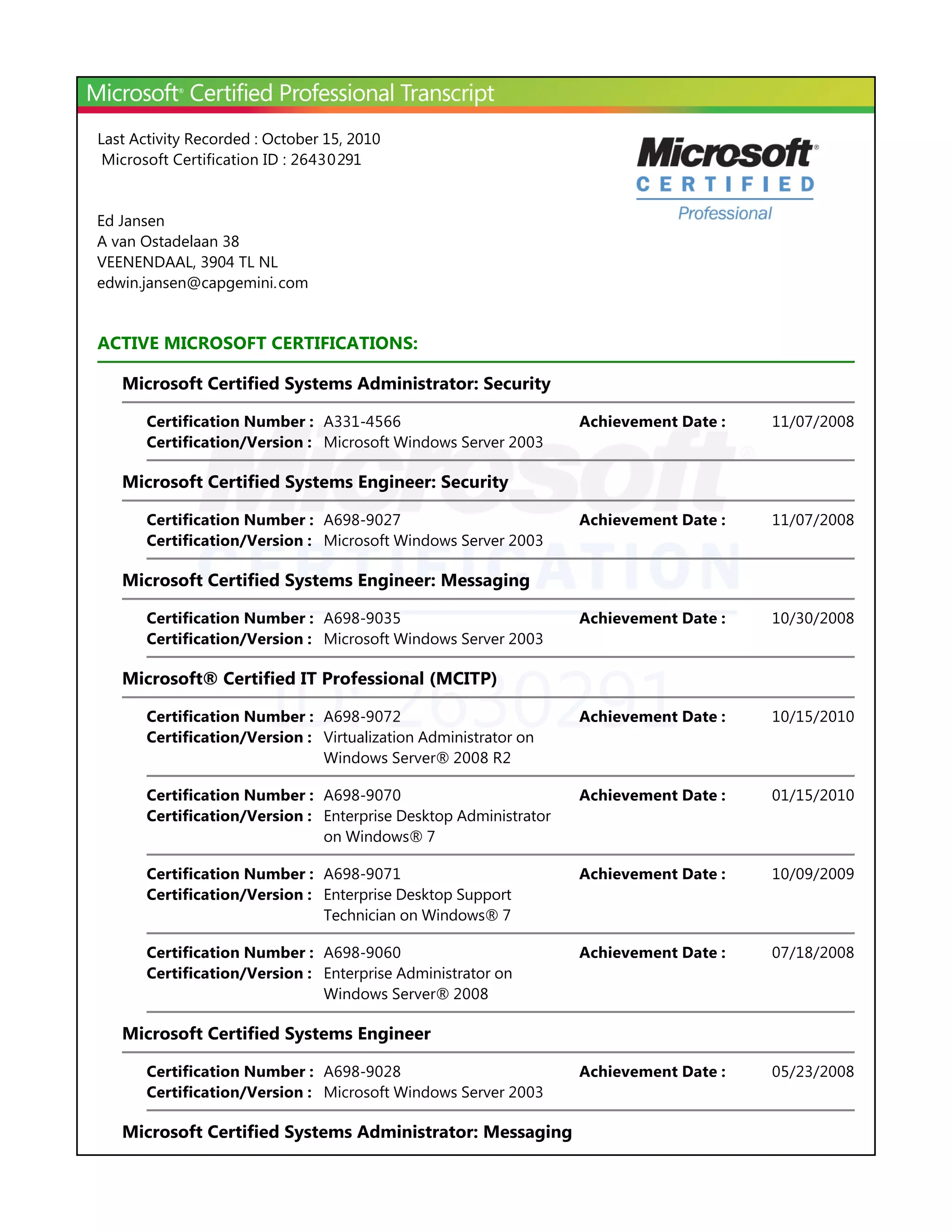
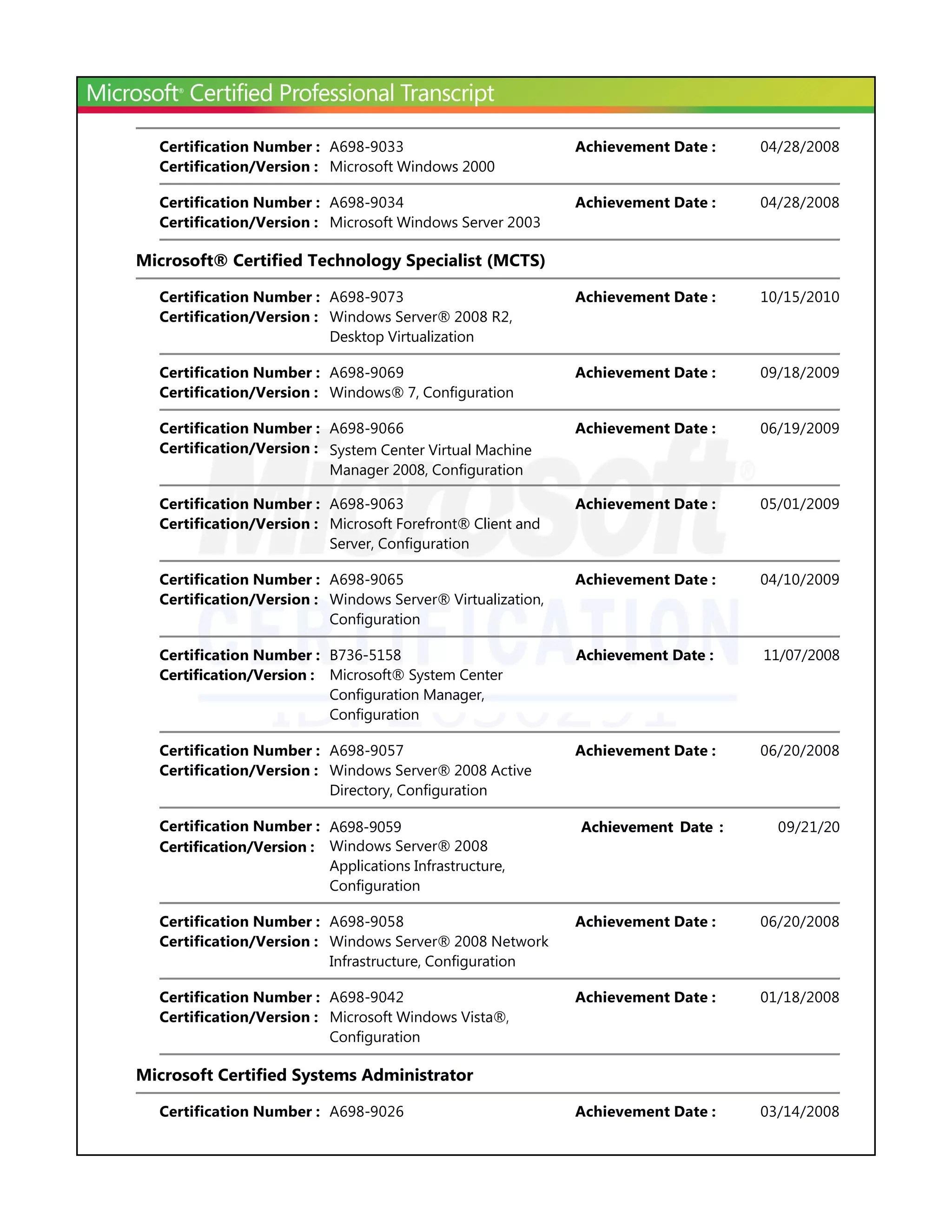
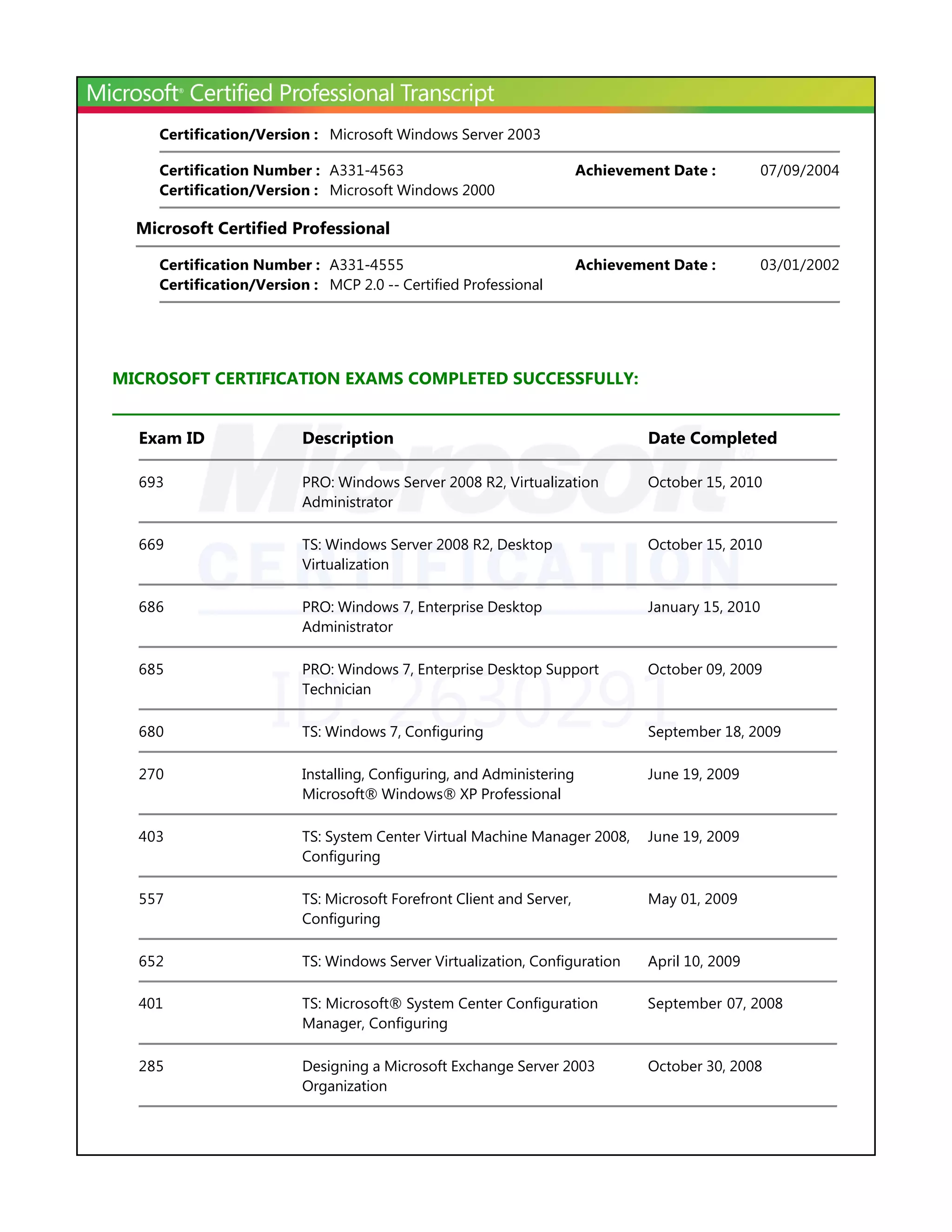
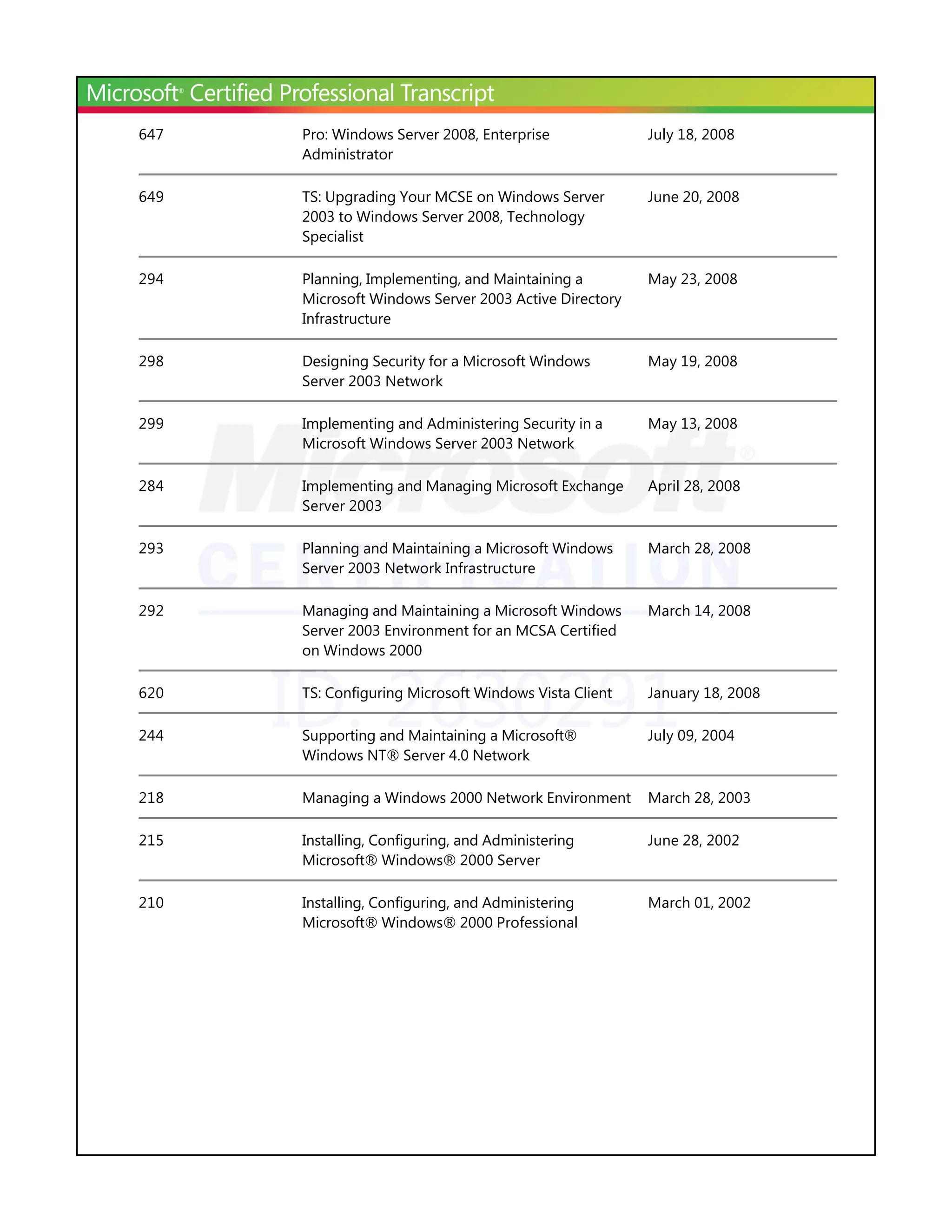
This document lists the active Microsoft certifications held by an individual with the ID 2630291. They hold certifications including Microsoft Certified Systems Administrator: Security, Microsoft Certified Systems Engineer: Security, and Microsoft Certified Systems Engineer: Messaging. The document also lists the individual's completed Microsoft certification exams and their dates.