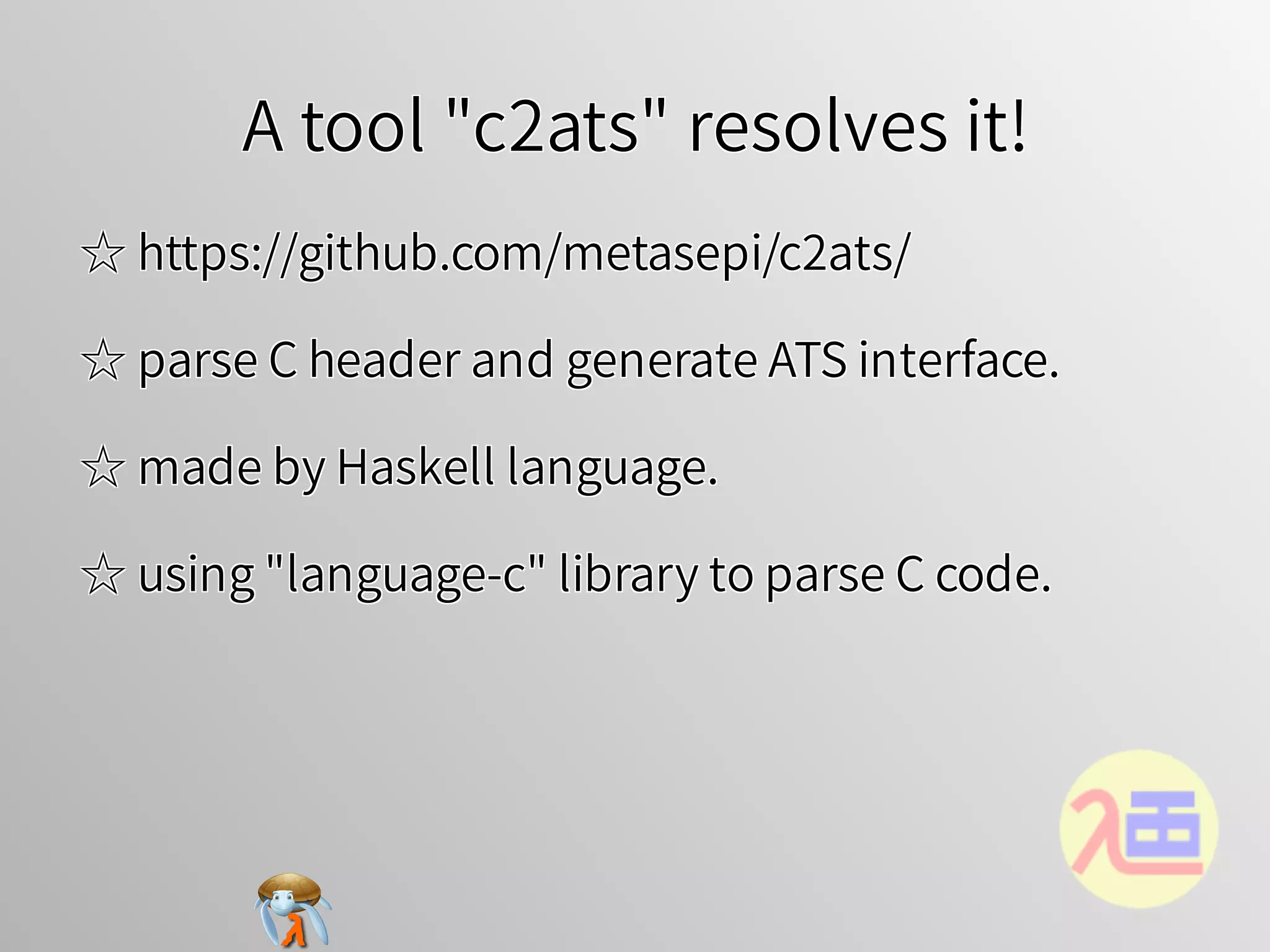
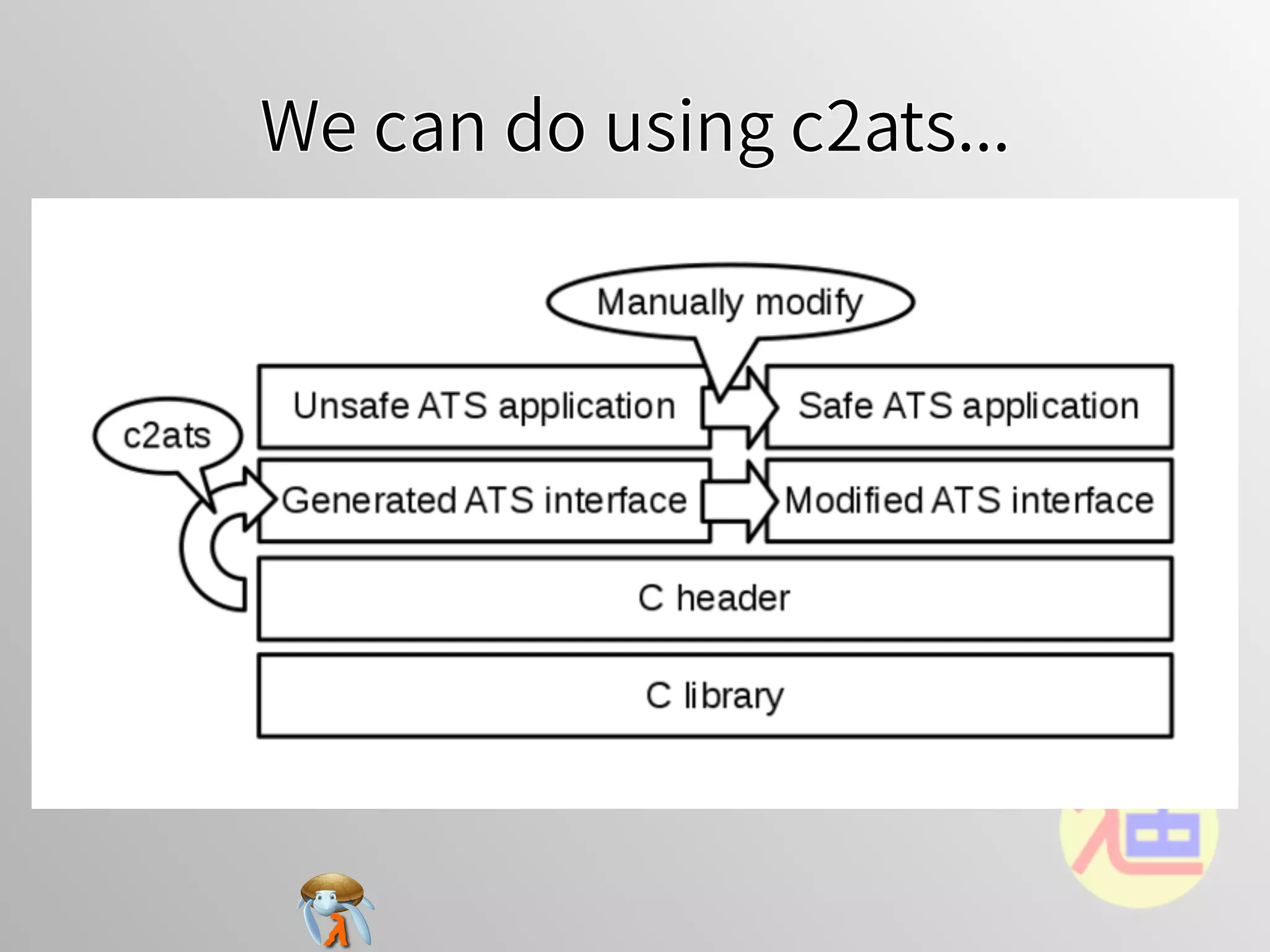
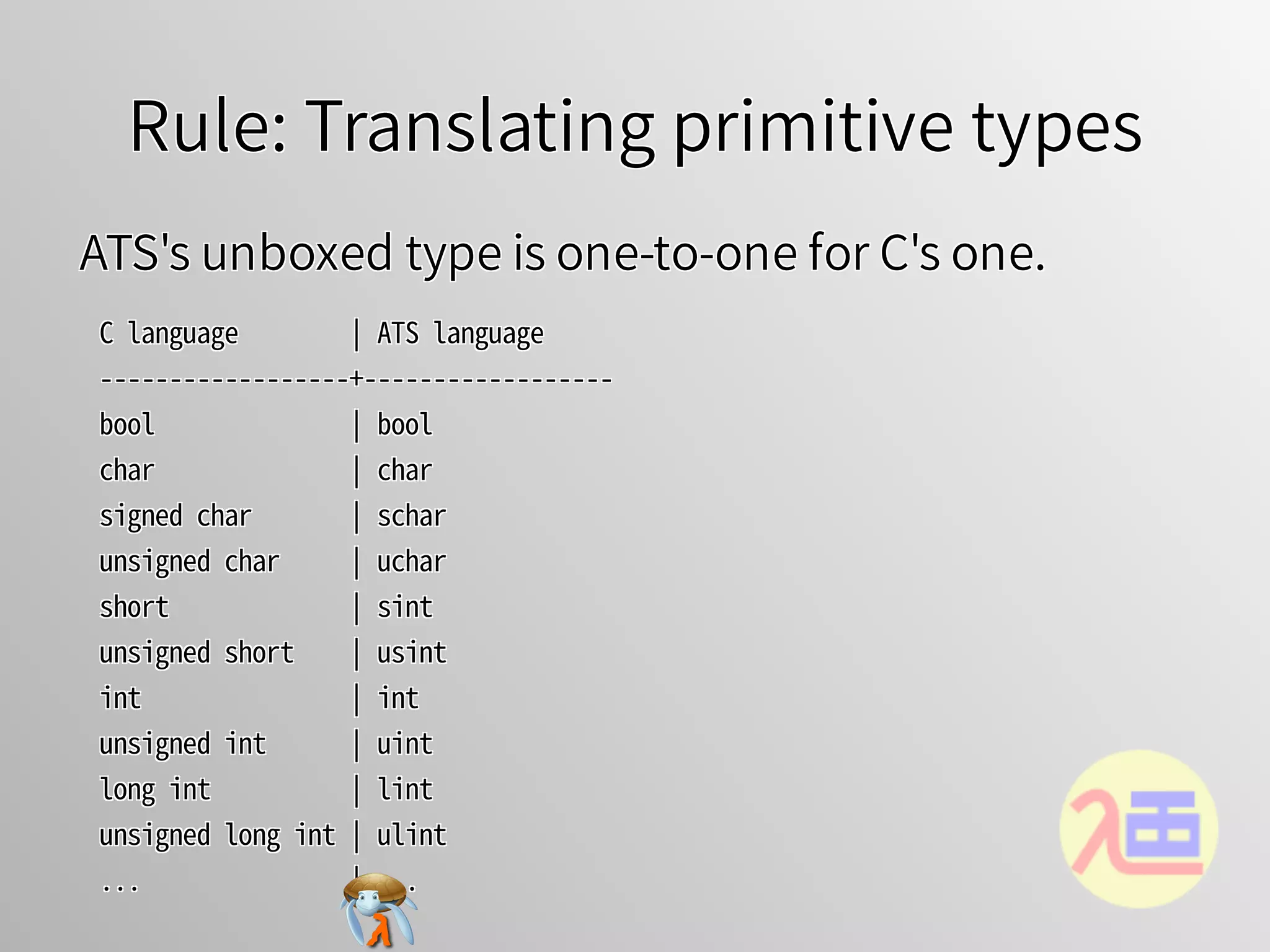
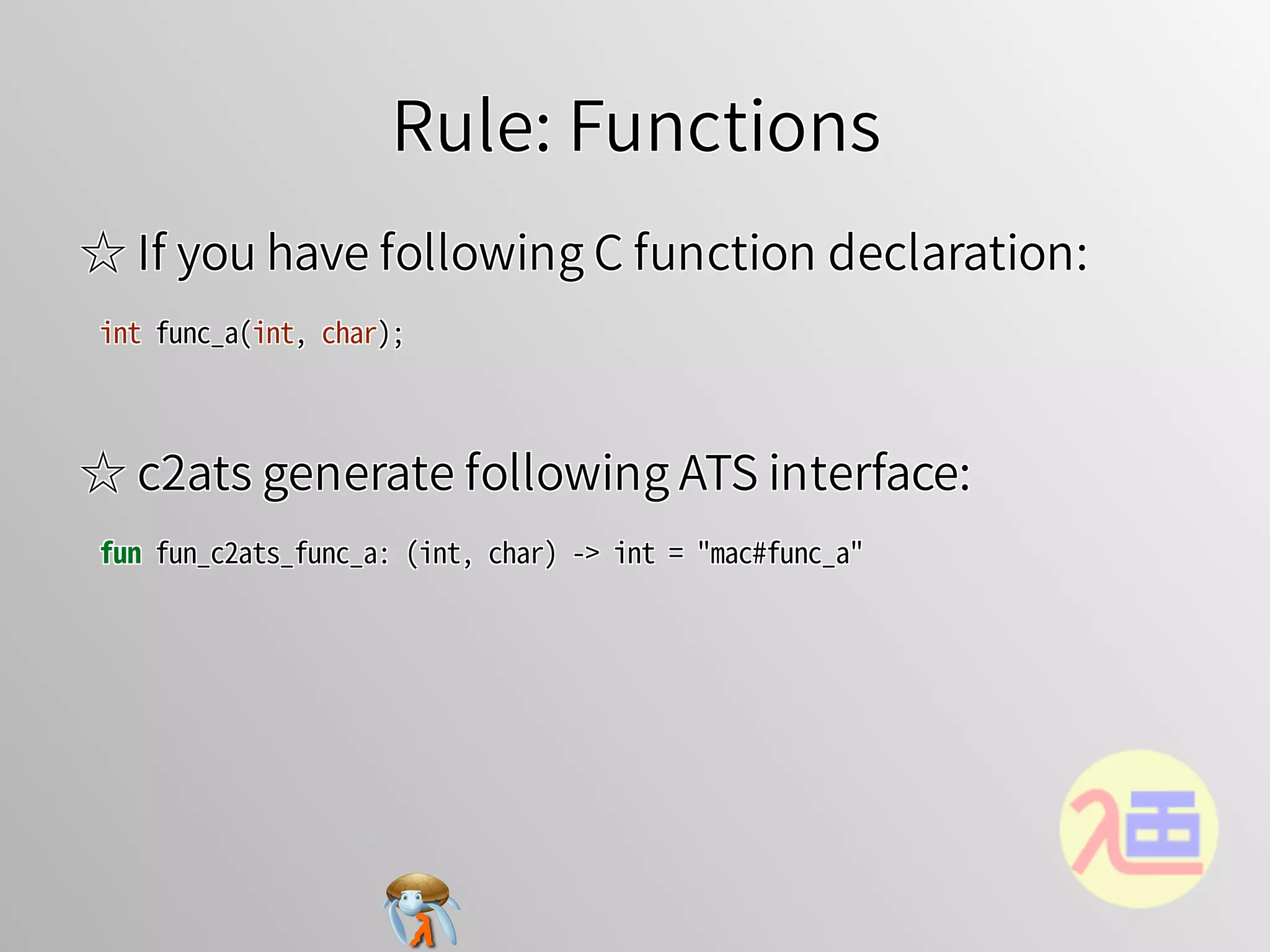
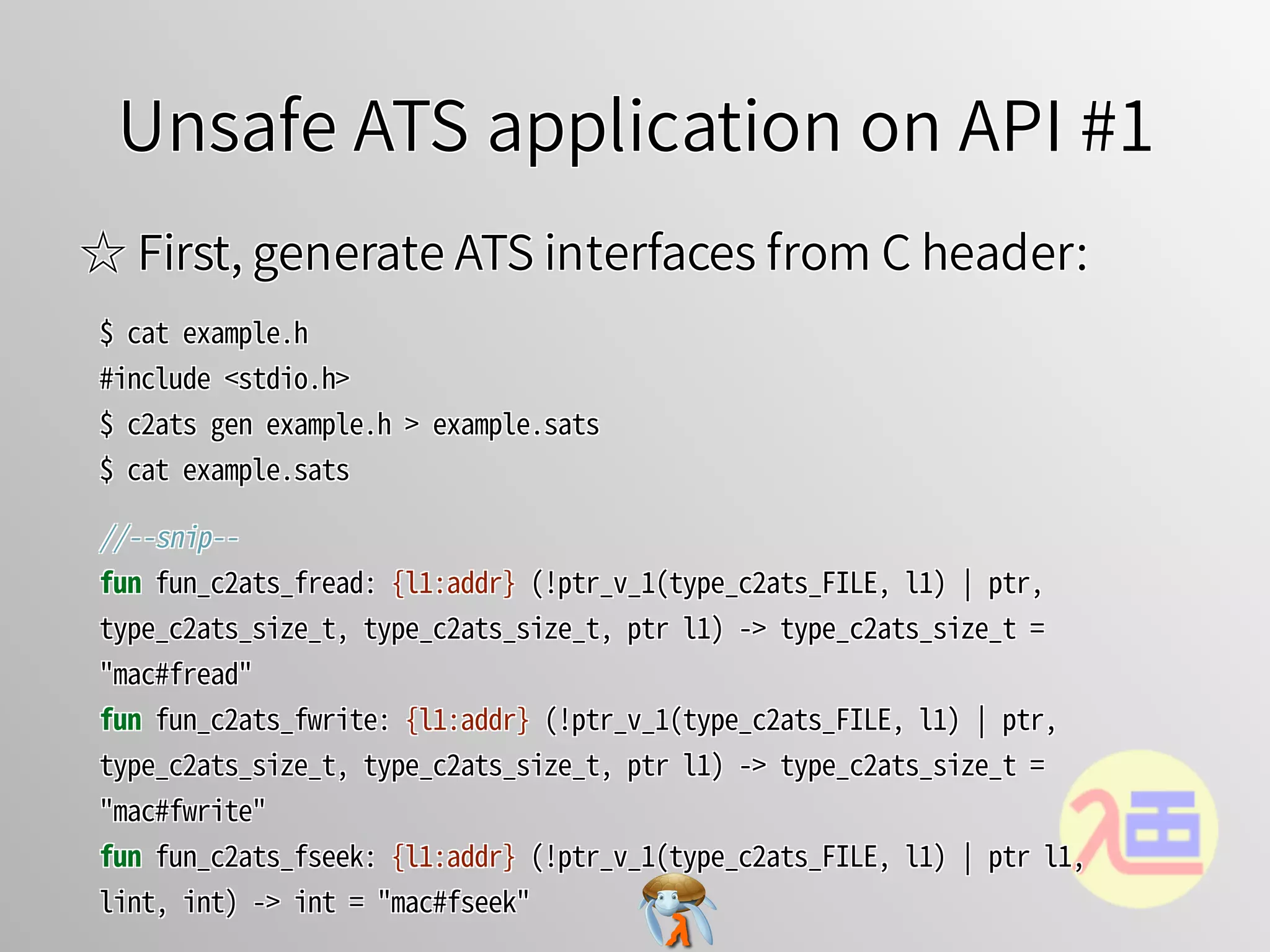
