What Is Cyber Security & Why We Need Cyber Security Expert – Lode Palle.pdf
•
0 likes•2 views
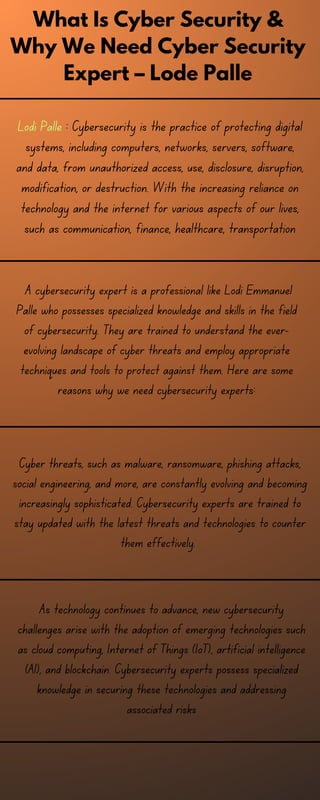
Lodi Palle : Cybersecurity is the practice of protecting digital systems, including computers, networks, servers, software, and data, from unauthorized access, use, disclosure, disruption, modification, or destruction. With the increasing reliance on technology and the internet for various aspects of our lives, such as communication, finance, healthcare, transportation, and more, the need for robust cybersecurity measures has become critical to safeguard against cyber threats.
Report
Share
Report
Share
Download to read offline
Recommended
The Future of Cybersecurity courses.pptx

Cybersecurity encompasses a set of practices, technologies, processes, and measures designed to protect digital systems, networks, devices, and data from cyber threats, unauthorized access, and malicious attacks.
Stay Ahead of Threats The Importance of Cyber Security Services.pdf

The role of cyber security services in safeguarding our digital existence cannot be overstated. As we delve deeper into the digital age, protecting against cyber threats becomes not just about defence but ensuring our digital endeavours’ continued success and safety. Proactive cyber security is an investment in the future, a shield against the unknown, and a commitment to the digital safety of our businesses and personal lives. please visit: https://sads.com/insights/stay-ahead-of-threats-the-importance-of-cyber-security-services/
cyber security services | MasGlobal Services

MasGlobal is a one-stop shop for cyber security consulting services in the USA. We provide cyber security services to protect systems, networks, programs, devices, and data from cyberattacks.
For more information: https://www.masglobalservices.com/services/
Top Industries Looking for Cyber Security Experts.pdf

With cyber-crimes taking a toll on almost all the industries out there, there is a rising demand for cyber security experts. From finance to healthcare to defense, and more, industries all across the world are actively hunting for cybersecurity specialists. Businesses worldwide are also flexible to offer high pay packages, thereby assuring a thriving career opportunity for cybersecurity professionals. The blog offers a brief on the top industries that are looking for skilled cyber security experts.
CYBERSECURITYcoll[1].pptx![CYBERSECURITYcoll[1].pptx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![CYBERSECURITYcoll[1].pptx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
cyber security is now days mostly
trending in market
CYBERSECURITY
Cybersecurity is crucial in today's digital world. Let's explore the importance of protecting our data, the types of threats we face, and how to stay secure
Proactive Cyber Security: Protecting Your Digital World
ICT Security 262112 in Australia.pptx

ICT Security Specialists serve as guardians of the digital realm, protecting organizations and individuals from evolving cyber threats. Their expertise is crucial in preserving the integrity and security of RPL Australia's digital landscape.
Cybersecurity- Role of FinTech 

Cybersecurity is essential to protect your computer, servers, electronic devices, mobile devices, and networks from malicious and unauthorized attacks. Every day, tons of data is shared across different platforms. This data is sometimes confidential; at other times, it is sensitive. There is always a threat to such data. Therefore, robust cybersecurity is a crucial requirement for every organization.
Recommended
The Future of Cybersecurity courses.pptx

Cybersecurity encompasses a set of practices, technologies, processes, and measures designed to protect digital systems, networks, devices, and data from cyber threats, unauthorized access, and malicious attacks.
Stay Ahead of Threats The Importance of Cyber Security Services.pdf

The role of cyber security services in safeguarding our digital existence cannot be overstated. As we delve deeper into the digital age, protecting against cyber threats becomes not just about defence but ensuring our digital endeavours’ continued success and safety. Proactive cyber security is an investment in the future, a shield against the unknown, and a commitment to the digital safety of our businesses and personal lives. please visit: https://sads.com/insights/stay-ahead-of-threats-the-importance-of-cyber-security-services/
cyber security services | MasGlobal Services

MasGlobal is a one-stop shop for cyber security consulting services in the USA. We provide cyber security services to protect systems, networks, programs, devices, and data from cyberattacks.
For more information: https://www.masglobalservices.com/services/
Top Industries Looking for Cyber Security Experts.pdf

With cyber-crimes taking a toll on almost all the industries out there, there is a rising demand for cyber security experts. From finance to healthcare to defense, and more, industries all across the world are actively hunting for cybersecurity specialists. Businesses worldwide are also flexible to offer high pay packages, thereby assuring a thriving career opportunity for cybersecurity professionals. The blog offers a brief on the top industries that are looking for skilled cyber security experts.
CYBERSECURITYcoll[1].pptx![CYBERSECURITYcoll[1].pptx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![CYBERSECURITYcoll[1].pptx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
cyber security is now days mostly
trending in market
CYBERSECURITY
Cybersecurity is crucial in today's digital world. Let's explore the importance of protecting our data, the types of threats we face, and how to stay secure
Proactive Cyber Security: Protecting Your Digital World
ICT Security 262112 in Australia.pptx

ICT Security Specialists serve as guardians of the digital realm, protecting organizations and individuals from evolving cyber threats. Their expertise is crucial in preserving the integrity and security of RPL Australia's digital landscape.
Cybersecurity- Role of FinTech 

