NIST SP 800-53 Revision 5 Controls Metadata
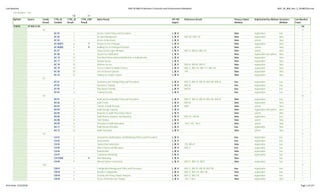
- 1. Low Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Low Baseline true 136 14 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Low Baseline Count 7/18/18 SP 800-53 R5 136 AC 13 AC-01 1 Access Control Policy and Procedures L, M, H false organization true 1 AC-02 2 Account Management L, M, H 800-162, 800-178 false organization false 1 AC-03 3 Access Enforcement L, M, H false system false 1 AC-06(07) 6 7 Review of User Privileges L, M, H false organization false 1 AC-06(09) 6 9 Auditing Use of Privileged Functions L, M, H false system false 1 AC-07 7 Unsuccessful Logon Attempts L, M, H 800-12, 800-63, 800-124 false system false 1 AC-08 8 System Use Notification L, M, H false organization-and-system false 1 AC-14 14 Permitted Actions without Identification or Authentication L, M, H false organization false 1 AC-17 17 Remote Access L, M, H false organization false 1 AC-18 18 Wireless Access L, M, H 800-94, 800-48, 800-97 false organization false 1 AC-19 19 Access Control for Mobile Devices L, M, H 800-12, 800-124, 800-114, 800-164 false organization false 1 AC-20 20 Use of External Systems L, M, H 199 false organization false 1 AC-22 22 Publicly Accessible Content L, M, H false organization false 1 AT 4 AT-01 1 Awareness and Training Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-50 true organization true 1 AT-02 2 Awareness Training L, M, H 800-50 true organization true 1 AT-03 3 Role-Based Training L, M, H 800-50 true organization true 1 AT-04 4 Training Records L, M, H true organization true 1 AU 10 AU-01 1 Audit and Accountability Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-50 false organization true 1 AU-02 2 Audit Events L, M, H 800-92 false organization false 1 AU-03 3 Content of Audit Records L, M, H 8062 false system false 1 AU-04 4 Audit Storage Capacity L, M, H false organization-and-system false 1 AU-05 5 Response to Audit Processing Failures L, M, H false system false 1 AU-06 6 Audit Review, Analysis, and Reporting L, M, H 800-101, 800-86 false organization true 1 AU-08 8 Time Stamps L, M, H false system false 1 AU-09 9 Protection of Audit Information L, M, H 140-2, 202, 180-4 false system false 1 AU-11 11 Audit Record Retention L, M, H true organization false 1 AU-12 12 Audit Generation L, M, H false system false 1 CA 8 CA-01 1 Assessment, Authorization, and Monitoring Policies and Procedures L, M, H true organization true 1 CA-02 2 Assessments L, M, H true organization true 1 CA-03 3 System Interconnections L, M, H 199, 800-47 false organization true 1 CA-05 5 Plan of Action and Milestones L, M, H 800-37 true organization true 1 CA-06 6 Authorization L, M, H false organization true 1 CA-07 7 Continuous Monitoring L, M, H true organization true 1 CA-07(04) 7 4 Risk Monitoring L, M, H false ~ true 1 CA-09 9 Internal System Connections L, M, H 800-12, 800-124, 8023 false organization true 1 CM 9 CM-01 1 Configuration Management Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 true organization true 1 CM-02 2 Baseline Configuration L, M, H 800-12, 800-124, 800-128 false organization true 1 CM-04 4 Security and Privacy Impact Analyses L, M, H 800-12, 800-128 true organization true 1 CM-05 5 Access Restrictions for Change L, M, H 140-2, 186-4 false organization false 1 Print Date: 7/23/2018 Page 1 of 127
- 2. Low Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Low Baseline true 136 14 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Low Baseline Count 7/18/18 SP 800-53 R5 136 CM-06 6 Configuration Settings L, M, H false organization false 1 CM-07 7 Least Functionality L, M, H 140-2, 186-4, 202, 180-4 false organization false 1 CM-08 8 System Component Inventory L, M, H false organization true 1 CM-10 10 Software Usage Restrictions L, M, H false organization false 1 CM-11 11 User-Installed Software L, M, H false organization false 1 CP 6 CP-01 1 Contingency Planning Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-34 true organization true 1 CP-02 2 Contingency Plan L, M, H 800-34, 8179 true organization false 1 CP-03 3 Contingency Training L, M, H 800-50 true organization true 1 CP-04 4 Contingency Plan Testing L, M, H 199, 800-34, 800-84 true organization true 1 CP-09 9 System Backup L, M, H 140-2, 186-4, 800-34, 800-130 false organization false 1 CP-10 10 System Recovery and Reconstitution L, M, H 800-34 false organization false 1 IA 16 IA-01 1 Identification and Authentication Policy and Procedures L, M, H true organization true 1 IA-02 2 Identification and Authentication (Organizational Users) L, M, H false organization-and-system false 1 IA-02(01) 2 1 Multifactor Authentication to Privileged Accounts L, M, H false system false 1 IA-02(02) 2 2 Multifactor Authentication to Non-Privileged Accounts L, M, H false system false 1 IA-02(08) 2 8 Access to Accounts — Replay Resistant L, M, H false system false 1 IA-02(12) 2 12 Acceptance of Piv Credentials L, M, H false system false 1 IA-04 4 Identifier Management L, M, H 201, 800-63, 800-73, 800-76 false organization false 1 IA-05 5 Authenticator Management L, M, H false organization false 1 IA-05(01) 5 1 Password-Based Authentication L, M, H false organization-and-system false 1 IA-06 6 Authenticator Feedback L, M, H false system false 1 IA-07 7 Cryptographic Module Authentication L, M, H 140-2 false system false 1 IA-08 8 Identification and Authentication (Non-Organizational Users) L, M, H false system false 1 IA-08(01) 8 1 Acceptance of Piv Credentials From Other Agencies L, M, H false system false 1 IA-08(02) 8 2 Acceptance of External Party Credentials L, M, H false system false 1 IA-08(04) 8 4 Use of Nist-Issued Profiles L, M, H false system false 1 IA-11 11 Re-authentication L, M, H false organization-and-system false 1 IR 7 IR-01 1 Incident Response Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-61, 800-83 true organization true 1 IR-02 2 Incident Response Training L, M, H 800-50 true organization true 1 IR-04 4 Incident Handling L, M, H 800-61, 800-101, 800-86 true organization false 1 IR-05 5 Incident Monitoring L, M, H 800-61 true organization true 1 IR-06 6 Incident Reporting L, M, H 800-61 true organization false 1 IR-07 7 Incident Response Assistance L, M, H 7559 true organization false 1 IR-08 8 Incident Response Plan L, M, H 800-61 true organization false 1 MA 4 MA-01 1 System Maintenance Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 MA-02 2 Controlled Maintenance L, M, H 8023 false organization false 1 MA-04 4 Nonlocal Maintenance L, M, H 140-2, 201, 800-63, 197 false organization false 1 MA-05 5 Maintenance Personnel L, M, H false organization false 1 MP 4 MP-01 1 Media Protection Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 Print Date: 7/23/2018 Page 2 of 127
- 3. Low Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Low Baseline true 136 14 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Low Baseline Count 7/18/18 SP 800-53 R5 136 MP-02 2 Media Access L, M, H 199, 800-111 false organization false 1 MP-06 6 Media Sanitization L, M, H false organization false 1 MP-07 7 Media Use L, M, H 199, 800-111 false organization false 1 PE 10 PE-01 1 Physical and Environmental Protection Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 PE-02 2 Physical Access Authorizations L, M, H 201, 800-73, 800-78, 800-76 false organization false 1 PE-03 3 Physical Access Control L, M, H 201, 800-73, 800-78, 800-76 false organization false 1 PE-06 6 Monitoring Physical Access L, M, H false organization true 1 PE-08 8 Visitor Access Records L, M, H false organization true 1 PE-12 12 Emergency Lighting L, M, H false organization false 1 PE-13 13 Fire Protection L, M, H false organization false 1 PE-14 14 Temperature and Humidity Controls L, M, H false organization false 1 PE-15 15 Water Damage Protection L, M, H false organization false 1 PE-16 16 Delivery and Removal L, M, H false organization false 1 PL 6 PL-01 1 Planning Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-18 true organization true 1 PL-02 2 Security and Privacy Plans L, M, H 800-18 true organization true 1 PL-04 4 Rules of Behavior L, M, H 800-18 true organization true 1 PL-04(01) 4 1 Social Media and Networking Restrictions L, M, H false organization true 1 PL-10 10 Baseline Selection L, M, H false organization false 1 PL-11 11 Baseline Tailoring L, M, H false organization false 1 PS 8 PS-01 1 Personnel Security Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 PS-02 2 Position Risk Designation L, M, H 5 C.F.R. 731.106 false organization false 1 PS-03 3 Personnel Screening L, M, H false organization false 1 PS-04 4 Personnel Termination L, M, H false organization false 1 PS-05 5 Personnel Transfer L, M, H false organization false 1 PS-06 6 Access Agreements L, M, H false organization true 1 PS-07 7 External Personnel Security L, M, H 800-35 false organization true 1 PS-08 8 Personnel Sanctions L, M, H false organization false 1 RA 6 RA-01 1 Risk Assessment Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 RA-02 2 Security Categorization L, M, H false organization false 1 RA-03 3 Risk Assessment L, M, H 800-39, 800-30, 800-161 false organization true 1 RA-05 5 Vulnerability Scanning L, M, H false organization true 1 RA-05(02) 5 2 Update by Frequency, Prior to New Scan, or When Identified L, M, H false organization true 1 RA-07 7 Risk Response L, M, H false organization true 1 SA 9 SA-01 1 System and Services Acquisition Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 true organization true 1 SA-02 2 Allocation of Resources L, M, H 800-65 false organization true 1 SA-03 3 System Development Life Cycle L, M, H 800-30, 800-37, 800-64 true organization true 1 SA-04 4 Acquisition Process L, M, H true organization true 1 SA-04(10) 4 10 Use of Approved Piv Products L, M, H false organization true 1 SA-05 5 System Documentation L, M, H false organization true 1 Print Date: 7/23/2018 Page 3 of 127
- 4. Low Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Low Baseline true 136 14 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Low Baseline Count 7/18/18 SP 800-53 R5 136 SA-08 8 Security and Privacy Engineering Principles L, M, H true organization true 1 SA-09 9 External System Services L, M, H 800-161, 800-35 true organization true 1 SA-22 22 Unsupported System Components L, M, H false organization true 1 SC 10 SC-01 1 System and Communications Protection Policy and Procedures L, M, H 800-12, 800-100 true organization true 1 SC-05 5 Denial of Service Protection L, M, H false system false 1 SC-07 7 Boundary Protection L, M, H 199, 800-77, 800-41 false system false 1 SC-12 12 Cryptographic Key Establishment and Management L, M, H false organization-and-system false 1 SC-13 13 Cryptographic Protection L, M, H 140-2 false system false 1 SC-15 15 Collaborative Computing Devices and Applications L, M, H false system false 1 SC-20 20 Secure Name/Address Resolution Service (Authoritative Source) L, M, H 140-2, 186-4, 800-81 false system false 1 SC-21 21 Secure Name/Address Resolution Service (Recursive or Caching Resolver) L, M, H 800-81 false system false 1 SC-22 22 Architecture and Provisioning for Name/Address Resolution Service L, M, H 800-81 false system false 1 SC-39 39 Process Isolation L, M, H false system true 1 SI 6 SI-01 1 System and Information Integrity Policy and Procedures L, M, H 800-12, 800-100 true organization true 1 SI-02 2 Flaw Remediation L, M, H false organization false 1 SI-03 3 Malicious Code Protection L, M, H 800-12, 800-177, 800-83, 800-125B false organization false 1 SI-04 4 System Monitoring L, M, H 800-137, 800-61, 800-83, 800-92, 800-94 false organization-and-system true 1 SI-05 5 Security Alerts, Advisories, and Directives L, M, H 800-40 false organization true 1 SI-12 12 Information Management and Retention L, M, H 800-18, 800-188 true organization false 1 Total 136 Print Date: 7/23/2018 Page 4 of 127
