The use of force in international law
•
0 likes•155 views
The use of force in international law
Report
Share
Report
Share
Download to read offline
Recommended
Politics media and war 9 11 and its aftermaths

the open university = Politics media and war 9 11 and its aftermaths
Recommended
Politics media and war 9 11 and its aftermaths

the open university = Politics media and war 9 11 and its aftermaths
Designing Schneier’s Five Step Risk Analysis Process into an Online Role Play...

Designing Schneier’s Five Step Risk Analysis Process into an Online Role Play...Nicola Marae Allain, PhD
Risk analysis and security policy development are essential components of an educated approach to security.
The author discusses an online security role play scenario and policy development exercise designed to include Schneier’s five step risk assessment methodology, while developing higher level cognitive, consensus building, communication, and decision-making skills.
A Poster Presentation for the Educause Conference, October 24th 2007FN3440 Project 1 P ROJECT D ES CRIP TION .docx

FN3440
Project
1
P ROJECT D ES CRIP TION
Project Introduction:
This project signifies a milestone for you in your quest to earn an associate’s degree in the Business Accounting
Technology program. The focus of a financial analysis is to help management identify potential issues in the
organization. A horizontal analysis compares the income statement and balance sheet information of different periods
for the same organization. A vertical analysis uses the relationships among financial statement data elements to detect
trends. A ratio analysis uses the relationships among various financial elements to measure liquidity, efficiency, and
solvency. In this project, you need to carry out a financial analysis and comparisons for three different companies.
Course Objectives Tested:
1. Analyze the logic behind the determination of interest rates and the required rates of return in the capital
markets.
2. Compute a firm’s debt ratio to ascertain how the firm is financing its assets.
3. Calculate the present and future value of an investment and an annuity.
4. Demonstrate how portfolio diversification can affect the expected return and the riskiness of investments.
5. Compute the present and future value of a bond under conditions of varying market interest rates.
6. Research and use the guidelines for capital budgeting to evaluate investment proposals. Measure a project’s
free cash flows.
7. Calculate the cost of debt capital, preferred stock, and common stock.
P ROJECT S UBMIS S ION P LA N
Description/Requirements of Project Evaluation Criteria
Assessment Preparation Checklist:
Perform the following tasks to prepare for this assessment:
Review the topic “Project Reckoner” in Week 6 online
lesson.
Read Chapters 1–6, pp. 1–187, from your textbook,
Foundations of Finance: The Logic and Practice of
Financial Management. These chapters will help you
while you are completing your research and compiling
the ratios. The financial analysis will further enhance
Did you analyze the trend for each
ratio during the three year timeframe?
Did you compare the three company’s
ratios properly?
Did you provide sufficient rationale to
justify your analysis of ratios for each
company?
Did you effectively and completely
answer all the questions contained in
project detail three?
FN3440
Project
2
Description/Requirements of Project Evaluation Criteria
your conceptual understanding of the material.
Title: Financial Analysis
1. Identify three companies from the Standard and Poor’s
500 Companies found in the ITT Tech Virtual Library. Two
of the companies should be in the same industry Global
Industry Classification Standards (GICS) while one should
be from a different industry segment.
2. Obtain the financial information for the selected
companies for the last three years by visiting the
individual company website and utilizing the Investor ...
School of Science, Technology, Engineering and MathDep.docx