Cybersecurity is essential to protect your computer, servers, electronic devices, mobile devices, and networks from malicious and unauthorized attacks. Every day, tons of data is shared across different platforms. This data is sometimes confidential; at other times, it is sensitive. There is always a threat to such data. Therefore, robust cybersecurity is a crucial requirement for every organization.
How Modern Cybersecurity Software Shields Against the Latest Threats.pdf

Modern cybersecurity software is designed to integrate seamlessly with other security tools and systems. This allows for a unified security posture that can more effectively detect, prevent, and respond to threats. Integration with threat intelligence platforms, SIEM (Security Information and Event Management) systems, and other security solutions enhances the overall effectiveness of cybersecurity defenses. As cyber threats continue to evolve, so too will the cybersecurity solutions offered by companies like Webtrills. By leveraging advanced technologies, such as machine learning and AI, and maintaining a proactive, intelligence-driven approach to cybersecurity, Webtrills aims to not only respond to the current threat landscape but also anticipate and neutralize future challenges.
AI IN CYBERSECURITY: THE NEW FRONTIER OF DIGITAL PROTECTION

Artificial Intelligence (AI) fortifies cybersecurity by dynamically identifying and neutralizing cyber threats. With machine learning algorithms, AI analyzes patterns in real-time data, swiftly detecting anomalies and potential security breaches. This proactive approach enhances the overall defense mechanism, ensuring robust protection against evolving cyber threats in the ever-changing digital landscape.
Cyber security cdg.io

Cyber Defense Group is a trusted cyber security consultancy located in Los Angeles, CA formed by cyber security professionals from multiple industries.
What is Cybersecurity and career paths.

Dive into the world of cybersecurity with our latest blog post, "Navigating the Digital Frontier: Exploring Cybersecurity and Its Lucrative Career Opportunities." 🛡️💻
In today's interconnected digital landscape, the significance of cybersecurity cannot be underestimated. Our blog takes you on a journey to understand the essence of cybersecurity - the art and science of safeguarding computer systems, networks, and data from cyber threats. Discover the pivotal role it plays in maintaining confidentiality, integrity, and availability of information in an age where technology shapes every aspect of our lives.
Are you intrigued by the idea of becoming a guardian of the digital realm? Our blog unveils the plethora of exciting career opportunities that cybersecurity offers. From cybersecurity analysts who monitor and respond to security incidents, to ethical hackers who use their skills for good, and security architects who design robust defense systems – the possibilities are as diverse as your interests.
The digital age calls for modern heroes - those who can defend against hackers, thwart data breaches, and ensure the secure transmission of information. As you read through our blog, you'll gain insights into the skills and knowledge required to thrive in this field. Explore the roles of security consultants who provide expert guidance, incident responders who act swiftly in times of crisis, and cryptographers who create secure communication methods.
Are you ready to embrace a career that not only promises personal growth but also contributes to the digital safety of our interconnected world? Join us in uncovering the dynamic world of cybersecurity and discover how you can play a crucial role in shaping a secure digital future. Read our blog now and become part of the next generation of cybersecurity experts! 🌐🔒🚀
ATS Connection.pdf

ATS Connection
15, Old Printing House Square, Tarrant St, Arundel BN18 9JH, United Kingdom
+441903255159
https://atsconnection.co.uk/
https://www.google.com/maps?cid=6871096897964695418
Cyber Security Mastery.pdf

Cybersecurity mastery is a critical skill set in today's digital age, where cyber threats are becoming increasingly frequent and sophisticated. By mastering cybersecurity, individuals and organisations can better protect themselves against cyberattacks and minimise the risk of data breaches and other cyber incidents.
Cyber security course in India - GICSEH.pdf

One of the greatest cyber security courses available in India is provided by GICSEH, which also offers thorough instruction and the development of useful skills.
Call us for Detailed Information: 8800955639
Get Started with Cyber Security and Its Landscape Null Community Presentation...

Get Started with Cyber Security and Its Landscape Null Community Presentation...null - The Open Security Community
Get Started with Cyber Security and Its landscape-
null Kolkata Meet 16 September 2023 Monthly Meetup What is Cyber Security - Avantika University

What is Cyber Security? Cyber Security is the practice of defending or controlling the systems, programs, networks, data, and devices from unauthorized access to data and baleful threats. Many aspiring students are enrolling in Top Engineering colleges in MP to make a bright career in Cyber Security.
To get more details, visit us at : https://www.avantikauniversity.edu.in/engineering-colleges/what-is-cyber-security.php
Advance Your Career with Cyber Security Training in Kerala

Boost your IT career with our cyber security courses in Kerala. Hands-on training, latest tools, and techniques. Secure your future in the growing field of IT security!
Malware Forensic Expertise: Analyzing and Neutralizing Cyber Threats.pdf

Malware Forensic Expertise: Analyzing and Neutralizing Cyber Threats
Cyber Security in the Modern World 1.pdf

Strong cybersecurity practises are essential in the current world to safeguard your digital assets and sensitive data. Utilise secure networks, data encryption, and strict access controls to protect against growing cyber threats. Regular security training, incident response planning, and adherence to industry regulations will help you stay one step ahead of thieves. To build a safer online environment, embrace innovative technology while reducing hazards and encourage collaboration. Discover the value of cybersecurity in today's networked society and learn how to protect your online presence from disruptions, unauthorised access, and data breaches.
Cybersecurity In IoT Challenges And Effective Strategies.pdf

Explore the world of IoT cybersecurity. Expose challenges and discover effective strategies to secure your digital security. Stay secure in the dynamical landscape of cybersecurity in IoT.
Fortifying the Digital Frontier Exploring the Crucial Dimensions of Cyber sec...

