Vulnerability Management Detection & Response
•
0 likes•53 views
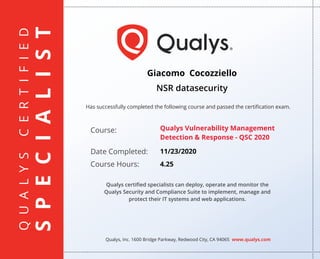
Qualys certified specialists can deploy, operate and monitor the Qualys Security and Compliance Suite to implement, manage and protect their IT systems and web applications.
Report
Share
Report
Share
Recommended
Policy Compliance 

Giacomo Cocozziello of NSR datasecurity successfully completed Qualys' Policy Compliance course on December 2, 2020, passing the certification exam. The 8-hour course trained specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
PCI Compliance 

Qualys certified specialists can deploy, operate and monitor the
Qualys Security and Compliance Suite to implement, manage and protect their IT systems and web applications.
Web Application Scanning 

Giacomo Cocozziello of NSR datasecurity successfully completed the 8-hour Qualys Web Application Scanning course on November 27, 2020 and passed the certification exam. As a Qualys certified specialist, Giacomo is qualified to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys vulnerability management course completion certificate

Mattia M De Lillo of Maticmind S.p.A successfully completed the Qualys Vulnerability Management course on November 13, 2018, passing the certification exam. As a Qualys certified specialist, Mattia can deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys web application scanning certificate

Mattia M De Lillo of Maticmind S.p.A successfully completed an 8-hour Qualys Web Application Scanning course on November 14, 2018 and passed the certification exam, earning the designation of Qualys certified specialist. As a certified specialist, Mattia can deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys - Policy compliance certificate Mattia De Lillo

Mattia M De Lillo successfully completed the Qualys Policy Compliance course on January 10, 2019, passing the certification exam after 8 hours of training. The course certified specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
PCI Compliance

Aniello Giugliano successfully completed the Qualys PCI Compliance course on October 7, 2020, passing the certification exam after 4 hours of training. The course certified him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications in accordance with PCI standards.
Global it asset inventory

Aniello Giugliano of DGS S.p.A successfully completed the Global IT Asset Inventory and Management course from Qualys, Inc. on November 19, 2020, passing the certification exam after 3 hours of training. The certification qualifies specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Recommended
Policy Compliance 

Giacomo Cocozziello of NSR datasecurity successfully completed Qualys' Policy Compliance course on December 2, 2020, passing the certification exam. The 8-hour course trained specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
PCI Compliance 

Qualys certified specialists can deploy, operate and monitor the
Qualys Security and Compliance Suite to implement, manage and protect their IT systems and web applications.
Web Application Scanning 

Giacomo Cocozziello of NSR datasecurity successfully completed the 8-hour Qualys Web Application Scanning course on November 27, 2020 and passed the certification exam. As a Qualys certified specialist, Giacomo is qualified to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys vulnerability management course completion certificate

Mattia M De Lillo of Maticmind S.p.A successfully completed the Qualys Vulnerability Management course on November 13, 2018, passing the certification exam. As a Qualys certified specialist, Mattia can deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys web application scanning certificate

Mattia M De Lillo of Maticmind S.p.A successfully completed an 8-hour Qualys Web Application Scanning course on November 14, 2018 and passed the certification exam, earning the designation of Qualys certified specialist. As a certified specialist, Mattia can deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys - Policy compliance certificate Mattia De Lillo

Mattia M De Lillo successfully completed the Qualys Policy Compliance course on January 10, 2019, passing the certification exam after 8 hours of training. The course certified specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
PCI Compliance

Aniello Giugliano successfully completed the Qualys PCI Compliance course on October 7, 2020, passing the certification exam after 4 hours of training. The course certified him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications in accordance with PCI standards.
Global it asset inventory