School of Science, Technology, Engineering and Math
Department of Information TechnologyISSC331: Legal Issues in Information Security
3 Credit Hours
8 Week Course
Prerequisite(s): None
Table of Contents
Course Description
Evaluation Procedures
Course Scope
Grading Scale
Course Objectives
Course Outline
Course Delivery Method
Policies
Resources
Academic Services
Course Description (Catalog)
This course examines information security issues and the law. The rapid growth of technology has given rise to legal issues surrounding technology. Information security is the practice of protecting information to ensure the goals of confidentiality, integrity and availability are met. Information security makes sure that accurate information is available to authorized individuals when it is needed. When governments, private organizations, and individuals do a poor job of protecting the information entrusted to them, legislatures respond with new laws. The course will examine key conflicts involving technology and the legal system to include: privacy issues, civil, criminal, and administrative law, Children’s Online Privacy Protection Act (COPPA), Sarbanes Oxley, and information security governance. This course examines current literature on such topics.
Course Scope
This course offers an overview of the legal processes involved in implementing and maintaining an e-commerce Web site. In addition, this course examines security issues involved in maintaining a Web or intranet/Internet site and opportunities for misuse.
Course Objectives
The successful student will fulfill the following learning objectives:
CO-1: Describe common concepts in information security, privacy and the law
CO-2: Categorize the basic components and structure of the federal and state court systems
CO-3: Analyze the types of crimes that have evolved due to the use of technology and the laws that are in place to support them
CO-4: Differentiate between civil, criminal, common, and administrative law
CO-5: Analyze the issues surrounding jurisdiction that have been created by technology
CO-6: Critique the federal and state laws and legal concepts that affect how governments and organizations think about information security
CO-7: Explain reasonable expectations of privacy on the Internet
CO-8: Compare and contrast information security programs that address the laws and compliance requirements
Course Delivery Method
This course offers an overview of the legal processes involved in implementing and maintaining an e-commerce Web site. In addition, this course exa.
Administrative Law Sem8.docx

detailed step by step syllabus to cover major topics of adminsitartive law
Morality Essay.pdf

Amazing Morality Essay ~ Thatsnotus. Religion and Morality Free Essay Example. What Is Morality Why Should Society Be Moral At All Essay. ≫ Slave Morality versus Master Morality Free Essay Sample on Samploon.com. Law and Morality Essay Sample. Essay on morals and ethics - lawwustl.web.fc2.com. Criminal law morality essay. Culture and Morality Essay Example | Topics and Well Written Essays .... Moral Reasoning and Ethical Complexity Free Essay Example. Sample Morality Essay. The moral values for Aristotle - Free Essay Example | PapersOwl.com. Essay on Morality. #1 Essay on morals. Pay For Expert Online Writing Service.. Moral essay ideas - sanjran.web.fc2.com. Law And Morality Essay – yfecywami6. Moral and Ethical Essay | Legal Studies - Year 12 HSC | Thinkswap. Moral Values Essay | Essay on Moral Values for Students and Children in .... What Is the Role of Morality in Modern Society Essay Example .... Law and Morality Essay - ‘Discuss the extent to which the law should be .... Contemporary Moral Issues Essay. Essay on Morality | PHIL2646 - Philosophy and Literature - USYD | Thinkswap. PPT - ETHICS AND MORALITY Chapter 1: why be ethical? PowerPoint .... Essay on Moral Values | Importance of Moral Values & Ethics in Life. Sample essay on ethics. 2005 Morality Sample Answer. Pin on Essay Writing Help. Theories of Morality. Essay on morals - The Writing Center.. Law Essay Morals | Morality | Crimes. ≫ Should We Always Be Moral? Free Essay Sample on Samploon.com.
Changing law mental capacity legislation

the open university = Changing law mental capacity legislation
Course Syllabus CJS200 Foundations of the Criminal Jus.docx

Course Syllabus
CJS200
Foundations of the Criminal Justice System
Course Start Date: 02/15/2010
Course End Date: 04/18/2010
Please print a copy of this syllabus for handy reference.
Whenever there is a question about what assignments are due, please remember this syllabus is
considered the ruling document.
Copyright
Copyright ©2009 by University of Phoenix. All rights reserved.
University of Phoenix© is a registered trademark of Apollo Group, Inc. in the United States and/or other countries.
Microsoft©, Windows©, and Windows NT© are registered trademarks of Microsoft Corporation in the United States and/or other
countries. All other company and product names are trademarks or registered trademarks of their respective companies. Use of
these marks is not intended to imply endorsement, sponsorship, or affiliation.
Edited in accordance with University of Phoenix© editorial standards and practices.
Facilitator Information
John Scott
[email protected] (University of Phoenix)
[email protected] (Personal)
772-216-6013 (EST)
Facilitator Availability
I am available from 9 a.m. - 2 p.m. Eastern Time on most days, but I attempt to reserve Sunday for my
family. During the week, I am online most of the time during that 9 a.m. - 2 p.m. and 11 p.m. - 12 a.m.
time frame.
On Saturdays, I tend to be online in the morning only. If these times are not convenient for you, please let
me know. I will be happy to accommodate your schedule, if possible. I provide you with these times to
make it easier to communicate with me, and not to limit our contact.
I want you to know that, should you need to contact me outside these time frames, you should not
hesitate to do so.
For emergencies, when you are not able to gain access to messages on the Online Learning System
(OLS), please send a message to my personal email address. In the event a third party needs to contact
me, please direct them to my contact information listed under "facilitator information." No third party
should use your login credentials to gain access to the classroom.
Where to Go to Class
Main: This is the main forum for the class and is where discussion is conducted. It has read-and-write
access for everyone.
Chat-Room: This is a read-and-write access forum. It is designed as a place to discuss issues not related
to the course content. This is the forum to which we will send our bios.
Course-Materials: This is a read-only forum, which means you can read messages here but cannot send
any. This is where I will post the course syllabus and materials.
Individual Forum: You will see one forum with your name on it. This is a private forum, shared only by
you and me, the facilitator. Your classmates will not.
JAN - APR 2023 SEMESTER COURSE OUTLINE.pptx