In an era defined by the proliferation of digital technology, the significance of cybersecurity has escalated to unprecedented heights. With each passing day, our reliance on interconnected systems, online transactions, and digital communication grows, underscoring the imperative need to safeguard our digital world from an array of malicious threats. Diploma In Cloud Computing & Cyber Security.
40 under 40 in cybersecurity. top cyber news magazine

40 under 40 in cybersecurity. top cyber news magazine
40 under 40 in Cybersecurity 2022. Top Cyber News MAGAZINE

Own Your Future!
“It is time for us all to stand and cheer for the doer, the achiever - the one who recognizes the challenges and does something about it.” Vince Lombardi
ONLY talents! NO ranking here!
With the global skills shortage, it is crucial to encourage talents who dedicate their life and career to cybersecurity.
This special edition spotlights remarkable cybersecurity and industry 4.0 professionals. Top Cyber News Magazine is pleased to unveil a constellation of young and devoted men and women: amabasadors, erudites, and influencers.
All, part and inspiring force behind the global Cybersecurity Awareness movement. These talented experts and brilliant people coming from nineteen countries and five continents.
I invite you to discover these wonderful people. Speak about them. See the light in others and you will be stunned how this light comes back to you! Enjoy reading! Share! Learn!
40 under 40! Move to the Front Lines!
Editorial by Steve KING
Managing Director at CyberTheory
As the gap expands between supply and demand in cybersecurity skills, we now see over 70 online eLearning courses available that focus across a wide range of upskilling opportunities from data privacy to compliance to risk and vulnerability assessment and audit. As we celebrate our newest class of 40 under 40, we are optimistic that this generation of cybersecurity enthusiasts are interested in the actual battle zones upon which our current war is being fought and not on preparation for the administrative roles which are also necessary in battle, yet not feeling the pressure from the current skills gap.
In our work with our own eLearning platform, CyberEd.io, we have discovered that the key employment opportunities lie along the front lines of deployment, where trained cyber-warriors are so necessary not just to defend our critical assets but to serve as a deterrent to the flood of cyber-criminals assaulting our fortresses. Every CISO we talk to confirms this requirement with both anecdotal and empirical evidence that is leading to almost daily breaches across all industrial sectors with specific threats to banking, education, healthcare, military and industrial control systems in automated factories (OT).
The cyber-warrior education career path starts with a solid grasp of network engineering fundamentals, followed by security architecture & engineering with an emphasis on Cloud/SysOps/*nix (*Unix/Linux Linux, FreeBSD, and Mac OS X), ICS/IoT, identity access management, security assessment & testing, current threat profiles and malware infrastructure and architecture, vector identification, incident detection, security operations with forensics and incident handling, pen testing, and exploitation.
Without properly trained resources in advanced cyber-warfare, we will never prevail in our constant challenge to protect and defend, let alone being able to take the threat to the enemy. As more and more entry candidates choose training to prepare them for ...
Guarding the Digital Fortress Unmasking 10 Common Types of Cybersecurity Thre...

To guard our digital assets and ourselves from cyber threats, it’s crucial to be vigilant and proactive. Understanding common varieties of threats is essential, but enforcing preventive measures is likewise important. In the present-day virtual age, cybersecurity is a shared obligation. Adopting sturdy password practices, staying vigilant against phishing attempts, and keeping software programs up-to-date can lessen publicity to threats. https://mverve.com/
Guarding the Digital Fortress.pdf

To know how we can protect the data, firstly we need to know how someone can steal it. And in this blog, we will address the 10 common cyber security threats that are most prevalent and also the preventive measures that we can take to control them.
https://mverve.com/
Insights from Lode Palle Demystifying Desktop Application Development.pptx

In the ever-evolving landscape of technology, desktop applications remain a cornerstone of digital innovation, providing users with powerful tools and seamless experiences across various platforms. Lode Palle, a seasoned expert in software development, offers valuable insights into the intricacies of desktop application development, shedding light on its significance, challenges, and best practices.
Lode Emmanuel Palle - Real-Time Communication in Full Stack Applications.pptx

Lode Emmanuel Palle, a proficient advocate for cutting-edge technologies, offers illuminating insights into the intricate mechanisms and practical applications of real-time communication within full stack applications. At its core, real-time communication enables seamless, bidirectional data flow between clients and servers, eliminating the need for manual page refreshes and enabling dynamic, interactive user experiences.
More Related Content
Similar to What Is Cyber Security & Why We Need Cyber Security Expert – Lode Palle.pdf
How Modern Cybersecurity Software Shields Against the Latest Threats.pdf

Modern cybersecurity software is designed to integrate seamlessly with other security tools and systems. This allows for a unified security posture that can more effectively detect, prevent, and respond to threats. Integration with threat intelligence platforms, SIEM (Security Information and Event Management) systems, and other security solutions enhances the overall effectiveness of cybersecurity defenses. As cyber threats continue to evolve, so too will the cybersecurity solutions offered by companies like Webtrills. By leveraging advanced technologies, such as machine learning and AI, and maintaining a proactive, intelligence-driven approach to cybersecurity, Webtrills aims to not only respond to the current threat landscape but also anticipate and neutralize future challenges.
AI IN CYBERSECURITY: THE NEW FRONTIER OF DIGITAL PROTECTION

Artificial Intelligence (AI) fortifies cybersecurity by dynamically identifying and neutralizing cyber threats. With machine learning algorithms, AI analyzes patterns in real-time data, swiftly detecting anomalies and potential security breaches. This proactive approach enhances the overall defense mechanism, ensuring robust protection against evolving cyber threats in the ever-changing digital landscape.
Cyber security cdg.io

Cyber Defense Group is a trusted cyber security consultancy located in Los Angeles, CA formed by cyber security professionals from multiple industries.
What is Cybersecurity and career paths.