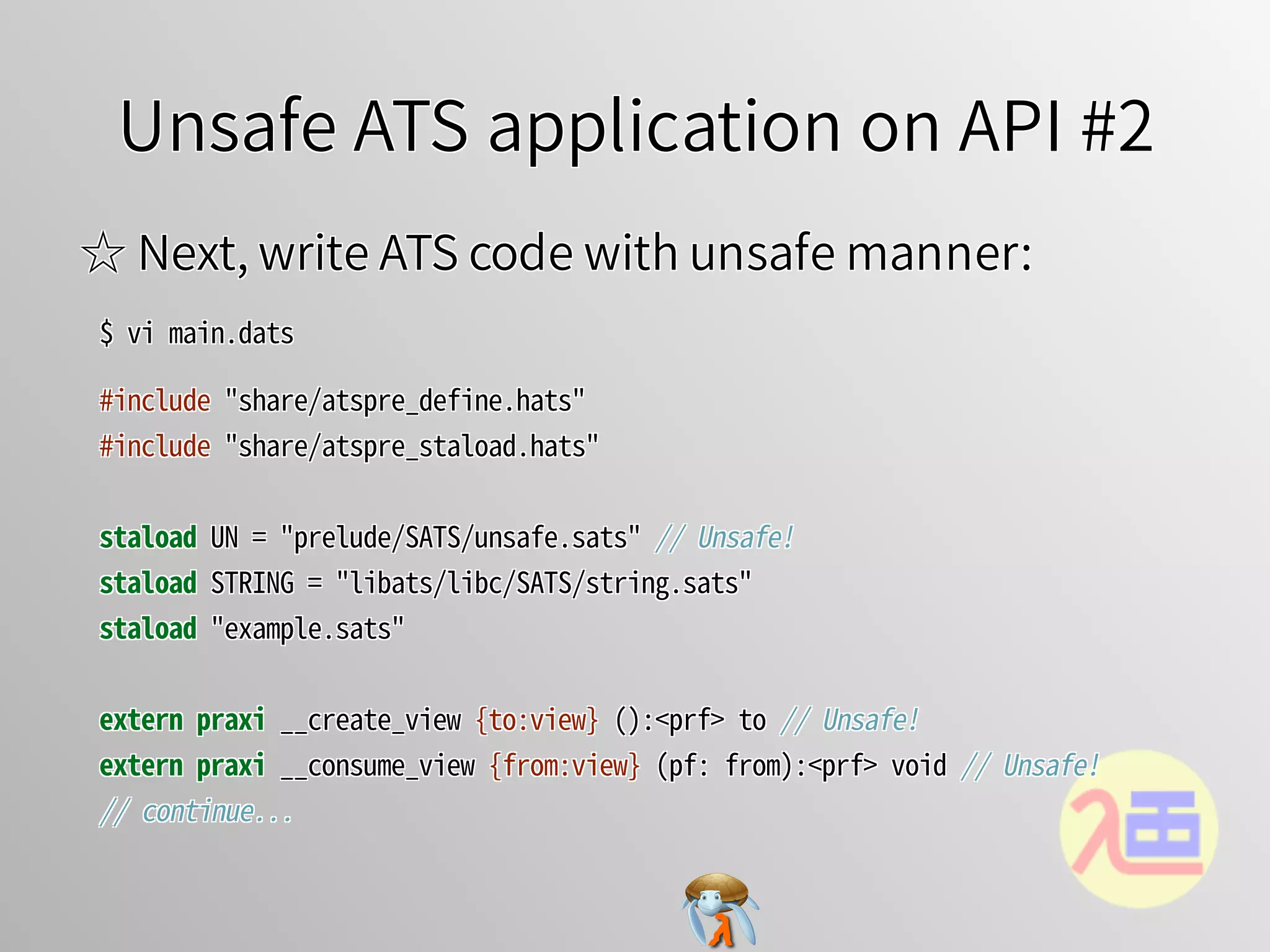
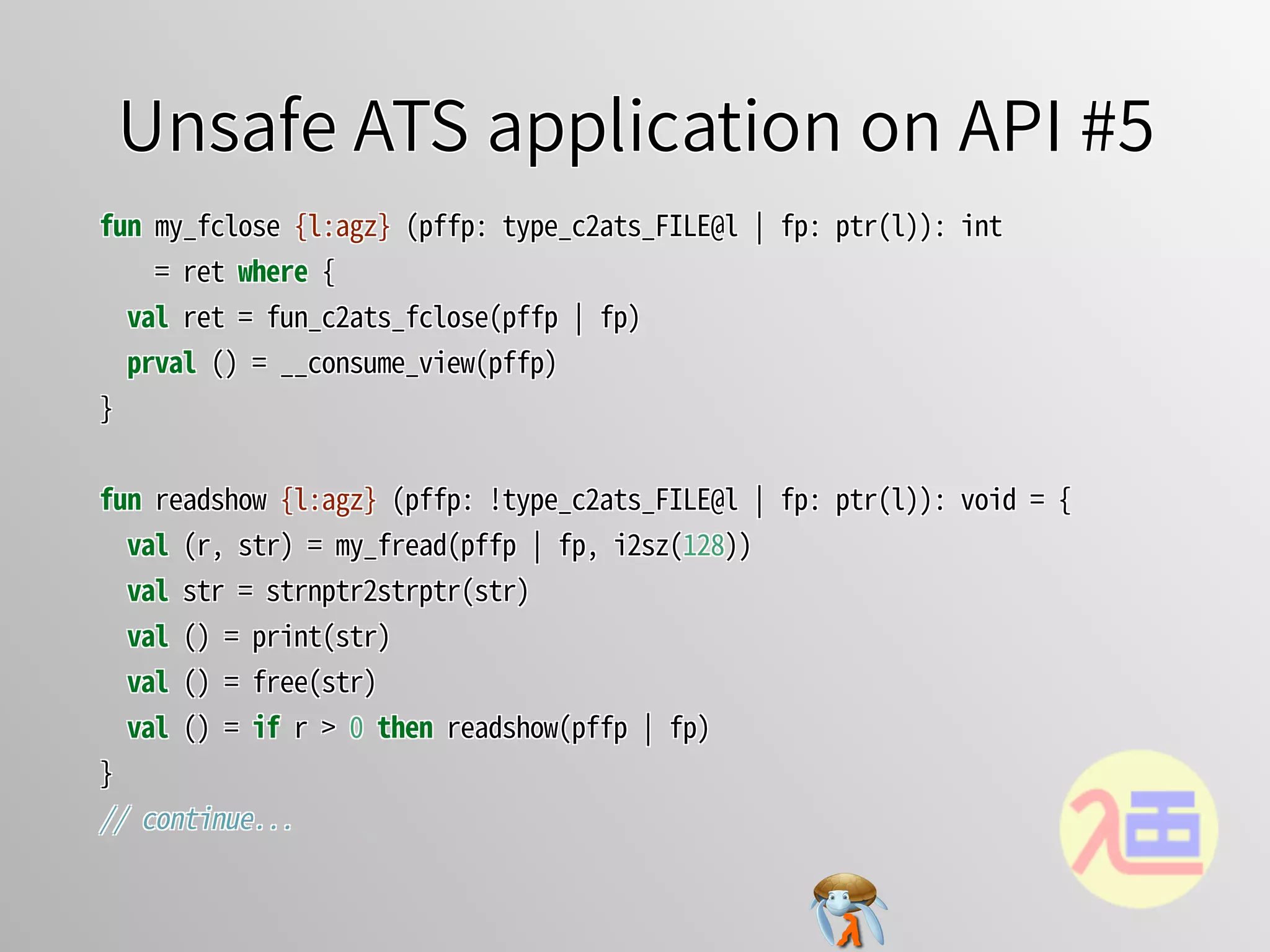
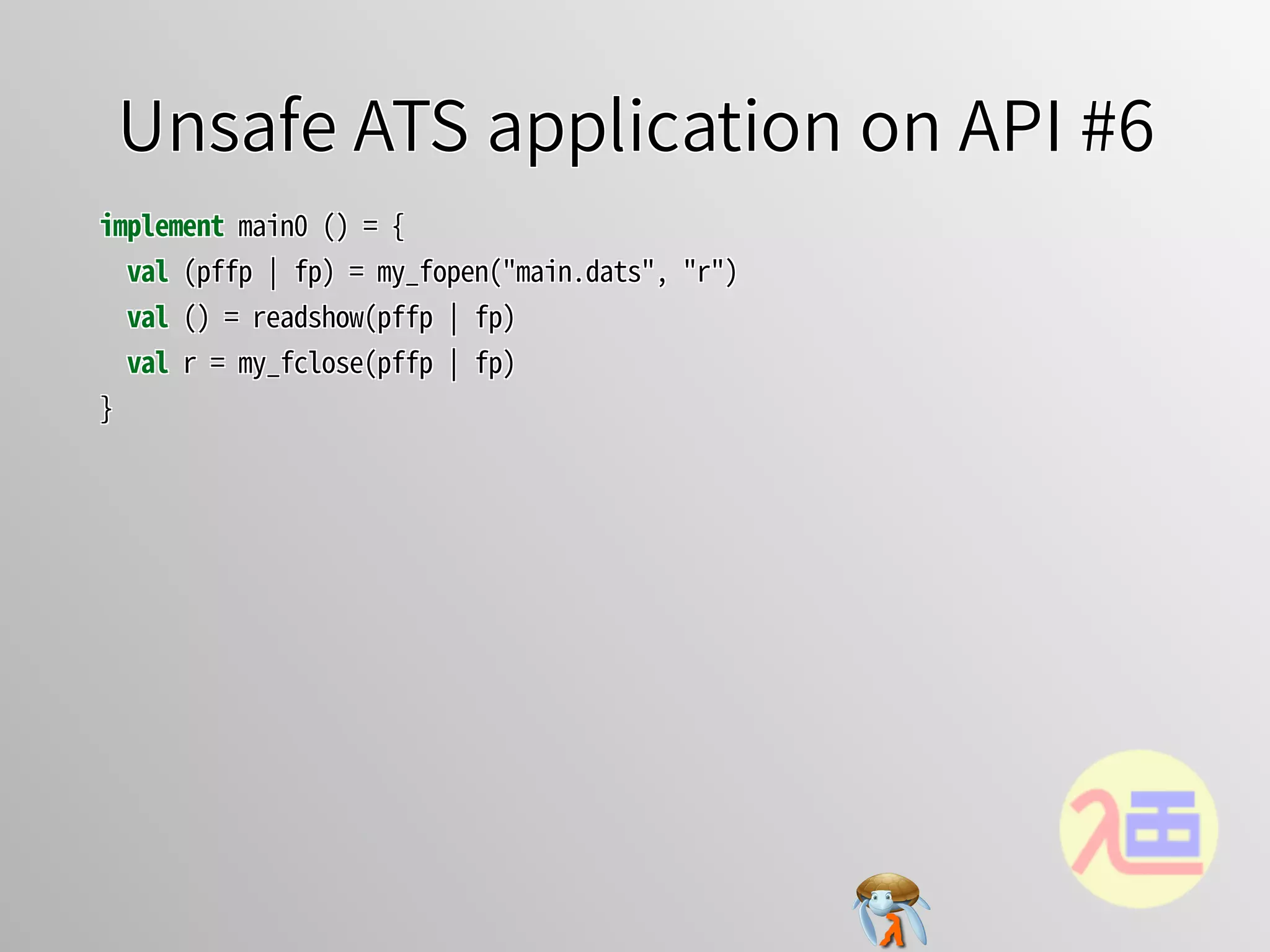
The document discusses using the ATS programming language for low-level programming as an alternative to C. It describes c2ats, a tool that can generate ATS interfaces from C code. This allows C libraries to be accessed from ATS. The document provides examples of how c2ats translates C primitive types, functions, structures, and pointers to equivalent ATS definitions. This allows existing C code to be integrated with ATS for improved type safety and compile-time error checking compared to C alone.
