Registration form tk12
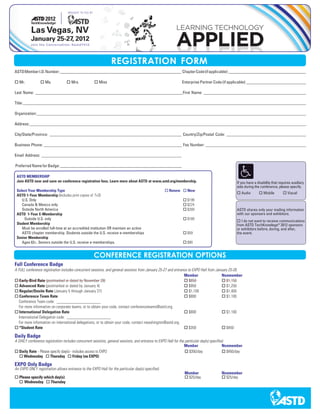
- 1. REGISTRATION FORM ASTD Member I.D. Number: __________________________________________________________ Chapter Code (if applicable): _____________________________________ o Mr. o Ms. o Mrs. o Miss Enterprise Partner Code (if applicable): _____________________________ Last Name: ______________________________________________________________________ First Name: _________________________________________________ Title: _________________________________________________________________ _______________________________________________________________________ Organization: _____________________________________________________________ ____________________________________________________________________ Address: _______________________________________________________________ _______________________________________________________________________ City/State/Province: _______________________________________________________________ Country/Zip/Postal Code: ______________________________________ Business Phone: __________________________________________________________________ Fax Number: ________________________________________________ Email Address: ___________________________________________________________________ Preferred Name for Badge: __________________________________________________________ ASTD MEMBERSHIP Join ASTD now and save on conference registration fees. Learn more about ASTD at www.astd.org/membership. If you have a disability that requires auxiliary aids during the conference, please specify. Select Your Membership Type o Renew o New o Audio o Mobile o Visual ASTD 1-Year Membership (Includes print copies of T+D) U.S. Only o $199 Canada & Mexico only o $224 Outside North America o $269 ASTD shares only your mailing information ASTD 1-Year E-Membership with our sponsors and exhibitors. Outside U.S. only o $169 o I do not want to receive communications Student Membership from ASTD TechKnowlege® 2012 sponsors Must be enrolled full-time at an accredited institution OR maintain an active or exhibitors before, during, and after, ASTD chapter membership. Students outside the U.S. receive e-memberships o $59 the event. Senior Membership Ages 62+. Seniors outside the U.S. receive e-memberships. o $90 CONFERENCE REGISTRATION OPTIONS Full Conference Badge A FULL conference registration includes concurrent sessions, and general sessions from January 25-27 and entrance to EXPO Hall from January 25-26. Member Nonmember o Early-Bird Rate (postmarked or dated by November 28) o $850 o $1,150 o Advanced Rate (postmarked or dated by January 4) o $950 o $1,250 o Regular/Onsite Rate (January 5 through January 27) o $1,100 o $1,400 o Conference Team Rate o $800 o $1,100 Conference Team code: _____________________ For more information on corporate teams, or to obtain your code, contact conferenceteams@astd.org. o International Delegation Rate o $800 o $1,100 International Delegation code: _____________________ For more information on international delegations, or to obtain your code, contact nwashington@astd.org. o *Student Rate o $350 o $450 Daily Badge A DAILY conference registration includes concurrent sessions, general sessions, and entrance to EXPO Hall for the particular day(s) specified. Member Nonmember o Daily Rate - Please specify day(s) - includes access to EXPO o $350/day o $450/day o Wednesday o Thursday o Friday (no EXPO) EXPO Only Badge An EXPO ONLY registration allows entrance to the EXPO Hall for the particular day(s) specified. Member Nonmember o Please specify which day(s): o $25/day o $25/day o Wednesday o Thursday
- 2. Last Name: First Name: ASTD Member I.D. Number (if applicable): PRECONFERENCE WORKSHOPS AND CERTIFICATE PROGRAMS Events Full-day Preconference Workshops – January 24, 2012 (9:00 a.m. - 5:00 p.m.) Member Nonmember o Workshop 1 - Creating Scenarios and Story Interactions Using Articulate StoryLine ® o $405 o $505 o Workshop 2 - Prototyping for Mobile on a Shoestring Budget with Virtually No Tech Skills! o $405 o $505 o Workshop 3 - Lights! Camera! Training! How to Create Video for Training o $405 o $505 o Workshop 4 - Photoshop: From introduction to fixing and preparing digital images o $405 o $505 Half-day Preconference Workshops – January 24, 2012 Member Nonmember o Workshop 5 - ISD for the Synchronous Environment (8:30 a.m. - 12:00 p.m.) o $200 o $300 o Workshop 6 - Making E-Learning Stick: Techniques To Increase Transfer of Training (1:00 p.m. - 4:30 p.m.) o $200 o $300 o Workshop 7 - Hands-on with A Variety of Technology Based Learning Tools (8:30 a.m. - 12:00 p.m.) o $200 o $300 o Workshop 8 - Introducing a Social Learning System for Formal and Informal Learning (1:00 p.m. - 4:30 p.m.) o $200 o $300 o Workshop 9 - Video Editing for Trainers (1:00 p.m. - 5:00 p.m.) o $200 o $300 Certificate Programs – January 22 – January 24, 2012 (8:30 a.m. - 4:30 p.m.) Member Nonmember Designing Learning Certificate (DLLV0112) o $1,495 o $1,795 Measuring and Evaluating Learning Certificate (MELLV0112) o $1,495 o $1,795 Training Certificate (TCLV0112) o $1,395 o $1,695 Certificate Programs – January 23 – January 24, 2012 (8:30 a.m. - 4:30 p.m.) Member Nonmember Advanced E-learning Instructional Design Certificate (AELLV0112) o $1,295 o $1,595 Blended Learning Certificate (BLLV0112) o $1,295 o $1,595 Consulting Skills for Trainers Certificate (CSTLV0112) o $1,095 o $1,395 CPLP Study Prep Workshop (PRELV0112) o $995 o $1,295 E-learning Instructional Design Certificate (ELLV0112) o $1,095 o $1,395 Managing Organizational Knowledge Certificate (MOKLV0112) o $1,095 o $1,395 Multimedia for Instructional Designers Certificate Program (MIDLV0112) o $1,295 o $1,595 Project Management for Learning Professionals (PMLV0112) o $1,095 o $1,395 PAYMENT INFORMATION 5 Total Fee: _______________ Easy Way to Register! Please check method of payment: online: www.tk12.astd.org o VISA o MasterCard o Discover o American Express fax: 1.703.299.8723 phone: 1.800.628.2783 or Card Number Expiration Date 1.703.683.8100 mail: American Society for Signature Today’s Date Training & Development P.O. Box 1567 Merrifield, VA U.S.A. o Purchase order number – A signed P.O. must accompany this form on company letterhead. 22116-1567 o Check Enclosed – Please make checks payable to ASTD in U.S. dollars. Registration cannot be processed if check is not enclosed. wire transfer: Please call 1.703.683.8100 o Wire transfer – Registration cannot be processed until wire is received. Call Customer Care for wire transfer info. for complete instructions 111119.45410 Badge Credentials will be mailed to attendees who have registered before December 13, 2011. There will be no refunds issued after December 13, 2011. All cancellations prior to December 13, 2011 are required in writing and a $50 cancellation fee will apply. Online and pre-registration ends at 6:00 p.m. EST on January 17, 2012. After this time, attendees will need to register onsite. Visit www.astd.org/cancellation for complete terms and conditions. All credits issued must be used within a year. *12 credit hours per year required to be eligible for student rate.
