Cyber Liability - Personal
•
0 likes•48 views
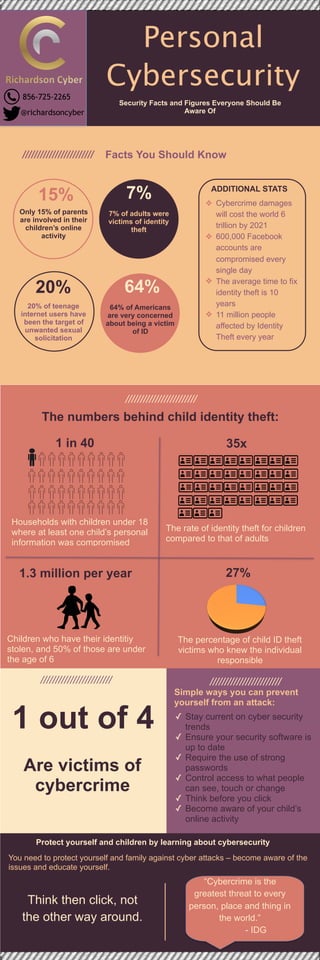
Stats illustrating the cyber liability faced by individuals.
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
Similar to Cyber Liability - Personal
Similar to Cyber Liability - Personal (20)
Info Session on Cybersecurity & Cybersecurity Study Jams

Info Session on Cybersecurity & Cybersecurity Study Jams
Protecting Your Business from Cybercrime - Cybersecurity 101

Protecting Your Business from Cybercrime - Cybersecurity 101
Preventing Nonprofit Banking Fraud and the Tools You Can Use!

Preventing Nonprofit Banking Fraud and the Tools You Can Use!
Center for Identity Webcast: The Internet of Things 

Center for Identity Webcast: The Internet of Things
Cyber CrimeAs Internet usage is growing daily the world is coming.pdf

Cyber CrimeAs Internet usage is growing daily the world is coming.pdf
Recently uploaded
Recently uploaded (20)
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
Unblocking The Main Thread Solving ANRs and Frozen Frames

Unblocking The Main Thread Solving ANRs and Frozen Frames
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
Injustice - Developers Among Us (SciFiDevCon 2024)

Injustice - Developers Among Us (SciFiDevCon 2024)
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...

Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...
Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...

Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...
Cyber Liability - Personal
- 1. Personal Cybersecurity Security Facts and Figures Everyone Should Be Aware Of //////////////////////// Facts You Should Know //////////////////////// The numbers behind child identity theft: //////////////////////// //////////////////////// 1 out of 4 Are victims of cybercrime Simple ways you can prevent yourself from an attack: ✓ Stay current on cyber security trends ✓ Ensure your security software is up to date ✓ Require the use of strong passwords ✓ Control access to what people can see, touch or change ✓ Think before you click ✓ Become aware of your child’s online activity 15% 7% 20% 64% ❖ Cybercrime damages will cost the world 6 trillion by 2021 ❖ 600,000 Facebook accounts are compromised every single day ❖ The average time to fix identity theft is 10 years ❖ 11 million people affected by Identity Theft every year ADDITIONAL STATS Only 15% of parents are involved in their children’s online activity 20% of teenage internet users have been the target of unwanted sexual solicitation 7% of adults were victims of identity theft 64% of Americans are very concerned about being a victim of ID Protect yourself and children by learning about cybersecurity You need to protect yourself and family against cyber attacks – become aware of the issues and educate yourself. Households with children under 18 where at least one child’s personal information was compromised 1 in 40 35x The rate of identity theft for children compared to that of adults 27% The percentage of child ID theft victims who knew the individual responsible Children who have their identitiy stolen, and 50% of those are under the age of 6 1.3 million per year “Cybercrime is the greatest threat to every person, place and thing in the world.” - IDG Think then click, not the other way around. 856-725-2265 @richardsoncyber