Dive into the world of cybersecurity with our latest blog post, "Navigating the Digital Frontier: Exploring Cybersecurity and Its Lucrative Career Opportunities." 🛡️💻
In today's interconnected digital landscape, the significance of cybersecurity cannot be underestimated. Our blog takes you on a journey to understand the essence of cybersecurity - the art and science of safeguarding computer systems, networks, and data from cyber threats. Discover the pivotal role it plays in maintaining confidentiality, integrity, and availability of information in an age where technology shapes every aspect of our lives.
Are you intrigued by the idea of becoming a guardian of the digital realm? Our blog unveils the plethora of exciting career opportunities that cybersecurity offers. From cybersecurity analysts who monitor and respond to security incidents, to ethical hackers who use their skills for good, and security architects who design robust defense systems – the possibilities are as diverse as your interests.
The digital age calls for modern heroes - those who can defend against hackers, thwart data breaches, and ensure the secure transmission of information. As you read through our blog, you'll gain insights into the skills and knowledge required to thrive in this field. Explore the roles of security consultants who provide expert guidance, incident responders who act swiftly in times of crisis, and cryptographers who create secure communication methods.
Are you ready to embrace a career that not only promises personal growth but also contributes to the digital safety of our interconnected world? Join us in uncovering the dynamic world of cybersecurity and discover how you can play a crucial role in shaping a secure digital future. Read our blog now and become part of the next generation of cybersecurity experts! 🌐🔒🚀
ATS Connection.pdf

ATS Connection
15, Old Printing House Square, Tarrant St, Arundel BN18 9JH, United Kingdom
+441903255159
https://atsconnection.co.uk/
https://www.google.com/maps?cid=6871096897964695418
Cyber Security Mastery.pdf

Cybersecurity mastery is a critical skill set in today's digital age, where cyber threats are becoming increasingly frequent and sophisticated. By mastering cybersecurity, individuals and organisations can better protect themselves against cyberattacks and minimise the risk of data breaches and other cyber incidents.
Cyber security course in India - GICSEH.pdf

One of the greatest cyber security courses available in India is provided by GICSEH, which also offers thorough instruction and the development of useful skills.
Call us for Detailed Information: 8800955639
Get Started with Cyber Security and Its Landscape Null Community Presentation...

Get Started with Cyber Security and Its Landscape Null Community Presentation...null - The Open Security Community
Get Started with Cyber Security and Its landscape-
null Kolkata Meet 16 September 2023 Monthly Meetup What is Cyber Security - Avantika University

What is Cyber Security? Cyber Security is the practice of defending or controlling the systems, programs, networks, data, and devices from unauthorized access to data and baleful threats. Many aspiring students are enrolling in Top Engineering colleges in MP to make a bright career in Cyber Security.
To get more details, visit us at : https://www.avantikauniversity.edu.in/engineering-colleges/what-is-cyber-security.php
Advance Your Career with Cyber Security Training in Kerala

Boost your IT career with our cyber security courses in Kerala. Hands-on training, latest tools, and techniques. Secure your future in the growing field of IT security!
Malware Forensic Expertise: Analyzing and Neutralizing Cyber Threats.pdf

Malware Forensic Expertise: Analyzing and Neutralizing Cyber Threats
Cyber Security in the Modern World 1.pdf

Strong cybersecurity practises are essential in the current world to safeguard your digital assets and sensitive data. Utilise secure networks, data encryption, and strict access controls to protect against growing cyber threats. Regular security training, incident response planning, and adherence to industry regulations will help you stay one step ahead of thieves. To build a safer online environment, embrace innovative technology while reducing hazards and encourage collaboration. Discover the value of cybersecurity in today's networked society and learn how to protect your online presence from disruptions, unauthorised access, and data breaches.
Cybersecurity In IoT Challenges And Effective Strategies.pdf

Explore the world of IoT cybersecurity. Expose challenges and discover effective strategies to secure your digital security. Stay secure in the dynamical landscape of cybersecurity in IoT.
Fortifying the Digital Frontier Exploring the Crucial Dimensions of Cyber sec...

In an era defined by the proliferation of digital technology, the significance of cybersecurity has escalated to unprecedented heights. With each passing day, our reliance on interconnected systems, online transactions, and digital communication grows, underscoring the imperative need to safeguard our digital world from an array of malicious threats. Diploma In Cloud Computing & Cyber Security.
40 under 40 in cybersecurity. top cyber news magazine

40 under 40 in cybersecurity. top cyber news magazine
40 under 40 in Cybersecurity 2022. Top Cyber News MAGAZINE

Own Your Future!
“It is time for us all to stand and cheer for the doer, the achiever - the one who recognizes the challenges and does something about it.” Vince Lombardi
ONLY talents! NO ranking here!
With the global skills shortage, it is crucial to encourage talents who dedicate their life and career to cybersecurity.
This special edition spotlights remarkable cybersecurity and industry 4.0 professionals. Top Cyber News Magazine is pleased to unveil a constellation of young and devoted men and women: amabasadors, erudites, and influencers.
All, part and inspiring force behind the global Cybersecurity Awareness movement. These talented experts and brilliant people coming from nineteen countries and five continents.
I invite you to discover these wonderful people. Speak about them. See the light in others and you will be stunned how this light comes back to you! Enjoy reading! Share! Learn!
40 under 40! Move to the Front Lines!
Editorial by Steve KING
Managing Director at CyberTheory
As the gap expands between supply and demand in cybersecurity skills, we now see over 70 online eLearning courses available that focus across a wide range of upskilling opportunities from data privacy to compliance to risk and vulnerability assessment and audit. As we celebrate our newest class of 40 under 40, we are optimistic that this generation of cybersecurity enthusiasts are interested in the actual battle zones upon which our current war is being fought and not on preparation for the administrative roles which are also necessary in battle, yet not feeling the pressure from the current skills gap.
In our work with our own eLearning platform, CyberEd.io, we have discovered that the key employment opportunities lie along the front lines of deployment, where trained cyber-warriors are so necessary not just to defend our critical assets but to serve as a deterrent to the flood of cyber-criminals assaulting our fortresses. Every CISO we talk to confirms this requirement with both anecdotal and empirical evidence that is leading to almost daily breaches across all industrial sectors with specific threats to banking, education, healthcare, military and industrial control systems in automated factories (OT).
The cyber-warrior education career path starts with a solid grasp of network engineering fundamentals, followed by security architecture & engineering with an emphasis on Cloud/SysOps/*nix (*Unix/Linux Linux, FreeBSD, and Mac OS X), ICS/IoT, identity access management, security assessment & testing, current threat profiles and malware infrastructure and architecture, vector identification, incident detection, security operations with forensics and incident handling, pen testing, and exploitation.
Without properly trained resources in advanced cyber-warfare, we will never prevail in our constant challenge to protect and defend, let alone being able to take the threat to the enemy. As more and more entry candidates choose training to prepare them for ...
Guarding the Digital Fortress Unmasking 10 Common Types of Cybersecurity Thre...

