Why Should by Wi-Fi be PCI Compliant?
*** Companion blog http://blog.airtightnetworks.com/pci-3-1-guidelines-ssl-vulnerability *** Companion whitepapers: 1) Do My Security Controls Achieve Wireless PCI DSS? PCI Compliance in the New World of Threats – whitepaper [PDF] http://go.airtightnetworks.com/PCI_DSS_3.1_Whitepaper_Impact_on_Wi-Fi_Security.html 2) PCI 3.1 and the Impact on Wi-Fi Security – whitepaper [PDF] http://go.airtightnetworks.com/PCI_DSS_3.1_Compliance_In_A_New_World_Of_Threats.html *** Companion webinar: Do my security controls achieve the spirit of wireless PCI DSS? Register for the webinar: May 5th 8am PDT [on-demand] https://attendee.gotowebinar.com/register/3592031186368052738 --------- On April 15th 2015, the PCI Security Standards Council (PCI SSC) published PCI Data Security Standard (PCI DSS) Version 3.1 and supporting guidance. The revision addresses vulnerabilities within the Secure Sockets Layer (SSL) encryption protocol that can put payment data at risk. Available now on the PCI SSC website, PCI 3.1 is effective immediately. https://www.pcisecuritystandards.org/security_standards/documents.php >>> PCI DSS 3.0 will be retired on 30 June 2015. <<< PCI SSC explains: https://www.pcisecuritystandards.org/pdfs/15_04_15%20PCI%20DSS%203%201%20Press%20Release.pdf “The National Institute of Standards and Technology (NIST) identified SSL (a cryptographic protocol designed to provide secure communications over a computer network) as not being acceptable for the protection of data due to inherent weaknesses within the protocol. Upgrading to a current, secure version of Transport Layer Security (TLS), the successor protocol to SSL, is the only known way to remediate these vulnerabilities, which have been exploited by browser attacks such as POODLE and BEAST.” Source: PCI Council Publishes Revision to PCI Data Security Standard — PCI DSS 3.1 and supporting guidance helps organizations address vulnerabilities within SSL protocol that put payment data at risk; PA-DSS revision to follow — PCI Security Council, April 2015.
Recommended
Recommended
More Related Content
Recently uploaded
Recently uploaded (20)
Featured
Featured (20)
Why Should by Wi-Fi be PCI Compliant?
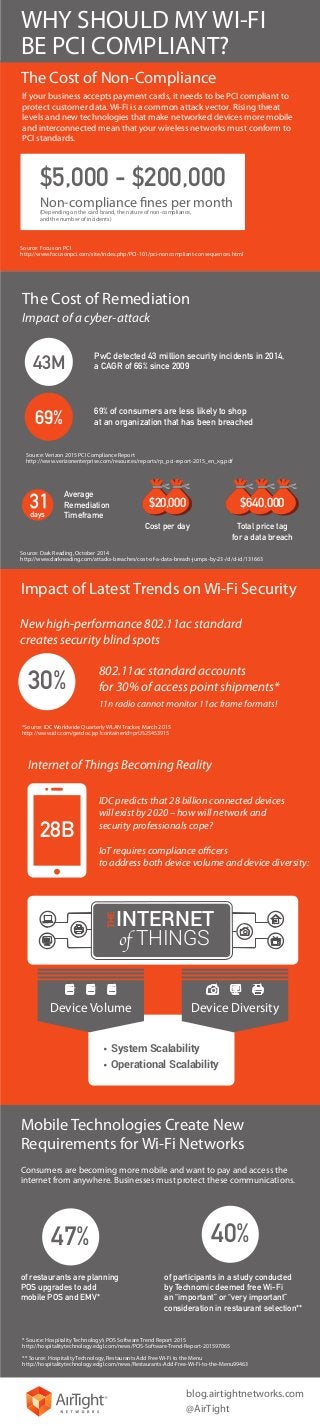
- 1. Source: Focus on PCI http://www.focusonpci.com/site/index.php/PCI-101/pci-noncompliant-consequences.html Source: Verizon 2015 PCI Compliance Report http://www.verizonenterprise.com/resources/reports/rp_pci-report-2015_en_xg.pdf The Cost of Non-Compliance WHY SHOULD MY WI-FI BE PCI COMPLIANT? Impact of Latest Trends on Wi-Fi Security Internet of Things Becoming Reality Source: Dark Reading, October 2014 http://www.darkreading.com/attacks-breaches/cost-of-a-data-breach-jumps-by-23-/d/d-id/131663 *Source: IDC Worldwide Quarterly WLAN Tracker, March 2015 http://www.idc.com/getdoc.jsp?containerId=prUS25453915 The Cost of Remediation $5,000 - $200,000 Non-compliance fines per month (Depending on the card brand, the nature of non-compliance, and the number of incidents) Cost per day $20,000 Total price tag for a data breach $640,000 Average Remediation Timeframedays Impact of a cyber-attack New high-performance 802.11ac standard creates security blind spots IDC predicts that 28 billion connected devices will exist by 2020 – how will network and security professionals cope? IoT requires compliance officers to address both device volume and device diversity: 30% 43M 69% 28B 802.11ac standard accounts for 30% of access point shipments* 11n radio cannot monitor 11ac frame formats! THE INTERNET of THINGS Device Volume Device Diversity System Scalability Operational Scalability Mobile Technologies Create New Requirements for Wi-Fi Networks 40%47% of restaurants are planning POS upgrades to add mobile POS and EMV* of participants in a study conducted by Technomic deemed free Wi-Fi an “important” or “very important” consideration in restaurant selection** * Source: Hospitality Technology’s POS Software Trend Report 2015 http://hospitalitytechnology.edgl.com/news/POS-Software-Trend-Report-201597065 ** Source: Hospitality Technology, Restaurants Add Free Wi-Fi to the Menu http://hospitalitytechnology.edgl.com/news/Restaurants-Add-Free-Wi-Fi-to-the-Menu99463 blog.airtightnetworks.com @AirTight If your business accepts payment cards, it needs to be PCI compliant to protect customer data. Wi-Fi is a common attack vector. Rising threat levels and new technologies that make networked devices more mobile and interconnected mean that your wireless networks must conform to PCI standards. Consumers are becoming more mobile and want to pay and access the internet from anywhere. Businesses must protect these communications. 69% of consumers are less likely to shop at an organization that has been breached PwC detected 43 million security incidents in 2014, a CAGR of 66% since 2009