Aniello Giugliano of DGS S.p.A successfully completed the Global IT Asset Inventory and Management course from Qualys, Inc. on November 19, 2020, passing the certification exam after 3 hours of training. The certification qualifies specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Policy compliance

Aniello Giugliano successfully completed the Qualys Policy Compliance course on October 8, 2020, passing the certification exam after 8 hours of training. The course certified him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
File integrity monitoring

Aniello Giugliano successfully completed a 3-hour File Integrity Monitoring self-paced training course from Qualys, Inc. on October 8, 2020 and passed the certification exam, allowing him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Api Fundamentals

Aniello Giugliano successfully completed the Qualys API Fundamentals course on October 9, 2020, passing the certification exam with 3 hours of training. The course certified him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications using the Qualys API.
Qualys Certificate Vulnerability Management 

Aniello Giugliano has successfully completed the Qualys Vulnerability Management course on August 30, 2019, passing the certification exam. The 8-hour course certifies specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys web-app-scanning Certificate

Aniello Giugliano has successfully completed the Qualys Web Application Scanning course on August 31, 2019, passing the certification exam. The 8-hour course certifies specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys Certification 

Pukhraj Singh has successfully completed the Qualys Vulnerability Management course on November 24, 2019, passing the certification exam with 8 hours of training. As a Qualys certified specialist, he can now deploy, operate and monitor the Qualys Security and Compliance Suite to implement, manage and protect IT systems and web applications.
Coursecompletion (1)

Alessio A Cocilovo has successfully completed an 8-hour Qualys web application scanning certification course on April 13, 2021 and passed the exam. The certification allows him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Coursecompletion

Alessio A Cocilovo has successfully completed the Qualys certified specialist training course on Policy Compliance Strategies & Best Practices on April 8, 2021, passing the certification exam to become a Qualys certified specialist. As a certified specialist, Alessio is qualified to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
VCA_CLOUD

Pat Gelsinger, CEO of VMware, awarded Jacques Roux the VMware Certified Associate Cloud certification in recognition of successfully completing all certification requirements for Cloud as of July 30, 2015. The certificate includes a verification code to validate its authenticity on the VMware website.
VCA-DCV_eCertificate

This document certifies that Marc Langlois successfully completed all requirements for VMware Certified Associate in Data Center Virtualization. It recognizes his achievement and awards him the title on October 10, 2013. The document is signed by Pat Gelsinger, CEO of VMware, and provides a verification code to validate the authenticity of the certification.
MTA Cert

David Glasgow has passed the Microsoft Technology Associate: Networking Fundamentals certification exam administered by St. Paul Technical College on May 7, 2015. This digital transcript from Certiport authenticates his certification and shows that he passed the 98-366 MTA: Networking Fundamentals exam. Certiport is a global organization that tracks certification exams taken at over 12,000 testing centers worldwide.
Jaco Aucamp Certified Usability Analyst

This certificate certifies that Eric Schaer has met the requirements for and demonstrated mastery in usability by successfully completing the HFI-Certified Usability Analyst Examination. He is hereby certified as a Certified Usability Analyst by Human Factors International on August 25, 2015.
Certificate CRTE (certified Red Team Expert).pdf

A certification holder has expertise in following skills: - Active Directory Enumeration
- Abusing built-in functionality for code execution
- Local Privilege Escalation
- Credentials Replay
- Using administration tools to compromise other machines
- Bypassing countermeasures like Application White-listing and anti-virus.
- Pivot through windows machines to bypass Firewall rules.
- Domain Privilege Escalation using Kerberoast, Kerberos delegation, Abusing protected groups, abusing enterprise applications and more.
- Domain Persistence and Dominance using Golden and Silver ticket, Skeleton key, DSRM abuse, AdminSDHolder, DCSync, ACLs abuse, host security descriptors and more.
- Forest privilege escalation using cross trust attacks.
- Inter-forest trust attacks
- Abusing SQL Server Trusts
- Lateral movement and hunting for business secrets using built-in Windows tools.
Effective classification of android malware families through dynamic features...