In order to solve these problems as they might exist at given points in time, government is always seen formulating policies in response to them and in relation to the objectives of growth, national development and wellbeing of the citizens.
PS 1010, American Government 1 Course Description .docx

PS 1010, American Government 1
Course Description
In-depth study of American government and politics focusing on a balanced, unbiased, and up-to-date introduction to
constitutional, governmental, political, social, and economic structures and processes.
Prerequisites
None
Course Textbook
Patterson, T. E. (2008). The American democracy (8th ed.). Boston, MA: McGraw-Hill.
Course Learning Objectives
Upon completion of this course, students should be able to:
1. Describe the different forms of government (totalitarian regime, oligarchy, aristocracy, democracy, and anarchy).
2. Identify the patterns in early American colonization that influenced later governmental structure and operation.
3. Describe the historical context surrounding the drafting and ratification of the Constitution.
4. Identify and explain the classification of powers between the national and state governments in the U.S. federal
system.
5. Describe the expansion of civil rights through legislation and amendments to the Constitution in the post-Civil War
period, including the Emancipation Proclamation, the Thirteenth, Fourteenth and Fifteenth Amendments, the
Civil Rights Acts of 1865 – 1877, and the Civil Rights cases of 1883 (especially Plessey v. Ferguson).
6. Explain the nature of the problem of gender-based discrimination in the workplace and the importance of Title VII,
definitional problems associated with regulations, the problems of wage discrimination, pay equity, and the
glass ceiling.
7. Explain how public opinion is formed in the U.S., including political socialization by families, education, and peers
and the influence of religion, economic status, political events, and opinion leaders.
8. Describe the impact of the media on political socialization.
9. Define an interest group and describe its function.
10. Identify and analyze the direct tactics used by interest groups, including lobbying, rating systems, campaign
assistance, and the formations of political action committees.
11. Describe the presidential election process from primaries to the general election.
12. Identify the major functions performed by the mass media in our society, including entertainment, reporting news,
identifying public problems, socializing a new generation, and providing a political forum.
13. Explain the major functions of Congress, including lawmaking, constituent service, and oversight and conflict
resolution.
14. Compare the basic differences between the House of Representatives and the Senate.
15. Identify and explain the roles of the President (including Chief of State, Chief Executive, Commander in Chief,
Chief Diplomat, and Chief Legislator).
16. Explain the major concepts of the American legal system that were developed in the English common law system,
including the common law tradition, precedent, jurisdiction, and stare decisis.
17. Identify the principal agencies t ...
national commission for women

prasad shivaji shevate
my gov certificate national commission for women
ministry of health and family welfare

prasad shivaji shevate
my gov certificate ministry of health and family welfare
More Related Content
Similar to The use of force in international law
Designing Schneier’s Five Step Risk Analysis Process into an Online Role Play...