- 5. Moderate Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Moderate Baseline true 282 113 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Moderate Baseline Count 7/18/18 SP 800-53 R5 282 AC 40 AC-01 1 Access Control Policy and Procedures L, M, H false organization true 1 AC-02 2 Account Management L, M, H 800-162, 800-178 false organization false 1 AC-02(01) 2 1 Automated System Account Management M, H false organization false 1 AC-02(02) 2 2 Removal of Temporary and Emergency Accounts M, H false system false 1 AC-02(03) 2 3 Disable Accounts M, H false system false 1 AC-02(04) 2 4 Automated Audit Actions M, H false system false 1 AC-02(05) 2 5 Inactivity Logout M, H false organization-and-system false 1 AC-02(10) 2 10 Shared and Group Account Credential Change M, H false organization false 1 AC-02(13) 2 13 Disable Accounts for High-Risk Individuals M, H false organization false 1 AC-03 3 Access Enforcement L, M, H false system false 1 AC-04 4 Information Flow Enforcement M, H 800-162, 800-178 false system false 1 AC-05 5 Separation of Duties M, H false organization false 1 AC-06 6 Least Privilege M, H false organization false 1 AC-06(01) 6 1 Authorize Access to Security Functions M, H false organization false 1 AC-06(02) 6 2 Non-Privileged Access for Nonsecurity Functions M, H false organization false 1 AC-06(05) 6 5 Privileged Accounts M, H false organization false 1 AC-06(07) 6 7 Review of User Privileges L, M, H false organization false 1 AC-06(09) 6 9 Auditing Use of Privileged Functions L, M, H false system false 1 AC-06(10) 6 10 Prohibit Non-Privileged Users From Executing Privileged Functions M, H false system false 1 AC-07 7 Unsuccessful Logon Attempts L, M, H 800-12, 800-63, 800-124 false system false 1 AC-08 8 System Use Notification L, M, H false organization-and-system false 1 AC-11 11 Device Lock M, H false system false 1 AC-11(01) 11 1 Pattern-Hiding Displays M, H false system false 1 AC-12 12 Session Termination M, H false system false 1 AC-14 14 Permitted Actions without Identification or Authentication L, M, H false organization false 1 AC-17 17 Remote Access L, M, H false organization false 1 AC-17(01) 17 1 Automated Monitoring and Control M, H false system false 1 AC-17(02) 17 2 Protection of Confidentiality and Integrity Using Encryption M, H false system false 1 AC-17(03) 17 3 Managed Access Control Points M, H false system false 1 AC-17(04) 17 4 Privileged Commands and Access M, H false organization false 1 AC-18 18 Wireless Access L, M, H 800-94, 800-48, 800-97 false organization false 1 AC-18(01) 18 1 Authentication and Encryption M, H false system false 1 AC-18(03) 18 3 Disable Wireless Networking M, H false organization-and-system false 1 AC-19 19 Access Control for Mobile Devices L, M, H 800-12, 800-124, 800-114, 800-164 false organization false 1 AC-19(05) 19 5 Full Device and Container-Based Encryption M, H false organization false 1 AC-20 20 Use of External Systems L, M, H 199 false organization false 1 AC-20(01) 20 1 Limits on Authorized Use M, H false organization false 1 AC-20(02) 20 2 Portable Storage Devices M, H false organization false 1 AC-21 21 Information Sharing M, H 8062, 800-150 true organization false 1 AC-22 22 Publicly Accessible Content L, M, H false organization false 1 AT 6 AT-01 1 Awareness and Training Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-50 true organization true 1 AT-02 2 Awareness Training L, M, H 800-50 true organization true 1 AT-02(02) 2 2 Insider Threat M, H false organization true 1 Print Date: 7/23/2018 Page 5 of 127
- 6. Moderate Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Moderate Baseline true 282 113 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Moderate Baseline Count 7/18/18 SP 800-53 R5 282 AT-02(03) 2 3 Social Engineering and Mining M, H false organization true 1 AT-03 3 Role-Based Training L, M, H 800-50 true organization true 1 AT-04 4 Training Records L, M, H true organization true 1 AU 18 AU-01 1 Audit and Accountability Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-50 false organization true 1 AU-02 2 Audit Events L, M, H 800-92 false organization false 1 AU-02(03) 2 3 Reviews and Updates M, H false organization false 1 AU-03 3 Content of Audit Records L, M, H 8062 false system false 1 AU-03(01) 3 1 Additional Audit Information M, H false system false 1 AU-04 4 Audit Storage Capacity L, M, H false organization-and-system false 1 AU-05 5 Response to Audit Processing Failures L, M, H false system false 1 AU-06 6 Audit Review, Analysis, and Reporting L, M, H 800-101, 800-86 false organization true 1 AU-06(01) 6 1 Automated Process Integration M, H false organization true 1 AU-06(03) 6 3 Correlate Audit Repositories M, H false organization true 1 AU-07 7 Audit Reduction and Report Generation M, H false system true 1 AU-07(01) 7 1 Automatic Processing M, H false system true 1 AU-08 8 Time Stamps L, M, H false system false 1 AU-08(01) 8 1 Synchronization With Authoritative Time Source M, H false system false 1 AU-09 9 Protection of Audit Information L, M, H 140-2, 202, 180-4 false system false 1 AU-09(04) 9 4 Access by Subset of Privileged Users M, H false organization false 1 AU-11 11 Audit Record Retention L, M, H true organization false 1 AU-12 12 Audit Generation L, M, H false system false 1 CA 11 CA-01 1 Assessment, Authorization, and Monitoring Policies and Procedures L, M, H true organization true 1 CA-02 2 Assessments L, M, H true organization true 1 CA-02(01) 2 1 Independent Assessors M, H true organization true 1 CA-03 3 System Interconnections L, M, H 199, 800-47 false organization true 1 CA-03(05) 3 5 Restrictions on External System Connections M, H false organization false 1 CA-05 5 Plan of Action and Milestones L, M, H 800-37 true organization true 1 CA-06 6 Authorization L, M, H false organization true 1 CA-07 7 Continuous Monitoring L, M, H true organization true 1 CA-07(01) 7 1 Independent Assessment M, H true organization true 1 CA-07(04) 7 4 Risk Monitoring L, M, H false ~ true 1 CA-09 9 Internal System Connections L, M, H 800-12, 800-124, 8023 false organization true 1 CM 24 CM-01 1 Configuration Management Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 true organization true 1 CM-02 2 Baseline Configuration L, M, H 800-12, 800-124, 800-128 false organization true 1 CM-02(02) 2 2 Automation Support for Accuracy and Currency M, H false organization true 1 CM-02(03) 2 3 Retention of Previous Configurations M, H false organization true 1 CM-02(07) 2 7 Configure Systems and Components for High-Risk Areas M, H false organization true 1 CM-03 3 Configuration Change Control M, H 800-12, 800-124, 800-128 false organization true 1 CM-03(02) 3 2 Testing, Validation, and Documentation of Changes M, H false organization true 1 CM-03(04) 3 4 Security Representative M, H false organization false 1 CM-04 4 Security and Privacy Impact Analyses L, M, H 800-12, 800-128 true organization true 1 CM-04(02) 4 2 Verification of Security and Privacy Functions M, H true organization true 1 Print Date: 7/23/2018 Page 6 of 127
- 7. Moderate Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Moderate Baseline true 282 113 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Moderate Baseline Count 7/18/18 SP 800-53 R5 282 CM-05 5 Access Restrictions for Change L, M, H 140-2, 186-4 false organization false 1 CM-06 6 Configuration Settings L, M, H false organization false 1 CM-07 7 Least Functionality L, M, H 140-2, 186-4, 202, 180-4 false organization false 1 CM-07(01) 7 1 Periodic Review M, H false organization false 1 CM-07(02) 7 2 Prevent Program Execution M, H false system false 1 CM-07(05) 7 5 Authorized Software — Whitelisting M, H false organization false 1 CM-08 8 System Component Inventory L, M, H false organization true 1 CM-08(01) 8 1 Updates During Installation and Removal M, H false organization true 1 CM-08(03) 8 3 Automated Unauthorized Component Detection M, H false organization true 1 CM-09 9 Configuration Management Plan M, H 800-12, 800-128 false organization false 1 CM-10 10 Software Usage Restrictions L, M, H false organization false 1 CM-11 11 User-Installed Software L, M, H false organization false 1 CM-12 12 Information Location M, H 199, 800-60-2, 800-60-1 true organization true 1 CM-12(01) 12 1 Automated Tools to Support Information Location M, H true organization true 1 CP 23 CP-01 1 Contingency Planning Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-34 true organization true 1 CP-02 2 Contingency Plan L, M, H 800-34, 8179 true organization false 1 CP-02(01) 2 1 Coordinate With Related Plans M, H true organization false 1 CP-02(03) 2 3 Resume Essential Missions and Business Functions M, H true organization false 1 CP-02(08) 2 8 Identify Critical Assets M, H true organization false 1 CP-03 3 Contingency Training L, M, H 800-50 true organization true 1 CP-04 4 Contingency Plan Testing L, M, H 199, 800-34, 800-84 true organization true 1 CP-04(01) 4 1 Coordinate With Related Plans M, H true organization true 1 CP-06 6 Alternate Storage Site M, H 800-34 false organization false 1 CP-06(01) 6 1 Separation From Primary Site M, H false organization false 1 CP-06(03) 6 3 Accessibility M, H false organization false 1 CP-07 7 Alternate Processing Site M, H 800-34 false organization false 1 CP-07(01) 7 1 Separation From Primary Site M, H false organization false 1 CP-07(02) 7 2 Accessibility M, H false organization false 1 CP-07(03) 7 3 Priority of Service M, H false organization false 1 CP-08 8 Telecommunications Services M, H 800-34 false organization false 1 CP-08(01) 8 1 Priority of Service Provisions M, H false organization false 1 CP-08(02) 8 2 Single Points of Failure M, H false organization false 1 CP-09 9 System Backup L, M, H 140-2, 186-4, 800-34, 800-130 false organization false 1 CP-09(01) 9 1 Testing for Reliability and Integrity M, H false organization false 1 CP-09(08) 9 8 Cryptographic Protection M, H false organization false 1 CP-10 10 System Recovery and Reconstitution L, M, H 800-34 false organization false 1 CP-10(02) 10 2 Transaction Recovery M, H false organization false 1 IA 24 IA-01 1 Identification and Authentication Policy and Procedures L, M, H true organization true 1 IA-02 2 Identification and Authentication (Organizational Users) L, M, H false organization-and-system false 1 IA-02(01) 2 1 Multifactor Authentication to Privileged Accounts L, M, H false system false 1 IA-02(02) 2 2 Multifactor Authentication to Non-Privileged Accounts L, M, H false system false 1 IA-02(08) 2 8 Access to Accounts — Replay Resistant L, M, H false system false 1 IA-02(12) 2 12 Acceptance of Piv Credentials L, M, H false system false 1 Print Date: 7/23/2018 Page 7 of 127
