Luncheon 2015-05-21 - CISO Roundtable by David Stanton
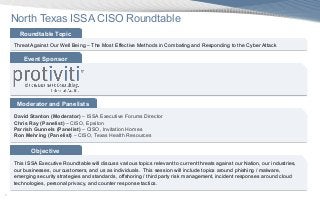
- 1. 1 North Texas ISSA CISO Roundtable Moderator and Panelists David Stanton (Moderator) – ISSA Executive Forums Director Chris Ray (Panelist) – CISO, Epsilon Parrish Gunnels (Panelist) – CISO, Invitation Homes Ron Mehring (Panelist) – CISO, Texas Health Resources Roundtable Topic Threat Against Our Well Being – The Most Effective Methods in Combating and Responding to the Cyber Attack Objective This ISSA Executive Roundtable will discuss various topics relevant to current threats against our Nation, our industries, our businesses, our customers, and us as individuals. This session will include topics around phishing / malware, emerging security strategies and standards, offshoring / third party risk management, incident responses around cloud technologies, personal privacy, and counter response tactics. Event Sponsor
- 2. 2 CISO Roundtable – Agenda and Topics • Chapter Announcements (5 – 10 minutes) • Roundtable Introductions (5 – 10 minutes) • Topics (80 minutes) o Current cyber threats against our organizations (Anthem, Sony, Target, Home Depot, etc.) o Various methods for reducing exposure to these threats o Attacks against us as individuals o Protecting and tracking sensitive data o Emerging technologies demanded by the business (BYOD, Cloud Services, etc.) • Questions from the Audience (5 – 10 minutes) • Closing and Drawings
- 3. 3 About Me David Stanton, ISSA Executive Forum Director, Security & Privacy Director at Protiviti, and regularly acting in senior security roles for various clients (Moderator) David has more than 16 years of IT and IT Security consulting experience and received a BBA in Managerial Information Systems from Baylor University. He joined the Protiviti Dallas office in the IT Consulting practice focusing on Security and Privacy in 2013. Prior to Protiviti, David held the position of Data Protection and Privacy lead for a Fortune Global 500 consulting firm, acted as an interim Chief Information Security for a large entertainment company, and was previously Information Security Officer (ISO) for a top 5 US credit union. Currently, David is also the ISSA Executive Forums Director, is the senior security leader for a local Healthcare Provider, and regularly speaks to large audiences around top of mind security topics (including Cloud Security, Third Party Risk Management Forensics / Incident Handling, and Cyber Threats). Powerful Insights. Proven Delivery.™ Phone: +1.214.850.7051 david.stanton@protiviti.com David Stanton Director, Security and Privacy Dallas, TX
- 4. 4 Risk Consulting & Advisory Protiviti (www.protiviti.com) is a global consulting firm that helps companies solve problems in finance, technology, operations, governance, risk, and internal audit. Through our network of more than 70 offices in over 20 countries, we have served more than 35 percent of FORTUNE® 1000 and Global 500 companies. We also work with smaller, growing companies, large multi-national corporations, as well as with educational institutions and government agencies. Protiviti – Who we are e Embedded Internal ControlProgram and Project Management Managing Applications Managing the Business of IT IT Security Business and Finance Operations Improvement Strategic and Operational Risk Internal Audit Sourcing & Consulting Restructuring & Financing Forecasting & Business Planning IT Consulting Governance, Risk & Audit Regulatory Compliance Finance & Performance Integrated Performance & Risk Management We help clients improve performance and manage risks. We believe in combining business insight and entrepreneurial spirit with experience and pragmatism. Now more than ever, this combination is essential for growing value whilst retaining control.
- 5. 5 Protiviti IT Consulting Offerings at a Glance
- 6. 6 Cyber Attacks describes the recent surge of internet sourced attacks focusing on effecting business operations, causing reputation harm, degrading eCommerce, stealing digital assets, and espionage against foreign entities. Usually these attack motivators are driven by financial, political, reputational, and personal interests in creating physical or logical harm. Rule of Thumb – What is important to you or to your company is likely of value to and target of someone else. What are Cyber Attacks?