![Rule: Accessor for global variables #1Rule: Accessor for global variables #1Rule: Accessor for global variables #1Rule: Accessor for global variables #1Rule: Accessor for global variables #1
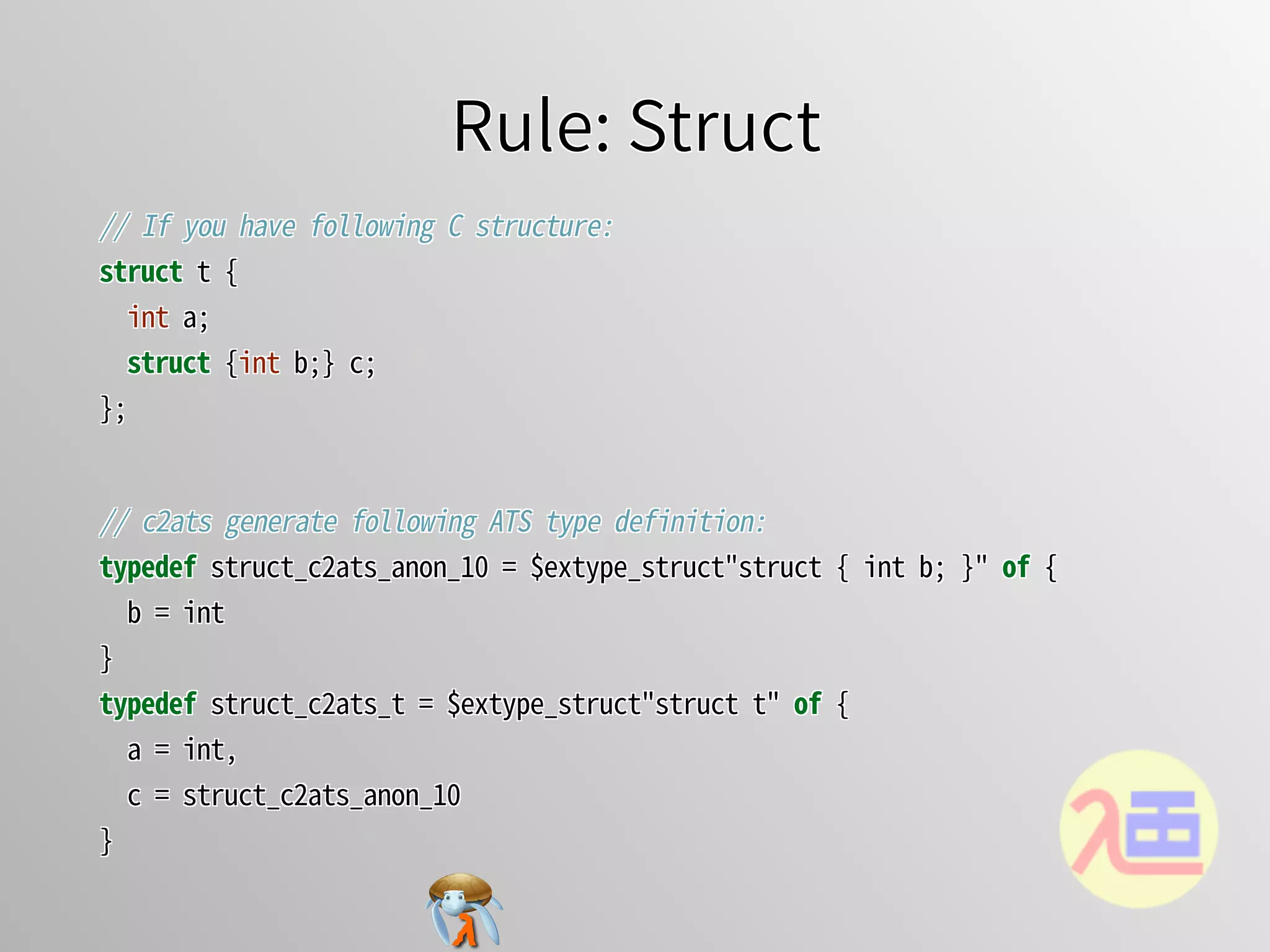
//�If�you�have�following�C�declaration:
struct�foo�{int�i;�char�*s;};
extern�struct�foo�g_foo;
//�If�you�have�following�C�declaration:
struct�foo�{int�i;�char�*s;};
extern�struct�foo�g_foo;
//�If�you�have�following�C�declaration:
struct�foo�{int�i;�char�*s;};
extern�struct�foo�g_foo;
//�If�you�have�following�C�declaration:
struct�foo�{int�i;�char�*s;};
extern�struct�foo�g_foo;
//�If�you�have�following�C�declaration:
struct�foo�{int�i;�char�*s;};
extern struct�foo�g_foo;
//�c2ats�generate�following�ATS�definition:
typedef�struct_c2ats_foo�=�$extype_struct"struct�foo"�of�{
��i�=�int,
��s�=�ptr�(*�cPtr0(char)�*)
}
macdef�takeout_c2ats_g_foo�=�$extval([l1:addr]�(ptr_v_1(struct_c2ats_foo,�
l1)�│�ptr�l1),�"&g_foo")
praxi�addback_c2ats_g_foo�{l1:addr}�(ptr_v_1(struct_c2ats_foo,�l1)�│�ptr�
l1):�void
//�c2ats�generate�following�ATS�definition:
typedef�struct_c2ats_foo�=�$extype_struct"struct�foo"�of�{
��i�=�int,
��s�=�ptr�(*�cPtr0(char)�*)
}
macdef�takeout_c2ats_g_foo�=�$extval([l1:addr]�(ptr_v_1(struct_c2ats_foo,�
l1)�│�ptr�l1),�"&g_foo")
praxi�addback_c2ats_g_foo�{l1:addr}�(ptr_v_1(struct_c2ats_foo,�l1)�│�ptr�
l1):�void
//�c2ats�generate�following�ATS�definition:
typedef�struct_c2ats_foo�=�$extype_struct"struct�foo"�of�{
��i�=�int,
��s�=�ptr�(*�cPtr0(char)�*)
}
macdef�takeout_c2ats_g_foo�=�$extval([l1:addr]�(ptr_v_1(struct_c2ats_foo,�
l1)�│�ptr�l1),�"&g_foo")
praxi�addback_c2ats_g_foo�{l1:addr}�(ptr_v_1(struct_c2ats_foo,�l1)�│�ptr�
l1):�void
//�c2ats�generate�following�ATS�definition:
typedef�struct_c2ats_foo�=�$extype_struct"struct�foo"�of�{
��i�=�int,
��s�=�ptr�(*�cPtr0(char)�*)
}
macdef�takeout_c2ats_g_foo�=�$extval([l1:addr]�(ptr_v_1(struct_c2ats_foo,�
l1)�│�ptr�l1),�"&g_foo")
praxi�addback_c2ats_g_foo�{l1:addr}�(ptr_v_1(struct_c2ats_foo,�l1)�│�ptr�
l1):�void
//�c2ats�generate�following�ATS�definition:
typedef�struct_c2ats_foo�=�$extype_struct"struct�foo"�of�{
��i�=�int,
��s�=�ptr�(*�cPtr0(char)�*)
}
macdef�takeout_c2ats_g_foo�=�$extval([l1:addr]�(ptr_v_1(struct_c2ats_foo,�
l1)�│�ptr�l1),�"&g_foo")
praxi�addback_c2ats_g_foo�{l1:addr}�(ptr_v_1(struct_c2ats_foo,�l1)�│�ptr�
l1):�void](https://image.slidesharecdn.com/20170308ppl2017c2ats-170309080325/75/Poster-Generate-ATS-interface-from-C-code-and-introduce-linear-type-13-2048.jpg)
![Unsafe ATS application on API #3Unsafe ATS application on API #3Unsafe ATS application on API #3Unsafe ATS application on API #3Unsafe ATS application on API #3
fun�my_fopen�(file:�string,�mode:�string):
����[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
��val�pn�=�string2ptr(file)
��val�(pfnat,�fpfnat�│�pn)�=�$UN.ptr_vtake(pn)�//�Unsafe!
��val�pm�=�string2ptr(mode)
��val�(pfmat,�fpfmat�│�pm)�=�$UN.ptr_vtake(pm)�//�Unsafe!
��val�(pffp�│�fp)�=�fun_c2ats_fopen(pfnat,�pfmat�│�pn,�pm)
��prval�()�=�fpfnat(pfnat)
��prval�()�=�fpfmat(pfmat)
��val�()�=�assertloc(fp�>�0)
��val�ret�=�(pffp�│�fp)
}
//�continue...
fun�my_fopen�(file:�string,�mode:�string):
����[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
��val�pn�=�string2ptr(file)
��val�(pfnat,�fpfnat�│�pn)�=�$UN.ptr_vtake(pn)�//�Unsafe!
��val�pm�=�string2ptr(mode)
��val�(pfmat,�fpfmat�│�pm)�=�$UN.ptr_vtake(pm)�//�Unsafe!
��val�(pffp�│�fp)�=�fun_c2ats_fopen(pfnat,�pfmat�│�pn,�pm)
��prval�()�=�fpfnat(pfnat)
��prval�()�=�fpfmat(pfmat)
��val�()�=�assertloc(fp�>�0)
��val�ret�=�(pffp�│�fp)
}
//�continue...
fun�my_fopen�(file:�string,�mode:�string):
����[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
��val�pn�=�string2ptr(file)
��val�(pfnat,�fpfnat�│�pn)�=�$UN.ptr_vtake(pn)�//�Unsafe!
