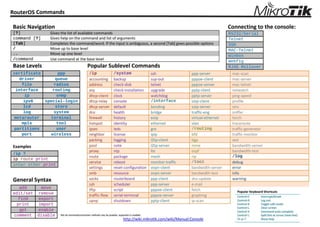
RouterOS Commands
•
0 likes•138 views
คำสั่ง ไมโครติก เร้าเตอร์ ยอดฮิท RouterOS Popular Commands
Report
Share
Report
Share
Download to read offline
Recommended
อัตรา Rain Rate ในแถบ East-Asia 

อัตรา Rain Rate ในแถบ East-Asia
ไว้ สำหรับ ประกอบ การ คำนวณ Fresnel Zone
ขั้นตอนการปรับตำแหน่งจาน Mikrotik mANT 30dBi 5Ghz MIMO ให้ feed สัญญาณ Slant ...

ขั้นตอน การปรับตำแหน่งจาน Mikrotik mANT 30dBi 5Ghz MIMO
ให้ feed สัญญาณ Slant -+45 องศา
ผลของการ feed สัญญาณ +45°/-45° (X)
1.แบบ ±45° ลด RF interference ได้มากกว่าแบบ HV
2.แบบ ±45° ลดการรบกวนจากย่าน microwave ได้
3.สัญญาณเป็นอันหนึ่งอันเดียวกัน เมื่อผ่าน ฝน ทะเล แม่น้ำ
การคอนฟิกส์ OSPF บน Ubiquiti Edge Router

The document provides instructions for configuring three Ubiquiti EdgeRouter devices (R1, R2, R3) with OSPF routing. It describes setting the IP addresses and OSPF parameters for each router, including their router IDs, networks, and areas. It confirms the OSPF configuration is working by showing R1 has learned the route to network 10.0.60.0/24 through R2 and can ping and trace route to R3 on that network. It also lists some common OSPF commands for viewing routes, neighbors, and interface information.
MTCNA Training outline, Certified Network Associate (MTCNA)

This document outlines the training objectives, structure, and modules of a 4-day MikroTik Certified Network Associate (MTCNA) course. The course introduces students to RouterOS software and RouterBoard hardware, and teaches them how to configure a MikroTik router, provide basic network services, and perform basic troubleshooting. It is aimed at network engineers and technicians and assumes knowledge of TCP/IP and subnetting. The course consists of 8 modules covering topics like routing, bridging, wireless networking, firewalls, and VPN tunnels, with each module concluding with hands-on labs to reinforce the material.
MTCWE Training outline, Course prerequisites – MTCNA certificate

This document outlines a training course on MikroTik wireless technologies. It covers topics such as wireless installations, standards, tools, troubleshooting, advanced settings, 802.11n, security, WDS, mesh, bridging, and the Nstreme and Nv2 protocols. Each topic includes objectives and hands-on labs for skills application. The course requires an MTCNA certificate as a prerequisite.
MTCRE Training outline, Course prerequisites – MTCNA certificate

This document outlines a training course on MTCRE that covers topics such as static routing, point-to-point addressing, VPNs, VLANs, and OSPF. Static routing covers more specific routes, ECMP, forcing gateways, and route policies. VPN topics include the different types of VPNs and site-to-site connectivity using tunnels. VLAN sessions cover VLAN usage and QinQ implementation. The OSPF section delves into how the protocol works, its network structure, neighbor states, route distribution, interface configuration, SPT calculation, multicast, area types, virtual links and routing filters.
MTCINE training outline, Course prerequisites – MTCNA and MTCRE certificates

This training outline covers BGP, MPLS, and Traffic Engineering topics. It includes labs for each section to provide hands-on experience. The BGP section will cover the path vector algorithm, different BGP configurations, route selection, and attributes. MPLS concepts like label distribution, VPLS tunnels, and fragmentation will be examined. Finally, traffic engineering principles like CSPF and bandwidth allocation will be demonstrated in labs.
บล๊อกเวปไซท์ บน Open WRT หรือ บน Ubiquiti NanoStation M5 หรือ บน airOS

The document provides instructions for setting up web blocking on an OpenWRT router using DNS redirection or host files. It involves:
1) Connecting via SSH and editing the /etc/persistent/rc.poststart file to add redirection commands
2) Editing the firewall and DNSmasq configuration files to redirect DNS requests to the local router for blocking at the DNS level
3) Rebooting the router to apply the changes and then testing blocked domains.
Recommended
อัตรา Rain Rate ในแถบ East-Asia 

อัตรา Rain Rate ในแถบ East-Asia
ไว้ สำหรับ ประกอบ การ คำนวณ Fresnel Zone
ขั้นตอนการปรับตำแหน่งจาน Mikrotik mANT 30dBi 5Ghz MIMO ให้ feed สัญญาณ Slant ...