Designing Schneier’s Five Step Risk Analysis Process into an Online Role Play...Nicola Marae Allain, PhD
Risk analysis and security policy development are essential components of an educated approach to security.
The author discusses an online security role play scenario and policy development exercise designed to include Schneier’s five step risk assessment methodology, while developing higher level cognitive, consensus building, communication, and decision-making skills.
A Poster Presentation for the Educause Conference, October 24th 2007FN3440 Project 1 P ROJECT D ES CRIP TION .docx

FN3440
Project
1
P ROJECT D ES CRIP TION
Project Introduction:
This project signifies a milestone for you in your quest to earn an associate’s degree in the Business Accounting
Technology program. The focus of a financial analysis is to help management identify potential issues in the
organization. A horizontal analysis compares the income statement and balance sheet information of different periods
for the same organization. A vertical analysis uses the relationships among financial statement data elements to detect
trends. A ratio analysis uses the relationships among various financial elements to measure liquidity, efficiency, and
solvency. In this project, you need to carry out a financial analysis and comparisons for three different companies.
Course Objectives Tested:
1. Analyze the logic behind the determination of interest rates and the required rates of return in the capital
markets.
2. Compute a firm’s debt ratio to ascertain how the firm is financing its assets.
3. Calculate the present and future value of an investment and an annuity.
4. Demonstrate how portfolio diversification can affect the expected return and the riskiness of investments.
5. Compute the present and future value of a bond under conditions of varying market interest rates.
6. Research and use the guidelines for capital budgeting to evaluate investment proposals. Measure a project’s
free cash flows.
7. Calculate the cost of debt capital, preferred stock, and common stock.
P ROJECT S UBMIS S ION P LA N
Description/Requirements of Project Evaluation Criteria
Assessment Preparation Checklist:
Perform the following tasks to prepare for this assessment:
Review the topic “Project Reckoner” in Week 6 online
lesson.
Read Chapters 1–6, pp. 1–187, from your textbook,
Foundations of Finance: The Logic and Practice of
Financial Management. These chapters will help you
while you are completing your research and compiling
the ratios. The financial analysis will further enhance
Did you analyze the trend for each
ratio during the three year timeframe?
Did you compare the three company’s
ratios properly?
Did you provide sufficient rationale to
justify your analysis of ratios for each
company?
Did you effectively and completely
answer all the questions contained in
project detail three?
FN3440
Project
2
Description/Requirements of Project Evaluation Criteria
your conceptual understanding of the material.
Title: Financial Analysis
1. Identify three companies from the Standard and Poor’s
500 Companies found in the ITT Tech Virtual Library. Two
of the companies should be in the same industry Global
Industry Classification Standards (GICS) while one should
be from a different industry segment.
2. Obtain the financial information for the selected
companies for the last three years by visiting the
individual company website and utilizing the Investor ...
School of Science, Technology, Engineering and MathDep.docx

School of Science, Technology, Engineering and Math
Department of Information TechnologyISSC331: Legal Issues in Information Security
3 Credit Hours
8 Week Course
Prerequisite(s): None
Table of Contents
Course Description
Evaluation Procedures
Course Scope
Grading Scale
Course Objectives
Course Outline
Course Delivery Method
Policies
Resources
Academic Services
Course Description (Catalog)
This course examines information security issues and the law. The rapid growth of technology has given rise to legal issues surrounding technology. Information security is the practice of protecting information to ensure the goals of confidentiality, integrity and availability are met. Information security makes sure that accurate information is available to authorized individuals when it is needed. When governments, private organizations, and individuals do a poor job of protecting the information entrusted to them, legislatures respond with new laws. The course will examine key conflicts involving technology and the legal system to include: privacy issues, civil, criminal, and administrative law, Children’s Online Privacy Protection Act (COPPA), Sarbanes Oxley, and information security governance. This course examines current literature on such topics.
Course Scope
This course offers an overview of the legal processes involved in implementing and maintaining an e-commerce Web site. In addition, this course examines security issues involved in maintaining a Web or intranet/Internet site and opportunities for misuse.
Course Objectives
The successful student will fulfill the following learning objectives:
CO-1: Describe common concepts in information security, privacy and the law
CO-2: Categorize the basic components and structure of the federal and state court systems
CO-3: Analyze the types of crimes that have evolved due to the use of technology and the laws that are in place to support them
CO-4: Differentiate between civil, criminal, common, and administrative law
CO-5: Analyze the issues surrounding jurisdiction that have been created by technology
CO-6: Critique the federal and state laws and legal concepts that affect how governments and organizations think about information security
CO-7: Explain reasonable expectations of privacy on the Internet
CO-8: Compare and contrast information security programs that address the laws and compliance requirements
Course Delivery Method
This course offers an overview of the legal processes involved in implementing and maintaining an e-commerce Web site. In addition, this course exa.
Administrative Law Sem8.docx

detailed step by step syllabus to cover major topics of adminsitartive law
Morality Essay.pdf

