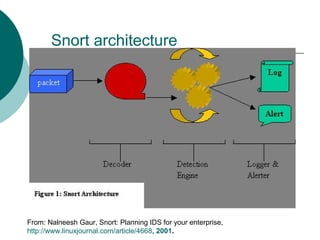
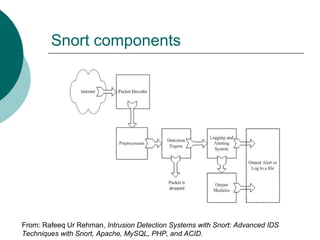
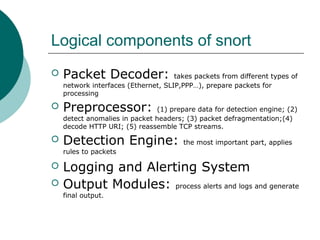
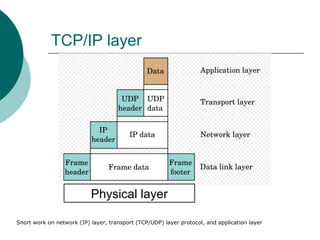
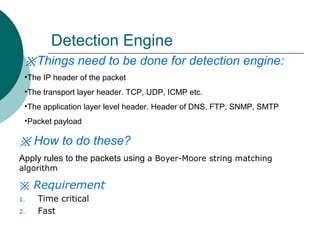
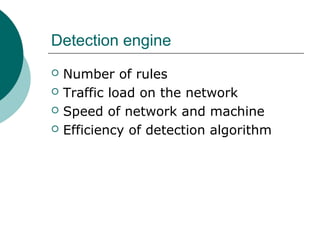
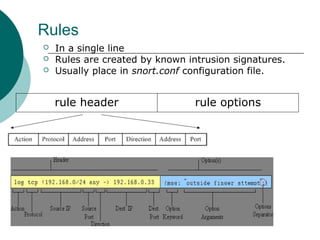
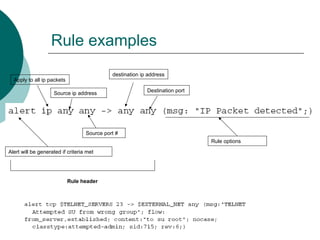
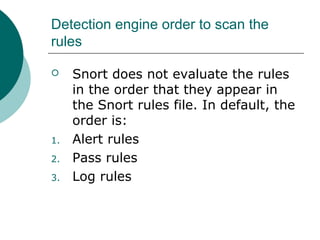
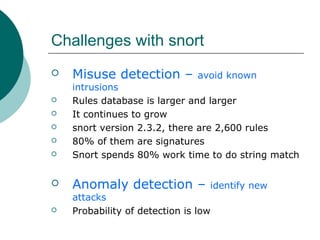
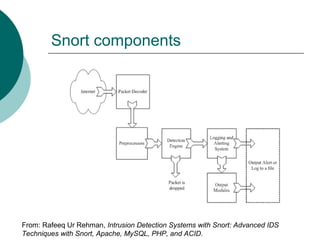
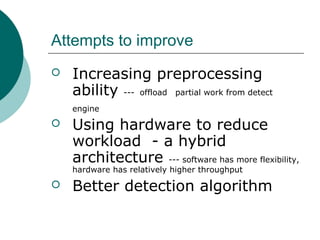
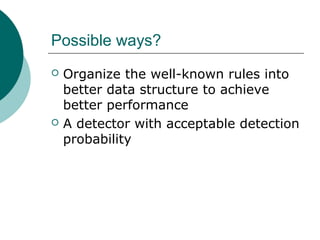
This document summarizes a student's class presentation on the network intrusion prevention and detection system called Snort. It describes what Snort is, its architecture and components, how its detection engine uses rules to detect intrusions, and possible research areas to improve Snort such as developing more efficient detection algorithms or organizing rules into better data structures.