- 8. Moderate Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Moderate Baseline true 282 113 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Moderate Baseline Count 7/18/18 SP 800-53 R5 282 IA-03 3 Device Identification and Authentication M, H false system false 1 IA-04 4 Identifier Management L, M, H 201, 800-63, 800-73, 800-76 false organization false 1 IA-04(04) 4 4 Identify User Status M, H true organization false 1 IA-05 5 Authenticator Management L, M, H false organization false 1 IA-05(01) 5 1 Password-Based Authentication L, M, H false organization-and-system false 1 IA-05(02) 5 2 Public Key-Based Authentication M, H false system false 1 IA-05(06) 5 6 Protection of Authenticators M, H false organization false 1 IA-06 6 Authenticator Feedback L, M, H false system false 1 IA-07 7 Cryptographic Module Authentication L, M, H 140-2 false system false 1 IA-08 8 Identification and Authentication (Non-Organizational Users) L, M, H false system false 1 IA-08(01) 8 1 Acceptance of Piv Credentials From Other Agencies L, M, H false system false 1 IA-08(02) 8 2 Acceptance of External Party Credentials L, M, H false system false 1 IA-08(04) 8 4 Use of Nist-Issued Profiles L, M, H false system false 1 IA-11 11 Re-authentication L, M, H false organization-and-system false 1 IA-12 12 Identity Proofing M, H 201, 800-63, 800-63A false organization false 1 IA-12(02) 12 2 Identity Evidence M, H false organization false 1 IA-12(03) 12 3 Identity Evidence Validation and Verification M, H false organization false 1 IA-12(05) 12 5 Address Confirmation M, H false organization false 1 IR 13 IR-01 1 Incident Response Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-61, 800-83 true organization true 1 IR-02 2 Incident Response Training L, M, H 800-50 true organization true 1 IR-03 3 Incident Response Testing M, H 800-115, 800-84 true organization true 1 IR-03(02) 3 2 Coordination With Related Plans M, H true organization true 1 IR-04 4 Incident Handling L, M, H 800-61, 800-101, 800-86 true organization false 1 IR-04(01) 4 1 Automated Incident Handling Processes M, H false organization false 1 IR-05 5 Incident Monitoring L, M, H 800-61 true organization true 1 IR-06 6 Incident Reporting L, M, H 800-61 true organization false 1 IR-06(01) 6 1 Automated Reporting M, H false organization false 1 IR-06(03) 6 3 Supply Chain Coordination M, H false organization false 1 IR-07 7 Incident Response Assistance L, M, H 7559 true organization false 1 IR-07(01) 7 1 Automation Support for Availability of Information and Support M, H false organization false 1 IR-08 8 Incident Response Plan L, M, H 800-61 true organization false 1 MA 9 MA-01 1 System Maintenance Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 MA-02 2 Controlled Maintenance L, M, H 8023 false organization false 1 MA-03 3 Maintenance Tools M, H 800-88 false organization false 1 MA-03(01) 3 1 Inspect Tools M, H false organization false 1 MA-03(02) 3 2 Inspect Media M, H false organization false 1 MA-03(03) 3 3 Prevent Unauthorized Removal M, H false organization false 1 MA-04 4 Nonlocal Maintenance L, M, H 140-2, 201, 800-63, 197 false organization false 1 MA-05 5 Maintenance Personnel L, M, H false organization false 1 MA-06 6 Timely Maintenance M, H false organization false 1 MP 7 MP-01 1 Media Protection Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 MP-02 2 Media Access L, M, H 199, 800-111 false organization false 1 Print Date: 7/23/2018 Page 8 of 127
- 9. Moderate Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Moderate Baseline true 282 113 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Moderate Baseline Count 7/18/18 SP 800-53 R5 282 MP-03 3 Media Marking M, H 199 false organization false 1 MP-04 4 Media Storage M, H false organization false 1 MP-05 5 Media Transport M, H 199, 800-60-2, 800-60-1 false organization false 1 MP-06 6 Media Sanitization L, M, H false organization false 1 MP-07 7 Media Use L, M, H 199, 800-111 false organization false 1 PE 18 PE-01 1 Physical and Environmental Protection Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 PE-02 2 Physical Access Authorizations L, M, H 201, 800-73, 800-78, 800-76 false organization false 1 PE-03 3 Physical Access Control L, M, H 201, 800-73, 800-78, 800-76 false organization false 1 PE-04 4 Access Control for Transmission M, H false organization false 1 PE-05 5 Access Control for Output Devices M, H 8023 false organization false 1 PE-06 6 Monitoring Physical Access L, M, H false organization true 1 PE-06(01) 6 1 Intrusion Alarms and Surveillance Equipment M, H false organization true 1 PE-08 8 Visitor Access Records L, M, H false organization true 1 PE-09 9 Power Equipment and Cabling M, H false organization false 1 PE-10 10 Emergency Shutoff M, H false organization false 1 PE-11 11 Emergency Power M, H false organization false 1 PE-12 12 Emergency Lighting L, M, H false organization false 1 PE-13 13 Fire Protection L, M, H false organization false 1 PE-13(01) 13 1 Detection Devices and Systems M, H false organization false 1 PE-14 14 Temperature and Humidity Controls L, M, H false organization false 1 PE-15 15 Water Damage Protection L, M, H false organization false 1 PE-16 16 Delivery and Removal L, M, H false organization false 1 PE-17 17 Alternate Work Site M, H 800-46 false organization false 1 PL 8 PL-01 1 Planning Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-18 true organization true 1 PL-02 2 Security and Privacy Plans L, M, H 800-18 true organization true 1 PL-02(03) 2 3 Plan and Coordinate With Other Organizational Entities M, H true organization true 1 PL-04 4 Rules of Behavior L, M, H 800-18 true organization true 1 PL-04(01) 4 1 Social Media and Networking Restrictions L, M, H false organization true 1 PL-08 8 Security and Privacy Architectures M, H true organization true 1 PL-10 10 Baseline Selection L, M, H false organization false 1 PL-11 11 Baseline Tailoring L, M, H false organization false 1 PS 8 PS-01 1 Personnel Security Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 PS-02 2 Position Risk Designation L, M, H 5 C.F.R. 731.106 false organization false 1 PS-03 3 Personnel Screening L, M, H false organization false 1 PS-04 4 Personnel Termination L, M, H false organization false 1 PS-05 5 Personnel Transfer L, M, H false organization false 1 PS-06 6 Access Agreements L, M, H false organization true 1 PS-07 7 External Personnel Security L, M, H 800-35 false organization true 1 PS-08 8 Personnel Sanctions L, M, H false organization false 1 RA 9 RA-01 1 Risk Assessment Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 RA-02 2 Security Categorization L, M, H false organization false 1 Print Date: 7/23/2018 Page 9 of 127
- 10. Moderate Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Moderate Baseline true 282 113 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Moderate Baseline Count 7/18/18 SP 800-53 R5 282 RA-03 3 Risk Assessment L, M, H 800-39, 800-30, 800-161 false organization true 1 RA-03(01) 3 1 Supply Chain Risk Assessment M, H false organization false 1 RA-05 5 Vulnerability Scanning L, M, H false organization true 1 RA-05(02) 5 2 Update by Frequency, Prior to New Scan, or When Identified L, M, H false organization true 1 RA-05(05) 5 5 Privileged Access M, H false organization true 1 RA-07 7 Risk Response L, M, H false organization true 1 RA-09 9 Criticality Analysis M, H false organization false 1 SA 18 SA-01 1 System and Services Acquisition Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 true organization true 1 SA-02 2 Allocation of Resources L, M, H 800-65 false organization true 1 SA-03 3 System Development Life Cycle L, M, H 800-30, 800-37, 800-64 true organization true 1 SA-04 4 Acquisition Process L, M, H true organization true 1 SA-04(01) 4 1 Functional Properties of Controls M, H false organization true 1 SA-04(02) 4 2 Design and Implementation Information for Controls M, H false organization true 1 SA-04(09) 4 9 Functions, Ports, Protocols, and Services in Use M, H false organization true 1 SA-04(10) 4 10 Use of Approved Piv Products L, M, H false organization true 1 SA-05 5 System Documentation L, M, H false organization true 1 SA-08 8 Security and Privacy Engineering Principles L, M, H true organization true 1 SA-09 9 External System Services L, M, H 800-161, 800-35 true organization true 1 SA-09(02) 9 2 Identification of Functions, Ports, Protocols, and Services M, H false organization true 1 SA-10 10 Developer Configuration Management M, H 800-12, 140-2, 202, 800-128, 180-4 false organization true 1 SA-11 11 Developer Testing and Evaluation M, H 800-30, 800-53A, 15408, 800-154 true organization true 1 SA-12 12 Supply Chain Risk Management M, H false organization true 1 SA-15 15 Development Process, Standards, and Tools M, H false organization true 1 SA-15(03) 15 3 Criticality Analysis M, H false organization true 1 SA-22 22 Unsupported System Components L, M, H false organization true 1 SC 26 SC-01 1 System and Communications Protection Policy and Procedures L, M, H 800-12, 800-100 true organization true 1 SC-02 2 Application Partitioning M, H false system true 1 SC-04 4 Information in Shared System Resources M, H false system false 1 SC-05 5 Denial of Service Protection L, M, H false system false 1 SC-07 7 Boundary Protection L, M, H 199, 800-77, 800-41 false system false 1 SC-07(03) 7 3 Access Points M, H false system false 1 SC-07(04) 7 4 External Telecommunications Services M, H false organization false 1 SC-07(05) 7 5 Deny by Default — Allow by Exception M, H false system false 1 SC-07(07) 7 7 Prevent Split Tunneling for Remote Devices M, H false system false 1 SC-07(08) 7 8 Route Traffic to Authenticated Proxy Servers M, H false system false 1 SC-08 8 Transmission Confidentiality and Integrity M, H false system false 1 SC-08(01) 8 1 Cryptographic Protection M, H false system false 1 SC-10 10 Network Disconnect M, H false system false 1 SC-12 12 Cryptographic Key Establishment and Management L, M, H false organization-and-system false 1 SC-13 13 Cryptographic Protection L, M, H 140-2 false system false 1 SC-15 15 Collaborative Computing Devices and Applications L, M, H false system false 1 SC-17 17 Public Key Infrastructure Certificates M, H 800-63, 800-57-2, 800-57-1, 800-57-3, 800-32 false organization-and-system false 1 SC-18 18 Mobile Code M, H 800-28 false organization false 1 Print Date: 7/23/2018 Page 10 of 127
- 11. Moderate Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Moderate Baseline true 282 113 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Moderate Baseline Count 7/18/18 SP 800-53 R5 282 SC-19 19 Voice Over Internet Protocol M, H 800-58 false organization false 1 SC-20 20 Secure Name/Address Resolution Service (Authoritative Source) L, M, H 140-2, 186-4, 800-81 false system false 1 SC-21 21 Secure Name/Address Resolution Service (Recursive or Caching Resolver) L, M, H 800-81 false system false 1 SC-22 22 Architecture and Provisioning for Name/Address Resolution Service L, M, H 800-81 false system false 1 SC-23 23 Session Authenticity M, H 800-77, 800-113, 800-52, 800-95 false system false 1 SC-28 28 Protection of Information at Rest M, H false system false 1 SC-28(01) 28 1 Cryptographic Protection M, H false system false 1 SC-39 39 Process Isolation L, M, H false system true 1 SI 20 SI-01 1 System and Information Integrity Policy and Procedures L, M, H 800-12, 800-100 true organization true 1 SI-02 2 Flaw Remediation L, M, H false organization false 1 SI-02(02) 2 2 Automated Flaw Remediation Status M, H false organization false 1 SI-03 3 Malicious Code Protection L, M, H 800-12, 800-177, 800-83, 800-125B false organization false 1 SI-03(01) 3 1 Central Management M, H false organization false 1 SI-04 4 System Monitoring L, M, H 800-137, 800-61, 800-83, 800-92, 800-94 false organization-and-system true 1 SI-04(02) 4 2 Automated Tools and Mechanisms for Real-Time Analysis M, H false system true 1 SI-04(04) 4 4 Inbound and Outbound Communications Traffic M, H false system true 1 SI-04(05) 4 5 System-Generated Alerts M, H false system true 1 SI-05 5 Security Alerts, Advisories, and Directives L, M, H 800-40 false organization true 1 SI-07 7 Software, Firmware, and Information Integrity M, H false organization-and-system true 1 SI-07(01) 7 1 Integrity Checks M, H false system true 1 SI-07(07) 7 7 Integration of Detection and Response M, H false organization true 1 SI-08 8 Spam Protection M, H 800-177, 800-45 false organization false 1 SI-08(01) 8 1 Central Management M, H false organization false 1 SI-08(02) 8 2 Automatic Updates M, H false system false 1 SI-10 10 Information Input Validation M, H 800-167 false system true 1 SI-11 11 Error Handling M, H false system false 1 SI-12 12 Information Management and Retention L, M, H 800-18, 800-188 true organization false 1 SI-16 16 Memory Protection M, H false system true 1 Total 282 Print Date: 7/23/2018 Page 11 of 127