The document discusses a study that aimed to develop an effective machine learning model for classifying Android malware families. It proposes a new dataset called UnisaMalwareDataset (UMD) which was created by extracting static and dynamic features from Android apps using the CuckooDroid sandbox. Experiments were conducted using common machine learning and deep learning techniques to demonstrate that efficient malware classification can be achieved by training models on the proposed dataset.
ICS/SCADA Cyber Security Certificate.pdf

Due to the potential impact of an attack on the physical safety of communities, employees or customers, ICS /SCADA security is an even higher priority than for traditional IT systems. Cyber criminals have already developed malware threats such as Triton/TRISIS and Stuxnet that can disrupt industrial Operation Technology (OT).
The ICS/SCADA Cyber Security Training Course is a hands-on training which will enable you to learn the foundation of security and defending architectures from attacks. You will look at the concept of “thinking like a hacker” to learn techniques to defend from the types of attacks that are commonly conducted against the oil and gas IT corporate and control network
Web Application Penetration Tester Extreme

EWPTX certification provides an advanced level on web application topics. Topics covered range from XSS, to SQLi, CSRF, Attacking Deserialization, etc.
Purple Teaming Fundamentals Cocozziello Giacomo.pdf

In this course I got to see the following aspects of cybersecurity:
- Analyses and investigate various Web, Network, Host And Active Directory based attacks by various defensive solutions.
- Hunt Cyber Threats in a realistic enterprise environment
- Perform Breach and Attack Simulation on Web, Network, Host & AD
- Collect Evidence & investigate Cyber Attacks using DFIR solutions
- Custom Rule creation on multiple defensive solutions
Secure_Wireless_LAN

Fortinet's Wireless LAN appliances leverage secure networking to provide secure wireless access to the corporate LAN perimeter. Our solution integrates seamlessly with the Fortinet Security Fabric to provide integrated security, end-to-end network visibility and automated threat response. You can easily manage your wireless network and security with a single console to minimize administration time.
OWASP API SECURITY TOP 10.pdf

APIs expose application logic and sensitive data such as Personally Identifiable Information (PII) and because of this, APIs have increasingly become a target for attackers. Without secure APIs, rapid innovation would be impossible.
Practical Industrial Control System Penetration Testing

The pentesting of ICS cannot be compared to the typical pentesting of the IT world. Industrial plants need to be continuously available and hardly any plant operator wants to risk a production stop. Typically, security testing is performed at the lowest or second lowest aggressiveness level. So if you are hoping to pwn your device with buffer overflows, kernel exploits, privilege escalation and root shells, you are in the wrong place.
Network Simulation

In this course I learned about various networking concepts. Starting from wiring to configuration of network equipment. Configuring routing protocols (RIP, OSPF, BGP). Configuration of protocols and services (DNS, NTP, DHCP, SYSLOG, SNMP, POE, Dual Power Supply), Configuration of network devices (Switch, Multi-layer Switch, Hub, Bridge, Wireless LAN Controller) and Security and features (NAT, ACL, NAT Pool, Mac Filtering, Unused Ports Switch, Trunk Port, Port Aggregation).
CyberSecurity Asset Management (CSAM).pdf

With CyberSecurity Asset Management (CSAM), Security and IT Ops gain both an attackers and defenders view of their environment for complete, 360-degree visibility of assets, asset groups, domains, subdomains, End-of-Life (EOL) tracking, and more. Together, with External Attack Surface Management (EASM), CSAM helps organizations discover, enrich, detect, prioritize, and orchestrate workflows between Security and IT Teams to eliminate workflow friction, improve remediation, and slash cyber risk.
More Related Content
What's hot
Policy compliance

Aniello Giugliano successfully completed the Qualys Policy Compliance course on October 8, 2020, passing the certification exam after 8 hours of training. The course certified him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
File integrity monitoring

