Vinay Kumar
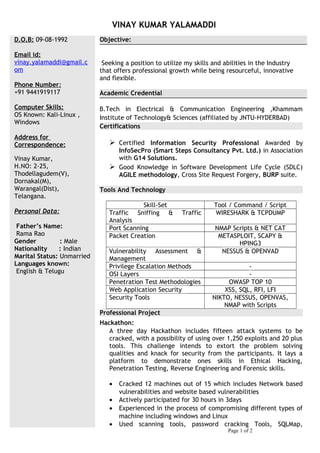
- 1. VINAY KUMAR YALAMADDI D.O.B: 09-08-1992 Email id: vinay.yalamaddi@gmail.c om Phone Number: +91 9441919117 Computer Skills: OS Known: Kali-Linux , Windows Address for Correspondence: Vinay Kumar, H.NO: 2-25, Thodellagudem(V), Dornakal(M), Warangal(Dist), Telangana. Personal Data: Father’s Name: Rama Rao Gender : Male Nationality : Indian Marital Status: Unmarried Languages known: English & Telugu Objective: Seeking a position to utilize my skills and abilities in the Industry that offers professional growth while being resourceful, innovative and flexible. Academic Credential B.Tech in Electrical & Communication Engineering ,Khammam Institute of Technology& Sciences (affiliated by JNTU-HYDERBAD) Certifications Certified Information Security Professional Awarded by InfoSecPro (Smart Steps Consultancy Pvt. Ltd.) in Association with G14 Solutions. Good Knowledge in Software Development Life Cycle (SDLC) AGILE methodology, Cross Site Request Forgery, BURP suite. Tools And Technology Skill-Set Tool / Command / Script Traffic Sniffing & Traffic Analysis WIRESHARK & TCPDUMP Port Scanning NMAP Scripts & NET CAT Packet Creation METASPLOIT, SCAPY & HPING3 Vulnerability Assessment & Management NESSUS & OPENVAD Privilege Escalation Methods - OSI Layers - Penetration Test Methodologies OWASP TOP 10 Web Application Security XSS, SQL, RFI, LFI Security Tools NIKTO, NESSUS, OPENVAS, NMAP with Scripts Professional Project Hackathon: A three day Hackathon includes fifteen attack systems to be cracked, with a possibility of using over 1,250 exploits and 20 plus tools. This challenge intends to extort the problem solving qualities and knack for security from the participants. It lays a platform to demonstrate ones skills in Ethical Hacking, Penetration Testing, Reverse Engineering and Forensic skills. • Cracked 12 machines out of 15 which includes Network based vulnerabilities and website based vulnerabilities • Actively participated for 30 hours in 3days • Experienced in the process of compromising different types of machine including windows and Linux • Used scanning tools, password cracking Tools, SQLMap, Page 1 of 2
- 2. Information Security Skills: Knowledge of key security concepts - PKI Infrastructure, Digital Certificates & Signatures, CIA, AAA - RBAC & Single SSO (Single Sign-on), Cryptography, TCP Handshake, and related protocols like SSL/TLS, PAP, CHAP, Kerberos, LDAP Extensive knowledge in Anatomy of an Attack and APT attack process. Wide exposure in various attacks like Application Layer Attacks (HTTP, FTP, SNMP, DNS, Malwares and SQL injections, Cross Site Scripting) , Network layer attacks (DOS/DDOS, Buffer Overflow, SYN Flood, Smurf Attacks, IP & MAC address Spoofing, ARP Poisoning), SSL/TLS attacks. Information Gathering and Foot printing tools like Maltego, Google Hacking & DNS Reconnaissance Port Scanning with Nmap & Net cat Traffic Sniffing & Traffic Analysis with Wire shark and TCPdump. Good with analyzing traffic patterns like port scans, finger printing, DOS/DDOS and ARP attacks, Troubleshooting ACL and common network problems Packet Crafting with Scapy, Hping3, Metasploit Expertise in System Hacking on Windows and Linux Platforms. Knowledge of Vulnerability Management and Assessment Process with NESSUS & OPENVAS. Used NESSUS for scanning network & host, editing Policies, generating and analyzing reports. Great exposure and Hands-on experience on Exploit techniques like Social engineering and client side attacks, Virus & backdoors. Exploits using file transfers using interactive and non interactive shells over FTP, TFTP Privilege Escalation methods in Windows and Linux Platforms. Good at Attack methods like Web Application Attacks including cross site scripting, SQL injection and file inclusions. Password Attacks using password profiling, brute force and hashing or hash cracking methods. Including finding Wi-Fi password in WEP & WPA protected systems. Good knowledge of OSI layer and clear understanding of protocols functioning at each layer in terms of network security. Exposure to IPv4 and its Subnets. Date: Place: (Vinay Kumar Yalamaddi)