- 7. 7 Initial Compromise Establish Foothold Escalate Privileges Complete Mission Move Laterally Maintain Presence The Story of the Attack
- 8. 8 11% 8% 11% 34% 25% 0% 5% 10% 15% 20% 25% 30% 35% 40% Manufacturing, Transportation, and Utilities Information and Professional Services Firms Retail Environments Financial Institutions Larger Organizations Who are the victims? Source: 2014 Verizon Data Breach Investigations Report, State of Cybersecurity: Implications for 2015 11% 31% 13% 55% 88% 2% 0% 20% 40% 60% 80% 100% Priviledged Misuse and Abuse Social Tactics Physical Attacks Malware Hacking Error How the breaches occur? Who did they get and how?
- 9. 9 1% 7% 13% 18% 90% 0% 20% 40% 60% 80% 100% Business Partners Multiple Parties Insiders State-affiliated Actors Outsiders Who is the attacker ? External (Trend) Internal (Trend) Partner (Trend) Source: 2014 Verizon Data Breach Investigations Report, State of Cybersecurity: Implications for 2015 78% 72% 86% 98% 92% 95% 39% 48% 12% 4% 14% 12%6% 6% 2% 1% 1% -20% 0% 20% 40% 60% 80% 100% 2008 2009 2010 2011 2012 2013 What is the trends of attacker? Who is after us and Why?
- 10. 10 Monitor – Build capabilities that identify anomalies quickly and accurately. Establish a baseline. Protect – Build a set of layers to protect infrastructure based upon risk. Resilient – Build elastic and flexible capabilities that can compensate for each other and adapt to new threats. Awareness – Improve internal and external awareness around capabilities. Being smart about what you share externally. Monitor ProtectResilient Awareness How to Respond?
- 11. 11 Parrish Gunnels, Sr. Director and CISO of Information Security at Invitation Homes Parrish has more than 16 years of IT experience in various functions such as business analysis, project management, development, policy and process creation, business continuity management, internal / external audit, risk management and information security. He joined Invitation Homes, a Blackstone company, in February of this year. His experience includes working in multiple industries including financial services, telecommunications, and chemical manufacturing. Over the past few years, he has been focused on developing information security programs and securing existing networks through risk analysis, control definition, and user experience. Parrish holds a Master’s of Business Administration from Texas Christian University and certifications as a Professional Project Manager (PMP), Certified Information Systems Auditor (CISA), Certified in Risk and Information Systems Control (CRISC), and Certified Information Systems Security Professional (CISSP). Chris Ray, SVP and CISO at Epsilon, Inc. Since November 2011 and as CISO of Epsilon, Chris oversees many facets of information security, including security operations, incident response, identity management and regulatory compliance. Prior to Epsilon, Chris was the CISO at Aflac Corporation for 7½ years and responsible for Information Security and Software Change Management. He also started and oversaw the first infosec department at Healthsouth Corporation. Finally, Chris served as an active duty United States Air Force (USAF) enlisted airman and then officer for 13 years with another 8 years in the active USAF Reserves. He retired in 2009 after 21 years of service. For over a decade, he worked at the Air Force Information Warfare Center conducting global cyber-warfare and cyber-terrorism exercises to provide government agencies information warfare tactics, techniques and procedures. Chris holds a BS in Computer Science from the University of Texas at Austin and a CISSP (Certified Information Systems Security Professional) certification as well as an ISSMP concentration in management. Ron Mehring, Sr. Director and CISO of Information Security at Texas Health Resources Ron Mehring serves as the chief information security officer / senior director, information security for Texas Health Resources, one of the largest faith-based, nonprofit health care delivery systems in the United States. At Texas health Resources, Ron leads IT GRC, security architecture, security operations, and the IT BC DR program. His current initiatives are focused on improving team performance, improving resiliency management, integrating a threat-management architecture that accounts for present and emerging threats, and maturing a technology risk management program that is aligned with the strategic goals of the organization. Ron holds an MBA in Risk Management from NYIT and is a Certified Information Systems Security Professional (CISSP). About Our Panelists
