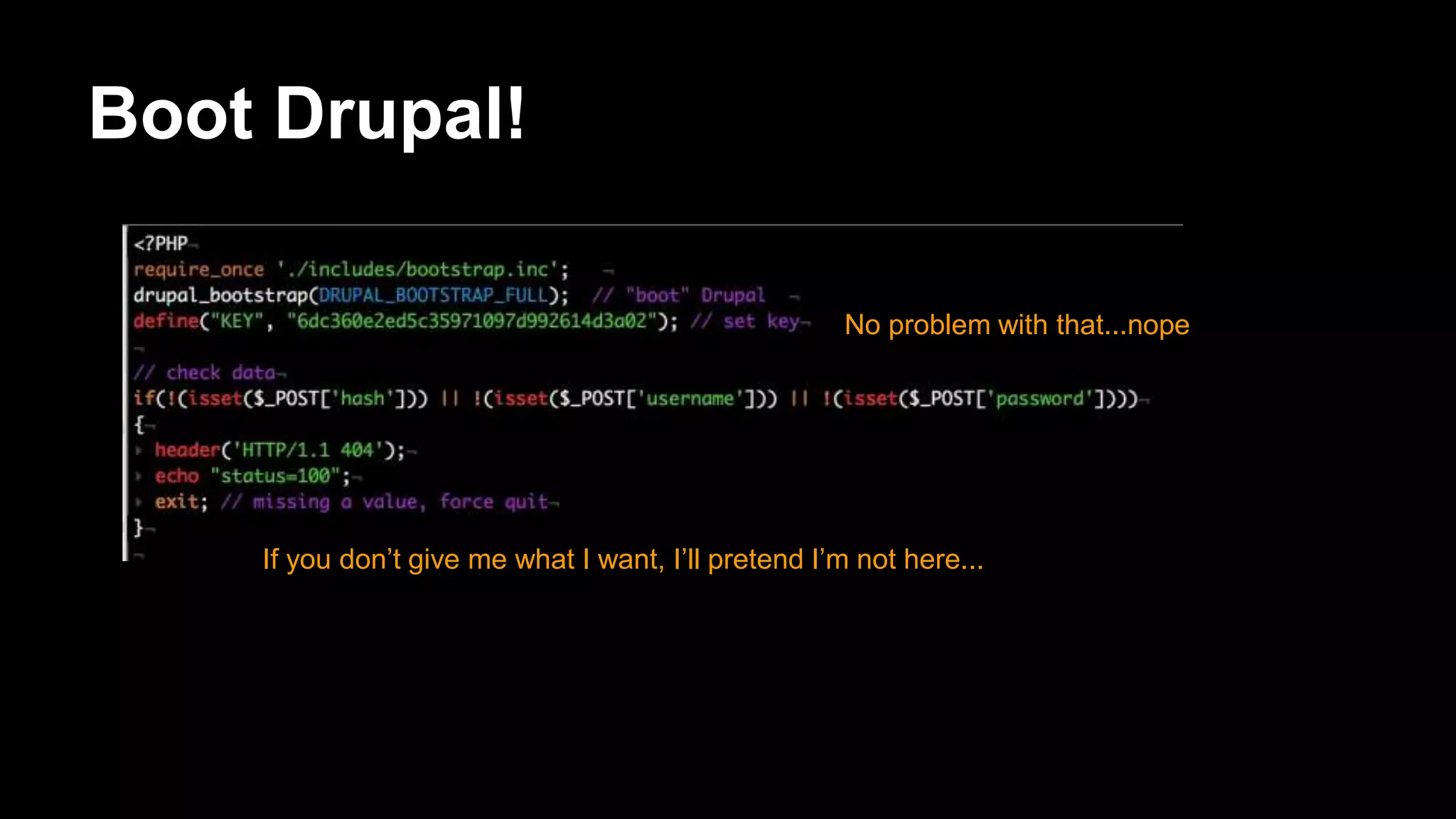
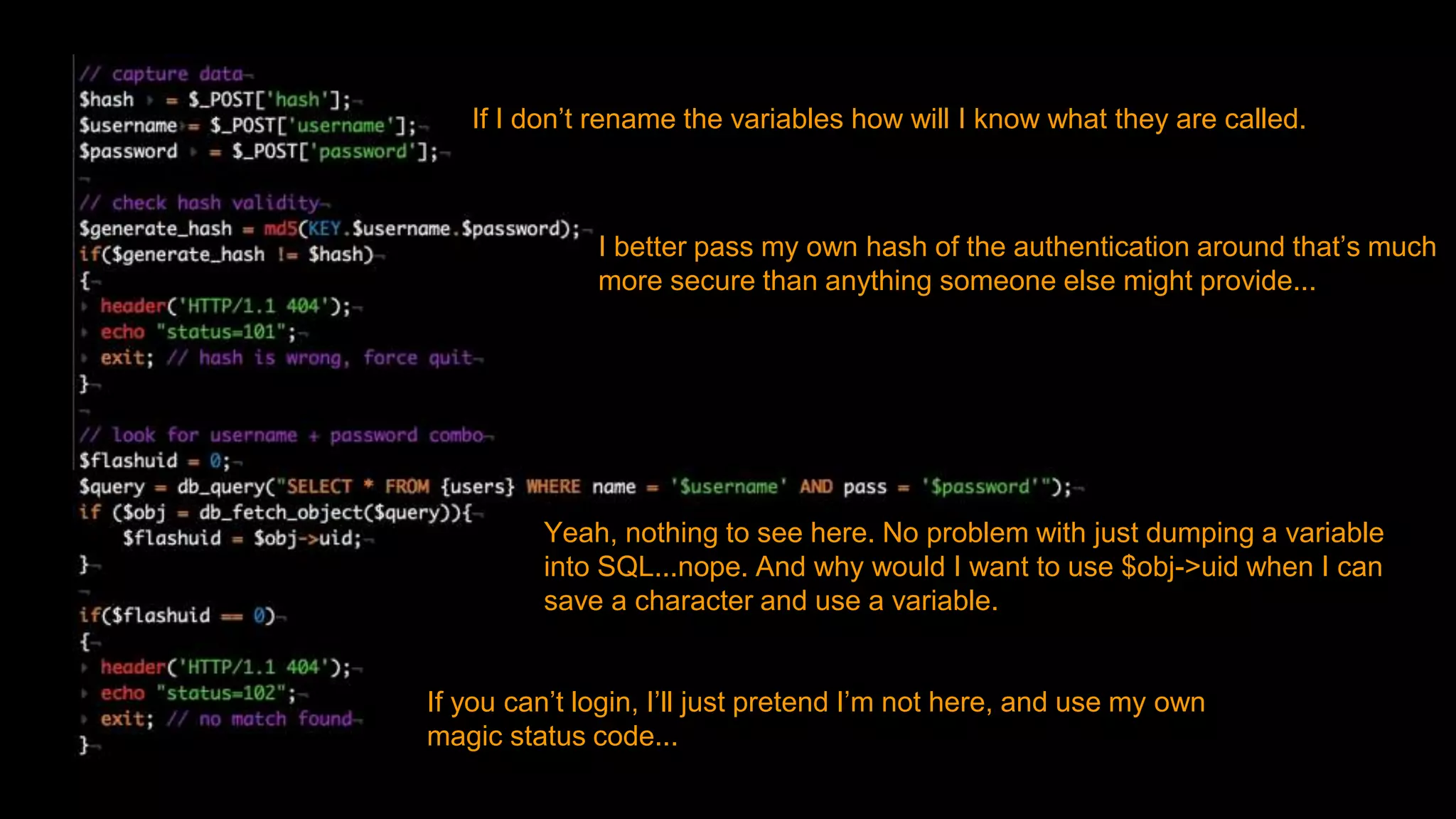
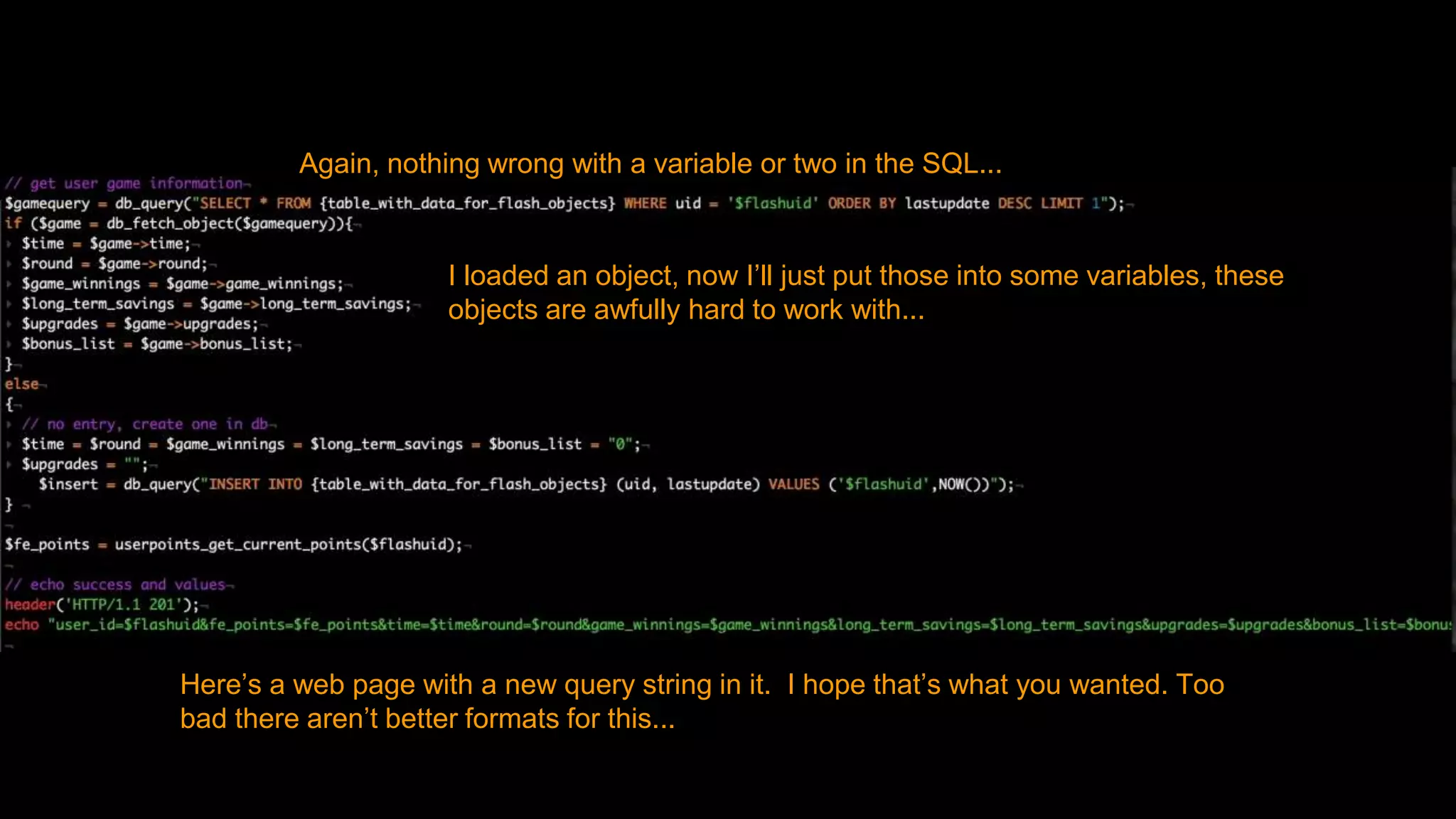
The document discusses sinsful ways developers have integrated third party applications with Drupal by bypassing security protections and treating Drupal like a database. It then provides better solutions like using Drupal's menu and services modules to define custom paths and interfaces, and using Drupal functions and APIs to properly authenticate users, retrieve and save data to the database in a secure manner.
