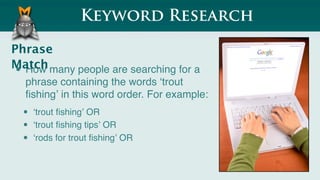
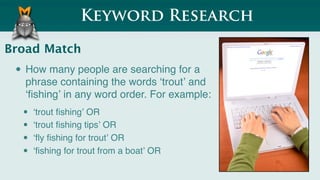
The document provides an overview of keyword research, specifically focusing on the differences between exact, phrase, and broad match data. It discusses the implications of using these match types for SEO traffic potential, categorized as short, medium, and long-term traffic. Additionally, it includes examples related to the term 'trout fishing' and its variations in search patterns.