Amazing Morality Essay ~ Thatsnotus. Religion and Morality Free Essay Example. What Is Morality Why Should Society Be Moral At All Essay. ≫ Slave Morality versus Master Morality Free Essay Sample on Samploon.com. Law and Morality Essay Sample. Essay on morals and ethics - lawwustl.web.fc2.com. Criminal law morality essay. Culture and Morality Essay Example | Topics and Well Written Essays .... Moral Reasoning and Ethical Complexity Free Essay Example. Sample Morality Essay. The moral values for Aristotle - Free Essay Example | PapersOwl.com. Essay on Morality. #1 Essay on morals. Pay For Expert Online Writing Service.. Moral essay ideas - sanjran.web.fc2.com. Law And Morality Essay – yfecywami6. Moral and Ethical Essay | Legal Studies - Year 12 HSC | Thinkswap. Moral Values Essay | Essay on Moral Values for Students and Children in .... What Is the Role of Morality in Modern Society Essay Example .... Law and Morality Essay - ‘Discuss the extent to which the law should be .... Contemporary Moral Issues Essay. Essay on Morality | PHIL2646 - Philosophy and Literature - USYD | Thinkswap. PPT - ETHICS AND MORALITY Chapter 1: why be ethical? PowerPoint .... Essay on Moral Values | Importance of Moral Values & Ethics in Life. Sample essay on ethics. 2005 Morality Sample Answer. Pin on Essay Writing Help. Theories of Morality. Essay on morals - The Writing Center.. Law Essay Morals | Morality | Crimes. ≫ Should We Always Be Moral? Free Essay Sample on Samploon.com.
Changing law mental capacity legislation

the open university = Changing law mental capacity legislation
Course Syllabus CJS200 Foundations of the Criminal Jus.docx

Course Syllabus
CJS200
Foundations of the Criminal Justice System
Course Start Date: 02/15/2010
Course End Date: 04/18/2010
Please print a copy of this syllabus for handy reference.
Whenever there is a question about what assignments are due, please remember this syllabus is
considered the ruling document.
Copyright
Copyright ©2009 by University of Phoenix. All rights reserved.
University of Phoenix© is a registered trademark of Apollo Group, Inc. in the United States and/or other countries.
Microsoft©, Windows©, and Windows NT© are registered trademarks of Microsoft Corporation in the United States and/or other
countries. All other company and product names are trademarks or registered trademarks of their respective companies. Use of
these marks is not intended to imply endorsement, sponsorship, or affiliation.
Edited in accordance with University of Phoenix© editorial standards and practices.
Facilitator Information
John Scott
[email protected] (University of Phoenix)
[email protected] (Personal)
772-216-6013 (EST)
Facilitator Availability
I am available from 9 a.m. - 2 p.m. Eastern Time on most days, but I attempt to reserve Sunday for my
family. During the week, I am online most of the time during that 9 a.m. - 2 p.m. and 11 p.m. - 12 a.m.
time frame.
On Saturdays, I tend to be online in the morning only. If these times are not convenient for you, please let
me know. I will be happy to accommodate your schedule, if possible. I provide you with these times to
make it easier to communicate with me, and not to limit our contact.
I want you to know that, should you need to contact me outside these time frames, you should not
hesitate to do so.
For emergencies, when you are not able to gain access to messages on the Online Learning System
(OLS), please send a message to my personal email address. In the event a third party needs to contact
me, please direct them to my contact information listed under "facilitator information." No third party
should use your login credentials to gain access to the classroom.
Where to Go to Class
Main: This is the main forum for the class and is where discussion is conducted. It has read-and-write
access for everyone.
Chat-Room: This is a read-and-write access forum. It is designed as a place to discuss issues not related
to the course content. This is the forum to which we will send our bios.
Course-Materials: This is a read-only forum, which means you can read messages here but cannot send
any. This is where I will post the course syllabus and materials.
Individual Forum: You will see one forum with your name on it. This is a private forum, shared only by
you and me, the facilitator. Your classmates will not.
JAN - APR 2023 SEMESTER COURSE OUTLINE.pptx