- 12. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 AC 47 AC-01 1 Access Control Policy and Procedures L, M, H false organization true 1 AC-02 2 Account Management L, M, H 800-162, 800-178 false organization false 1 AC-02(01) 2 1 Automated System Account Management M, H false organization false 1 AC-02(02) 2 2 Removal of Temporary and Emergency Accounts M, H false system false 1 AC-02(03) 2 3 Disable Accounts M, H false system false 1 AC-02(04) 2 4 Automated Audit Actions M, H false system false 1 AC-02(05) 2 5 Inactivity Logout M, H false organization-and-system false 1 AC-02(10) 2 10 Shared and Group Account Credential Change M, H false organization false 1 AC-02(11) 2 11 Usage Conditions H false system false 1 AC-02(12) 2 12 Account Monitoring for Atypical Usage H false organization false 1 AC-02(13) 2 13 Disable Accounts for High-Risk Individuals M, H false organization false 1 AC-03 3 Access Enforcement L, M, H false system false 1 AC-04 4 Information Flow Enforcement M, H 800-162, 800-178 false system false 1 AC-04(04) 4 4 Flow Control of Encrypted Information H false system false 1 AC-05 5 Separation of Duties M, H false organization false 1 AC-06 6 Least Privilege M, H false organization false 1 AC-06(01) 6 1 Authorize Access to Security Functions M, H false organization false 1 AC-06(02) 6 2 Non-Privileged Access for Nonsecurity Functions M, H false organization false 1 AC-06(03) 6 3 Network Access to Privileged Commands H false organization false 1 AC-06(05) 6 5 Privileged Accounts M, H false organization false 1 AC-06(07) 6 7 Review of User Privileges L, M, H false organization false 1 AC-06(09) 6 9 Auditing Use of Privileged Functions L, M, H false system false 1 AC-06(10) 6 10 Prohibit Non-Privileged Users From Executing Privileged Functions M, H false system false 1 AC-07 7 Unsuccessful Logon Attempts L, M, H 800-12, 800-63, 800-124 false system false 1 AC-08 8 System Use Notification L, M, H false organization-and-system false 1 AC-10 10 Concurrent Session Control H false system false 1 AC-11 11 Device Lock M, H false system false 1 AC-11(01) 11 1 Pattern-Hiding Displays M, H false system false 1 AC-12 12 Session Termination M, H false system false 1 AC-14 14 Permitted Actions without Identification or Authentication L, M, H false organization false 1 AC-17 17 Remote Access L, M, H false organization false 1 AC-17(01) 17 1 Automated Monitoring and Control M, H false system false 1 AC-17(02) 17 2 Protection of Confidentiality and Integrity Using Encryption M, H false system false 1 AC-17(03) 17 3 Managed Access Control Points M, H false system false 1 AC-17(04) 17 4 Privileged Commands and Access M, H false organization false 1 AC-18 18 Wireless Access L, M, H 800-94, 800-48, 800-97 false organization false 1 AC-18(01) 18 1 Authentication and Encryption M, H false system false 1 AC-18(03) 18 3 Disable Wireless Networking M, H false organization-and-system false 1 AC-18(04) 18 4 Restrict Configurations by Users H false organization false 1 AC-18(05) 18 5 Antennas and Transmission Power Levels H false organization false 1 AC-19 19 Access Control for Mobile Devices L, M, H 800-12, 800-124, 800-114, 800-164 false organization false 1 Print Date: 7/23/2018 Page 12 of 127
- 13. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 AC-19(05) 19 5 Full Device and Container-Based Encryption M, H false organization false 1 AC-20 20 Use of External Systems L, M, H 199 false organization false 1 AC-20(01) 20 1 Limits on Authorized Use M, H false organization false 1 AC-20(02) 20 2 Portable Storage Devices M, H false organization false 1 AC-21 21 Information Sharing M, H 8062, 800-150 true organization false 1 AC-22 22 Publicly Accessible Content L, M, H false organization false 1 AT 6 AT-01 1 Awareness and Training Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-50 true organization true 1 AT-02 2 Awareness Training L, M, H 800-50 true organization true 1 AT-02(02) 2 2 Insider Threat M, H false organization true 1 AT-02(03) 2 3 Social Engineering and Mining M, H false organization true 1 AT-03 3 Role-Based Training L, M, H 800-50 true organization true 1 AT-04 4 Training Records L, M, H true organization true 1 AU 28 AU-01 1 Audit and Accountability Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-50 false organization true 1 AU-02 2 Audit Events L, M, H 800-92 false organization false 1 AU-02(03) 2 3 Reviews and Updates M, H false organization false 1 AU-03 3 Content of Audit Records L, M, H 8062 false system false 1 AU-03(01) 3 1 Additional Audit Information M, H false system false 1 AU-03(02) 3 2 Centralized Management of Planned Audit Record Content H false system false 1 AU-04 4 Audit Storage Capacity L, M, H false organization-and-system false 1 AU-05 5 Response to Audit Processing Failures L, M, H false system false 1 AU-05(01) 5 1 Audit Storage Capacity H false system false 1 AU-05(02) 5 2 Real-Time Alerts H false system false 1 AU-06 6 Audit Review, Analysis, and Reporting L, M, H 800-101, 800-86 false organization true 1 AU-06(01) 6 1 Automated Process Integration M, H false organization true 1 AU-06(03) 6 3 Correlate Audit Repositories M, H false organization true 1 AU-06(05) 6 5 Integrated Analysis of Audit Records H false organization true 1 AU-06(06) 6 6 Correlation With Physical Monitoring H false organization true 1 AU-07 7 Audit Reduction and Report Generation M, H false system true 1 AU-07(01) 7 1 Automatic Processing M, H false system true 1 AU-08 8 Time Stamps L, M, H false system false 1 AU-08(01) 8 1 Synchronization With Authoritative Time Source M, H false system false 1 AU-09 9 Protection of Audit Information L, M, H 140-2, 202, 180-4 false system false 1 AU-09(02) 9 2 Store on Separate Physical Systems or Components H false system false 1 AU-09(03) 9 3 Cryptographic Protection H false system false 1 AU-09(04) 9 4 Access by Subset of Privileged Users M, H false organization false 1 AU-10 10 Non-repudiation H 140-2, 186-4, 202, 180-4 false system true 1 AU-11 11 Audit Record Retention L, M, H true organization false 1 AU-12 12 Audit Generation L, M, H false system false 1 AU-12(01) 12 1 System-Wide and Time-Correlated Audit Trail H false system false 1 AU-12(03) 12 3 Changes by Authorized Individuals H false system false 1 Print Date: 7/23/2018 Page 13 of 127
- 14. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 CA 15 CA-01 1 Assessment, Authorization, and Monitoring Policies and Procedures L, M, H true organization true 1 CA-02 2 Assessments L, M, H true organization true 1 CA-02(01) 2 1 Independent Assessors M, H true organization true 1 CA-02(02) 2 2 Specialized Assessments H false organization true 1 CA-03 3 System Interconnections L, M, H 199, 800-47 false organization true 1 CA-03(05) 3 5 Restrictions on External System Connections M, H false organization false 1 CA-03(06) 3 6 Secondary and Tertiary Connections H false organization false 1 CA-05 5 Plan of Action and Milestones L, M, H 800-37 true organization true 1 CA-06 6 Authorization L, M, H false organization true 1 CA-07 7 Continuous Monitoring L, M, H true organization true 1 CA-07(01) 7 1 Independent Assessment M, H true organization true 1 CA-07(04) 7 4 Risk Monitoring L, M, H false ~ true 1 CA-08 8 Penetration Testing H false organization true 1 CA-08(01) 8 1 Independent Penetration Agent or Team H false organization true 1 CA-09 9 Internal System Connections L, M, H 800-12, 800-124, 8023 false organization true 1 CM 34 CM-01 1 Configuration Management Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 true organization true 1 CM-02 2 Baseline Configuration L, M, H 800-12, 800-124, 800-128 false organization true 1 CM-02(02) 2 2 Automation Support for Accuracy and Currency M, H false organization true 1 CM-02(03) 2 3 Retention of Previous Configurations M, H false organization true 1 CM-02(07) 2 7 Configure Systems and Components for High-Risk Areas M, H false organization true 1 CM-03 3 Configuration Change Control M, H 800-12, 800-124, 800-128 false organization true 1 CM-03(01) 3 1 Automated Documentation, Notification, and Prohibition of Changes H false organization true 1 CM-03(02) 3 2 Testing, Validation, and Documentation of Changes M, H false organization true 1 CM-03(04) 3 4 Security Representative M, H false organization false 1 CM-03(06) 3 6 Cryptography Management H false organization false 1 CM-04 4 Security and Privacy Impact Analyses L, M, H 800-12, 800-128 true organization true 1 CM-04(01) 4 1 Separate Test Environments H false organization true 1 CM-04(02) 4 2 Verification of Security and Privacy Functions M, H true organization true 1 CM-05 5 Access Restrictions for Change L, M, H 140-2, 186-4 false organization false 1 CM-05(01) 5 1 Automated Access Enforcement and Auditing H false system false 1 CM-05(02) 5 2 Review System Changes H false organization false 1 CM-05(03) 5 3 Signed Components H false organization-and-system false 1 CM-06 6 Configuration Settings L, M, H false organization false 1 CM-06(01) 6 1 Automated Management, Application, and Verification H false organization false 1 CM-06(02) 6 2 Respond to Unauthorized Changes H false organization false 1 CM-07 7 Least Functionality L, M, H 140-2, 186-4, 202, 180-4 false organization false 1 CM-07(01) 7 1 Periodic Review M, H false organization false 1 CM-07(02) 7 2 Prevent Program Execution M, H false system false 1 CM-07(05) 7 5 Authorized Software — Whitelisting M, H false organization false 1 CM-08 8 System Component Inventory L, M, H false organization true 1 Print Date: 7/23/2018 Page 14 of 127