ขั้นตอน การปรับตำแหน่งจาน Mikrotik mANT 30dBi 5Ghz MIMO
ให้ feed สัญญาณ Slant -+45 องศา
ผลของการ feed สัญญาณ +45°/-45° (X)
1.แบบ ±45° ลด RF interference ได้มากกว่าแบบ HV
2.แบบ ±45° ลดการรบกวนจากย่าน microwave ได้
3.สัญญาณเป็นอันหนึ่งอันเดียวกัน เมื่อผ่าน ฝน ทะเล แม่น้ำ
การคอนฟิกส์ OSPF บน Ubiquiti Edge Router

The document provides instructions for configuring three Ubiquiti EdgeRouter devices (R1, R2, R3) with OSPF routing. It describes setting the IP addresses and OSPF parameters for each router, including their router IDs, networks, and areas. It confirms the OSPF configuration is working by showing R1 has learned the route to network 10.0.60.0/24 through R2 and can ping and trace route to R3 on that network. It also lists some common OSPF commands for viewing routes, neighbors, and interface information.
MTCNA Training outline, Certified Network Associate (MTCNA)

This document outlines the training objectives, structure, and modules of a 4-day MikroTik Certified Network Associate (MTCNA) course. The course introduces students to RouterOS software and RouterBoard hardware, and teaches them how to configure a MikroTik router, provide basic network services, and perform basic troubleshooting. It is aimed at network engineers and technicians and assumes knowledge of TCP/IP and subnetting. The course consists of 8 modules covering topics like routing, bridging, wireless networking, firewalls, and VPN tunnels, with each module concluding with hands-on labs to reinforce the material.
MTCWE Training outline, Course prerequisites – MTCNA certificate

This document outlines a training course on MikroTik wireless technologies. It covers topics such as wireless installations, standards, tools, troubleshooting, advanced settings, 802.11n, security, WDS, mesh, bridging, and the Nstreme and Nv2 protocols. Each topic includes objectives and hands-on labs for skills application. The course requires an MTCNA certificate as a prerequisite.
MTCRE Training outline, Course prerequisites – MTCNA certificate

This document outlines a training course on MTCRE that covers topics such as static routing, point-to-point addressing, VPNs, VLANs, and OSPF. Static routing covers more specific routes, ECMP, forcing gateways, and route policies. VPN topics include the different types of VPNs and site-to-site connectivity using tunnels. VLAN sessions cover VLAN usage and QinQ implementation. The OSPF section delves into how the protocol works, its network structure, neighbor states, route distribution, interface configuration, SPT calculation, multicast, area types, virtual links and routing filters.
MTCINE training outline, Course prerequisites – MTCNA and MTCRE certificates

This training outline covers BGP, MPLS, and Traffic Engineering topics. It includes labs for each section to provide hands-on experience. The BGP section will cover the path vector algorithm, different BGP configurations, route selection, and attributes. MPLS concepts like label distribution, VPLS tunnels, and fragmentation will be examined. Finally, traffic engineering principles like CSPF and bandwidth allocation will be demonstrated in labs.
บล๊อกเวปไซท์ บน Open WRT หรือ บน Ubiquiti NanoStation M5 หรือ บน airOS

The document provides instructions for setting up web blocking on an OpenWRT router using DNS redirection or host files. It involves:
1) Connecting via SSH and editing the /etc/persistent/rc.poststart file to add redirection commands
2) Editing the firewall and DNSmasq configuration files to redirect DNS requests to the local router for blocking at the DNS level
3) Rebooting the router to apply the changes and then testing blocked domains.
Introduction to Data Centre 3.0

Introduction to Data Centre 3.0
❖ What is Data Centre 3.0?
❖ Why Do I Care?
❖ Layer 2 Multi-path
❖ Data Centre Bridging
Windows Server 2012 R2 products & editions comparison

This document compares editions of Windows Server 2012 R2 and related products. It lists features such as maximum users, RAM, server roles, and features for editions including Windows Server 2012 R2 Datacenter, Standard, Essentials, Foundation, Hyper-V Server 2012 R2, and Windows Storage Server 2012 R2 Standard and Workgroup. Key differences between editions are related to licensing limits, supported server roles and features, and virtualization capabilities.
Settings MikroTik Router and Access Point to schedule AP radio on off via script

ตัวอย่าง การใช้ MikroTik Script ปิด-เปิด สัญญาณ AP เป็นเวลา เปิดปิดเน็ตเป็นเวลา (Settings MikroTik Router or Access Point to schedule AP radio on off via script)
แนะนำแนวทางการออกแบบ การปรับแต่ง การรับส่งสัญญาณ airFiber 24 - airFiber Desig...