In order to solve these problems as they might exist at given points in time, government is always seen formulating policies in response to them and in relation to the objectives of growth, national development and wellbeing of the citizens.
PS 1010, American Government 1 Course Description .docx

PS 1010, American Government 1
Course Description
In-depth study of American government and politics focusing on a balanced, unbiased, and up-to-date introduction to
constitutional, governmental, political, social, and economic structures and processes.
Prerequisites
None
Course Textbook
Patterson, T. E. (2008). The American democracy (8th ed.). Boston, MA: McGraw-Hill.
Course Learning Objectives
Upon completion of this course, students should be able to:
1. Describe the different forms of government (totalitarian regime, oligarchy, aristocracy, democracy, and anarchy).
2. Identify the patterns in early American colonization that influenced later governmental structure and operation.
3. Describe the historical context surrounding the drafting and ratification of the Constitution.
4. Identify and explain the classification of powers between the national and state governments in the U.S. federal
system.
5. Describe the expansion of civil rights through legislation and amendments to the Constitution in the post-Civil War
period, including the Emancipation Proclamation, the Thirteenth, Fourteenth and Fifteenth Amendments, the
Civil Rights Acts of 1865 – 1877, and the Civil Rights cases of 1883 (especially Plessey v. Ferguson).
6. Explain the nature of the problem of gender-based discrimination in the workplace and the importance of Title VII,
definitional problems associated with regulations, the problems of wage discrimination, pay equity, and the
glass ceiling.
7. Explain how public opinion is formed in the U.S., including political socialization by families, education, and peers
and the influence of religion, economic status, political events, and opinion leaders.
8. Describe the impact of the media on political socialization.
9. Define an interest group and describe its function.
10. Identify and analyze the direct tactics used by interest groups, including lobbying, rating systems, campaign
assistance, and the formations of political action committees.
11. Describe the presidential election process from primaries to the general election.
12. Identify the major functions performed by the mass media in our society, including entertainment, reporting news,
identifying public problems, socializing a new generation, and providing a political forum.
13. Explain the major functions of Congress, including lawmaking, constituent service, and oversight and conflict
resolution.
14. Compare the basic differences between the House of Representatives and the Senate.
15. Identify and explain the roles of the President (including Chief of State, Chief Executive, Commander in Chief,
Chief Diplomat, and Chief Legislator).
16. Explain the major concepts of the American legal system that were developed in the English common law system,
including the common law tradition, precedent, jurisdiction, and stare decisis.
17. Identify the principal agencies t ...
Similar to The use of force in international law (20)
Introduction To The Symposium On Legal Externships 2 Learning ... 1

Introduction To The Symposium On Legal Externships 2 Learning ... 1
Designing Schneier’s Five Step Risk Analysis Process into an Online Role Play...

Designing Schneier’s Five Step Risk Analysis Process into an Online Role Play...
School of Science, Technology, Engineering and MathDep.docx

School of Science, Technology, Engineering and MathDep.docx
booklet_M.A. in Public International Law and Diplomacy v6.pdf

booklet_M.A. in Public International Law and Diplomacy v6.pdf
Introduction To The Symposium On Legal Externships 2 Learning ...

Introduction To The Symposium On Legal Externships 2 Learning ...
Course Syllabus CJS200 Foundations of the Criminal Jus.docx

Course Syllabus CJS200 Foundations of the Criminal Jus.docx
PS 1010, American Government 1 Course Description .docx

PS 1010, American Government 1 Course Description .docx
More from Prasad Shevate
national commission for women

prasad shivaji shevate
my gov certificate national commission for women
ministry of health and family welfare

prasad shivaji shevate
my gov certificate ministry of health and family welfare
my gov certificate National human right commission india

prasad shivaji shevate
my gov certificate National human right commission india
my gov certificate Padma awards version2

prasad shivaji shevate
my gov certificate Padma awards version2
my gov certificate Rashtriya ekta diwas pledge

prasad shivaji shevate
my gov certificate Rashtriya ekta diwas pledge
my gov certificate Reducing corruption through technology

prasad shivaji shevate
my gov certificate Reducing corruption through technology
my gov certificate Soil health pledge on world soil daymembers of parliament

prasad shivaji shevate
my gov certificate Soil health pledge on world soil daymembers of parliament
More from Prasad Shevate (20)
my gov certificate National human right commission india

my gov certificate National human right commission india
my gov certificate Reducing corruption through technology

my gov certificate Reducing corruption through technology
my gov certificate Soil health pledge on world soil daymembers of parliament

my gov certificate Soil health pledge on world soil daymembers of parliament
Recently uploaded
The Main Procedures for Obtaining Cypriot Citizenship