Aniello Giugliano successfully completed a 3-hour File Integrity Monitoring self-paced training course from Qualys, Inc. on October 8, 2020 and passed the certification exam, allowing him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Api Fundamentals

Aniello Giugliano successfully completed the Qualys API Fundamentals course on October 9, 2020, passing the certification exam with 3 hours of training. The course certified him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications using the Qualys API.
Qualys Certificate Vulnerability Management 

Aniello Giugliano has successfully completed the Qualys Vulnerability Management course on August 30, 2019, passing the certification exam. The 8-hour course certifies specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys web-app-scanning Certificate

Aniello Giugliano has successfully completed the Qualys Web Application Scanning course on August 31, 2019, passing the certification exam. The 8-hour course certifies specialists to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Qualys Certification 

Pukhraj Singh has successfully completed the Qualys Vulnerability Management course on November 24, 2019, passing the certification exam with 8 hours of training. As a Qualys certified specialist, he can now deploy, operate and monitor the Qualys Security and Compliance Suite to implement, manage and protect IT systems and web applications.
Coursecompletion (1)

Alessio A Cocilovo has successfully completed an 8-hour Qualys web application scanning certification course on April 13, 2021 and passed the exam. The certification allows him to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
Coursecompletion

Alessio A Cocilovo has successfully completed the Qualys certified specialist training course on Policy Compliance Strategies & Best Practices on April 8, 2021, passing the certification exam to become a Qualys certified specialist. As a certified specialist, Alessio is qualified to deploy, operate, and monitor the Qualys Security and Compliance Suite to implement, manage, and protect IT systems and web applications.
VCA_CLOUD

Pat Gelsinger, CEO of VMware, awarded Jacques Roux the VMware Certified Associate Cloud certification in recognition of successfully completing all certification requirements for Cloud as of July 30, 2015. The certificate includes a verification code to validate its authenticity on the VMware website.
VCA-DCV_eCertificate

This document certifies that Marc Langlois successfully completed all requirements for VMware Certified Associate in Data Center Virtualization. It recognizes his achievement and awards him the title on October 10, 2013. The document is signed by Pat Gelsinger, CEO of VMware, and provides a verification code to validate the authenticity of the certification.
MTA Cert

David Glasgow has passed the Microsoft Technology Associate: Networking Fundamentals certification exam administered by St. Paul Technical College on May 7, 2015. This digital transcript from Certiport authenticates his certification and shows that he passed the 98-366 MTA: Networking Fundamentals exam. Certiport is a global organization that tracks certification exams taken at over 12,000 testing centers worldwide.
Jaco Aucamp Certified Usability Analyst

This certificate certifies that Eric Schaer has met the requirements for and demonstrated mastery in usability by successfully completing the HFI-Certified Usability Analyst Examination. He is hereby certified as a Certified Usability Analyst by Human Factors International on August 25, 2015.
What's hot (12)
More from GiacomoCocozziello
Certificate CRTE (certified Red Team Expert).pdf

A certification holder has expertise in following skills: - Active Directory Enumeration
- Abusing built-in functionality for code execution
- Local Privilege Escalation
- Credentials Replay
- Using administration tools to compromise other machines
- Bypassing countermeasures like Application White-listing and anti-virus.
- Pivot through windows machines to bypass Firewall rules.
- Domain Privilege Escalation using Kerberoast, Kerberos delegation, Abusing protected groups, abusing enterprise applications and more.
- Domain Persistence and Dominance using Golden and Silver ticket, Skeleton key, DSRM abuse, AdminSDHolder, DCSync, ACLs abuse, host security descriptors and more.
- Forest privilege escalation using cross trust attacks.
- Inter-forest trust attacks
- Abusing SQL Server Trusts
- Lateral movement and hunting for business secrets using built-in Windows tools.
Effective classification of android malware families through dynamic features...

