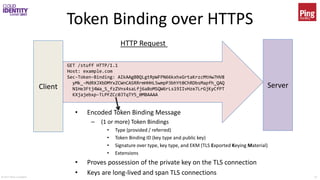
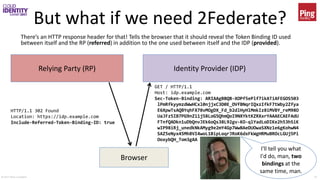
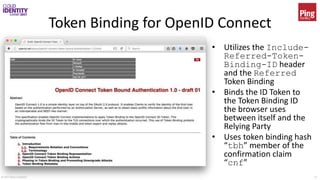
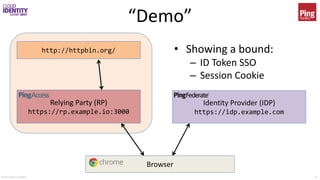
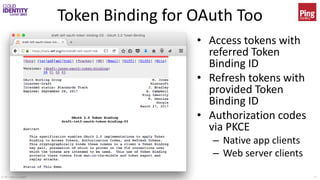
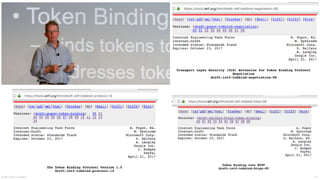
The document discusses bearer token binding as a method to enhance web security through a client-generated public-private key pair. It outlines the mechanism of token binding, its application in Single Sign-On (SSO) and OAuth 2.0, and emphasizes its privacy implications. The presentation also highlights ongoing developments in IETF token binding specifications and their adoption in various platforms.




![© 2017 Brian Campbell 11
Do you even bind tokens, bro?
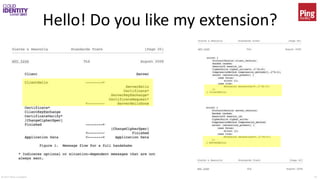
Client Server
ClientHello
...
token_binding [24]
token_binding_version [1,0]
key_parameters_list [2,0]
ServerHello
...
token_binding [24]
token_binding_version [1,0]
key_parameters_list [2]
Key Parameters:
(0) rsa2048_pkcs1.5
(1) rsa2048_pss
(2) ecdsap256
Also need extenstions:
Extended Master Secret
Renegotiation Indication
TLS Handshake](https://image.slidesharecdn.com/cis2017-campbell-tokenbinding-170620232740/85/Beyond-Bearer-Token-Binding-as-the-Foundation-for-a-More-Secure-Web-11-320.jpg)