You can discover more details on the main procedures for obtaining Cypriot citizenship at https://immigration-cyprus.co/obtain-citizenship-in-cyprus/.
Business and Corporate Case Update (2024)

Presentation at the Idaho State Bar Business & Corporate Law Section's Annual Meeting on June 4, 2024
ALL EYES ON RAFAH BUT WHY Explain more.pdf

All eyes on Rafah: But why?. The Rafah border crossing, a crucial point between Egypt and the Gaza Strip, often finds itself at the center of global attention. As we explore the significance of Rafah, we’ll uncover why all eyes are on Rafah and the complexities surrounding this pivotal region.
INTRODUCTION
What makes Rafah so significant that it captures global attention? The phrase ‘All eyes are on Rafah’ resonates not just with those in the region but with people worldwide who recognize its strategic, humanitarian, and political importance. In this guide, we will delve into the factors that make Rafah a focal point for international interest, examining its historical context, humanitarian challenges, and political dimensions.
NATURE, ORIGIN AND DEVELOPMENT OF INTERNATIONAL LAW.pptx

These slides helps the student of international law to understand what is the nature of international law? and how international law was originated and developed?.
The slides was well structured along with the highlighted points for better understanding .
Military Commissions details LtCol Thomas Jasper as Detailed Defense Counsel

Military Commissions Trial Judiciary, Guantanamo Bay, Cuba. Notice of the Chief Defense Counsel's detailing of LtCol Thomas F. Jasper, Jr. USMC, as Detailed Defense Counsel for Abd Al Hadi Al-Iraqi on 6 August 2014 in the case of United States v. Hadi al Iraqi (10026)
Abdul Hakim Shabazz Deposition Hearing in Federal Court

This is Abdul Hakim Shabazz deposition hearing in the Marion County Fairground Boards, money misappropriating scandal.
办理(waikato毕业证书)新西兰怀卡托大学毕业证双学位证书原版一模一样

原版纸张【微信:741003700 】【(waikato毕业证书)新西兰怀卡托大学毕业证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Secure Your Brand: File a Trademark Today

A "File Trademark" is a legal term referring to the registration of a unique symbol, logo, or name used to identify and distinguish products or services. This process provides legal protection, granting exclusive rights to the trademark owner, and helps prevent unauthorized use by competitors.
Visit Now: https://www.tumblr.com/trademark-quick/751620857551634432/ensure-legal-protection-file-your-trademark-with?source=share
Roles of a Bankruptcy Lawyer John Cavitt

Bankruptcy is a complicated process but there are many resources you can use to select the best bankruptcy lawyer for your case.
Rokita Releases Soccer Stadium Legal Opinion

Indiana Attorney General Todd Rokita is weighing in on the proposed MLS soccer stadium project.
Highlights_of_Bhartiya_Nyaya_Sanhita.pptx

In 2020, the Ministry of Home Affairs established a committee led by Prof. (Dr.) Ranbir Singh, former Vice Chancellor of National Law University (NLU), Delhi. This committee was tasked with reviewing the three codes of criminal law. The primary objective of the committee was to propose comprehensive reforms to the country’s criminal laws in a manner that is both principled and effective.
The committee’s focus was on ensuring the safety and security of individuals, communities, and the nation as a whole. Throughout its deliberations, the committee aimed to uphold constitutional values such as justice, dignity, and the intrinsic value of each individual. Their goal was to recommend amendments to the criminal laws that align with these values and priorities.
Subsequently, in February, the committee successfully submitted its recommendations regarding amendments to the criminal law. These recommendations are intended to serve as a foundation for enhancing the current legal framework, promoting safety and security, and upholding the constitutional principles of justice, dignity, and the inherent worth of every individual.
Responsibilities of the office bearers while registering multi-state cooperat...