The document discusses a study that aimed to develop an effective machine learning model for classifying Android malware families. It proposes a new dataset called UnisaMalwareDataset (UMD) which was created by extracting static and dynamic features from Android apps using the CuckooDroid sandbox. Experiments were conducted using common machine learning and deep learning techniques to demonstrate that efficient malware classification can be achieved by training models on the proposed dataset.
ICS/SCADA Cyber Security Certificate.pdf

Due to the potential impact of an attack on the physical safety of communities, employees or customers, ICS /SCADA security is an even higher priority than for traditional IT systems. Cyber criminals have already developed malware threats such as Triton/TRISIS and Stuxnet that can disrupt industrial Operation Technology (OT).
The ICS/SCADA Cyber Security Training Course is a hands-on training which will enable you to learn the foundation of security and defending architectures from attacks. You will look at the concept of “thinking like a hacker” to learn techniques to defend from the types of attacks that are commonly conducted against the oil and gas IT corporate and control network
Web Application Penetration Tester Extreme

EWPTX certification provides an advanced level on web application topics. Topics covered range from XSS, to SQLi, CSRF, Attacking Deserialization, etc.
Purple Teaming Fundamentals Cocozziello Giacomo.pdf

In this course I got to see the following aspects of cybersecurity:
- Analyses and investigate various Web, Network, Host And Active Directory based attacks by various defensive solutions.
- Hunt Cyber Threats in a realistic enterprise environment
- Perform Breach and Attack Simulation on Web, Network, Host & AD
- Collect Evidence & investigate Cyber Attacks using DFIR solutions
- Custom Rule creation on multiple defensive solutions
Secure_Wireless_LAN

Fortinet's Wireless LAN appliances leverage secure networking to provide secure wireless access to the corporate LAN perimeter. Our solution integrates seamlessly with the Fortinet Security Fabric to provide integrated security, end-to-end network visibility and automated threat response. You can easily manage your wireless network and security with a single console to minimize administration time.
OWASP API SECURITY TOP 10.pdf

APIs expose application logic and sensitive data such as Personally Identifiable Information (PII) and because of this, APIs have increasingly become a target for attackers. Without secure APIs, rapid innovation would be impossible.
Practical Industrial Control System Penetration Testing

The pentesting of ICS cannot be compared to the typical pentesting of the IT world. Industrial plants need to be continuously available and hardly any plant operator wants to risk a production stop. Typically, security testing is performed at the lowest or second lowest aggressiveness level. So if you are hoping to pwn your device with buffer overflows, kernel exploits, privilege escalation and root shells, you are in the wrong place.
Network Simulation

In this course I learned about various networking concepts. Starting from wiring to configuration of network equipment. Configuring routing protocols (RIP, OSPF, BGP). Configuration of protocols and services (DNS, NTP, DHCP, SYSLOG, SNMP, POE, Dual Power Supply), Configuration of network devices (Switch, Multi-layer Switch, Hub, Bridge, Wireless LAN Controller) and Security and features (NAT, ACL, NAT Pool, Mac Filtering, Unused Ports Switch, Trunk Port, Port Aggregation).
CyberSecurity Asset Management (CSAM).pdf

With CyberSecurity Asset Management (CSAM), Security and IT Ops gain both an attackers and defenders view of their environment for complete, 360-degree visibility of assets, asset groups, domains, subdomains, End-of-Life (EOL) tracking, and more. Together, with External Attack Surface Management (EASM), CSAM helps organizations discover, enrich, detect, prioritize, and orchestrate workflows between Security and IT Teams to eliminate workflow friction, improve remediation, and slash cyber risk.
Certificate FortiDeceptor.pdf

FortiDeceptor detects and responds to attacks in the network, such as the use of stolen credentials, lateral movement, man in the middle, and ransomware. Adding FortiDeceptor as part of your cybersecurity strategy helps change your defenses from reactive to proactive with intrusion-based detection layered with contextual information.
Qualys API

