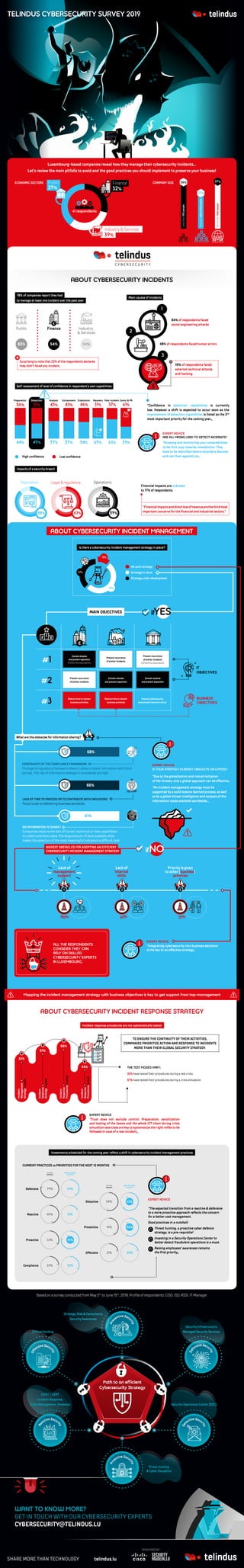
Luxembourg cybersecurity survey reveals incident response priorities
- 1. 000100 IDENTIFICATION DIVISION. 000200 PROGRAM-ID. HELLOWORLD. 000300 000400* 000500 ENVIRONMENT DIVISION. 000600 CONFIGURATION SECTION. 000700 SOURCE-COMPUTER. RM-COBOL. 000800 OBJECT-COMPUTER. RM-COBOL. 000900 001000 DATA DIVISION. 001100 FILE SECTION. Morethan500people Between100&500people Lessthan100people 36% 27% 37% 41 respondents Public 29% Finance 32% Industry & Services 39% Morethan500people Between100&500people Lessthan100people36% 27% 37% 41 respondents Public 29% Finance 32% Industry & Services 39% ECONOMIC SECTORS COMPANY SIZE 37% 27% Morethan500people Between100&500people Lessthan100people 36% 54% AFTER12MONTHS 63% 39%57% 43% 46% 31% 61%37% Defense Detection Reactive Preventive Proactive Compliance Offensive 79% 39% 40% 9% 9% 1%31% 15% 43% 54% 46% 41% 33% 23% 21% 15% 32% 20% 63% 56% 76% Containment Eradication Recovery Post-incident Comm. & PR 69% 1 23 37% 27% 56% Ope Morethan500people Between100&500people Lessthan100people 36% AFTER12MONTHS 34% Defense Detection Reactive Preventive Proactive Compliance Offensive 79% 39% 40% 9% 9% 1%31% 15% 43% 54% 46% 41% 33% 23% 21% 15% 32% 20% 63% 56% 76% 1 23 37% 27% Morethan500people Between100&500people Lessthan100people 36% AFTER12MONTHS 63% 39% 61%37% Defense Detection Reactive Preventive Proactive Compliance Offensive 79% 39% 40% 9% 9% 1%31% 15% 43% 54% 46% 41% 33% 23% 21% 15% 32% 20% 63% 56% 76% Post-incident Comm. & PR 1 23 84% of respondents faced social engineering attacks Main causes of incidents Luxembourg-based companies reveal how they manage their cybersecurity incidents… Let’s review the main pitfalls to avoid and the good practices you should implement to preserve your business! Impacts of a security breach “Integrating cybersecurity into business decisions is the key to an effective strategy„ EXPERT ADVICE telindus.lu 48% of respondents faced human errors What are the obstacles for information sharing? ABOUT CYBERSECURITY INCIDENTS 78% of companies report they had to manage at least one incident over the past year Public 83% Finance 54% Industry & Services 94% 19% of respondents faced external technical attacks and hacking Self-assessment of level of confidence in respondent’s own capabilities “Confidence in detection capabilities is currently low. However a shift is expected to occur soon as the improvement of detection capabilities is listed as the 2nd most important priority for the coming year„ Lessthan100people 36% 44% 49% 57% 54% 63% 39% 56% 51% 43% 57% 43% 46% 31% 61%37% Preparation Detection Analysis Containment Eradication Recovery Post-incident Comm. & PR 69% “Knowing and monitoring your vulnerabilities is the first step towards remediation. They have to be identified before attackers discover and use them against you„ EXPERT ADVICE ARE ALL MEANS USED TO DETECT INCIDENTS? ‘’Financialimpactsanddirectlossofrevenuearethethirdmost important concerns for the financial and industrial sectors.’’ Financial impacts are unknown to 17% of respondents. 44% 56% 22% During the last 12 MONTHS Operations ReputationLegal & regulatory Less than 6 (once every two months or less) Between 6 & 12 (once a month or less) More than 12 (more than once a month) None 46% 17% 14% 54% 50% 25% 66%34% 1 2 44% 56% 22% During the last 12 MONTHS Operations ReputationLegal & regulatory Less than 6 (once every two months or less) Between 6 & 12 (once a month or less) More than 12 (more than once a month) None 46% 17% 14% 54% 50% 25% 66%34% 1 2 2% Reputationlatory Less than 6 (once every two months or less) Between 6 & 12 (once a month or less) More than 12 (more than once a month) None 17% 14% % 25% 39% 29% 32% 41 respondents Finance Public Industry & Services Contain the attack and prevent expansion of the compromised set of IT assets Prevent recurrence of similar incidents Reduce time to recover to normal activity to preserve business activities Improve cybersecurity awareness and internal culture 44% 49% 57% 54% 63% 39% 56% 51% 43% 57% 43% 46% 31% 61%37% 51% 12% Preparation Detection Analysis Containment Eradication Recovery Post-incident Comm. 37% 69% Is there a cybersecurity incident management strategy in place? No such strategy Strategy in place Strategy under development “Due to the globalization and industrialization of the threats, only a global approach can be effective„ EXPERT ADVICE IS YOUR STRATEGY ALREADY OBSOLETE OR LIMITED? MAIN OBJECTIVES 53% 3 60% 2 Lack of internal skills Priority is given to other (business) activities 100% 1 ALL THE RESPONDENTS CONSIDER THEY CAN RELY ON SKILLED CYBERSECURITY EXPERTS IN LUXEMBOURG. 