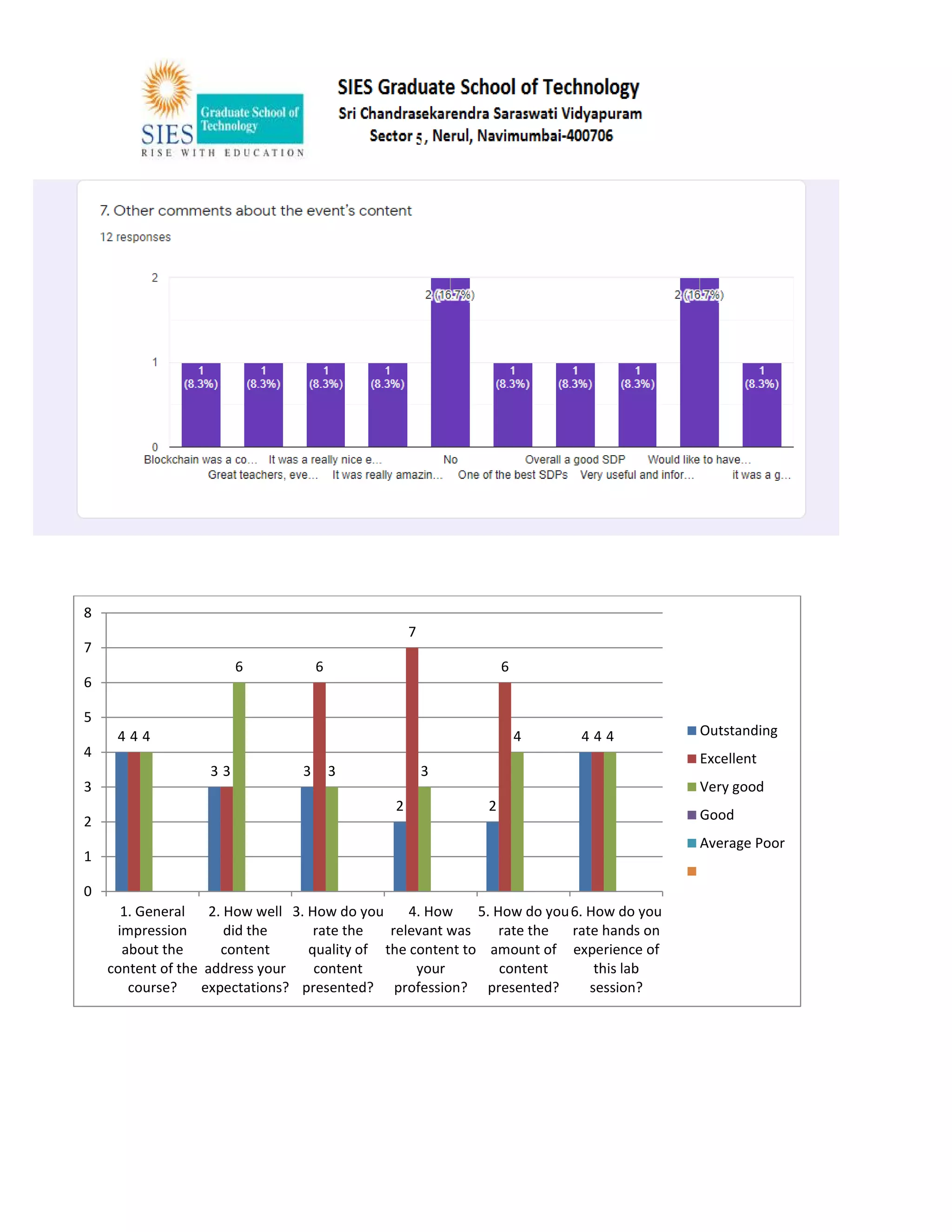
The document describes a 6-day student development program on blockchain technology organized by the Department of Computer Engineering at SIES Graduate School of Technology from June 15-20, 2020. The program provided conceptual and practical training on blockchain concepts, tools, and applications to undergraduate students. Over the six days, students learned about blockchain fundamentals, cryptocurrencies, smart contracts, and blockchain implementation using tools like Hyperledger, Ethereum, and Node.js. Students were assigned practical work and the program concluded with a 15-day internship for students to develop blockchain-based projects.