Sql server difference between questions list- 1
•
1 like•806 views
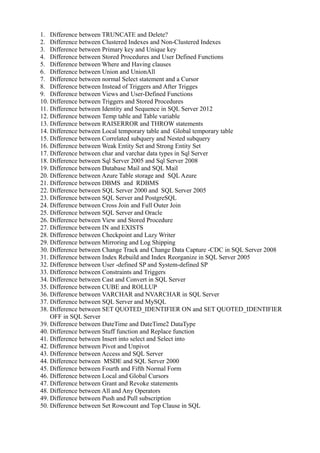
This document lists 50 questions about differences between various SQL concepts and features. It provides a high-level overview of differences between things like TRUNCATE and DELETE, clustered and non-clustered indexes, primary keys and unique keys, stored procedures and user defined functions, and more. The document also provides a link to a blog for further updates on difference-related questions and answers.
Report
Share
Report
Share
Recommended
ADO.NET Difference FAQs-2

This provides a list of ADO.NET FAQs-2 which are of "Difference between" kind
.NET Difference Between Interview Questions - Compiled

This provides a categorized .NET FAQs which are of "Difference between" kind
Dotnet difference between questions list- 1

This provides a list -1 of Dotnet Difference Between Questions
ASP.NET MVC difference between questions list 1

This document provides a brief list of ASP.NET MVC difference between questions.
Recommended
ADO.NET Difference FAQs-2

This provides a list of ADO.NET FAQs-2 which are of "Difference between" kind
.NET Difference Between Interview Questions - Compiled

This provides a categorized .NET FAQs which are of "Difference between" kind
Dotnet difference between questions list- 1

This provides a list -1 of Dotnet Difference Between Questions
ASP.NET MVC difference between questions list 1

This document provides a brief list of ASP.NET MVC difference between questions.
Best interview questions

competency based interview questions and answers and cs technical interview questions
30 top my sql interview questions and answers

30 TOP MySql Interview Questions and Answers, MySql Objective type Questions and Answers
Oracle fundamentals and plsql for beginners

This PL/SQL course is designed for new bees in Database programming world. This course covers writing PL/SQL code
in real world. The training is designed to cover the basic concept to writing PL/SQL Code to writing professional PL/SQL
code for complex business problems. The course also talks about writing optimized PL/SQL Code. The course is going to
cover many real time case studies in various scenarios. Implementing the PL/SQL code for business rules, Data Quality
Checks, working in enterprise Data Warehousing and data transformation rules.
Sql interview question part 6

Learn about SQL Server Interview Questions for further carrier development.
Difference between ActionResult() and ViewResult()

Difference between ActionResult() and ViewResult()
More Related Content
Similar to Sql server difference between questions list- 1
Best interview questions

competency based interview questions and answers and cs technical interview questions
30 top my sql interview questions and answers

30 TOP MySql Interview Questions and Answers, MySql Objective type Questions and Answers
Oracle fundamentals and plsql for beginners

This PL/SQL course is designed for new bees in Database programming world. This course covers writing PL/SQL code
in real world. The training is designed to cover the basic concept to writing PL/SQL Code to writing professional PL/SQL
code for complex business problems. The course also talks about writing optimized PL/SQL Code. The course is going to
cover many real time case studies in various scenarios. Implementing the PL/SQL code for business rules, Data Quality
Checks, working in enterprise Data Warehousing and data transformation rules.
Sql interview question part 6

Learn about SQL Server Interview Questions for further carrier development.
Similar to Sql server difference between questions list- 1 (20)
Most comprehensive list of interview questions for sap bw consultants

Most comprehensive list of interview questions for sap bw consultants
Indows soft solutions experience 2 years in my sql

Indows soft solutions experience 2 years in my sql
More from Umar Ali
Difference between ActionResult() and ViewResult()

Difference between ActionResult() and ViewResult()
Difference between asp.net mvc 3 and asp.net mvc 4

Difference between ASP.NET MVC 3 and ASP.NET MVC 4
Difference between asp.net web api and asp.net mvc

Difference between ASP.NET Web API and ASP.NET MVC
Difference between asp.net web forms and asp.net mvc

Difference between ASP.NET WebForms and ASP.NET MVC
Link checkers 1

Want to know the list of file hosting link checkers to ease your manual method of file checking ?
Affiliate Networks Sites-1

Want to know the list of popular Affiliate Networks site for your online income,then kindly look at this document
Technical Video Training Sites- 1

Want to enhance your technical skills, then kindly look at this document
How to create user friendly file hosting link sites

Want to know How to create user-friendly File Hosting Link Sites ?
Weak hadiths in tamil

Collection of Weak Hadiths in Tamil. This is for creating awareness to the Tamil Muslim Community.
Asp.net website usage and job trends

This provides a brief statistics of how many websites in the world are developed with ASP.Net Technology and the current Job Opportunities of studying the .NET.
Photo sharing sites- 1 

Want to know the list of photo / image sharing sites ?, then look at this document
File hosting search engines