- 15. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 CM-08(01) 8 1 Updates During Installation and Removal M, H false organization true 1 CM-08(02) 8 2 Automated Maintenance H false organization true 1 CM-08(03) 8 3 Automated Unauthorized Component Detection M, H false organization true 1 CM-08(04) 8 4 Accountability Information H false organization true 1 CM-09 9 Configuration Management Plan M, H 800-12, 800-128 false organization false 1 CM-10 10 Software Usage Restrictions L, M, H false organization false 1 CM-11 11 User-Installed Software L, M, H false organization false 1 CM-12 12 Information Location M, H 199, 800-60-2, 800-60-1 true organization true 1 CM-12(01) 12 1 Automated Tools to Support Information Location M, H true organization true 1 CP 36 CP-01 1 Contingency Planning Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-34 true organization true 1 CP-02 2 Contingency Plan L, M, H 800-34, 8179 true organization false 1 CP-02(01) 2 1 Coordinate With Related Plans M, H true organization false 1 CP-02(02) 2 2 Capacity Planning H false organization false 1 CP-02(03) 2 3 Resume Essential Missions and Business Functions M, H true organization false 1 CP-02(04) 2 4 Resume All Missions and Business Functions H true organization false 1 CP-02(05) 2 5 Continue Essential Missions and Business Functions H true organization false 1 CP-02(08) 2 8 Identify Critical Assets M, H true organization false 1 CP-03 3 Contingency Training L, M, H 800-50 true organization true 1 CP-03(01) 3 1 Simulated Events H true organization true 1 CP-04 4 Contingency Plan Testing L, M, H 199, 800-34, 800-84 true organization true 1 CP-04(01) 4 1 Coordinate With Related Plans M, H true organization true 1 CP-04(02) 4 2 Alternate Processing Site H false organization true 1 CP-06 6 Alternate Storage Site M, H 800-34 false organization false 1 CP-06(01) 6 1 Separation From Primary Site M, H false organization false 1 CP-06(02) 6 2 Recovery Time and Recovery Point Objectives H false organization false 1 CP-06(03) 6 3 Accessibility M, H false organization false 1 CP-07 7 Alternate Processing Site M, H 800-34 false organization false 1 CP-07(01) 7 1 Separation From Primary Site M, H false organization false 1 CP-07(02) 7 2 Accessibility M, H false organization false 1 CP-07(03) 7 3 Priority of Service M, H false organization false 1 CP-07(04) 7 4 Preparation for Use H false organization false 1 CP-08 8 Telecommunications Services M, H 800-34 false organization false 1 CP-08(01) 8 1 Priority of Service Provisions M, H false organization false 1 CP-08(02) 8 2 Single Points of Failure M, H false organization false 1 CP-08(03) 8 3 Separation of Primary and Alternate Providers H false organization false 1 CP-08(04) 8 4 Provider Contingency Plan H false organization false 1 CP-09 9 System Backup L, M, H 140-2, 186-4, 800-34, 800-130 false organization false 1 CP-09(01) 9 1 Testing for Reliability and Integrity M, H false organization false 1 CP-09(02) 9 2 Test Restoration Using Sampling H false organization false 1 CP-09(03) 9 3 Separate Storage for Critical Information H false organization false 1 CP-09(05) 9 5 Transfer to Alternate Storage Site H false organization false 1 Print Date: 7/23/2018 Page 15 of 127
- 16. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 CP-09(08) 9 8 Cryptographic Protection M, H false organization false 1 CP-10 10 System Recovery and Reconstitution L, M, H 800-34 false organization false 1 CP-10(02) 10 2 Transaction Recovery M, H false organization false 1 CP-10(04) 10 4 Restore Within Time-Period H false organization false 1 IA 26 IA-01 1 Identification and Authentication Policy and Procedures L, M, H true organization true 1 IA-02 2 Identification and Authentication (Organizational Users) L, M, H false organization-and-system false 1 IA-02(01) 2 1 Multifactor Authentication to Privileged Accounts L, M, H false system false 1 IA-02(02) 2 2 Multifactor Authentication to Non-Privileged Accounts L, M, H false system false 1 IA-02(05) 2 5 Individual Authentication With Group Authentication H false organization false 1 IA-02(08) 2 8 Access to Accounts — Replay Resistant L, M, H false system false 1 IA-02(12) 2 12 Acceptance of Piv Credentials L, M, H false system false 1 IA-03 3 Device Identification and Authentication M, H false system false 1 IA-04 4 Identifier Management L, M, H 201, 800-63, 800-73, 800-76 false organization false 1 IA-04(04) 4 4 Identify User Status M, H true organization false 1 IA-05 5 Authenticator Management L, M, H false organization false 1 IA-05(01) 5 1 Password-Based Authentication L, M, H false organization-and-system false 1 IA-05(02) 5 2 Public Key-Based Authentication M, H false system false 1 IA-05(06) 5 6 Protection of Authenticators M, H false organization false 1 IA-06 6 Authenticator Feedback L, M, H false system false 1 IA-07 7 Cryptographic Module Authentication L, M, H 140-2 false system false 1 IA-08 8 Identification and Authentication (Non-Organizational Users) L, M, H false system false 1 IA-08(01) 8 1 Acceptance of Piv Credentials From Other Agencies L, M, H false system false 1 IA-08(02) 8 2 Acceptance of External Party Credentials L, M, H false system false 1 IA-08(04) 8 4 Use of Nist-Issued Profiles L, M, H false system false 1 IA-11 11 Re-authentication L, M, H false organization-and-system false 1 IA-12 12 Identity Proofing M, H 201, 800-63, 800-63A false organization false 1 IA-12(02) 12 2 Identity Evidence M, H false organization false 1 IA-12(03) 12 3 Identity Evidence Validation and Verification M, H false organization false 1 IA-12(04) 12 4 In-Person Validation and Verification H false organization false 1 IA-12(05) 12 5 Address Confirmation M, H false organization false 1 IR 18 IR-01 1 Incident Response Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-61, 800-83 true organization true 1 IR-02 2 Incident Response Training L, M, H 800-50 true organization true 1 IR-02(01) 2 1 Simulated Events H true organization true 1 IR-02(02) 2 2 Automated Training Environments H true organization true 1 IR-03 3 Incident Response Testing M, H 800-115, 800-84 true organization true 1 IR-03(02) 3 2 Coordination With Related Plans M, H true organization true 1 IR-04 4 Incident Handling L, M, H 800-61, 800-101, 800-86 true organization false 1 IR-04(01) 4 1 Automated Incident Handling Processes M, H false organization false 1 IR-04(04) 4 4 Information Correlation H false organization false 1 IR-05 5 Incident Monitoring L, M, H 800-61 true organization true 1 Print Date: 7/23/2018 Page 16 of 127
- 17. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 IR-05(01) 5 1 Automated Tracking, Data Collection, and Analysis H true organization true 1 IR-06 6 Incident Reporting L, M, H 800-61 true organization false 1 IR-06(01) 6 1 Automated Reporting M, H false organization false 1 IR-06(03) 6 3 Supply Chain Coordination M, H false organization false 1 IR-07 7 Incident Response Assistance L, M, H 7559 true organization false 1 IR-07(01) 7 1 Automation Support for Availability of Information and Support M, H false organization false 1 IR-08 8 Incident Response Plan L, M, H 800-61 true organization false 1 IR-10 10 Integrated Information Security Analysis Team H 7559, 800-150 false organization false 1 MA 12 MA-01 1 System Maintenance Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 MA-02 2 Controlled Maintenance L, M, H 8023 false organization false 1 MA-02(02) 2 2 Automated Maintenance Activities H false organization false 1 MA-03 3 Maintenance Tools M, H 800-88 false organization false 1 MA-03(01) 3 1 Inspect Tools M, H false organization false 1 MA-03(02) 3 2 Inspect Media M, H false organization false 1 MA-03(03) 3 3 Prevent Unauthorized Removal M, H false organization false 1 MA-04 4 Nonlocal Maintenance L, M, H 140-2, 201, 800-63, 197 false organization false 1 MA-04(03) 4 3 Comparable Security and Sanitization H false organization false 1 MA-05 5 Maintenance Personnel L, M, H false organization false 1 MA-05(01) 5 1 Individuals Without Appropriate Access H false organization false 1 MA-06 6 Timely Maintenance M, H false organization false 1 MP 10 MP-01 1 Media Protection Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 MP-02 2 Media Access L, M, H 199, 800-111 false organization false 1 MP-03 3 Media Marking M, H 199 false organization false 1 MP-04 4 Media Storage M, H false organization false 1 MP-05 5 Media Transport M, H 199, 800-60-2, 800-60-1 false organization false 1 MP-06 6 Media Sanitization L, M, H false organization false 1 MP-06(01) 6 1 Review, Approve, Track, Document, Verify H false organization false 1 MP-06(02) 6 2 Equipment Testing H false organization false 1 MP-06(03) 6 3 Nondestructive Techniques H false organization false 1 MP-07 7 Media Use L, M, H 199, 800-111 false organization false 1 PE 25 PE-01 1 Physical and Environmental Protection Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 PE-02 2 Physical Access Authorizations L, M, H 201, 800-73, 800-78, 800-76 false organization false 1 PE-03 3 Physical Access Control L, M, H 201, 800-73, 800-78, 800-76 false organization false 1 PE-03(01) 3 1 System Access H false organization false 1 PE-04 4 Access Control for Transmission M, H false organization false 1 PE-05 5 Access Control for Output Devices M, H 8023 false organization false 1 PE-06 6 Monitoring Physical Access L, M, H false organization true 1 PE-06(01) 6 1 Intrusion Alarms and Surveillance Equipment M, H false organization true 1 PE-06(04) 6 4 Monitoring Physical Access to Systems H false organization true 1 Print Date: 7/23/2018 Page 17 of 127
- 18. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 PE-08 8 Visitor Access Records L, M, H false organization true 1 PE-08(01) 8 1 Automated Records Maintenance and Review H false organization false 1 PE-09 9 Power Equipment and Cabling M, H false organization false 1 PE-10 10 Emergency Shutoff M, H false organization false 1 PE-11 11 Emergency Power M, H false organization false 1 PE-11(01) 11 1 Long-Term Alternate Power Supply — Minimal Operational Capability H false organization false 1 PE-12 12 Emergency Lighting L, M, H false organization false 1 PE-13 13 Fire Protection L, M, H false organization false 1 PE-13(01) 13 1 Detection Devices and Systems M, H false organization false 1 PE-13(02) 13 2 Automatic Suppression Devices and Systems H false organization false 1 PE-14 14 Temperature and Humidity Controls L, M, H false organization false 1 PE-15 15 Water Damage Protection L, M, H false organization false 1 PE-15(01) 15 1 Automation Support H false organization false 1 PE-16 16 Delivery and Removal L, M, H false organization false 1 PE-17 17 Alternate Work Site M, H 800-46 false organization false 1 PE-18 18 Location of System Components H false organization false 1 PL 8 PL-01 1 Planning Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100, 800-18 true organization true 1 PL-02 2 Security and Privacy Plans L, M, H 800-18 true organization true 1 PL-02(03) 2 3 Plan and Coordinate With Other Organizational Entities M, H true organization true 1 PL-04 4 Rules of Behavior L, M, H 800-18 true organization true 1 PL-04(01) 4 1 Social Media and Networking Restrictions L, M, H false organization true 1 PL-08 8 Security and Privacy Architectures M, H true organization true 1 PL-10 10 Baseline Selection L, M, H false organization false 1 PL-11 11 Baseline Tailoring L, M, H false organization false 1 PS 9 PS-01 1 Personnel Security Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 PS-02 2 Position Risk Designation L, M, H 5 C.F.R. 731.106 false organization false 1 PS-03 3 Personnel Screening L, M, H false organization false 1 PS-04 4 Personnel Termination L, M, H false organization false 1 PS-04(02) 4 2 Automated Notification H false organization false 1 PS-05 5 Personnel Transfer L, M, H false organization false 1 PS-06 6 Access Agreements L, M, H false organization true 1 PS-07 7 External Personnel Security L, M, H 800-35 false organization true 1 PS-08 8 Personnel Sanctions L, M, H false organization false 1 RA 10 RA-01 1 Risk Assessment Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 false organization true 1 RA-02 2 Security Categorization L, M, H false organization false 1 RA-03 3 Risk Assessment L, M, H 800-39, 800-30, 800-161 false organization true 1 RA-03(01) 3 1 Supply Chain Risk Assessment M, H false organization false 1 RA-05 5 Vulnerability Scanning L, M, H false organization true 1 RA-05(02) 5 2 Update by Frequency, Prior to New Scan, or When Identified L, M, H false organization true 1 Print Date: 7/23/2018 Page 18 of 127
