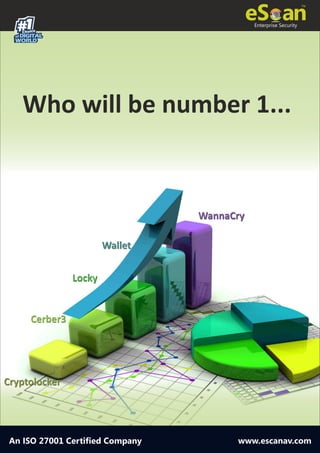
Ransomwares variants vying for the top slot
- 1. 1#Choice of DIGITAL WORLD Enterprise Security An ISO 27001 Certified Company www.escanav.com Who will be number 1... WannaCry Wallet Cerber3 Locky CryptolockerCryptolocker Cerber3 Locky Wallet WannaCry
- 2. An ISO 27001 Certified Company RANSOMWARES VARIANTS VYING FOR THE TOP SLOT WannaCry Ransomware is a game changer at all level in the arena ruled by the likes of Reveton, CryptoLocker, CryptoWall, Locky etc. WannaCry utilized not the encryption capabilities but also exploited vulnerabilities to propagate. WannaCry gained prominence due to its worm-like propagation method and due to sheer fact that the Eternal Blue vulnerability used by it was in-fact found in the arsenal of NSA. However, for past week WannaCry wasn’t the only Ransomware which wrecked havoc, Wallet and JAFF have too dominated, although the focus was on WannaCry. Our R&D team, has released the breakdown of the various Ransomwares attacks in past week, added that in the coming few weeks, moreover there would be an increase in such attacks. However we could observe increased activity amongst the various variants and families of different Ransomwares, vying for the top-position.
- 3. An ISO 27001 Certified Company From the available statistics it is apparent that Wallet/Jaff Ransomware commanded 41% of the total Ransomware incidents, while WannaCry was at 11%. There are other families of Ransomware which have continued to maintain their onslaught however; these are intermittent attempts which just add up to the numbers. However, it is to be noted that Ransomware, be it any variant of any family, is the most destructive piece of malware to have ever been created. The future is bleak, due to the fact that the anonymity offered by Crypto- Currencies has been embraced by cyber-criminals and till such time the currency conversion is handled by private / non-government organizations, Crypto-Currencies would gain prominence amongst the criminals and Ransomware would continue to rule the roost. There is stiff competition amongst the various families Ransomwares, as to who is the best and better of all and as we can observe, the fight for the Top Place has already begun. Would it be too early for us to state that Locky Ransomware is steadily loosing its market value in the Underground (Dark-Web) Market Places or shall we wait for the time to prove us correct once again? The cyber-crime ecosystem thrives on: 1. Fame. 2. The depth of the attack. 3. Stability of the infection. 4. Reliability of the Malware. 5. The most important of all, the ability of the authors to provide FUD (Fully Undetectable) at a very fast pace. Cyber Criminals are aware of these facts and in order to increase their revenue and grab their share of spoils are working hard to unleash a new wave of destruction.