��val�pm�=�string2ptr(mode)
��val�(pfmat,�fpfmat�│�pm)�=�$UN.ptr_vtake(pm)�//�Unsafe!
��val�(pffp�│�fp)�=�fun_c2ats_fopen(pfnat,�pfmat�│�pn,�pm)
��prval�()�=�fpfnat(pfnat)
��prval�()�=�fpfmat(pfmat)
��val�()�=�assertloc(fp�>�0)
��val�ret�=�(pffp�│�fp)
}
//�continue...
fun�my_fopen�(file:�string,�mode:�string):
����[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
��val�pn�=�string2ptr(file)
��val�(pfnat,�fpfnat�│�pn)�=�$UN.ptr_vtake(pn)�//�Unsafe!
��val�pm�=�string2ptr(mode)
��val�(pfmat,�fpfmat�│�pm)�=�$UN.ptr_vtake(pm)�//�Unsafe!
��val�(pffp�│�fp)�=�fun_c2ats_fopen(pfnat,�pfmat�│�pn,�pm)
��prval�()�=�fpfnat(pfnat)
��prval�()�=�fpfmat(pfmat)
��val�()�=�assertloc(fp�>�0)
��val�ret�=�(pffp�│�fp)
}
//�continue...
fun�my_fopen�(file:�string,�mode:�string):
[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
val�pn�=�string2ptr(file)
val�(pfnat,�fpfnat�│�pn)�=�$UN.ptr_vtake(pn)�//�Unsafe!
val�pm�=�string2ptr(mode)
val�(pfmat,�fpfmat�│�pm)�=�$UN.ptr_vtake(pm)�//�Unsafe!
val�(pffp�│�fp)�=�fun_c2ats_fopen(pfnat,�pfmat�│�pn,�pm)
prval�()�=�fpfnat(pfnat)
prval�()�=�fpfmat(pfmat)
val�()�=�assertloc(fp�>�0)
val�ret�=�(pffp�│�fp)
}
//�continue...](https://image.slidesharecdn.com/20170308ppl2017c2ats-170309080325/75/Poster-Generate-ATS-interface-from-C-code-and-introduce-linear-type-17-2048.jpg)
![Unsafe ATS application on API #4Unsafe ATS application on API #4Unsafe ATS application on API #4Unsafe ATS application on API #4Unsafe ATS application on API #4
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
����[m:int]�(size_t(m),�strnptr(m))�=�ret�where�{
��implement{}�string_tabulate$fopr(s)�=�'_'
��val�buf_strptr�=�strnptr2strptr(string_tabulate(len))
��val�buf_ptr�=�strptr2ptr(buf_strptr)
��val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
��val�r�=�fun_c2ats_fread(pffp�│�buf_ptr,�1UL,�$UN.cast2ulint(len),�fp)�//�
Unsafe!
��val�r�=�$UN.cast(r)�//�Unsafe!
��val�buf_strnptr�=�strptr2strnptr(buf_strptr)
��val�ret�=�(r,�buf_strnptr)
}
//�continue...
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
����[m:int]�(size_t(m),�strnptr(m))�=�ret�where�{
��implement{}�string_tabulate$fopr(s)�=�'_'
��val�buf_strptr�=�strnptr2strptr(string_tabulate(len))
��val�buf_ptr�=�strptr2ptr(buf_strptr)
��val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
��val�r�=�fun_c2ats_fread(pffp�│�buf_ptr,�1UL,�$UN.cast2ulint(len),�fp)�//�
Unsafe!
��val�r�=�$UN.cast(r)�//�Unsafe!
��val�buf_strnptr�=�strptr2strnptr(buf_strptr)
��val�ret�=�(r,�buf_strnptr)
}
//�continue...
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
����[m:int]�(size_t(m),�strnptr(m))�=�ret�where�{
��implement{}�string_tabulate$fopr(s)�=�'_'
��val�buf_strptr�=�strnptr2strptr(string_tabulate(len))
��val�buf_ptr�=�strptr2ptr(buf_strptr)
��val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
��val�r�=�fun_c2ats_fread(pffp�│�buf_ptr,�1UL,�$UN.cast2ulint(len),�fp)�//�
Unsafe!
��val�r�=�$UN.cast(r)�//�Unsafe!
��val�buf_strnptr�=�strptr2strnptr(buf_strptr)
��val�ret�=�(r,�buf_strnptr)
}
//�continue...
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
����[m:int]�(size_t(m),�strnptr(m))�=�ret�where�{
��implement{}�string_tabulate$fopr(s)�=�'_'
��val�buf_strptr�=�strnptr2strptr(string_tabulate(len))
��val�buf_ptr�=�strptr2ptr(buf_strptr)
��val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
��val�r�=�fun_c2ats_fread(pffp�│�buf_ptr,�1UL,�$UN.cast2ulint(len),�fp)�//�
Unsafe!
��val�r�=�$UN.cast(r)�//�Unsafe!
��val�buf_strnptr�=�strptr2strnptr(buf_strptr)
��val�ret�=�(r,�buf_strnptr)
}
//�continue...
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
[m:int]�(size_t(m),�strnptr(m))�=�ret�where�{
implement{}�string_tabulate$fopr(s)�=�'_'
val�buf_strptr�=�strnptr2strptr(string_tabulate(len))
val�buf_ptr�=�strptr2ptr(buf_strptr)
val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
val�r�=�fun_c2ats_fread(pffp�│�buf_ptr,�1UL,�$UN.cast2ulint(len),�fp)�//�
Unsafe!
val�r�=�$UN.cast(r)�//�Unsafe!
val�buf_strnptr�=�strptr2strnptr(buf_strptr)
val�ret�=�(r,�buf_strnptr)
}
//�continue...](https://image.slidesharecdn.com/20170308ppl2017c2ats-170309080325/75/Poster-Generate-ATS-interface-from-C-code-and-introduce-linear-type-18-2048.jpg)