37% 27% 44% 56% 22% During the last 12 MONTHS Operations ReputationLegal & regulatory Less than 6 (once every two months o Between 6 & 12 (once a month or less) More than 12 (more than once a month None Morethan500people Between100&500people Lessthan100people 36% 46% 17% 14% 4% 49% 57% 54% AFTER12MONTHS 63% 39% 6% 51% 43% 57% 43% 46% 31% 61%37% 54% 50% 25% 66%34% 1 2 Defense Detection Reactive Preventive Proactive Compliance Offensive 79% 39% 40% 9% 9% 1%31% 15% 43% 54% 46% 41% 33% 23% 21% 15% 32% 20% 63% 56% 76% aration Detection Analysis Containment Eradication Recovery Post-incident Comm. & PR 69% 1 23 BIGGEST OBSTACLES FOR ADOPTING AN EFFICIENT CYBERSECURITY INCIDENT MANAGEMENT STRATEGY ABOUT CYBERSECURITY INCIDENT RESPONSE STRATEGY Incident response procedures are not systematically tested 66% 51% 44% Incident Response Proceduresinplace Incident Management Strategyinplace Incident Response Procedurestested 61% Incident Response Strategyinplace TO ENSURE THE CONTINUITY OF THEIR ACTIVITIES, COMPANIES PRIORITIZE ACTION AND RESPONSE TO INCIDENTS MORE THAN THEIR GLOBAL SECURITY STRATEGY. 33% have tested their procedures during a real crisis 67% have tested their procedures during a crisis simulation THE TEST MODES VARY: “Trust does not exclude control. Preparation, sensitization and testing of the teams and the whole ICT chain during crisis simulation exercises are key to systematize the right reflex to be followed in case of a real incident„ EXPERT ADVICE Mapping the incident management strategy with business objectives is key to get support from top-management Investments scheduled for the coming year reflect a shift in cybersecurity incident management practices CURRENT PRACTICES vs PRIORITIES FOR THE NEXT 12 MONTHS Defensive 79% 39% Detective 54% 63% Reactive 46% 15% Preventive 41% 56% Proactive 33% 76% Offensive 21% 20% Compliance 23% 32% Current Next 12 months Current Next 12 months WANT TO KNOW MORE? GET IN TOUCH WITH OUR CYBERSECURITY EXPERTS CYBERSECURITY@TELINDUS.LU Containattacks andpreventexpansion (100%oftherespondents) Prevent recurrence of similar incidents Prevent recurrence of similar incidents (100%oftherespondents) Prevent recurrence of similar incidents Reduce time to recover business activities Reduce time to recover business activities Improve cybersecurity awareness & internal culture Contain attacks and prevent expansion Contain attacks and prevent expansion 61% NO INFORMATION TO SHARE? Companies deplore the lack of human, technical or time capabilities to collect and share data. The large amount of data available often makes the selection of the most meaningful indicators a difficult task. CONSTRAINTS OF THE COMPLIANCE FRAMEWORK The legal & regulatory framework doesn’t allow to share information with third parties. The risk of information leakage is considered too high. LACK OF TIME TO PROCESS OR TO CONTRIBUTE WITH INDICATORS Focus is set on delivering business activities. 68% 66% Based on a survey conducted from May 5th to June 15th , 2019. Profile of respondents: CISO, ISO, RSSI, IT Manager. SPONSORED BY 59%63%88% ABOUT CYBERSECURITY INCIDENT MANAGEMENT ifYES ifNO Lack of management support “The expected transition from a reactive & defensive to a more proactive approach reflects the concern for a better cost management. Good practices in a nutshell: Threat hunting, a proactive cyber defence strategy, is a pre-requisite! Investing in a Security Operations Center to better detect fraudulent operations is a must. Raising employees’ awareness remains the first priority„ EXPERT ADVICE Strategy, Risk & Consultancy Security Awareness Security Infrastructure Managed Security Services Security Operations Center (SOC) Path to an efficient Cybersecurity Strategy CSIRT / CERT Incident Response, Crisis Management, Forensics Re active Secur ity Ethical Hacking Off ensive Secur ity Pre ventive Secu rity Def ensive Secu rity Det ective Secu rity Pro active Secu rity Threat hunting & Cyber Deception “An incident management strategy must be supported by a solid lessons learned process, as well as by a global threat intelligence and analysis of the information made available worldwide.„ Surprising to note that 22% of the respondents declares they didn’t faced any incident. € € € TELINDUS CYBERSECURITY SURVEY 2019