The document is a certificate recognizing an individual's completion of a Qualys API Fundamentals course and certification exam. It includes the individual's name, the date and location where they completed the course, and the number of course hours. It also states that Qualys Certified Specialists can deploy, operate, and monitor the Qualys Cloud Platform to implement, manage, and protect IT systems.
Qualys Patch Management

Qualys Certified Specialists can deploy, operate, and monitor
the Qualys Cloud Platform to implement, manage, and
protect IT systems, devices and web applications.
eLearning Junior Penetration Testing

This document is a certificate from eLearnSecurity certifying that GIACOMO COCOZZIELLO has passed the eLearnSecurity Junior Penetration Tester (eJPT) exam on September 25, 2022. It lists the exam as eJPT v1.0 and provides a verification code of 7443196.
Nozomi Networks Certified Engineer

This certificate certifies that Giacomo Cocozziello successfully passed the Nozomi Networks Certified Engineer exam for Guardian version 21.0 on October 2, 2021. The certificate was issued by Kimberly Seale, the Global Training Delivery Manager at Nozomi Networks, and will expire on October 2, 2023.
Mitre attack defender mad attack for cyber threat intelligence

This certificate acknowledges that Giacomo Cocozziello completed a 3-hour continuing education training course provided by Cybrary on MITRE ATT&CK DefenderTM (MAD) ATT&CK® Cyber Threat Intelligence. The certificate awards 3 CEUs/CPES for successful completion of the course on September 29, 2021.
Nozomi Networks Level 1 Technical Certification

This certificate certifies that Giacomo Cocozziello successfully completed the Nozomi Networks Level 1 Technical Certification training program requirements on July 12, 2021 as an employee of NSR.SRL. The certificate is signed by Jeff Blake, WW Head of Sales Engineering for Nozomi Networks.
NSE 2 Network Security Associate 

This document is a certificate from the NSE Institute verifying that Giacomo Cocozziello completed the NSE 2 Network Security Associate course and can be authenticated on their website. It certifies his training for 2 years in network security from January 8, 2021.
NSE 1 Network Security Associate 

After completing NSE 1, you will have a general
understanding of the following:
- Who are the bad actors behind cyber-attacks and what
motives them
- The methods of attack that the bad actors use
- Best practices to protect yourself and the information
you are entrusted to secure
More from GiacomoCocozziello (20)
Effective classification of android malware families through dynamic features...

Effective classification of android malware families through dynamic features...
Purple Teaming Fundamentals Cocozziello Giacomo.pdf

Purple Teaming Fundamentals Cocozziello Giacomo.pdf
Practical Industrial Control System Penetration Testing

Practical Industrial Control System Penetration Testing
Mitre attack defender mad attack for cyber threat intelligence

Mitre attack defender mad attack for cyber threat intelligence
Recently uploaded
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
UiPath Test Automation using UiPath Test Suite series, part 6

Welcome to UiPath Test Automation using UiPath Test Suite series part 6. In this session, we will cover Test Automation with generative AI and Open AI.
UiPath Test Automation with generative AI and Open AI webinar offers an in-depth exploration of leveraging cutting-edge technologies for test automation within the UiPath platform. Attendees will delve into the integration of generative AI, a test automation solution, with Open AI advanced natural language processing capabilities.
Throughout the session, participants will discover how this synergy empowers testers to automate repetitive tasks, enhance testing accuracy, and expedite the software testing life cycle. Topics covered include the seamless integration process, practical use cases, and the benefits of harnessing AI-driven automation for UiPath testing initiatives. By attending this webinar, testers, and automation professionals can gain valuable insights into harnessing the power of AI to optimize their test automation workflows within the UiPath ecosystem, ultimately driving efficiency and quality in software development processes.
What will you get from this session?
1. Insights into integrating generative AI.
2. Understanding how this integration enhances test automation within the UiPath platform
3. Practical demonstrations
4. Exploration of real-world use cases illustrating the benefits of AI-driven test automation for UiPath
Topics covered:
What is generative AI
Test Automation with generative AI and Open AI.
UiPath integration with generative AI
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
Full-RAG: A modern architecture for hyper-personalization