There comes need to find files hosted on file hosting sites alone like rapidshare.com,mediafire.com,extabit.com etc., . Users who want to search effectively, then the following list of file hosting search engines will be useful.
Dotnet differences compiled -1

365 Dotnet Difference Between Questions & Answers from the blog: http://onlydifferencefaqs.blogspot.in/
More from Umar Ali (20)
Difference between ActionResult() and ViewResult()

Difference between ActionResult() and ViewResult()
Difference between asp.net mvc 3 and asp.net mvc 4

Difference between asp.net mvc 3 and asp.net mvc 4
Difference between asp.net web api and asp.net mvc

Difference between asp.net web api and asp.net mvc
Difference between asp.net web forms and asp.net mvc

Difference between asp.net web forms and asp.net mvc
How to create user friendly file hosting link sites

How to create user friendly file hosting link sites
Recently uploaded
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Have you ever wanted a Ruby client API to communicate with your web service? Smithy is a protocol-agnostic language for defining services and SDKs. Smithy Ruby is an implementation of Smithy that generates a Ruby SDK using a Smithy model. In this talk, we will explore Smithy and Smithy Ruby to learn how to generate custom feature-rich SDKs that can communicate with any web service, such as a Rails JSON API.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

In this insightful webinar, Inflectra explores how artificial intelligence (AI) is transforming software development and testing. Discover how AI-powered tools are revolutionizing every stage of the software development lifecycle (SDLC), from design and prototyping to testing, deployment, and monitoring.
Learn about:
• The Future of Testing: How AI is shifting testing towards verification, analysis, and higher-level skills, while reducing repetitive tasks.
• Test Automation: How AI-powered test case generation, optimization, and self-healing tests are making testing more efficient and effective.
• Visual Testing: Explore the emerging capabilities of AI in visual testing and how it's set to revolutionize UI verification.
• Inflectra's AI Solutions: See demonstrations of Inflectra's cutting-edge AI tools like the ChatGPT plugin and Azure Open AI platform, designed to streamline your testing process.
Whether you're a developer, tester, or QA professional, this webinar will give you valuable insights into how AI is shaping the future of software delivery.
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Recently uploaded (20)
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Generating a custom Ruby SDK for your web service or Rails API using Smithy
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
Sql server difference between questions list- 1
- 1. 1. Difference between TRUNCATE and Delete? 2. Difference between Clustered Indexes and Non-Clustered Indexes 3. Difference between Primary key and Unique key 4. Difference between Stored Procedures and User Defined Functions 5. Difference between Where and Having clauses 6. Difference between Union and UnionAll 7. Difference between normal Select statement and a Cursor 8. Difference between Instead of Triggers and After Trigges 9. Difference between Views and User-Defined Functions 10. Difference between Triggers and Stored Procedures 11. Difference between Identity and Sequence in SQL Server 2012 12. Difference between Temp table and Table variable 13. Difference between RAISERROR and THROW statements 14. Difference between Local temporary table and Global temporary table 15. Difference between Correlated subquery and Nested subquery 16. Difference between Weak Entity Set and Strong Entity Set 17. Difference between char and varchar data types in Sql Server 18. Difference between Sql Server 2005 and Sql Server 2008 19. Difference between Database Mail and SQL Mail 20. Difference between Azure Table storage and SQL Azure 21. Difference between DBMS and RDBMS 22. Difference between SQL Server 2000 and SQL Server 2005 23. Difference between SQL Server and PostgreSQL 24. Difference between Cross Join and Full Outer Join 25. Difference between SQL Server and Oracle 26. Difference between View and Stored Procedure 27. Difference between IN and EXISTS 28. Difference between Checkpoint and Lazy Writer 29. Difference between Mirroring and Log Shipping 30. Difference between Change Track and Change Data Capture -CDC in SQL Server 2008 31. Difference between Index Rebuild and Index Reorganize in SQL Server 2005 32. Difference between User -defined SP and System-defined SP 33. Difference between Constraints and Triggers 34. Difference between Cast and Convert in SQL Server 35. Difference between CUBE and ROLLUP 36. Difference between VARCHAR and NVARCHAR in SQL Server 37. Difference between SQL Server and MySQL 38. Difference between SET QUOTED_IDENTIFIER ON and SET QUOTED_IDENTIFIER OFF in SQL Server 39. Difference between DateTime and DateTime2 DataType 40. Difference between Stuff function and Replace function 41. Difference between Insert into select and Select into 42. Difference between Pivot and Unpivot 43. Difference between Access and SQL Server 44. Difference between MSDE and SQL Server 2000 45. Difference between Fourth and Fifth Normal Form 46. Difference between Local and Global Cursors 47. Difference between Grant and Revoke statements 48. Difference between All and Any Operators 49. Difference between Push and Pull subscription 50. Difference between Set Rowcount and Top Clause in SQL
- 2. And, further updates on difference between questions / Q&A, please visit my blog @ http://onlydifferencefaqs.blogspot.in/