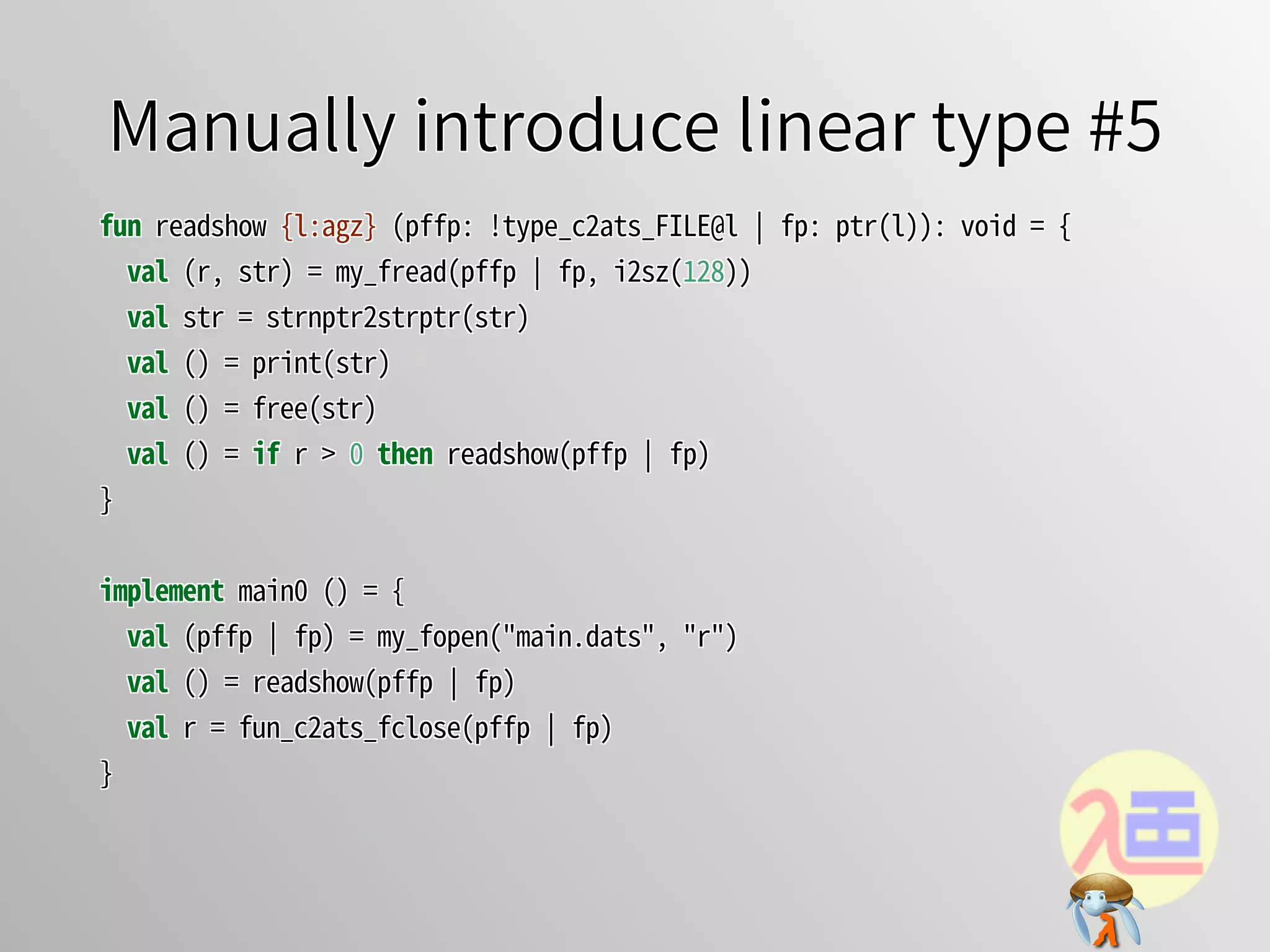
![Manually introduce linear type #1Manually introduce linear type #1Manually introduce linear type #1Manually introduce linear type #1Manually introduce linear type #1
☆ Generated ATS interfaces are:☆ Generated ATS interfaces are:☆ Generated ATS interfaces are:☆ Generated ATS interfaces are:☆ Generated ATS interfaces are:
$�cat�example.h
#include�<stdio.h>
$�c2ats�gen�example.h�>�example.sats
$�cat�example.sats
$�cat�example.h
#include�<stdio.h>
$�c2ats�gen�example.h�>�example.sats
$�cat�example.sats
$�cat�example.h
#include�<stdio.h>
$�c2ats�gen�example.h�>�example.sats
$�cat�example.sats
$�cat�example.h
#include�<stdio.h>
$�c2ats�gen�example.h�>�example.sats
$�cat�example.sats
$�cat�example.h
#include�<stdio.h>
$�c2ats�gen�example.h�>�example.sats
$�cat�example.sats
//�--snip--
fun�fun_c2ats_fclose:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�{l1,l2:addr}�(!ptr_v_1(char,�l1),�!ptr_v_1(char,�l2)�│�
ptr�l1,�ptr�l2)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�l3)�│�ptr�l3)�=�
"mac#fopen"
fun�fun_c2ats_fread:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr,�
type_c2ats_size_t,�type_c2ats_size_t,�ptr�l1)�->�type_c2ats_size_t�=�
"mac#fread"
//�--snip--
fun�fun_c2ats_fclose:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�{l1,l2:addr}�(!ptr_v_1(char,�l1),�!ptr_v_1(char,�l2)�│�
ptr�l1,�ptr�l2)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�l3)�│�ptr�l3)�=�
"mac#fopen"
fun�fun_c2ats_fread:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr,�
type_c2ats_size_t,�type_c2ats_size_t,�ptr�l1)�->�type_c2ats_size_t�=�
"mac#fread"
//�--snip--
fun�fun_c2ats_fclose:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�{l1,l2:addr}�(!ptr_v_1(char,�l1),�!ptr_v_1(char,�l2)�│�
ptr�l1,�ptr�l2)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�l3)�│�ptr�l3)�=�
"mac#fopen"
fun�fun_c2ats_fread:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr,�
type_c2ats_size_t,�type_c2ats_size_t,�ptr�l1)�->�type_c2ats_size_t�=�
"mac#fread"
//�--snip--
fun�fun_c2ats_fclose:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�{l1,l2:addr}�(!ptr_v_1(char,�l1),�!ptr_v_1(char,�l2)�│�
ptr�l1,�ptr�l2)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�l3)�│�ptr�l3)�=�
"mac#fopen"
fun�fun_c2ats_fread:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr,�
type_c2ats_size_t,�type_c2ats_size_t,�ptr�l1)�->�type_c2ats_size_t�=�
"mac#fread"
//�--snip--
fun�fun_c2ats_fclose:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�{l1,l2:addr}�(!ptr_v_1(char,�l1),�!ptr_v_1(char,�l2)�│�
ptr�l1,�ptr�l2)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�l3)�│�ptr�l3)�=�
"mac#fopen"
fun�fun_c2ats_fread:�{l1:addr}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�ptr,�
type_c2ats_size_t,�type_c2ats_size_t,�ptr�l1)�->�type_c2ats_size_t�=�
"mac#fread"](https://image.slidesharecdn.com/20170308ppl2017c2ats-170309080325/75/Poster-Generate-ATS-interface-from-C-code-and-introduce-linear-type-21-2048.jpg)
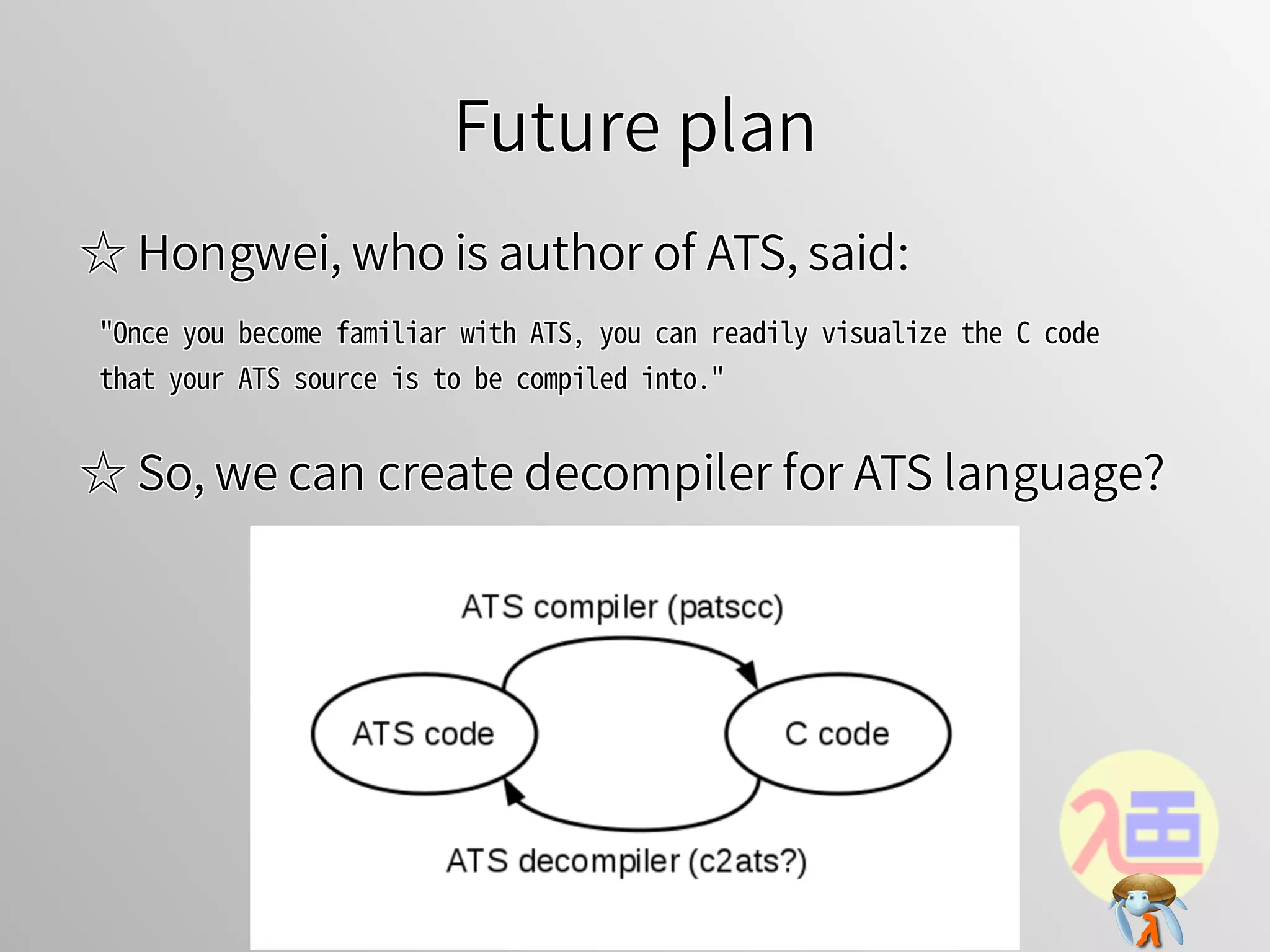
![Manually introduce linear type #2Manually introduce linear type #2Manually introduce linear type #2Manually introduce linear type #2Manually introduce linear type #2
☆ If you modify the interfaces with safe manner:☆ If you modify the interfaces with safe manner:☆ If you modify the interfaces with safe manner:☆ If you modify the interfaces with safe manner:☆ If you modify the interfaces with safe manner:
$�cp�example.sats�example_welltyped.sats
$�vi�example_welltyped.sats
$�cp�example.sats�example_welltyped.sats
$�vi�example_welltyped.sats
$�cp�example.sats�example_welltyped.sats
$�vi�example_welltyped.sats
$�cp�example.sats�example_welltyped.sats
$�vi�example_welltyped.sats
$�cp�example.sats�example_welltyped.sats
$�vi�example_welltyped.sats
//�--snip--
fun�fun_c2ats_fclose:�{l1:agz}�(ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�(string,�string)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�
l3)�│�ptr�l3)�=�"mac#fopen"
fun�fun_c2ats_fread:�{l1:agz}{n,m:nat}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�!