The document provides guidelines for optimizing the configuration of an airFiber AF24 wireless platform. It recommends using Frequency Division Duplexing (FDD) for maximum speed and lowest latency, as well as for line-of-sight installations free of reflections. Time Division Duplexing (TDD) is recommended for installations in environments with scattering, heavy rain, or foliage, as it provides higher robustness at the cost of reduced throughput and slightly higher latency. The document also provides tips on establishing an initial link and fine-tuning the alignment between the master and slave units.
How to link public addresses (real ip) to private ip or lan ip

The document provides instructions for configuring Network Address Translation (NAT) on a router to link private IP addresses on a local area network to public IP addresses. It describes adding two public IP addresses and a private address to the router's interfaces, setting a default route specifying one public address, creating a destination NAT rule to access an internal server via a public address, and source NAT rules to translate the internal server's address and other hosts' addresses to the public addresses.
FAQ - Rogue AP - What is Rogue Access Point?

Rogue access points pose a security threat to enterprise networks by providing unauthorized wireless access to the wired network. Traditional defenses like firewalls and encryption are ineffective against rogue APs. A wireless intrusion prevention system uses sensors and wireless/wired connectivity testing to automatically detect, classify, locate, and block rogue APs on the network. Accurately testing an AP's connectivity to the enterprise network is key to reliable rogue AP protection.
เอกสาร แนวทาง การอินติเกรท Mac OS X เข้ากับ ระบบ Active Directory อย่างไร Bes...

เอกสาร แนวทาง การเชื่อมโยง Mac OS X เข้ากับระบบ Active Directory อย่างไร
Best Practices How to Integrating Mac OS X with Active Directory Technical White Paper
Windows server 2012 r2 Hyper-v Component architecture 

Windows server 2012 r2 Hyper-V Component Architecture
แผนภาพโปสเตอร์ของส่วนประกอบทางสถาปัตยกรรมของระบบ
ใน Windows Server 2012 R2
แผนภาพ โปสเตอร์ ขนาดใหญ่ 48 X 24 นิ้ว
Gigabit Wi-Fi 802.11AC In Depth

This document summarizes key aspects of 802.11ac including:
- 802.11ac aims to support wireless speeds over 1Gbps for multi-station throughput and 500Mbps for single links.
- It utilizes wider 80/160MHz channels, more spatial streams up to 8, 256-QAM, and downlink multi-user MIMO.
- These new features and techniques are aimed at supporting bandwidth-intensive applications like wireless display and distribution of high-definition video content.
ค่า Tx Power Mode ใน Ubiquiti และ Mikrotik (RF Tx Power Mode Settings)

1) The document investigates the power settings of Ubiquiti radio cards when used with Mikrotik software. It finds that using Mikrotik's power override setting can cause throughput degradation, compliance issues, and reliability problems.
2) Testing showed that the default power settings produced the best results in terms of throughput and output power. Increasing power above specifications slowed throughput and caused other issues.
3) The document concludes that the default power settings should always be used, and provides information on power offsets and Mikrotik's implementation for different Ubiquiti card models.
SwOS (MikroTik Switch OS) Administration Guide

SwOS is an operating system designed specifically for administration of MikroTik Switch products that use Switch OS (SwOS) for RB250GS and now RB260GS with SFP Port for extend the network to up to 20KM ans support VLAN and VLAN Trunk on Gigabit Ethernet.
ความรู้เกี่ยวกับ MikroTik Nstreme Version 2 (Nv2)

ความรู้เกียวกับ MikroTik Nstreme Version 2 (Nv2)
New and Improved Wireless Networking with
Nstreme Version 2
RouterOS v6

RouterOS v6 will include several new features and improvements, including support for new hardware, an updated Linux kernel, additional CPU architecture support, and a reworked QoS system. It features improved performance on multi-CPU systems, enhanced interface drivers, lifted CPU core limits, and simplified simple queue configuration. New capabilities include wireless advanced channels, SCEP protocol support, and more flexible DHCP options handling.
Building a hyper v cluster for under $2,000 - ข้อมูลสำหรับ สร้าง Hyper-V 2012...

Building Hyper-V Cluster for under $2,000 - ข้อมูลสำหรับ สร้าง Hyper-V 2012 เป็น Cluster แบบใช้ค่าใช้จ่ายต่ำ ประมาณ 5-6 หมืนบาท
Solution Wireless Link 10 – 20 KM Speed 200 Mbps MikroTik RB SXT 5nDr2 Lite 5...