Responsibilities of the office bearers while registering multi-state cooperat...Finlaw Consultancy Pvt Ltd
Introduction-
The process of register multi-state cooperative society in India is governed by the Multi-State Co-operative Societies Act, 2002. This process requires the office bearers to undertake several crucial responsibilities to ensure compliance with legal and regulatory frameworks. The key office bearers typically include the President, Secretary, and Treasurer, along with other elected members of the managing committee. Their responsibilities encompass administrative, legal, and financial duties essential for the successful registration and operation of the society. Recently uploaded (20)
The Main Procedures for Obtaining Cypriot Citizenship

The Main Procedures for Obtaining Cypriot Citizenship
NATURE, ORIGIN AND DEVELOPMENT OF INTERNATIONAL LAW.pptx

NATURE, ORIGIN AND DEVELOPMENT OF INTERNATIONAL LAW.pptx
Daftar Rumpun, Pohon, dan Cabang Ilmu (28 Mei 2024).pdf

Daftar Rumpun, Pohon, dan Cabang Ilmu (28 Mei 2024).pdf
Military Commissions details LtCol Thomas Jasper as Detailed Defense Counsel

Military Commissions details LtCol Thomas Jasper as Detailed Defense Counsel
Agrarian Reform Policies in the Philippines: a quiz

Agrarian Reform Policies in the Philippines: a quiz
Abdul Hakim Shabazz Deposition Hearing in Federal Court

Abdul Hakim Shabazz Deposition Hearing in Federal Court
Debt Mapping Camp bebas riba to know how much our debt

Debt Mapping Camp bebas riba to know how much our debt
ADR in criminal proceeding in Bangladesh with global perspective.

ADR in criminal proceeding in Bangladesh with global perspective.
Responsibilities of the office bearers while registering multi-state cooperat...

Responsibilities of the office bearers while registering multi-state cooperat...
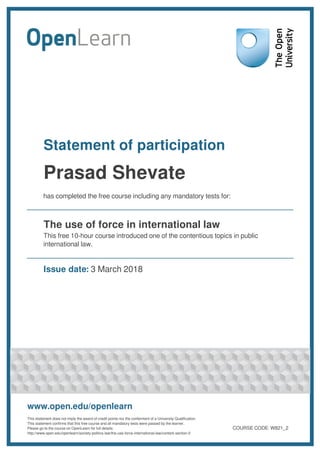
The use of force in international law
- 1. Statement of participation Prasad Shevate has completed the free course including any mandatory tests for: The use of force in international law This free 10-hour course introduced one of the contentious topics in public international law. Issue date: 3 March 2018 www.open.edu/openlearn This statement does not imply the award of credit points nor the conferment of a University Qualification. This statement confirms that this free course and all mandatory tests were passed by the learner. Please go to the course on OpenLearn for full details: http://www.open.edu/openlearn/society-politics-law/the-use-force-international-law/content-section-0 COURSE CODE: W821_2
- 2. The use of force in international law http://www.open.edu/openlearn/society-politics-law/the-use-force-international-law/content-section-0 Course summary This free course, The use of force in international law, is designed to provide you with an introduction to one of the contentious topics in public international law: the use of force. In this course, you will explore international rules governing the use of force, including an introduction to the laws of war (International Humanitarian Law). Finally, you will also consider the dilemma of humanitarian intervention, which you can later apply in the game Saving Setrus. Learning outcomes By completing this course, the learner should be able to: explain the rules governing the law on the use of force and their evolution analyse case examples relating to the use of force in international law and be able to critically analyse how the rules of international law have been (mis)applied in particular situations understand how international law regulates the conduct in wars of both international and non- international character comment on the key challenges to the operation of the rules on the use of force in the contemporary international setting demonstrate enhanced skills and confidence in conducting research in international law. Completed study The learner has completed the following: Section 1 History of the law on the use of force Section 2 The law of armed conflict Section 3 Humanitarian intervention and the responsibility to protect Section 4 Conclusion http://www.open.edu/openlearn COURSE CODE: W821_2 Powered by TCPDF (www.tcpdf.org)