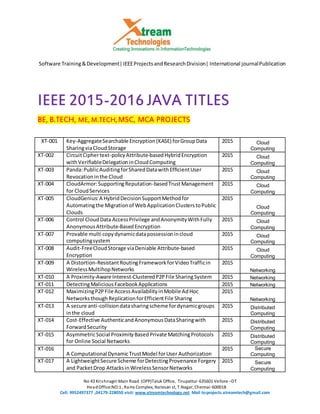
Ieee 2015 2016 java titles
- 1. Software Training&Development|IEEEProjectsandResearchDivision| International journalPublication No 43 Krishnagiri Main Road (OPP)Taluk Office, Tirupattur-635601 Vellore –DT HeadOffice:NO:1 , Rams Complex, Natesan st, T.Nagar, Chennai-600018 Cell: 9952497377 ,04179-228050 visit: www.xtreamtechnology.net Mail to:projects.xtreamtech@gmail.com IEEE 2015-2016JAVA TITLES BE, B.TECH, ME, M.TECH,MSC, MCA PROJECTS XT-001 Key-AggregateSearchable Encryption(KASE) forGroupData SharingviaCloudStorage 2015 Cloud Computing XT-002 CircuitCiphertext-policyAttribute-basedHybridEncryption withVerifiableDelegationinCloudComputing 2015 Cloud Computing XT-003 Panda:PublicAuditingforSharedDatawithEfficientUser Revocationinthe Cloud 2015 Cloud Computing XT-004 CloudArmor:SupportingReputation-basedTrustManagement for Cloud Services 2015 Cloud Computing XT-005 CloudGenius:A HybridDecisionSupportMethodfor Automatingthe Migrationof WebApplicationClusterstoPublic Clouds 2015 Cloud Computing XT-006 Control CloudData AccessPrivilege andAnonymityWithFully AnonymousAttribute-BasedEncryption 2015 Cloud Computing XT-007 Provable multi copydynamicdatapossessionincloud computingsystem 2015 Cloud Computing XT-008 Audit-FreeCloudStorage viaDeniable Attribute-based Encryption 2015 Cloud Computing XT-009 A Distortion-ResistantRoutingFrameworkforVideoTrafficin WirelessMultihopNetworks 2015 Networking XT-010 A Proximity-Aware Interest-ClusteredP2PFile SharingSystem 2015 Networking XT-011 DetectingMaliciousFacebookApplications 2015 Networking XT-012 MaximizingP2PFile AccessAvailabilityinMobile AdHoc NetworksthoughReplicationforEfficientFile Sharing 2015 Networking XT-013 A secure anti-collisiondatasharingscheme fordynamicgroups inthe cloud 2015 Distributed Computing XT-014 Cost-Effective AuthenticandAnonymousDataSharingwith ForwardSecurity 2015 Distributed Computing XT-015 AsymmetricSocial ProximityBasedPrivate MatchingProtocols for Online Social Networks 2015 Distributed Computing XT-016 A Computational DynamicTrustModel forUser Authorization 2015 Secure Computing XT-017 A LightweightSecure Scheme forDetectingProvenance Forgery and PacketDrop AttacksinWirelessSensorNetworks 2015 Secure Computing
- 2. Software Training&Development|IEEEProjectsandResearchDivision| International journalPublication No 43 Krishnagiri Main Road (OPP)Taluk Office, Tirupattur-635601 Vellore –DT HeadOffice:NO:1 , Rams Complex, Natesan st, T.Nagar, Chennai-600018 Cell: 9952497377 ,04179-228050 visit: www.xtreamtechnology.net Mail to:projects.xtreamtech@gmail.com XT-018 ContinuousandTransparent UserIdentityVerificationfor Secure InternetServices 2015 Secure Computing XT-019 Secure Data AggregationTechniqueforWirelessSensor Networksinthe Presence of CollusionAttacks 2015 Secure Computing XT-020 DDSGA: A Data-DrivenSemi-Global AlignmentApproachfor DetectingMasquerade Attacks 2015 Secure Computing XT-021 DesigningHighPerformanceWeb-BasedComputingServicesto Promote Telemedicine Database ManagementSystem 2015 Secure Computing XT-022 Location-Aware andPersonalized CollaborativeFilteringfor WebService Recommendation 2015 Service Computing XT-023 A Feature-BasedFrameworkforDevelopingandProvisioning Customizable WebServices 2015 Service Computing XT-024 AutomaticWebService CompositionBasedonUncertainty ExecutionEffects 2015 Service Computing XT-025 Constructinga Global Social Service NetworkforBetterQuality of WebService Discovery 2015 Service Computing XT-026 UnifiedCollaborative andContent-BasedWebService Recommendation 2015 Service Computing XT-027 A Computational DynamicTrustModel forUser Authorization 2015 Service Computing XT-028 Context-BasedDiversificationforKeywordQueriesoverXML Data 2015 Data Mining XT-029 PrivacyPolicyInference of User-UploadedImagesonContent SharingSites 2015 Data Mining XT-030 Scalable ConstrainedSpectral Clustering 2015 Data Mining XT-031 Route-Saver:LeveragingRoute APIsforAccurate andEfficient QueryProcessingatLocation-BasedServices 2015 Data Mining XT-032 TweetSegmentation andItsApplicationtoNamedEntity Recognition 2015 Data Mining