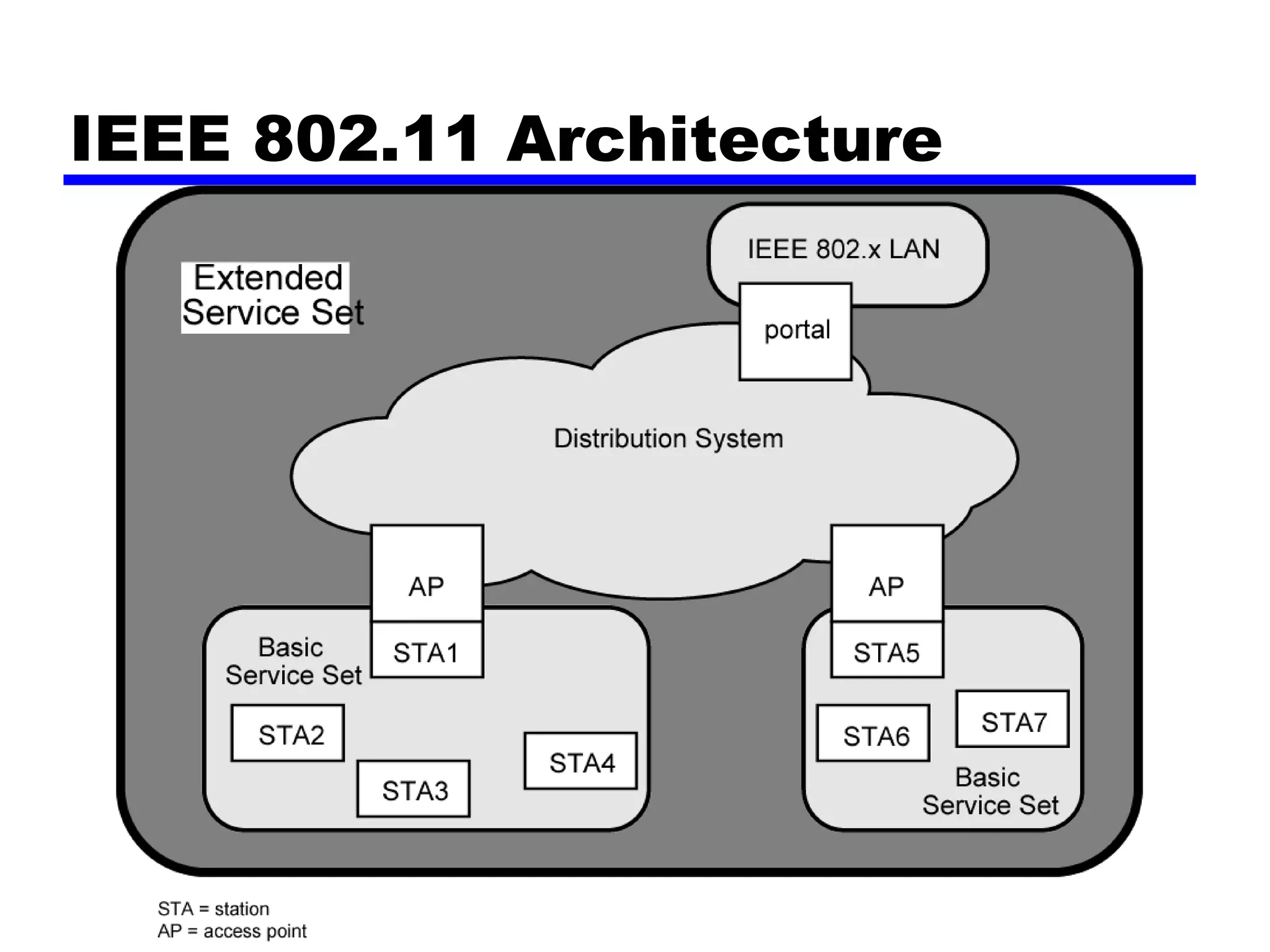
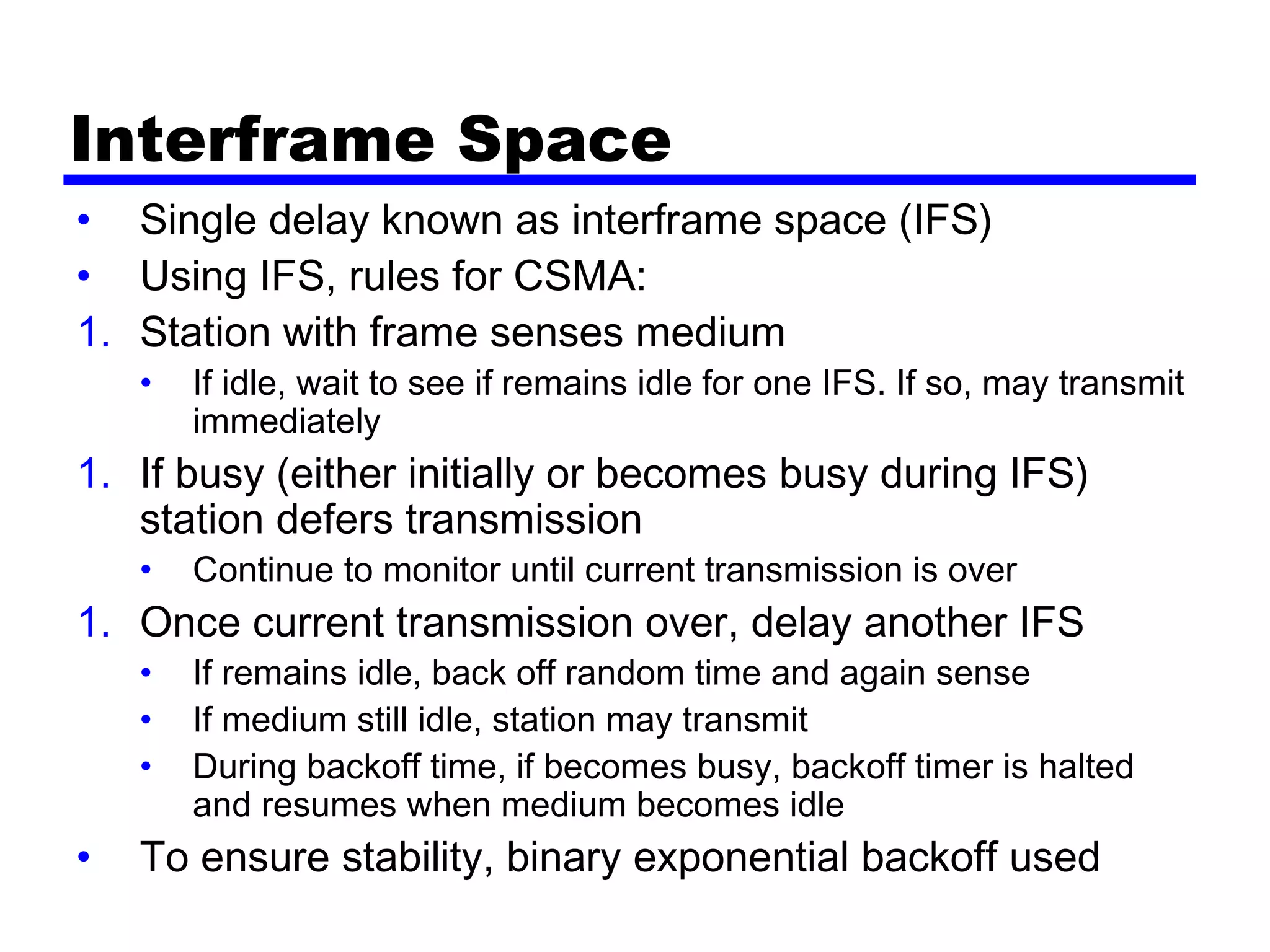
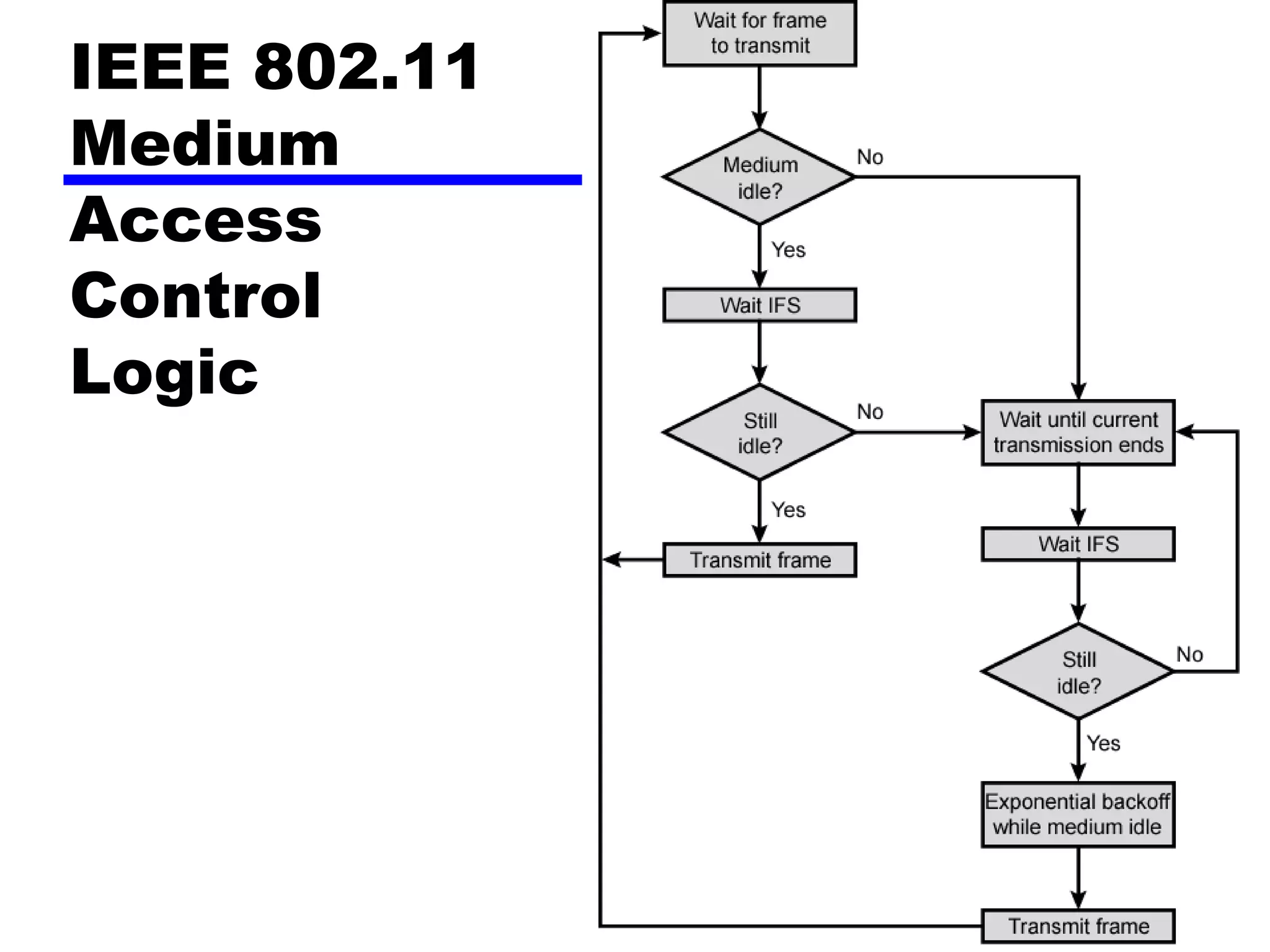
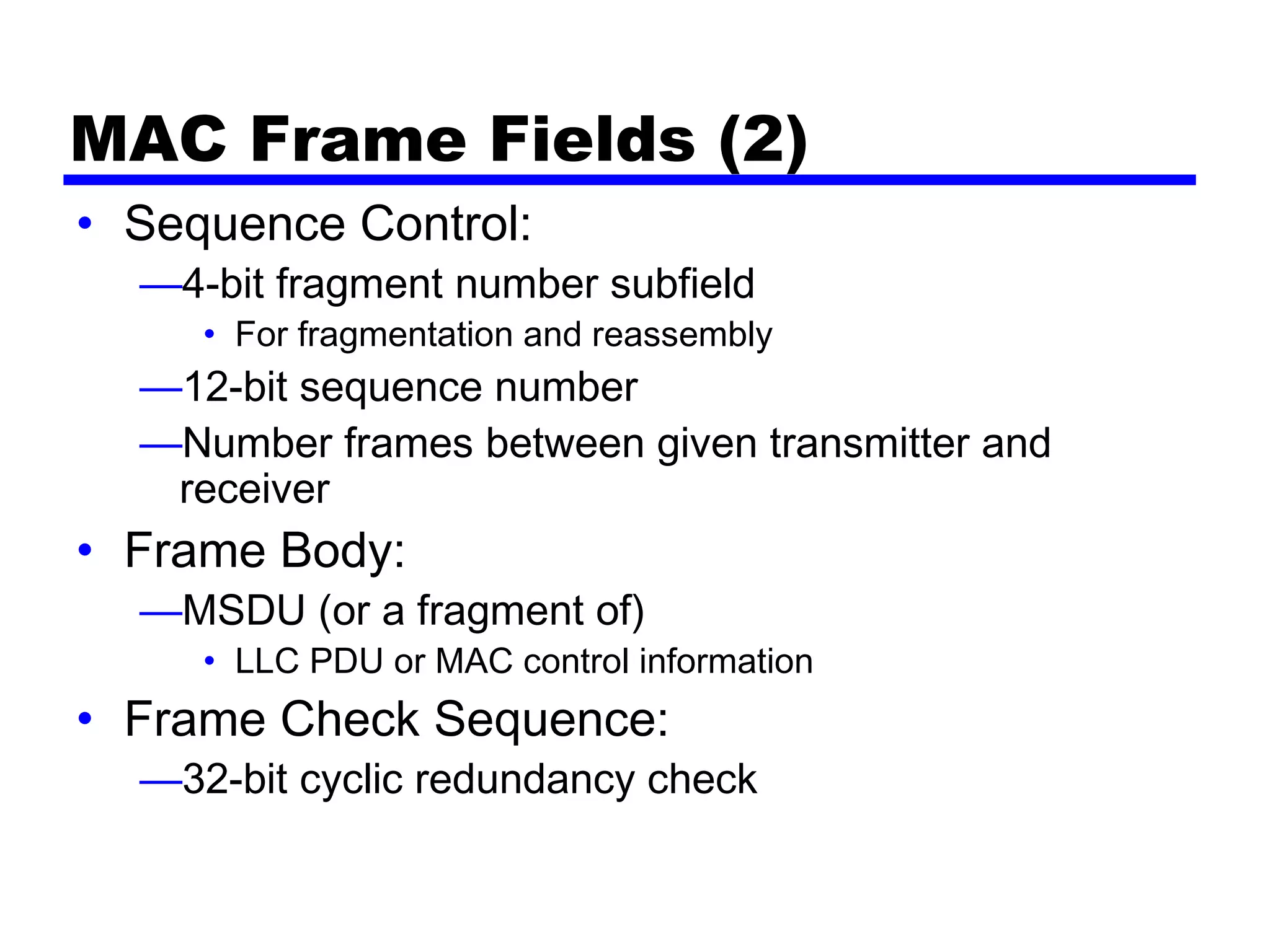