- 19. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 RA-05(04) 5 4 Discoverable Information H false organization true 1 RA-05(05) 5 5 Privileged Access M, H false organization true 1 RA-07 7 Risk Response L, M, H false organization true 1 RA-09 9 Criticality Analysis M, H false organization false 1 SA 22 SA-01 1 System and Services Acquisition Policy and Procedures L, M, H 800-12, 800-39, 800-30, 800-100 true organization true 1 SA-02 2 Allocation of Resources L, M, H 800-65 false organization true 1 SA-03 3 System Development Life Cycle L, M, H 800-30, 800-37, 800-64 true organization true 1 SA-04 4 Acquisition Process L, M, H true organization true 1 SA-04(01) 4 1 Functional Properties of Controls M, H false organization true 1 SA-04(02) 4 2 Design and Implementation Information for Controls M, H false organization true 1 SA-04(05) 4 5 System, Component, and Service Configurations H false organization true 1 SA-04(09) 4 9 Functions, Ports, Protocols, and Services in Use M, H false organization true 1 SA-04(10) 4 10 Use of Approved Piv Products L, M, H false organization true 1 SA-05 5 System Documentation L, M, H false organization true 1 SA-08 8 Security and Privacy Engineering Principles L, M, H true organization true 1 SA-09 9 External System Services L, M, H 800-161, 800-35 true organization true 1 SA-09(02) 9 2 Identification of Functions, Ports, Protocols, and Services M, H false organization true 1 SA-10 10 Developer Configuration Management M, H 800-12, 140-2, 202, 800-128, 180-4 false organization true 1 SA-11 11 Developer Testing and Evaluation M, H 800-30, 800-53A, 15408, 800-154 true organization true 1 SA-12 12 Supply Chain Risk Management M, H false organization true 1 SA-15 15 Development Process, Standards, and Tools M, H false organization true 1 SA-15(03) 15 3 Criticality Analysis M, H false organization true 1 SA-16 16 Developer-Provided Training H false organization true 1 SA-17 17 Developer Security Architecture and Design H 15408, 800-160 false organization true 1 SA-21 21 Developer Screening H false organization true 1 SA-22 22 Unsupported System Components L, M, H false organization true 1 SC 31 SC-01 1 System and Communications Protection Policy and Procedures L, M, H 800-12, 800-100 true organization true 1 SC-02 2 Application Partitioning M, H false system true 1 SC-03 3 Security Function Isolation H false system true 1 SC-04 4 Information in Shared System Resources M, H false system false 1 SC-05 5 Denial of Service Protection L, M, H false system false 1 SC-07 7 Boundary Protection L, M, H 199, 800-77, 800-41 false system false 1 SC-07(03) 7 3 Access Points M, H false system false 1 SC-07(04) 7 4 External Telecommunications Services M, H false organization false 1 SC-07(05) 7 5 Deny by Default — Allow by Exception M, H false system false 1 SC-07(07) 7 7 Prevent Split Tunneling for Remote Devices M, H false system false 1 SC-07(08) 7 8 Route Traffic to Authenticated Proxy Servers M, H false system false 1 SC-07(18) 7 18 Fail Secure H false system true 1 SC-07(21) 7 21 Isolation of System Components H false organization-and-system true 1 SC-08 8 Transmission Confidentiality and Integrity M, H false system false 1 Print Date: 7/23/2018 Page 19 of 127
- 20. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 SC-08(01) 8 1 Cryptographic Protection M, H false system false 1 SC-10 10 Network Disconnect M, H false system false 1 SC-12 12 Cryptographic Key Establishment and Management L, M, H false organization-and-system false 1 SC-12(01) 12 1 Availability H false organization-and-system false 1 SC-13 13 Cryptographic Protection L, M, H 140-2 false system false 1 SC-15 15 Collaborative Computing Devices and Applications L, M, H false system false 1 SC-17 17 Public Key Infrastructure Certificates M, H 800-63, 800-57-2, 800-57-1, 800-57-3, 800-32 false organization-and-system false 1 SC-18 18 Mobile Code M, H 800-28 false organization false 1 SC-19 19 Voice Over Internet Protocol M, H 800-58 false organization false 1 SC-20 20 Secure Name/Address Resolution Service (Authoritative Source) L, M, H 140-2, 186-4, 800-81 false system false 1 SC-21 21 Secure Name/Address Resolution Service (Recursive or Caching Resolver) L, M, H 800-81 false system false 1 SC-22 22 Architecture and Provisioning for Name/Address Resolution Service L, M, H 800-81 false system false 1 SC-23 23 Session Authenticity M, H 800-77, 800-113, 800-52, 800-95 false system false 1 SC-24 24 Fail in Known State H false system true 1 SC-28 28 Protection of Information at Rest M, H false system false 1 SC-28(01) 28 1 Cryptographic Protection M, H false system false 1 SC-39 39 Process Isolation L, M, H false system true 1 SI 32 SI-01 1 System and Information Integrity Policy and Procedures L, M, H 800-12, 800-100 true organization true 1 SI-02 2 Flaw Remediation L, M, H false organization false 1 SI-02(01) 2 1 Central Management H false organization false 1 SI-02(02) 2 2 Automated Flaw Remediation Status M, H false organization false 1 SI-03 3 Malicious Code Protection L, M, H 800-12, 800-177, 800-83, 800-125B false organization false 1 SI-03(01) 3 1 Central Management M, H false organization false 1 SI-04 4 System Monitoring L, M, H 800-137, 800-61, 800-83, 800-92, 800-94 false organization-and-system true 1 SI-04(02) 4 2 Automated Tools and Mechanisms for Real-Time Analysis M, H false system true 1 SI-04(04) 4 4 Inbound and Outbound Communications Traffic M, H false system true 1 SI-04(05) 4 5 System-Generated Alerts M, H false system true 1 SI-04(10) 4 10 Visibility of Encrypted Communications H false organization true 1 SI-04(12) 4 12 Automated Organization-Generated Alerts H false organization-and-system true 1 SI-04(14) 4 14 Wireless Intrusion Detection H false system true 1 SI-04(20) 4 20 Privileged Users H false system true 1 SI-04(22) 4 22 Unauthorized Network Services H false system true 1 SI-05 5 Security Alerts, Advisories, and Directives L, M, H 800-40 false organization true 1 SI-05(01) 5 1 Automated Alerts and Advisories H false organization true 1 SI-06 6 Security and Privacy Function Verification H true system true 1 SI-07 7 Software, Firmware, and Information Integrity M, H false organization-and-system true 1 SI-07(01) 7 1 Integrity Checks M, H false system true 1 SI-07(02) 7 2 Automated Notifications of Integrity Violations H false system true 1 SI-07(05) 7 5 Automated Response to Integrity Violations H false system true 1 SI-07(07) 7 7 Integration of Detection and Response M, H false organization true 1 SI-07(14) 7 14 Binary or Machine Executable Code H false organization-and-system true 1 Print Date: 7/23/2018 Page 20 of 127
- 21. High Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx High Baseline true 369 189 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute High Baseline Count 7/18/18 SP 800-53 R5 369 SI-07(15) 7 15 Code Authentication H false system true 1 SI-08 8 Spam Protection M, H 800-177, 800-45 false organization false 1 SI-08(01) 8 1 Central Management M, H false organization false 1 SI-08(02) 8 2 Automatic Updates M, H false system false 1 SI-10 10 Information Input Validation M, H 800-167 false system true 1 SI-11 11 Error Handling M, H false system false 1 SI-12 12 Information Management and Retention L, M, H 800-18, 800-188 true organization false 1 SI-16 16 Memory Protection M, H false system true 1 Total 369 Print Date: 7/23/2018 Page 21 of 127
- 22. Null Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Null Baseline Null 543 447 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Null Baseline Count 7/18/18 SP 800-53 R5 543 AC 75 AC-02(06) 2 6 Dynamic Privilege Management None false system false 1 AC-02(07) 2 7 Role-Based Schemes None false organization false 1 AC-02(08) 2 8 Dynamic Account Management None false system false 1 AC-02(09) 2 9 Restrictions on Use of Shared and Group Accounts None false organization false 1 AC-02(14) 2 14 Prohibit Specific Account Types None false organization false 1 AC-02(15) 2 15 Attribute-Based Schemes None false organization false 1 AC-03(02) 3 2 Dual Authorization None false system false 1 AC-03(03) 3 3 Mandatory Access Control None false system false 1 AC-03(04) 3 4 Discretionary Access Control None false system false 1 AC-03(05) 3 5 Security-Relevant Information None false system false 1 AC-03(07) 3 7 Role-Based Access Control None false organization-and-system false 1 AC-03(08) 3 8 Revocation of Access Authorizations None false organization-and-system false 1 AC-03(09) 3 9 Controlled Release None false organization-and-system false 1 AC-03(10) 3 10 Audited Override of Access Control Mechanisms None false organization false 1 AC-03(11) 3 11 Restrict Access to Specific Information None false system false 1 AC-03(12) 3 12 Assert and Enforce Application Access None false system false 1 AC-03(13) 3 13 Attribute-Based Access Control None false system false 1 AC-04(01) 4 1 Object Security Attributes None false system false 1 AC-04(02) 4 2 Processing Domains None false system false 1 AC-04(03) 4 3 Dynamic Information Flow Control None false system false 1 AC-04(05) 4 5 Embedded Data Types None false system false 1 AC-04(06) 4 6 Metadata None false system false 1 AC-04(07) 4 7 One-Way Flow Mechanisms None false system false 1 AC-04(08) 4 8 Security Policy Filters None false system false 1 AC-04(09) 4 9 Human Reviews None false organization false 1 AC-04(10) 4 10 Enable and Disable Security Policy Filters None false system false 1 AC-04(11) 4 11 Configuration of Security Policy Filters None false system false 1 AC-04(12) 4 12 Data Type Identifiers None false system false 1 AC-04(13) 4 13 Decomposition Into Policy-Relevant Subcomponents None false system false 1 AC-04(14) 4 14 Security Policy Filter Constraints None false system false 1 AC-04(15) 4 15 Detection of Unsanctioned Information None false system false 1 AC-04(17) 4 17 Domain Authentication None false system false 1 AC-04(19) 4 19 Validation of Metadata None false system false 1 AC-04(20) 4 20 Approved Solutions None false organization false 1 AC-04(21) 4 21 Physical and Logical Separation of Information Flows None false system false 1 AC-04(22) 4 22 Access Only None false system false 1 AC-06(04) 6 4 Separate Processing Domains None false system false 1 AC-06(06) 6 6 Privileged Access by Non-Organizational Users None false organization false 1 AC-06(08) 6 8 Privilege Levels for Code Execution None false system false 1 AC-07(02) 7 2 Purge or Wipe Mobile Device None false system false 1 AC-07(03) 7 3 Biometric Attempt Limiting None false organization false 1 AC-07(04) 7 4 Use of Alternate Factor None false organization false 1 AC-09 9 Previous Logon (Access) Notification None false system false 1 Print Date: 7/23/2018 Page 22 of 127