Solution Wireless Link 10 – 20 KM Speed 200 Mbps MikroTik RB SXT 5nDr2 Lite 5 - RB SXT 5nDr2 Lite 5 Complete Set
ระบบ Authentication (SCIPA Solution) For Education

ระบบ Authentication (SCIPA Solution) For Education
CIPA Compliance Information

1) The document discusses the Children's Internet Protection Act (CIPA) requirements for schools and libraries to receive E-Rate discounts, including using filtering technology and having an internet safety policy.
2) It provides examples of appropriate documentation for certifying that an organization is "undertaking actions" to comply with CIPA such as discussing procurement of filtering technology or internet safety policies.
3) A sample internet safety policy that complies with CIPA requirements is included, covering topics like blocking inappropriate content and monitoring student internet usage.
More Related Content
More from Tũi Wichets
Introduction to Data Centre 3.0

Introduction to Data Centre 3.0
❖ What is Data Centre 3.0?
❖ Why Do I Care?
❖ Layer 2 Multi-path
❖ Data Centre Bridging
Windows Server 2012 R2 products & editions comparison

This document compares editions of Windows Server 2012 R2 and related products. It lists features such as maximum users, RAM, server roles, and features for editions including Windows Server 2012 R2 Datacenter, Standard, Essentials, Foundation, Hyper-V Server 2012 R2, and Windows Storage Server 2012 R2 Standard and Workgroup. Key differences between editions are related to licensing limits, supported server roles and features, and virtualization capabilities.
Settings MikroTik Router and Access Point to schedule AP radio on off via script

ตัวอย่าง การใช้ MikroTik Script ปิด-เปิด สัญญาณ AP เป็นเวลา เปิดปิดเน็ตเป็นเวลา (Settings MikroTik Router or Access Point to schedule AP radio on off via script)
แนะนำแนวทางการออกแบบ การปรับแต่ง การรับส่งสัญญาณ airFiber 24 - airFiber Desig...

The document provides guidelines for optimizing the configuration of an airFiber AF24 wireless platform. It recommends using Frequency Division Duplexing (FDD) for maximum speed and lowest latency, as well as for line-of-sight installations free of reflections. Time Division Duplexing (TDD) is recommended for installations in environments with scattering, heavy rain, or foliage, as it provides higher robustness at the cost of reduced throughput and slightly higher latency. The document also provides tips on establishing an initial link and fine-tuning the alignment between the master and slave units.
How to link public addresses (real ip) to private ip or lan ip

The document provides instructions for configuring Network Address Translation (NAT) on a router to link private IP addresses on a local area network to public IP addresses. It describes adding two public IP addresses and a private address to the router's interfaces, setting a default route specifying one public address, creating a destination NAT rule to access an internal server via a public address, and source NAT rules to translate the internal server's address and other hosts' addresses to the public addresses.
FAQ - Rogue AP - What is Rogue Access Point?

Rogue access points pose a security threat to enterprise networks by providing unauthorized wireless access to the wired network. Traditional defenses like firewalls and encryption are ineffective against rogue APs. A wireless intrusion prevention system uses sensors and wireless/wired connectivity testing to automatically detect, classify, locate, and block rogue APs on the network. Accurately testing an AP's connectivity to the enterprise network is key to reliable rogue AP protection.
เอกสาร แนวทาง การอินติเกรท Mac OS X เข้ากับ ระบบ Active Directory อย่างไร Bes...

เอกสาร แนวทาง การเชื่อมโยง Mac OS X เข้ากับระบบ Active Directory อย่างไร
Best Practices How to Integrating Mac OS X with Active Directory Technical White Paper
Windows server 2012 r2 Hyper-v Component architecture 

Windows server 2012 r2 Hyper-V Component Architecture
แผนภาพโปสเตอร์ของส่วนประกอบทางสถาปัตยกรรมของระบบ
ใน Windows Server 2012 R2
แผนภาพ โปสเตอร์ ขนาดใหญ่ 48 X 24 นิ้ว
Gigabit Wi-Fi 802.11AC In Depth

This document summarizes key aspects of 802.11ac including:
- 802.11ac aims to support wireless speeds over 1Gbps for multi-station throughput and 500Mbps for single links.
- It utilizes wider 80/160MHz channels, more spatial streams up to 8, 256-QAM, and downlink multi-user MIMO.
- These new features and techniques are aimed at supporting bandwidth-intensive applications like wireless display and distribution of high-definition video content.
ค่า Tx Power Mode ใน Ubiquiti และ Mikrotik (RF Tx Power Mode Settings)

