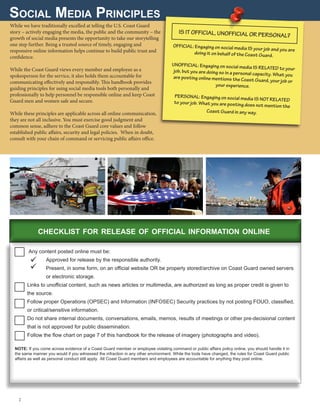
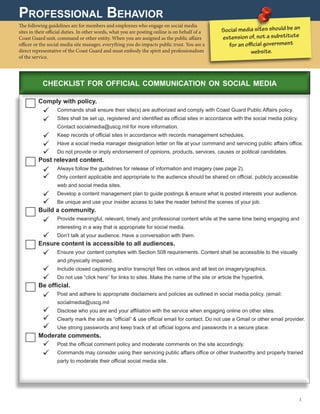
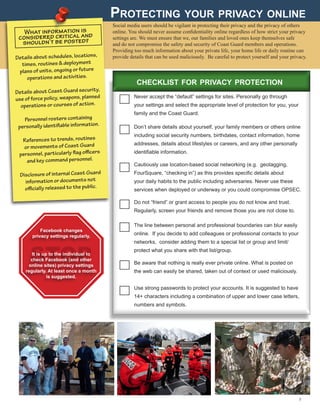
The document provides guidance for Coast Guard personnel on the responsible use of social media both personally and professionally. It outlines principles for official Coast Guard social media use, including only posting approved information, building an engaged community, and ensuring accessibility. It also provides guidance for personal social media use, stressing the need to follow all laws and policies, practice restraint, and realize that nothing posted is truly private or anonymous. A decision tree is included to help determine if a photo or video can be posted online.