- 23. Null Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Null Baseline Null 543 447 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Null Baseline Count 7/18/18 SP 800-53 R5 543 AC-09(01) 9 1 Unsuccessful Logons None false system false 1 AC-09(02) 9 2 Successful and Unsuccessful Logons None false system false 1 AC-09(03) 9 3 Notification of Account Changes None false system false 1 AC-09(04) 9 4 Additional Logon Information None false system false 1 AC-11(02) 11 2 Require User-Initiated Lock None false organization false 1 AC-12(01) 12 1 User-Initiated Logouts None false organization false 1 AC-12(02) 12 2 Termination Message None false system false 1 AC-12(03) 12 3 Timeout Warning Message None false system false 1 AC-16 16 Security and Privacy Attributes None 140-2, 186-4, 800-162, 800-178 true organization false 1 AC-16(01) 16 1 Dynamic Attribute Association None true system false 1 AC-16(02) 16 2 Attribute Value Changes by Authorized Individuals None true system false 1 AC-16(03) 16 3 Maintenance of Attribute Associations by System None true system false 1 AC-16(04) 16 4 Association of Attributes by Authorized Individuals None true system false 1 AC-16(05) 16 5 Attribute Displays for Output Devices None true system false 1 AC-16(06) 16 6 Maintenance of Attribute Association by Organization None true organization false 1 AC-16(07) 16 7 Consistent Attribute Interpretation None true organization false 1 AC-16(08) 16 8 Association Techniques and Technologies None true system false 1 AC-16(09) 16 9 Attribute Reassignment None true organization false 1 AC-16(10) 16 10 Attribute Configuration by Authorized Individuals None true organization false 1 AC-16(11) 16 11 Audit Changes None true system false 1 AC-17(06) 17 6 Protection of Information None false organization false 1 AC-17(09) 17 9 Disconnect or Disable Access None false organization false 1 AC-19(04) 19 4 Restrictions for Classified Information None false organization false 1 AC-20(03) 20 3 Non-Organizationally Owned Systems and Components None false organization false 1 AC-20(04) 20 4 Network Accessible Storage Devices None false organization false 1 AC-21(01) 21 1 Automated Decision Support None false system false 1 AC-21(02) 21 2 Information Search and Retrieval None false system false 1 AC-23 23 Data Mining Protection None true organization false 1 AC-24 24 Access Control Decisions None 800-162, 800-178 false organization false 1 AC-24(01) 24 1 Transmit Access Authorization Information None false system false 1 AC-24(02) 24 2 no User or Process Identity None false system false 1 AC-25 25 Reference Monitor None false system true 1 AT 6 AT-02(01) 2 1 Practical Exercises None true organization true 1 AT-03(01) 3 1 Environmental Controls None false organization true 1 AT-03(02) 3 2 Physical Security Controls None false organization true 1 AT-03(03) 3 3 Practical Exercises None true organization true 1 AT-03(04) 3 4 Suspicious Communications and Anomalous System Behavior None false organization true 1 AT-03(05) 3 5 Personally Identifiable Information Processing None true organization true 1 AU 32 AU-03(03) 3 3 Limit Personally Identifiable Information Elements None true organization false 1 AU-04(01) 4 1 Transfer to Alternate Storage None false organization false 1 AU-05(03) 5 3 Configurable Traffic Volume Thresholds None false system false 1 AU-05(04) 5 4 Shutdown on Failure None false system false 1 Print Date: 7/23/2018 Page 23 of 127
- 24. Null Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Null Baseline Null 543 447 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Null Baseline Count 7/18/18 SP 800-53 R5 543 AU-06(04) 6 4 Central Review and Analysis None false system true 1 AU-06(07) 6 7 Permitted Actions None false organization true 1 AU-06(08) 6 8 Full Text Analysis of Privileged Commands None false organization true 1 AU-06(09) 6 9 Correlation With Information From Nontechnical Sources None false organization true 1 AU-07(02) 7 2 Automatic Sort and Search None false system false 1 AU-08(02) 8 2 Secondary Authoritative Time Source None false system false 1 AU-09(01) 9 1 Hardware Write-Once Media None false system false 1 AU-09(05) 9 5 Dual Authorization None false organization-and-system false 1 AU-09(06) 9 6 Read-Only Access None false organization-and-system false 1 AU-09(07) 9 7 Store on Component With Different Operating System None false organization false 1 AU-10(01) 10 1 Association of Identities None false system true 1 AU-10(02) 10 2 Validate Binding of Information Producer Identity None false system true 1 AU-10(03) 10 3 Chain of Custody None false organization-and-system true 1 AU-10(04) 10 4 Validate Binding of Information Reviewer Identity None false system true 1 AU-11(01) 11 1 Long-Term Retrieval Capability None false organization true 1 AU-12(02) 12 2 Standardized Formats None false system false 1 AU-12(04) 12 4 Query Parameter Audits of Personally Identifiable Information None true system false 1 AU-13 13 Monitoring for Information Disclosure None false organization true 1 AU-13(01) 13 1 Use of Automated Tools None false organization-and-system true 1 AU-13(02) 13 2 Review of Monitored Sites None false organization true 1 AU-14 14 Session Audit None false system true 1 AU-14(01) 14 1 System Start-Up None false system true 1 AU-14(02) 14 2 Capture and Record Content None false system true 1 AU-14(03) 14 3 Remote Viewing and Listening None false system true 1 AU-15 15 Alternate Audit Capability None false organization false 1 AU-16 16 Cross-Organizational Auditing None true organization false 1 AU-16(01) 16 1 Identity Preservation None false organization false 1 AU-16(02) 16 2 Sharing of Audit Information None false organization false 1 CA 12 CA-02(03) 2 3 External Organizations None true organization true 1 CA-03(01) 3 1 Unclassified National Security System Connections None false organization false 1 CA-03(02) 3 2 Classified National Security System Connections None false organization false 1 CA-03(03) 3 3 Unclassified Non-National Security System Connections None false organization false 1 CA-03(04) 3 4 Connections to Public Networks None false organization false 1 CA-05(01) 5 1 Automation Support for Accuracy and Currency None false organization true 1 CA-06(01) 6 1 Joint Authorization — Same Organization None false organization true 1 CA-06(02) 6 2 Joint Authorization — Different Organizations None false organization true 1 CA-07(03) 7 3 Trend Analyses None false organization true 1 CA-08(02) 8 2 Red Team Exercises None false organization true 1 CA-08(03) 8 3 Facility Penetration Testing None false organization true 1 CA-09(01) 9 1 Compliance Checks None false system true 1 CM 17 CM-02(06) 2 6 Development and Test Environments None false organization true 1 CM-03(03) 3 3 Automated Change Implementation None false organization false 1 Print Date: 7/23/2018 Page 24 of 127
- 25. Null Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Null Baseline Null 543 447 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Null Baseline Count 7/18/18 SP 800-53 R5 543 CM-03(05) 3 5 Automated Security Response None false system false 1 CM-05(04) 5 4 Dual Authorization None false organization-and-system false 1 CM-05(05) 5 5 Privilege Limitation for Production and Operation None false organization false 1 CM-05(06) 5 6 Limit Library Privileges None false organization false 1 CM-07(03) 7 3 Registration Compliance None false organization false 1 CM-07(04) 7 4 Unauthorized Software — Blacklisting None false organization false 1 CM-08(05) 8 5 no Duplicate Accounting of Components None false organization true 1 CM-08(06) 8 6 Assessed Configurations and Approved Deviations None false organization true 1 CM-08(07) 8 7 Centralized Repository None false organization true 1 CM-08(08) 8 8 Automated Location Tracking None false organization true 1 CM-08(09) 8 9 Assignment of Components to Systems None false organization true 1 CM-08(10) 8 10 Data Action Mapping None true organization true 1 CM-09(01) 9 1 Assignment of Responsibility None false organization false 1 CM-10(01) 10 1 Open Source Software None false organization false 1 CM-11(02) 11 2 Software Installation With Privileged Status None false system false 1 CP 13 CP-02(06) 2 6 Alternate Processing and Storage Sites None false organization false 1 CP-02(07) 2 7 Coordinate With External Service Providers None true organization false 1 CP-03(02) 3 2 Automated Training Environments None true organization true 1 CP-04(03) 4 3 Automated Testing None false organization true 1 CP-04(04) 4 4 Full Recovery and Reconstitution None false organization true 1 CP-07(06) 7 6 Inability to Return to Primary Site None false organization false 1 CP-08(05) 8 5 Alternate Telecommunication Service Testing None false organization false 1 CP-09(06) 9 6 Redundant Secondary System None false organization false 1 CP-09(07) 9 7 Dual Authorization None false organization false 1 CP-10(06) 10 6 Component Protection None false organization false 1 CP-11 11 Alternate Communications Protocols None false organization false 1 CP-12 12 Safe Mode None false system true 1 CP-13 13 Alternative Security Mechanisms None false organization-and-system false 1 IA 27 IA-02(10) 2 10 Single Sign-On None false system false 1 IA-03(01) 3 1 Cryptographic Bidirectional Authentication None false system false 1 IA-03(03) 3 3 Dynamic Address Allocation None false organization false 1 IA-03(04) 3 4 Device Attestation None false organization false 1 IA-04(01) 4 1 Prohibit Account Identifiers As Public Identifiers None false organization false 1 IA-04(05) 4 5 Dynamic Management None false system false 1 IA-04(06) 4 6 Cross-Organization Management None false organization false 1 IA-04(08) 4 8 Pairwise Pseudonymous Identifiers None true organization false 1 IA-05(05) 5 5 Change Authenticators Prior to Delivery None false organization false 1 IA-05(07) 5 7 no Embedded Unencrypted Static Authenticators None false organization false 1 IA-05(08) 5 8 Multiple System Accounts None false organization false 1 IA-05(09) 5 9 Federated Credential Management None false organization false 1 IA-05(10) 5 10 Dynamic Credential Binding None false system false 1 IA-05(12) 5 12 Biometric Authentication Performance None false system false 1 Print Date: 7/23/2018 Page 25 of 127
- 26. Null Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Null Baseline Null 543 447 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Null Baseline Count 7/18/18 SP 800-53 R5 543 IA-05(13) 5 13 Expiration of Cached Authenticators None false system false 1 IA-05(14) 5 14 Managing Content of Pki Trust Stores None false organization false 1 IA-05(15) 5 15 Gsa-Approved Products and Services None false organization false 1 IA-05(16) 5 16 In-Person or Trusted External Party Authenticator Issuance None false organization false 1 IA-05(17) 5 17 Presentation Attack Detection for Biometric Authenticators None false system false 1 IA-08(05) 8 5 Acceptance of Piv-I Credentials None false system false 1 IA-08(06) 8 6 Disassociability None true organization false 1 IA-09 9 Service Identification and Authentication None false organization-and-system false 1 IA-09(01) 9 1 Information Exchange None false organization false 1 IA-09(02) 9 2 Transmission of Decisions None false organization false 1 IA-10 10 Adaptive Authentication None 800-63 false organization false 1 IA-12(01) 12 1 Supervisor Authorization None false organization false 1 IA-12(06) 12 6 Accept Externally-Proofed Identities None false organization false 1 IP 11 IP-01 1 Individual Participation Policy and Procedures None 800-12, 800-39, 800-30, 800-100 true organization false 1 IP-02 2 Consent None 8062, 800-63 true organization false 1 IP-02(01) 2 1 Attribute Management None true organization false 1 IP-02(02) 2 2 Just-In-Time Notice of Consent None true organization false 1 IP-03 3 Redress None true organization false 1 IP-03(01) 3 1 Notice of Correction or Amendment None true organization false 1 IP-03(02) 3 2 Appeal None true organization false 1 IP-04 4 Privacy Notice None 8062 true organization false 1 IP-04(01) 4 1 Just-In-Time Notice of Privacy Authorization None true organization false 1 IP-05 5 Privacy Act Statements None true organization false 1 IP-06 6 Individual Access None 8062 true organization false 1 IR 18 IR-03(01) 3 1 Automated Testing None false organization true 1 IR-03(03) 3 3 Continuous Improvement None false organization true 1 IR-04(02) 4 2 Dynamic Reconfiguration None false organization false 1 IR-04(03) 4 3 Continuity of Operations None false organization false 1 IR-04(05) 4 5 Automatic Disabling of System None false organization-and-system false 1 IR-04(06) 4 6 Insider Threats — Specific Capabilities None false organization false 1 IR-04(07) 4 7 Insider Threats — Intra-Organization Coordination None false organization false 1 IR-04(08) 4 8 Correlation With External Organizations None false organization false 1 IR-04(09) 4 9 Dynamic Response Capability None false organization false 1 IR-04(10) 4 10 Supply Chain Coordination None false organization false 1 IR-06(02) 6 2 Vulnerabilities Related to Incidents None false organization false 1 IR-07(02) 7 2 Coordination With External Providers None false organization false 1 IR-08(01) 8 1 Personally Identifiable Information Processes None true organization false 1 IR-09 9 Information Spillage Response None true organization false 1 IR-09(01) 9 1 Responsible Personnel None false organization false 1 IR-09(02) 9 2 Training None false organization false 1 IR-09(03) 9 3 Post-Spill Operations None false organization false 1 IR-09(04) 9 4 Exposure to Unauthorized Personnel None false organization false 1 Print Date: 7/23/2018 Page 26 of 127
