- SwiftLint is a linting tool for Swift that runs static analysis and identifies style and potential logic issues.
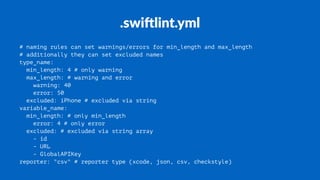
- It can be installed with Homebrew and configured using a .swiflint.yml file to set which rules to enable/disable and rule parameters.
- Rules check things like force casts, line lengths, naming conventions, and more. Many rules support auto-correction to fix issues automatically.
- The tool continues to be actively developed with new rules and improvements over time. Contributions are welcome to add new rules, improve performance, or fix bugs.