Android HTML File Vulnerability Report
•
1 like•301 views
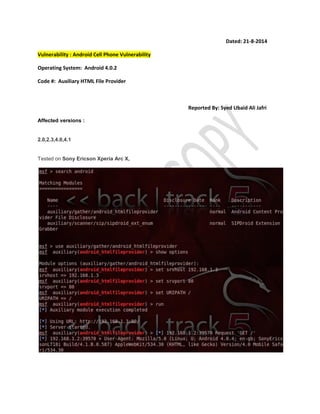
A vulnerability was reported in Android versions 2.0 through 4.1 where an auxiliary HTML file provider could be exploited. The vulnerability was tested on a Sony Ericsson Xperia Arc X phone running Android 4.0.2. A security researcher reported the issue and provided the code number for the vulnerability.
Report
Share
Report
Share
Download to read offline
Recommended
Securing PoS Terminal - A Technical Guideline on Securing PoS System From Hac...

Securing PoS Terminal - A Technical Guideline on Securing PoS System From Hac...Syed Ubaid Ali Jafri
Recommended
Securing PoS Terminal - A Technical Guideline on Securing PoS System From Hac...

Securing PoS Terminal - A Technical Guideline on Securing PoS System From Hac...Syed Ubaid Ali Jafri
More Related Content
More from Syed Ubaid Ali Jafri
More from Syed Ubaid Ali Jafri (14)
Final Year Projects Computer Science (Information security) -2015

Final Year Projects Computer Science (Information security) -2015
Final Year Projects (Computer Science 2013) - Syed Ubaid Ali Jafri

Final Year Projects (Computer Science 2013) - Syed Ubaid Ali Jafri
Syed Ubaid Ali Jafri - Secure IIS Configuration Windows 7

Syed Ubaid Ali Jafri - Secure IIS Configuration Windows 7
Syed Ubaid Ali Jafri - Black Box Penetration testing for Associates

Syed Ubaid Ali Jafri - Black Box Penetration testing for Associates
Syed Ubaid Ali Jafri Lecture on Information Technology 

Syed Ubaid Ali Jafri Lecture on Information Technology
Recently uploaded
Steps To Getting Up And Running Quickly With MyTimeClock Employee Scheduling ...

Steps To Getting Up And Running Quickly With MyTimeClock Employee Scheduling ...MyIntelliSource, Inc.
Try MyIntelliAccount Cloud Accounting Software As A Service Solution Risk Fre...

Try MyIntelliAccount Cloud Accounting Software As A Service Solution Risk Fre...MyIntelliSource, Inc.
Call Girls In Mukherjee Nagar 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SE...

Call Girls In Mukherjee Nagar 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SE...Call Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Recently uploaded (20)
Unveiling Design Patterns: A Visual Guide with UML Diagrams

Unveiling Design Patterns: A Visual Guide with UML Diagrams
Alluxio Monthly Webinar | Cloud-Native Model Training on Distributed Data

Alluxio Monthly Webinar | Cloud-Native Model Training on Distributed Data
(Genuine) Escort Service Lucknow | Starting ₹,5K To @25k with A/C 🧑🏽❤️🧑🏻 89...

(Genuine) Escort Service Lucknow | Starting ₹,5K To @25k with A/C 🧑🏽❤️🧑🏻 89...
Dealing with Cultural Dispersion — Stefano Lambiase — ICSE-SEIS 2024

Dealing with Cultural Dispersion — Stefano Lambiase — ICSE-SEIS 2024
Building a General PDE Solving Framework with Symbolic-Numeric Scientific Mac...

Building a General PDE Solving Framework with Symbolic-Numeric Scientific Mac...
BATTLEFIELD ORM: TIPS, TACTICS AND STRATEGIES FOR CONQUERING YOUR DATABASE

BATTLEFIELD ORM: TIPS, TACTICS AND STRATEGIES FOR CONQUERING YOUR DATABASE
Russian Call Girls in Karol Bagh Aasnvi ➡️ 8264348440 💋📞 Independent Escort S...

Russian Call Girls in Karol Bagh Aasnvi ➡️ 8264348440 💋📞 Independent Escort S...
Advancing Engineering with AI through the Next Generation of Strategic Projec...

Advancing Engineering with AI through the Next Generation of Strategic Projec...
Steps To Getting Up And Running Quickly With MyTimeClock Employee Scheduling ...

Steps To Getting Up And Running Quickly With MyTimeClock Employee Scheduling ...
Try MyIntelliAccount Cloud Accounting Software As A Service Solution Risk Fre...

Try MyIntelliAccount Cloud Accounting Software As A Service Solution Risk Fre...
Adobe Marketo Engage Deep Dives: Using Webhooks to Transfer Data

Adobe Marketo Engage Deep Dives: Using Webhooks to Transfer Data
Call Girls In Mukherjee Nagar 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SE...

Call Girls In Mukherjee Nagar 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SE...
Android HTML File Vulnerability Report
- 1. Dated: 21-8-2014 Vulnerability : Android Cell Phone Vulnerability Operating System: Android 4.0.2 Code #: Auxiliary HTML File Provider Reported By: Syed Ubaid Ali Jafri Affected versions : 2.0,2.3,4.0,4.1 Tested on Sony Ericson Xperia Arc X,