Mike Del Balso, CEO & Co-Founder at Tecton, presents "Full RAG," a novel approach to AI recommendation systems, aiming to push beyond the limitations of traditional models through a deep integration of contextual insights and real-time data, leveraging the Retrieval-Augmented Generation architecture. This talk will outline Full RAG's potential to significantly enhance personalization, address engineering challenges such as data management and model training, and introduce data enrichment with reranking as a key solution. Attendees will gain crucial insights into the importance of hyperpersonalization in AI, the capabilities of Full RAG for advanced personalization, and strategies for managing complex data integrations for deploying cutting-edge AI solutions.
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

ここ3000字までしか入らないけどタイトルの方がたくさん文字入ると思います。
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Introducing Milvus Lite: Easy-to-Install, Easy-to-Use vector database for you...

Join us to introduce Milvus Lite, a vector database that can run on notebooks and laptops, share the same API with Milvus, and integrate with every popular GenAI framework. This webinar is perfect for developers seeking easy-to-use, well-integrated vector databases for their GenAI apps.
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...

Sudheer Mechineni, Head of Application Frameworks, Standard Chartered Bank
Discover how Standard Chartered Bank harnessed the power of Neo4j to transform complex data access challenges into a dynamic, scalable graph database solution. This keynote will cover their journey from initial adoption to deploying a fully automated, enterprise-grade causal cluster, highlighting key strategies for modelling organisational changes and ensuring robust disaster recovery. Learn how these innovations have not only enhanced Standard Chartered Bank’s data infrastructure but also positioned them as pioneers in the banking sector’s adoption of graph technology.
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
UiPath Test Automation using UiPath Test Suite series, part 5

Welcome to UiPath Test Automation using UiPath Test Suite series part 5. In this session, we will cover CI/CD with devops.
Topics covered:
CI/CD with in UiPath
End-to-end overview of CI/CD pipeline with Azure devops
Speaker:
Lyndsey Byblow, Test Suite Sales Engineer @ UiPath, Inc.
“I’m still / I’m still / Chaining from the Block”

“An Outlook of the Ongoing and Future Relationship between Blockchain Technologies and Process-aware Information Systems.” Invited talk at the joint workshop on Blockchain for Information Systems (BC4IS) and Blockchain for Trusted Data Sharing (B4TDS), co-located with with the 36th International Conference on Advanced Information Systems Engineering (CAiSE), 3 June 2024, Limassol, Cyprus.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
Recently uploaded (20)
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

Cosa hanno in comune un mattoncino Lego e la backdoor XZ?
UiPath Test Automation using UiPath Test Suite series, part 6

UiPath Test Automation using UiPath Test Suite series, part 6
Full-RAG: A modern architecture for hyper-personalization

Full-RAG: A modern architecture for hyper-personalization
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Introducing Milvus Lite: Easy-to-Install, Easy-to-Use vector database for you...

Introducing Milvus Lite: Easy-to-Install, Easy-to-Use vector database for you...
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...

GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024
UiPath Test Automation using UiPath Test Suite series, part 5

UiPath Test Automation using UiPath Test Suite series, part 5
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
Vulnerability Management Detection & Response
- 1. QUALYSCERTIFIED SPECIALIST Has successfully completed the following course and passed the certification exam. Qualys, Inc. 1600 Bridge Parkway, Redwood City, CA 94065 www.qualys.com Course: Date Completed: Course Hours: Qualys certified specialists can deploy, operate and monitor the Qualys Security and Compliance Suite to implement, manage and protect their IT systems and web applications. Giacomo Cocozziello NSR datasecurity Qualys Vulnerability Management Detection & Response - QSC 2020 11/23/2020 4.25