The Schema Validation filter validates XML inputs against an XSD schema. It is commonly placed at the start of a Mule flow to determine if the incoming message should be handled. If validation fails, the message will not continue in the flow. This filter returns a true or false based on validation and can be wrapped in a message filter to throw exceptions or route to another flow if validation fails. The returnResult parameter controls whether the XML payload is retained if validation passes.
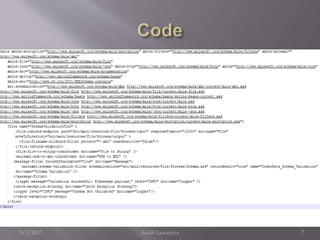
![Now in the XSD XML if we change the any of the element against the schema defined ,we
will be getting the below exception.
ERROR 2017-08-08 21:01:19,585 [[schemavalidation1].SchemaValidationFLow.stage1.02]
org.mule.exception.CatchMessagingExceptionStrategy:
********************************************************************************
Message : Message has been rejected by filter.
Filter : org.mule.module.xml.filters.SchemaValidationFilter@39c5e4bb (null)
Payload : <?xml version="1.0" encoding="UTF-8"?>
Element XML : <message-filter throwOnUnaccepted="true" doc:name="Message">
<mulexml:schema-validation-filter
schemaLocations="src/main/resources/File/Process/Schema.xsd" returnResult="true"
name="OrderData_Schema_Validation" doc:name="Schema Validation"></mulexml:schema-
validation-filter>
</message-filter>
Payload Type : org.apache.xerces.dom.DocumentImpl
Element : /SchemaValidationFLow/processors/2 @
schemavalidation1:schemavalidation1.xml:23 (Message)
--------------------------------------------------------------------------------
Root Exception stack trace:
org.mule.api.routing.filter.FilterUnacceptedException: Message has been rejected by filter.
9/3/2017 Ankit Lawaniya 10](https://image.slidesharecdn.com/schemavalidationfilterxmlschemavalidation-170903131231/85/Schema-validation-filter-xml-schema-validation-10-320.jpg)