To guard our digital assets and ourselves from cyber threats, it’s crucial to be vigilant and proactive. Understanding common varieties of threats is essential, but enforcing preventive measures is likewise important. In the present-day virtual age, cybersecurity is a shared obligation. Adopting sturdy password practices, staying vigilant against phishing attempts, and keeping software programs up-to-date can lessen publicity to threats. https://mverve.com/
Guarding the Digital Fortress.pdf

To know how we can protect the data, firstly we need to know how someone can steal it. And in this blog, we will address the 10 common cyber security threats that are most prevalent and also the preventive measures that we can take to control them.
https://mverve.com/
Similar to What Is Cyber Security & Why We Need Cyber Security Expert – Lode Palle.pdf (20)
How Modern Cybersecurity Software Shields Against the Latest Threats.pdf

How Modern Cybersecurity Software Shields Against the Latest Threats.pdf
AI IN CYBERSECURITY: THE NEW FRONTIER OF DIGITAL PROTECTION

AI IN CYBERSECURITY: THE NEW FRONTIER OF DIGITAL PROTECTION
Get Started with Cyber Security and Its Landscape Null Community Presentation...

Get Started with Cyber Security and Its Landscape Null Community Presentation...
Advance Your Career with Cyber Security Training in Kerala

Advance Your Career with Cyber Security Training in Kerala
Malware Forensic Expertise: Analyzing and Neutralizing Cyber Threats.pdf

Malware Forensic Expertise: Analyzing and Neutralizing Cyber Threats.pdf
Cybersecurity In IoT Challenges And Effective Strategies.pdf

Cybersecurity In IoT Challenges And Effective Strategies.pdf
Fortifying the Digital Frontier Exploring the Crucial Dimensions of Cyber sec...

Fortifying the Digital Frontier Exploring the Crucial Dimensions of Cyber sec...
40 under 40 in cybersecurity. top cyber news magazine

40 under 40 in cybersecurity. top cyber news magazine
40 under 40 in Cybersecurity 2022. Top Cyber News MAGAZINE

40 under 40 in Cybersecurity 2022. Top Cyber News MAGAZINE
Guarding the Digital Fortress Unmasking 10 Common Types of Cybersecurity Thre...

Guarding the Digital Fortress Unmasking 10 Common Types of Cybersecurity Thre...
More from Lode Emmanuel Palle
Insights from Lode Palle Demystifying Desktop Application Development.pptx

In the ever-evolving landscape of technology, desktop applications remain a cornerstone of digital innovation, providing users with powerful tools and seamless experiences across various platforms. Lode Palle, a seasoned expert in software development, offers valuable insights into the intricacies of desktop application development, shedding light on its significance, challenges, and best practices.
Lode Emmanuel Palle - Real-Time Communication in Full Stack Applications.pptx

Lode Emmanuel Palle, a proficient advocate for cutting-edge technologies, offers illuminating insights into the intricate mechanisms and practical applications of real-time communication within full stack applications. At its core, real-time communication enables seamless, bidirectional data flow between clients and servers, eliminating the need for manual page refreshes and enabling dynamic, interactive user experiences.
PerformanceOptimization Techniques with Lode Emmanuel Palle.pptx

In the realm of web and application development, performance optimization stands as a cornerstone for ensuring user satisfaction, retention, and overall success. Lode Emmanuel Palle, a seasoned software engineer renowned for his expertise in this domain, navigates the intricate landscape of performance optimization with finesse and innovation.
Lode Emmanuel Palle — The Impact of Advanced Computer Applications.

Lode Emmanuel Palle describes that computer applications have made significant advancements in recent years, revolutionizing various industries and aspects of our daily lives. From business operations to healthcare and education, the integration of computer applications has led to increased efficiency, improved decision-making, and enhanced convenience.
Lodi Palle – The Cornerstone of Modern Software Development..pdf

Version control is a critical aspect of modern software development, enabling developers like Lodi Palle to effectively manage and track changes in their codebase. Among the various version control systems available, Git has emerged as the de facto standard due to its flexibility, efficiency, and widespread adoption.
Lode Palle - Revolutionizing with High-Performance Computing..pptx

As described by Lode Palle High-performance computing (HPC) is a transformative technology that has revolutionized the way we approach complex scientific, engineering, and data-intensive problems. At its core, HPC involves the use of powerful and specialized computer systems that can process and analyze massive amounts of data at incredibly high speeds.
Blockchain's Versatile Role by Lodi Palle..pdf

The role of blockchain technology, as envisioned by thought leader Lodi Palle, is nothing short of revolutionary. Blockchain has transcended its origins as a mere ledger for cryptocurrencies like Bitcoin and has now emerged as a transformative force across diverse industries. At its core, blockchain is a decentralized and immutable digital ledger that securely records transactions.
What are the 7 Web Development Processes - Lodi Palle

While the exact number of steps can vary depending on the development methodology and the specific project, here are seven common web development processes explained by Lodi palle
Emmanuel Palle – The Versatility of Software Development Tools and IDEs..pptx

Emmanuel Palle describes that Software development tools and integrated development environments (IDEs) are crucial components in the software development process. These tools provide developers with the necessary features and functionalities to write, edit, debug, and test their code efficiently.
Lode Palle Keeping Pace with Software-Developing Techniques..pptx

Staying updated with new software-developing techniques is crucial in today’s fast-paced technological landscape. Here are some effective strategies of Lode Palle to ensure you stay ahead of the curve.
https://lodeemmanuelpalle.tumblr.com/post/722635395255451648/lode-palle-keeping-pace-with-software-developing
Lode Emmanuel Palle Exploring the Diverse Cybersecurity Approaches in Softwar...