1) The document investigates the power settings of Ubiquiti radio cards when used with Mikrotik software. It finds that using Mikrotik's power override setting can cause throughput degradation, compliance issues, and reliability problems.
2) Testing showed that the default power settings produced the best results in terms of throughput and output power. Increasing power above specifications slowed throughput and caused other issues.
3) The document concludes that the default power settings should always be used, and provides information on power offsets and Mikrotik's implementation for different Ubiquiti card models.
SwOS (MikroTik Switch OS) Administration Guide

SwOS is an operating system designed specifically for administration of MikroTik Switch products that use Switch OS (SwOS) for RB250GS and now RB260GS with SFP Port for extend the network to up to 20KM ans support VLAN and VLAN Trunk on Gigabit Ethernet.
ความรู้เกี่ยวกับ MikroTik Nstreme Version 2 (Nv2)

ความรู้เกียวกับ MikroTik Nstreme Version 2 (Nv2)
New and Improved Wireless Networking with
Nstreme Version 2
RouterOS v6

RouterOS v6 will include several new features and improvements, including support for new hardware, an updated Linux kernel, additional CPU architecture support, and a reworked QoS system. It features improved performance on multi-CPU systems, enhanced interface drivers, lifted CPU core limits, and simplified simple queue configuration. New capabilities include wireless advanced channels, SCEP protocol support, and more flexible DHCP options handling.
Building a hyper v cluster for under $2,000 - ข้อมูลสำหรับ สร้าง Hyper-V 2012...

Building Hyper-V Cluster for under $2,000 - ข้อมูลสำหรับ สร้าง Hyper-V 2012 เป็น Cluster แบบใช้ค่าใช้จ่ายต่ำ ประมาณ 5-6 หมืนบาท
Solution Wireless Link 10 – 20 KM Speed 200 Mbps MikroTik RB SXT 5nDr2 Lite 5...

Solution Wireless Link 10 – 20 KM Speed 200 Mbps MikroTik RB SXT 5nDr2 Lite 5 - RB SXT 5nDr2 Lite 5 Complete Set
ระบบ Authentication (SCIPA Solution) For Education

ระบบ Authentication (SCIPA Solution) For Education
CIPA Compliance Information

1) The document discusses the Children's Internet Protection Act (CIPA) requirements for schools and libraries to receive E-Rate discounts, including using filtering technology and having an internet safety policy.
2) It provides examples of appropriate documentation for certifying that an organization is "undertaking actions" to comply with CIPA such as discussing procurement of filtering technology or internet safety policies.
3) A sample internet safety policy that complies with CIPA requirements is included, covering topics like blocking inappropriate content and monitoring student internet usage.
More from Tũi Wichets (20)
Windows Server 2012 R2 products & editions comparison

Windows Server 2012 R2 products & editions comparison
Settings MikroTik Router and Access Point to schedule AP radio on off via script

Settings MikroTik Router and Access Point to schedule AP radio on off via script
แนะนำแนวทางการออกแบบ การปรับแต่ง การรับส่งสัญญาณ airFiber 24 - airFiber Desig...

แนะนำแนวทางการออกแบบ การปรับแต่ง การรับส่งสัญญาณ airFiber 24 - airFiber Desig...
How to link public addresses (real ip) to private ip or lan ip

How to link public addresses (real ip) to private ip or lan ip
เอกสาร แนวทาง การอินติเกรท Mac OS X เข้ากับ ระบบ Active Directory อย่างไร Bes...

เอกสาร แนวทาง การอินติเกรท Mac OS X เข้ากับ ระบบ Active Directory อย่างไร Bes...
Windows server 2012 r2 Hyper-v Component architecture 

Windows server 2012 r2 Hyper-v Component architecture
ค่า Tx Power Mode ใน Ubiquiti และ Mikrotik (RF Tx Power Mode Settings)

ค่า Tx Power Mode ใน Ubiquiti และ Mikrotik (RF Tx Power Mode Settings)
Building a hyper v cluster for under $2,000 - ข้อมูลสำหรับ สร้าง Hyper-V 2012...

Building a hyper v cluster for under $2,000 - ข้อมูลสำหรับ สร้าง Hyper-V 2012...
Solution Wireless Link 10 – 20 KM Speed 200 Mbps MikroTik RB SXT 5nDr2 Lite 5...

Solution Wireless Link 10 – 20 KM Speed 200 Mbps MikroTik RB SXT 5nDr2 Lite 5...
ระบบ Authentication (SCIPA Solution) For Education

ระบบ Authentication (SCIPA Solution) For Education
