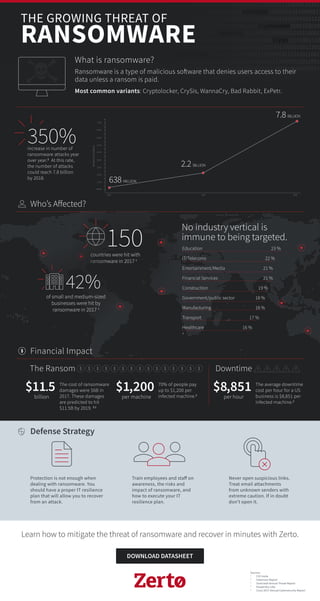
The Growing Threat of Ransomware
- 1. 111001010011001010011101Cryptolocker10001010101010101111000010111110011001010011100010101010101011110000101101 01WannaCry010110011001010011101100010101010101011110000110011001010011101100010101BadRabbit010101011110000111 0101000111001001100101001110110001010101010101111000010101010011100100011001100101001110110001010101010101111 0000101010010011001010011101100010101010101011110000110100010100111001010011001010011101Cryptolocker1000101010 101010111100001011111001100101001110CrySis110001010101010101111000010110101WannaCry01011001100101001110110001 0101010101011110000110011001010011101100010101010101011BadRabbit11000011101010001110010011000CrySis11101001110 1100010101010101011110000101010100111001000110011001010011101100010101010101011110000101010010011001010011101 100010101010101011110000110100010100111001010011001010011101Cryptolocker10001010101010101111000010111110011001 01001110CrySis110001010101010101111000010110101WannaCry010110011001010011101100010101010101011110000110011001 010011101100010101010101011BadRabbit1100001110101000111001001100101001110110001010101010101111000010101010011 Learn how to mitigate the threat of ransomware and recover in minutes with Zerto. Train employees and staff on awareness, the risks and impact of ransomware, and how to execute your IT resilience plan. Protection is not enough when dealing with ransomware. You should have a proper IT resilience plan that will allow you to recover from an attack. Never open suspicious links. Treat email attachments from unknown senders with extreme caution. If in doubt don’t open it. $11.5 billion countries were hit with ransomware in 2017 4 150 increase in number of ransomware attacks year over year.5 At this rate, the number of attacks could reach 7.8 billion by 2018. 350% The cost of ransomware damages were $6B in 2017. These damages are predicted to hit $11.5B by 2019. 3,1 $1,200 per machine 70% of people pay up to $1,200 per infected machine.2 $8,851 per hour The average downtime cost per hour for a US business is $8,851 per infected machine.2 What is ransomware? Financial Impact Defense Strategy Ransomware is a type of malicious software that denies users access to their data unless a ransom is paid. Most common variants: Cryptolocker, CrySis, WannaCry, Bad Rabbit, ExPetr. of small and medium-sized businesses were hit by ransomware in 2017 4 42% THE GROWING THREAT OF RANSOMWARE Education 23 % IT/Telecoms 22 % Entertainment/Media 21 % Financial Services 21 % Construction 19 % Government/public sector 18 % Manufacturing 18 % Transport 17 % Healthcare 16 % 4 No industry vertical is immune to being targeted. The Ransom Downtime Sources 1 CIO Insite 2 Osterman Report 3 Sonicwall Annual Threat Report 4 Kaspersky Labs 5 Cisco 2017 Annual Cybersecurity Report Who’s Affected? 400 M 2016 2017 2018 1.2 B 2.0 B 2.8 B 3.6 B 4.4 B 5.2 B 6.0 B 6.8 B 7.6 B NumberofIncidents