Lode Emmanuel Palle: When it comes to software development, ensuring robust cybersecurity measures is paramount. There are various types of cybersecurity techniques and practices that developers employ to protect software applications from potential threats and vulnerabilities. One essential aspect of software security is authentication and access control.
https://medium.com/@emmanuelpallelode/lode-emmanuel-palle-exploring-the-diverse-cybersecurity-approaches-in-software-development-dc15446bd619
Lodi Palle - UI vs. UX Design What's the Difference.pdf

According to Lodi Palle, UI design primarily deals with the visual and interactive aspects of a digital product, while UX design focuses on the overall user experience, including user research, information architecture, and the design of interactions and user flows. Both UI and UX design are crucial for creating successful and user-centered digital experiences.
Lode Palle - Programming Languages that UX Designers Should.pptx

According to Lode Palle, as a UX designer, it is not mandatory to be proficient in programming languages. However, having a basic understanding of certain programming languages can be beneficial and enable you to collaborate more effectively with developers.
Lode Emmanuel Palle - Why your website needs Essential 8 cyber security.pptx

Here are some reasons from Lode Emmanuel Palle why a website may benefit from implementing Essential 8 cybersecurity
Lode Palle - What are the 3 types of web design.pptx

According to Lodi Palle, It's important to note that these categories are not mutually exclusive, and many modern websites incorporate elements from multiple types of web design. The choice of approach depends on the specific goals, requirements, and target audience of the website.
Lode Palle - What are the qualifications for Software Developer.pdf

The qualifications for a software developer can vary depending on the specific job requirements and the industry in which they are working. However, here are some common qualifications described by Lode Palle and skills that are often sought after for software developer positions
Lodi Emmanuel Palle Cybersecurity and Technology Innovation.pptx

Lodi Palle is a junior software developer, and his main forte is in line with cybersecurity. He has honed and found passion in technology after doing various jobs to finally landed in software development. His work mainly focuses on Ruby on Rails, Ruby, SQL, Javascript, HTML, CSS, Bootstrap, React.js, node.js, Typescript, Android Studio, Flutter, Dart, Kotlin, ERP Systems, SAP, Tableau, Microsoft Power BI. Palle, confident enough to say that he can do the job, as he had finally found the career that he is most passionate about.
Lodi Palle Hot Take on Cyber Risk.pdf

Lodi Emmanuel Palle : Cyber Risk means the disruption and collection of data from your devices and malicious malware that’s been downloaded unknowingly. In layman’s terms, data breach from your own devices. As technology is widely known in any place in the world and at any age a person might be, they have their own social media accounts. Cyberspace has become more and more vulnerable and is now more prone to data breaching.
Understand significance of software development with Emmanuel Palle.pptx

Lodi Palle : Software development is the process of designing, coding, testing, and maintaining software applications or systems. It plays a crucial role in today's modern world. Software development drives technological advancement by creating innovative solutions to problems, automating tasks, and enhancing productivity across various industries. It enables the development of new technologies, such as artificial intelligence, blockchain, and virtual reality, which are transforming industries and reshaping the way we live and work - Emmanuel Palle.
How to Be an Efficient Software Engineer by Lodi Emmanuel Palle.pptx

Lodi Palle is a junior software engineer and a former healthcare professional. He has found a new passion in the cyber security field, and as someone who has experience working with teams, and is also very competent even in working under pressure, given the fact that the man has worked in a variety of work fields.
More from Lode Emmanuel Palle (20)
Insights from Lode Palle Demystifying Desktop Application Development.pptx

Insights from Lode Palle Demystifying Desktop Application Development.pptx
Lode Emmanuel Palle - Real-Time Communication in Full Stack Applications.pptx

Lode Emmanuel Palle - Real-Time Communication in Full Stack Applications.pptx
PerformanceOptimization Techniques with Lode Emmanuel Palle.pptx

PerformanceOptimization Techniques with Lode Emmanuel Palle.pptx
Lode Emmanuel Palle — The Impact of Advanced Computer Applications.

Lode Emmanuel Palle — The Impact of Advanced Computer Applications.
Lodi Palle – The Cornerstone of Modern Software Development..pdf

Lodi Palle – The Cornerstone of Modern Software Development..pdf
Lode Palle - Revolutionizing with High-Performance Computing..pptx

Lode Palle - Revolutionizing with High-Performance Computing..pptx
What are the 7 Web Development Processes - Lodi Palle

What are the 7 Web Development Processes - Lodi Palle
Emmanuel Palle – The Versatility of Software Development Tools and IDEs..pptx

Emmanuel Palle – The Versatility of Software Development Tools and IDEs..pptx
Lode Palle Keeping Pace with Software-Developing Techniques..pptx

Lode Palle Keeping Pace with Software-Developing Techniques..pptx
Lode Emmanuel Palle Exploring the Diverse Cybersecurity Approaches in Softwar...

Lode Emmanuel Palle Exploring the Diverse Cybersecurity Approaches in Softwar...
Lodi Palle - UI vs. UX Design What's the Difference.pdf

Lodi Palle - UI vs. UX Design What's the Difference.pdf
Lode Palle - Programming Languages that UX Designers Should.pptx

Lode Palle - Programming Languages that UX Designers Should.pptx
Lode Emmanuel Palle - Why your website needs Essential 8 cyber security.pptx

Lode Emmanuel Palle - Why your website needs Essential 8 cyber security.pptx
Lode Palle - What are the 3 types of web design.pptx

Lode Palle - What are the 3 types of web design.pptx
Lode Palle - What are the qualifications for Software Developer.pdf

Lode Palle - What are the qualifications for Software Developer.pdf
Lodi Emmanuel Palle Cybersecurity and Technology Innovation.pptx

Lodi Emmanuel Palle Cybersecurity and Technology Innovation.pptx
Understand significance of software development with Emmanuel Palle.pptx