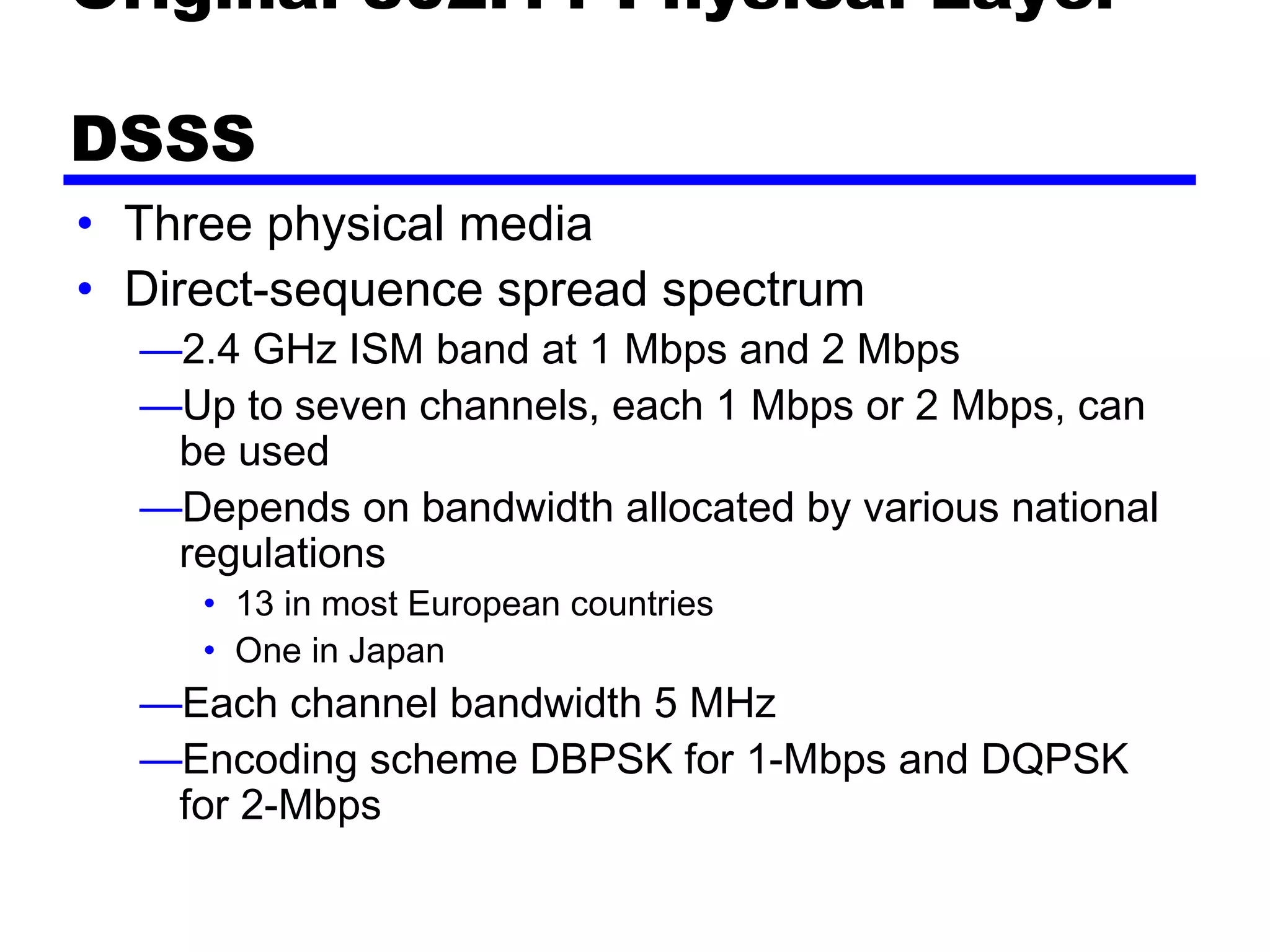
Wireless LANs use radio waves to connect devices within a local area network, avoiding the need to install network cabling. They can extend an existing wired LAN or provide connectivity in situations where wired infrastructure is not practical. The 802.11 standards define the specifications for implementing wireless LAN technology, including the media access control protocol and various physical layer options. Key components include access points, basic service sets, and an extended service set to interconnect multiple basic service sets over a distribution system.