- 27. Null Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Null Baseline Null 543 447 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Null Baseline Count 7/18/18 SP 800-53 R5 543 MA 14 MA-03(04) 3 4 Restricted Tool Use None false system false 1 MA-04(01) 4 1 Auditing and Review None false organization false 1 MA-04(04) 4 4 Authentication and Separation of Maintenance Sessions None false organization false 1 MA-04(05) 4 5 Approvals and Notifications None false organization false 1 MA-04(06) 4 6 Cryptographic Protection None false organization-and-system false 1 MA-04(07) 4 7 Remote Disconnect Verification None false system false 1 MA-05(02) 5 2 Security Clearances for Classified Systems None false organization false 1 MA-05(03) 5 3 Citizenship Requirements for Classified Systems None false organization false 1 MA-05(04) 5 4 Foreign Nationals None false organization false 1 MA-05(05) 5 5 Non-System Maintenance None false organization false 1 MA-06(01) 6 1 Preventive Maintenance None false organization false 1 MA-06(02) 6 2 Predictive Maintenance None false organization false 1 MA-06(03) 6 3 Automated Support for Predictive Maintenance None false organization false 1 MA-06(04) 6 4 Adequate Supply None false organization false 1 MP 11 MP-04(02) 4 2 Automated Restricted Access None false organization false 1 MP-05(03) 5 3 Custodians None false organization false 1 MP-06(07) 6 7 Dual Authorization None false organization false 1 MP-06(08) 6 8 Remote Purging or Wiping of Information None false organization false 1 MP-06(09) 6 9 Destruction of Personally Identifiable Information None false organization false 1 MP-07(02) 7 2 Prohibit Use of Sanitization-Resistant Media None false organization false 1 MP-08 8 Media Downgrading None false organization false 1 MP-08(01) 8 1 Documentation of Process None false organization false 1 MP-08(02) 8 2 Equipment Testing None false organization false 1 MP-08(03) 8 3 Controlled Unclassified Information None false organization false 1 MP-08(04) 8 4 Classified Information None false organization false 1 PA 6 PA-01 1 Privacy Authorization Policy and Procedures None 800-12, 800-39, 800-30, 800-100 true organization false 1 PA-02 2 Authority to Collect None true organization false 1 PA-03 3 Purpose Specification None true organization false 1 PA-03(01) 3 1 Usage Restrictions of Personally Identifiable Information None true organization false 1 PA-03(02) 3 2 Automation None true system false 1 PA-04 4 Information Sharing with External Parties None true organization false 1 PE 26 PE-02(01) 2 1 Access by Position and Role None false organization false 1 PE-02(02) 2 2 Two Forms of Identification None false organization false 1 PE-02(03) 2 3 Restrict Unescorted Access None false organization false 1 PE-03(02) 3 2 Facility and System Boundaries None false organization false 1 PE-03(03) 3 3 Continuous Guards None false organization false 1 PE-03(04) 3 4 Lockable Casings None false organization false 1 PE-03(05) 3 5 Tamper Protection None false organization false 1 PE-03(07) 3 7 Physical Barriers None false organization false 1 PE-05(01) 5 1 Access to Output by Authorized Individuals None false organization false 1 Print Date: 7/23/2018 Page 27 of 127
- 28. Null Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Null Baseline Null 543 447 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Null Baseline Count 7/18/18 SP 800-53 R5 543 PE-05(02) 5 2 Access to Output by Individual Identity None false system false 1 PE-05(03) 5 3 Marking Output Devices None false organization false 1 PE-06(02) 6 2 Automated Intrusion Recognition and Responses None false organization true 1 PE-06(03) 6 3 Video Surveillance None false organization true 1 PE-09(01) 9 1 Redundant Cabling None false organization false 1 PE-09(02) 9 2 Automatic Voltage Controls None false organization false 1 PE-11(02) 11 2 Long-Term Alternate Power Supply — Self-Contained None false organization false 1 PE-12(01) 12 1 Essential Missions and Business Functions None false organization false 1 PE-13(04) 13 4 Inspections None false organization false 1 PE-14(01) 14 1 Automatic Controls None false organization false 1 PE-14(02) 14 2 Monitoring With Alarms and Notifications None false organization false 1 PE-18(01) 18 1 Facility Site None false organization false 1 PE-19 19 Information Leakage None 199 false organization false 1 PE-19(01) 19 1 National Emissions and Tempest Policies and Procedures None false organization false 1 PE-20 20 Asset Monitoring and Tracking None false organization false 1 PE-21 21 Electromagnetic Pulse Protection None false organization false 1 PE-22 22 Component Marking None false organization false 1 PL 4 PL-07 7 Concept of Operations None true organization false 1 PL-08(01) 8 1 Defense-In-Depth None false organization true 1 PL-08(02) 8 2 Supplier Diversity None true organization true 1 PL-09 9 Central Management None 800-37 true organization true 1 PM 38 PM-01 1 Information Security Program Plan None false organization false 1 PM-02 2 Information Security Program Roles None 800-39, 800-37, 17-25 false organization false 1 PM-03 3 Information Security and Privacy Resources None 800-65 true organization false 1 PM-04 4 Plan of Action and Milestones Process None 800-37 true organization false 1 PM-05 5 System Inventory None false organization false 1 PM-06 6 Measures of Performance None 800-137, 800-55 true organization true 1 PM-07 7 Enterprise Architecture None 800-39 true organization false 1 PM-08 8 Critical Infrastructure Plan None HSPD 7, National Infrastructure Protection Plan true organization false 1 PM-09 9 Risk Management Strategy None 800-39, 800-30, 800-161 true organization true 1 PM-10 10 Authorization Process None 800-39, 800-37 false organization true 1 PM-11 11 Mission and Business Process Definition None 199, 800-60-2, 800-60-1 true organization false 1 PM-12 12 Insider Threat Program None false organization true 1 PM-13 13 Security and Privacy Workforce None NIST Cyber Workforce Framework true organization false 1 PM-14 14 Testing, Training, and Monitoring None 800-39, 800-37, 800-137, 800-53A true organization true 1 PM-15 15 Contacts with Groups and Associations None true organization false 1 PM-16 16 Threat Awareness Program None false organization true 1 PM-16(01) 16 1 Automated Means for Sharing Threat Intelligence None false organization true 1 PM-17 17 Protecting CUI on External Systems None 32 CFR 2002, 800-171, NARA CUI Registry false organization true 1 PM-18 18 Privacy Program Plan None true organization false 1 PM-19 19 Privacy Program Roles None true organization false 1 PM-20 20 System of Records Notice None true organization false 1 Print Date: 7/23/2018 Page 28 of 127
- 29. Null Baseline NIST SP 800‐53 Revision 5 Controls and Enhancement Metadata NIST_SP_800_Rev_5_20180722a.xlsx Null Baseline Null 543 447 RptDate Source Family Result CTRL-ID Sortable CTRL_ID Result CTRL_ENH Result Name Result FIP-199 Impact References Result Privacy-related Attribute Implemented-by Attribute Assurance Attribute Null Baseline Count 7/18/18 SP 800-53 R5 543 PM-21 21 Dissemination of Privacy Program Information None true organization false 1 PM-22 22 Accounting of Disclosures None true organization false 1 PM-23 23 Data Quality Management None 800-18, 800-188 true organization true 1 PM-23(01) 23 1 Automation None true organization true 1 PM-23(02) 23 2 Data Tagging None true organization true 1 PM-23(03) 23 3 Updating Personally Identifiable Information None true organization true 1 PM-24 24 Data Management Board None 800-18, 800-188 true organization true 1 PM-25 25 Data Integrity Board None true organization true 1 PM-25(01) 25 1 Publish Agreements on Website None true organization false 1 PM-26 26 Minimization of PII Used in Testing Training, and Research None true organization false 1 PM-27 27 Individual Access Control None true organization false 1 PM-28 28 Complaint Management None true organization false 1 PM-29 29 Inventory of PII None true organization false 1 PM-29(01) 29 1 Automation Support None true organization false 1 PM-30 30 Privacy Reporting None true organization false 1 PM-31 31 Supply Chain Risk Management Plan None 800-161 false organization false 1 PM-32 32 Risk Framing None 800-39 true organization true 1 PS 7 PS-03(01) 3 1 Classified Information None false organization false 1 PS-03(02) 3 2 Formal Indoctrination None false organization false 1 PS-03(03) 3 3 Information With Special Protection Measures None false organization false 1 PS-03(04) 3 4 Citizenship Requirements None false organization false 1 PS-04(01) 4 1 Post-Employment Requirements None false organization false 1 PS-06(02) 6 2 Classified Information Requiring Special Protection None false organization true 1 PS-06(03) 6 3 Post-Employment Requirements None false organization true 1 RA 7 RA-02(01) 2 1 Second-Level Categorization None false organization false 1 RA-05(03) 5 3 Breadth and Depth of Coverage None false organization true 1 RA-05(06) 5 6 Automated Trend Analyses None false organization true 1 RA-05(08) 5 8 Review Historic Audit Logs None false organization true 1 RA-05(10) 5 10 Correlate Scanning Information None false organization true 1 RA-06 6 Technical Surveillance Countermeasures Survey None false organization true 1 RA-08 8 Privacy Impact Assessments None false organization true 1 SA 64 SA-03(01) 3 1 Manage Development Environment None false organization true 1 SA-03(02) 3 2 Use of Live Data None false organization true 1 SA-03(03) 3 3 Technology Refresh None false organization true 1 SA-04(03) 4 3 Development Methods, Techniques, and Practices None false organization true 1 SA-04(06) 4 6 Use of Information Assurance Products None false organization true 1 SA-04(07) 4 7 Niap-Approved Protection Profiles None false organization true 1 SA-04(08) 4 8 Continuous Monitoring Plan for Controls None false organization true 1 SA-09(01) 9 1 Risk Assessments and Organizational Approvals None false organization true 1 SA-09(03) 9 3 Establish and Maintain Trust Relationship With Providers None true organization true 1 SA-09(04) 9 4 Consistent Interests of Consumers and Providers None false organization true 1 Print Date: 7/23/2018 Page 29 of 127