Understand significance of software development with Emmanuel Palle.pptx
How to Be an Efficient Software Engineer by Lodi Emmanuel Palle.pptx

How to Be an Efficient Software Engineer by Lodi Emmanuel Palle.pptx
Recently uploaded
20240425_ TJ Communications Credentials_compressed.pdf

"𝑩𝑬𝑮𝑼𝑵 𝑾𝑰𝑻𝑯 𝑻𝑱 𝑰𝑺 𝑯𝑨𝑳𝑭 𝑫𝑶𝑵𝑬"
𝐓𝐉 𝐂𝐨𝐦𝐬 (𝐓𝐉 𝐂𝐨𝐦𝐦𝐮𝐧𝐢𝐜𝐚𝐭𝐢𝐨𝐧𝐬) is a professional event agency that includes experts in the event-organizing market in Vietnam, Korea, and ASEAN countries. We provide unlimited types of events from Music concerts, Fan meetings, and Culture festivals to Corporate events, Internal company events, Golf tournaments, MICE events, and Exhibitions.
𝐓𝐉 𝐂𝐨𝐦𝐬 provides unlimited package services including such as Event organizing, Event planning, Event production, Manpower, PR marketing, Design 2D/3D, VIP protocols, Interpreter agency, etc.
Sports events - Golf competitions/billiards competitions/company sports events: dynamic and challenging
⭐ 𝐅𝐞𝐚𝐭𝐮𝐫𝐞𝐝 𝐩𝐫𝐨𝐣𝐞𝐜𝐭𝐬:
➢ 2024 BAEKHYUN [Lonsdaleite] IN HO CHI MINH
➢ SUPER JUNIOR-L.S.S. THE SHOW : Th3ee Guys in HO CHI MINH
➢FreenBecky 1st Fan Meeting in Vietnam
➢CHILDREN ART EXHIBITION 2024: BEYOND BARRIERS
➢ WOW K-Music Festival 2023
➢ Winner [CROSS] Tour in HCM
➢ Super Show 9 in HCM with Super Junior
➢ HCMC - Gyeongsangbuk-do Culture and Tourism Festival
➢ Korean Vietnam Partnership - Fair with LG
➢ Korean President visits Samsung Electronics R&D Center
➢ Vietnam Food Expo with Lotte Wellfood
"𝐄𝐯𝐞𝐫𝐲 𝐞𝐯𝐞𝐧𝐭 𝐢𝐬 𝐚 𝐬𝐭𝐨𝐫𝐲, 𝐚 𝐬𝐩𝐞𝐜𝐢𝐚𝐥 𝐣𝐨𝐮𝐫𝐧𝐞𝐲. 𝐖𝐞 𝐚𝐥𝐰𝐚𝐲𝐬 𝐛𝐞𝐥𝐢𝐞𝐯𝐞 𝐭𝐡𝐚𝐭 𝐬𝐡𝐨𝐫𝐭𝐥𝐲 𝐲𝐨𝐮 𝐰𝐢𝐥𝐥 𝐛𝐞 𝐚 𝐩𝐚𝐫𝐭 𝐨𝐟 𝐨𝐮𝐫 𝐬𝐭𝐨𝐫𝐢𝐞𝐬."
Global Interconnection Group Joint Venture[960] (1).pdf![Global Interconnection Group Joint Venture[960] (1).pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Global Interconnection Group Joint Venture[960] (1).pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Global Interconnection Group Joint Venture[960] (1).pdf
Meas_Dylan_DMBS_PB1_2024-05XX_Revised.pdf

Personal Brand Statement:
As an Army veteran dedicated to lifelong learning, I bring a disciplined, strategic mindset to my pursuits. I am constantly expanding my knowledge to innovate and lead effectively. My journey is driven by a commitment to excellence, and to make a meaningful impact in the world.
What is the TDS Return Filing Due Date for FY 2024-25.pdf

It is crucial for the taxpayers to understand about the TDS Return Filing Due Date, so that they can fulfill your TDS obligations efficiently. Taxpayers can avoid penalties by sticking to the deadlines and by accurate filing of TDS. Timely filing of TDS will make sure about the availability of tax credits. You can also seek the professional guidance of experts like Legal Pillers for timely filing of the TDS Return.
Cracking the Workplace Discipline Code Main.pptx

Cultivating and maintaining discipline within teams is a critical differentiator for successful organisations.
Forward-thinking leaders and business managers understand the impact that discipline has on organisational success. A disciplined workforce operates with clarity, focus, and a shared understanding of expectations, ultimately driving better results, optimising productivity, and facilitating seamless collaboration.
Although discipline is not a one-size-fits-all approach, it can help create a work environment that encourages personal growth and accountability rather than solely relying on punitive measures.
In this deck, you will learn the significance of workplace discipline for organisational success. You’ll also learn
• Four (4) workplace discipline methods you should consider
• The best and most practical approach to implementing workplace discipline.
• Three (3) key tips to maintain a disciplined workplace.
Putting the SPARK into Virtual Training.pptx

This 60-minute webinar, sponsored by Adobe, was delivered for the Training Mag Network. It explored the five elements of SPARK: Storytelling, Purpose, Action, Relationships, and Kudos. Knowing how to tell a well-structured story is key to building long-term memory. Stating a clear purpose that doesn't take away from the discovery learning process is critical. Ensuring that people move from theory to practical application is imperative. Creating strong social learning is the key to commitment and engagement. Validating and affirming participants' comments is the way to create a positive learning environment.
Premium MEAN Stack Development Solutions for Modern Businesses

Stay ahead of the curve with our premium MEAN Stack Development Solutions. Our expert developers utilize MongoDB, Express.js, AngularJS, and Node.js to create modern and responsive web applications. Trust us for cutting-edge solutions that drive your business growth and success.
Know more: https://www.synapseindia.com/technology/mean-stack-development-company.html
Pitch Deck Teardown: RAW Dating App's $3M Angel deck

Pitch Deck Teardown: RAW Dating App's $3M Angel deck
5 Things You Need To Know Before Hiring a Videographer

Dive into this presentation to discover the 5 things you need to know before hiring a videographer in Toronto.
India Orthopedic Devices Market: Unlocking Growth Secrets, Trends and Develop...

