Soil
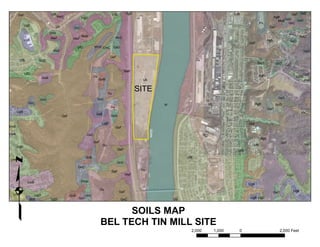
- 1. UfB UfB UgD CoB GsF GsD GsF WeF UgD AgB GsD GsD MoB Pn GsC UgD Ub GnC GsF GnD GsC MoB WnD GvC WeF WeF UgB AgB GsD GsF UfD WnD CmC GsD GsD HaD GsF UfB GnD Du GnD GsD GvD WeF UfD GpF Du AgB UgD UwB GnB Ub HaC Du SITE GnC GpC GnD GnC Ub AgB GpD W Du GsD UgB HaC GsB GsD GsF UgB GsF UwD GsF UwB GsC AgC GsF GpF Du UfB UgD UgD GsF UfD q GnB UfB UwD GnD GnC GsF Du WeF UgD UwB WhB UgB Du UgB GsF GsD UwD UgD GnB GnC BkB GsC Ub UgB UgD UgD GnC SOILS MAP BEL TECH TIN MILL SITE 2,000 1,000 0 2,000 Feet