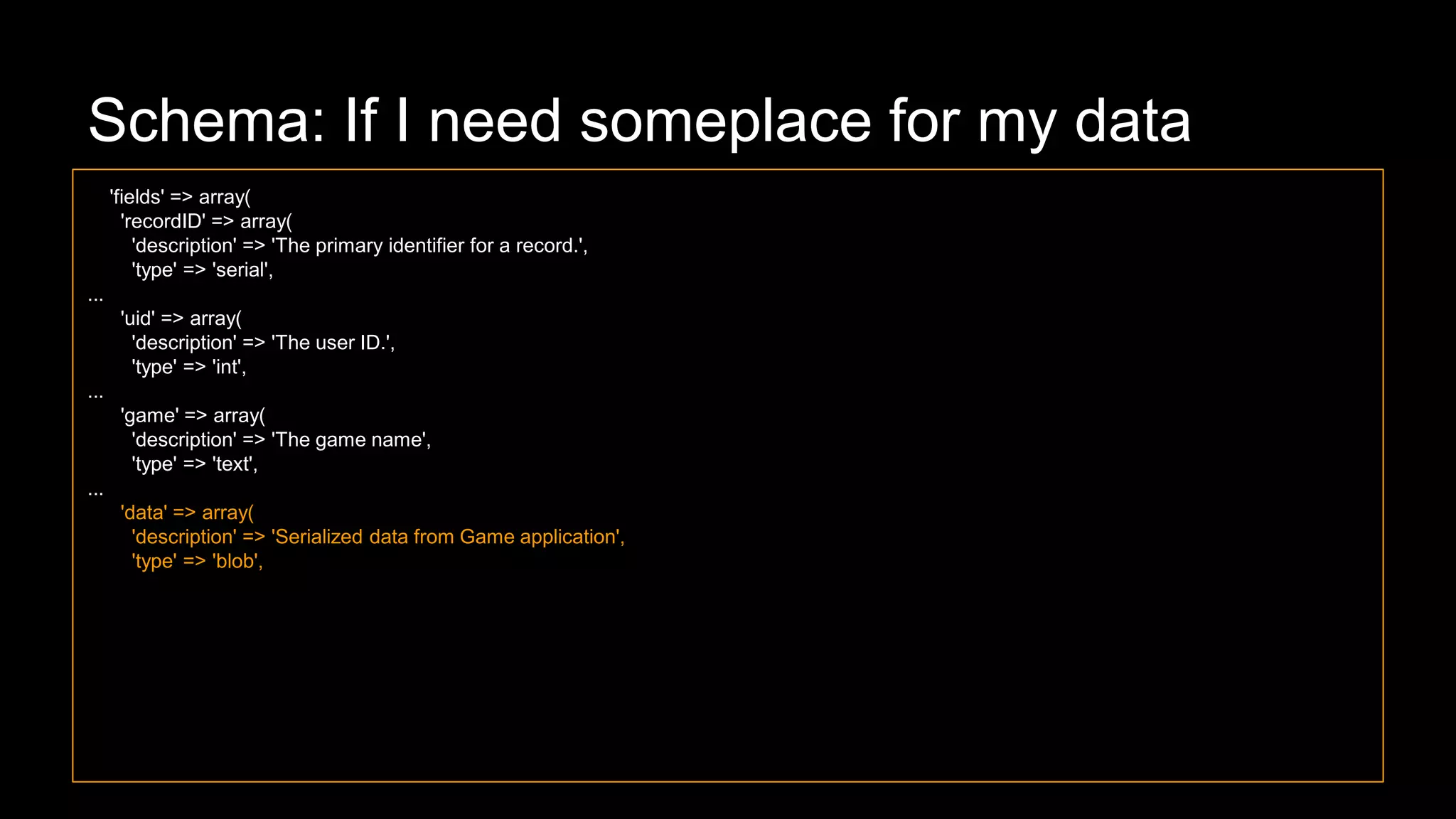
![function hook_menu() {
$items['games/auth'] = array(
'title' => 'Games Authorization',
'page callback' => 'game_module_auth_user',
'access arguments' => array('access content'),
'type' => MENU_CALLBACK,
);
$items['games/game_name/data'] = array( // yes, you could make that a variable instead of hard code
'title' => 'Game Data',
'page callback' => 'game_module_game_name_capture_data', // and if you did you could use one function and pass that variable
'access arguments' => array('player'),
'type' => MENU_CALLBACK,
);
return $items;
}](https://image.slidesharecdn.com/smezxbydt2qhqta9wmgk-signature-1751b3869b6d83b9538d0935c0b1205c0b8cdd47c89d09fa40d86cda1597eda2-poli-160813191758/75/Sins-Against-Drupal-2-8-2048.jpg)
![function game_module_auth_user($user_name = '', $pass = '') { // Here I am using GET, but I don’t have to
global $user;
if($user->uid != 0) { // They are logged in already, so reject them
drupal_access_denied();
}
$account = user_authenticate($user_name, $pass);
//Generate a response based on result....
}
function game_module_[game_name]_capture_data() {
global $user;
if($user->uid == 0) { // They aren’t logged in, so they can’t save data
drupal_access_denied();
}
$record = drupal_get_query_parameters($query = $_POST); // ← we can work with POST just as well as GET if we ask Drupal
to look in the right place.
db_insert('game_data')
->fields(array(
'uid' => $user->uid, 'game' => '[game_name]', 'data' => serialize($record), ))
->execute();
// Provide useful response.
}](https://image.slidesharecdn.com/smezxbydt2qhqta9wmgk-signature-1751b3869b6d83b9538d0935c0b1205c0b8cdd47c89d09fa40d86cda1597eda2-poli-160813191758/75/Sins-Against-Drupal-2-10-2048.jpg)