According to TechSci Research report, “India Orthopedic Devices Market -Industry Size, Share, Trends, Competition Forecast & Opportunities, 2030”, the India Orthopedic Devices Market stood at USD 1,280.54 Million in 2024 and is anticipated to grow with a CAGR of 7.84% in the forecast period, 2026-2030F. The India Orthopedic Devices Market is being driven by several factors. The most prominent ones include an increase in the elderly population, who are more prone to orthopedic conditions such as osteoporosis and arthritis. Moreover, the rise in sports injuries and road accidents are also contributing to the demand for orthopedic devices. Advances in technology and the introduction of innovative implants and prosthetics have further propelled the market growth. Additionally, government initiatives aimed at improving healthcare infrastructure and the increasing prevalence of lifestyle diseases have led to an upward trend in orthopedic surgeries, thereby fueling the market demand for these devices.
Buy Verified PayPal Account | Buy Google 5 Star Reviews

Buy Verified PayPal Account
Looking to buy verified PayPal accounts? Discover 7 expert tips for safely purchasing a verified PayPal account in 2024. Ensure security and reliability for your transactions.
PayPal Services Features-
🟢 Email Access
🟢 Bank Added
🟢 Card Verified
🟢 Full SSN Provided
🟢 Phone Number Access
🟢 Driving License Copy
🟢 Fasted Delivery
Client Satisfaction is Our First priority. Our services is very appropriate to buy. We assume that the first-rate way to purchase our offerings is to order on the website. If you have any worry in our cooperation usually You can order us on Skype or Telegram.
24/7 Hours Reply/Please Contact
usawebmarketEmail: support@usawebmarket.com
Skype: usawebmarket
Telegram: @usawebmarket
WhatsApp: +1(218) 203-5951
USA WEB MARKET is the Best Verified PayPal, Payoneer, Cash App, Skrill, Neteller, Stripe Account and SEO, SMM Service provider.100%Satisfection granted.100% replacement Granted.
Attending a job Interview for B1 and B2 Englsih learners

It is a sample of an interview for a business english class for pre-intermediate and intermediate english students with emphasis on the speking ability.
Role of Remote Sensing and Monitoring in Mining

Remote sensing and monitoring are changing the mining industry for the better. These are providing innovative solutions to long-standing challenges. Those related to exploration, extraction, and overall environmental management by mining technology companies Odisha. These technologies make use of satellite imaging, aerial photography and sensors to collect data that might be inaccessible or from hazardous locations. With the use of this technology, mining operations are becoming increasingly efficient. Let us gain more insight into the key aspects associated with remote sensing and monitoring when it comes to mining.
一比一原版加拿大渥太华大学毕业证(uottawa毕业证书)如何办理

一模一样【q/微:1954292140】【加拿大渥太华大学毕业证(uottawa毕业证书)成绩单Offer】【q/微:1954292140】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【q/微:1954292140】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【q/微:1954292140】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
Recently uploaded (20)
20240425_ TJ Communications Credentials_compressed.pdf

20240425_ TJ Communications Credentials_compressed.pdf
Set off and carry forward of losses and assessment of individuals.pptx

Set off and carry forward of losses and assessment of individuals.pptx
Global Interconnection Group Joint Venture[960] (1).pdf![Global Interconnection Group Joint Venture[960] (1).pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Global Interconnection Group Joint Venture[960] (1).pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Global Interconnection Group Joint Venture[960] (1).pdf
What is the TDS Return Filing Due Date for FY 2024-25.pdf

What is the TDS Return Filing Due Date for FY 2024-25.pdf
chapter 10 - excise tax of transfer and business taxation

chapter 10 - excise tax of transfer and business taxation
Premium MEAN Stack Development Solutions for Modern Businesses

Premium MEAN Stack Development Solutions for Modern Businesses
Pitch Deck Teardown: RAW Dating App's $3M Angel deck

Pitch Deck Teardown: RAW Dating App's $3M Angel deck
5 Things You Need To Know Before Hiring a Videographer

5 Things You Need To Know Before Hiring a Videographer
India Orthopedic Devices Market: Unlocking Growth Secrets, Trends and Develop...

India Orthopedic Devices Market: Unlocking Growth Secrets, Trends and Develop...
Buy Verified PayPal Account | Buy Google 5 Star Reviews

Buy Verified PayPal Account | Buy Google 5 Star Reviews
Attending a job Interview for B1 and B2 Englsih learners

Attending a job Interview for B1 and B2 Englsih learners
What Is Cyber Security & Why We Need Cyber Security Expert – Lode Palle.pdf
- 1. What Is Cyber Security & Why We Need Cyber Security Expert – Lode Palle Lodi Palle : Cybersecurity is the practice of protecting digital systems, including computers, networks, servers, software, and data, from unauthorized access, use, disclosure, disruption, modification, or destruction. With the increasing reliance on technology and the internet for various aspects of our lives, such as communication, finance, healthcare, transportation A cybersecurity expert is a professional like Lodi Emmanuel Palle who possesses specialized knowledge and skills in the field of cybersecurity. They are trained to understand the ever- evolving landscape of cyber threats and employ appropriate techniques and tools to protect against them. Here are some reasons why we need cybersecurity experts: Cyber threats, such as malware, ransomware, phishing attacks, social engineering, and more, are constantly evolving and becoming increasingly sophisticated. Cybersecurity experts are trained to stay updated with the latest threats and technologies to counter them effectively. As technology continues to advance, new cybersecurity challenges arise with the adoption of emerging technologies such as cloud computing, Internet of Things (IoT), artificial intelligence (AI), and blockchain. Cybersecurity experts possess specialized knowledge in securing these technologies and addressing associated risks
