Recommended
Recommended
More Related Content
What's hot
What's hot (11)
IoT mobile app device cloud identity and security architecture

IoT mobile app device cloud identity and security architecture
Viewers also liked
Viewers also liked (15)
Opexa Therapeutics December 2015 Corporate Presentation

Opexa Therapeutics December 2015 Corporate Presentation
Similar to OCTOWIRE
2015년 4월 21일 서울 코엑스에서 열렸던 AWS Summit Seoul 2015의 첫번째 트랙에서 Markku Lepisto 아마존 웹서비스 테크 에반젤리스트와 윤석찬 테크 에반젤리스트가 발표한 자료입니다.AWS Summit Seoul 2015 - 모바일 및 IoT 환경을 위한 AWS 클라우드 플랫폼의 진화 (윤석찬, Markku Lepisto)

AWS Summit Seoul 2015 - 모바일 및 IoT 환경을 위한 AWS 클라우드 플랫폼의 진화 (윤석찬, Markku Lepisto)Amazon Web Services Korea
In which the author explains how to design large-scale cloud platforms for document processingBook Widget -- Embedding automated photo-document publication on the web and ...

Book Widget -- Embedding automated photo-document publication on the web and ...Eamonn O'Brien-Strain
Similar to OCTOWIRE (20)
Transforming The Customer Experience With Real-Time Insights

Transforming The Customer Experience With Real-Time Insights
AWS Summit Seoul 2015 - 모바일 및 IoT 환경을 위한 AWS 클라우드 플랫폼의 진화 (윤석찬, Markku Lepisto)

AWS Summit Seoul 2015 - 모바일 및 IoT 환경을 위한 AWS 클라우드 플랫폼의 진화 (윤석찬, Markku Lepisto)
Splunk - Verwandeln Sie Datensilos in Operational Intelligence

Splunk - Verwandeln Sie Datensilos in Operational Intelligence
Book Widget -- Embedding automated photo-document publication on the web and ...

Book Widget -- Embedding automated photo-document publication on the web and ...
OCTOWIRE
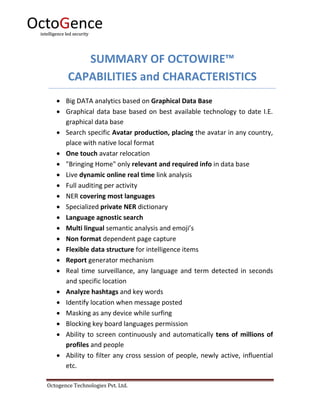
- 1. Octogence Technologies Pvt. Ltd. SUMMARY OF OCTOWIRE™ CAPABILITIES and CHARACTERISTICS Big DATA analytics based on Graphical Data Base Graphical data base based on best available technology to date I.E. graphical data base Search specific Avatar production, placing the avatar in any country, place with native local format One touch avatar relocation "Bringing Home" only relevant and required info in data base Live dynamic online real time link analysis Full auditing per activity NER covering most languages Specialized private NER dictionary Language agnostic search Multi lingual semantic analysis and emoji’s Non format dependent page capture Flexible data structure for intelligence items Report generator mechanism Real time surveillance, any language and term detected in seconds and specific location Analyze hashtags and key words Identify location when message posted Masking as any device while surfing Blocking key board languages permission Ability to screen continuously and automatically tens of millions of profiles and people Ability to filter any cross session of people, newly active, influential etc.
- 2. Octogence Technologies Pvt. Ltd. Ability to identify movers and shakers relative to a specific subject. Dark Web fully integrated. Integration of other sources such as crawlers SIGINT VISINT Location etc. (API) GUI supported in any language. Manage dynamic deep cover for unlimited avatars. Strong technical safeguards for maintaining avatar cover Organically log into and live undetected inside deep web sources. Capture and index any URL on the fly. Export avatars and related data for work on external computing resources, and import captured data back into HIWIRE™ database. Automatically create searchable and filterable audit log of all operator/avatar activity. Manage captured data in configurable structured format, i.e. case management. Assign cases to individuals or teams across the organization. Control data flow using fully fledged queue system. Enforce access permissions per user according to admin configurable roles. Encrypted alerts inside the system triggered by key case-related events. Support optional air-gap security mode of work, i.e. complete physical separation of case and data management from internet browsing. Providing full web intelligence cycle, starting at the Intelligence requirement through alerts and reports.