strnptr(n*m)>>strnptr(o),�size_t(n),�size_t(m),�ptr�l1)�->�#[o:nat�│�o�<=�
n*m]�size_t(o)�=�"mac#fread"
//�--snip--
fun�fun_c2ats_fclose:�{l1:agz}�(ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�(string,�string)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�
l3)�│�ptr�l3)�=�"mac#fopen"
fun�fun_c2ats_fread:�{l1:agz}{n,m:nat}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�!
strnptr(n*m)>>strnptr(o),�size_t(n),�size_t(m),�ptr�l1)�->�#[o:nat�│�o�<=�
n*m]�size_t(o)�=�"mac#fread"
//�--snip--
fun�fun_c2ats_fclose:�{l1:agz}�(ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�(string,�string)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�
l3)�│�ptr�l3)�=�"mac#fopen"
fun�fun_c2ats_fread:�{l1:agz}{n,m:nat}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�!
strnptr(n*m)>>strnptr(o),�size_t(n),�size_t(m),�ptr�l1)�->�#[o:nat�│�o�<=�
n*m]�size_t(o)�=�"mac#fread"
//�--snip--
fun�fun_c2ats_fclose:�{l1:agz}�(ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�(string,�string)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�
l3)�│�ptr�l3)�=�"mac#fopen"
fun�fun_c2ats_fread:�{l1:agz}{n,m:nat}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�!
strnptr(n*m)>>strnptr(o),�size_t(n),�size_t(m),�ptr�l1)�->�#[o:nat�│�o�<=�
n*m]�size_t(o)�=�"mac#fread"
//�--snip--
fun�fun_c2ats_fclose:�{l1:agz}�(ptr_v_1(type_c2ats_FILE,�l1)�│�ptr�l1)�->�
int�=�"mac#fclose"
fun�fun_c2ats_fopen:�(string,�string)�->�[l3:addr]�(ptr_v_1(type_c2ats_FILE,�
l3)�│�ptr�l3)�=�"mac#fopen"
fun�fun_c2ats_fread:�{l1:agz}{n,m:nat}�(!ptr_v_1(type_c2ats_FILE,�l1)�│�!
strnptr(n*m)>>strnptr(o),�size_t(n),�size_t(m),�ptr�l1)�->�#[o:nat�│�o�<=�
n*m]�size_t(o)�=�"mac#fread"](https://image.slidesharecdn.com/20170308ppl2017c2ats-170309080325/75/Poster-Generate-ATS-interface-from-C-code-and-introduce-linear-type-22-2048.jpg)
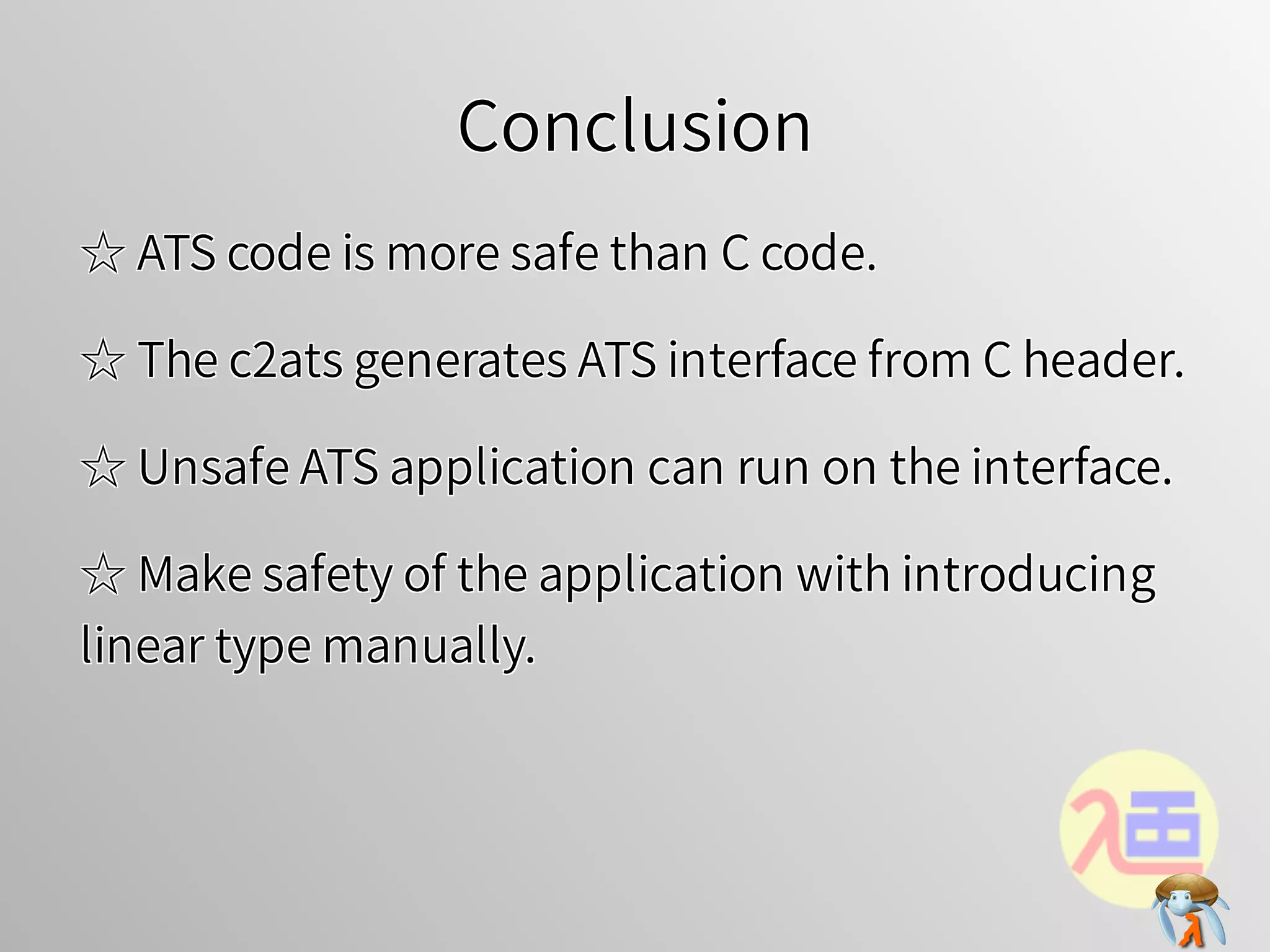
![Manually introduce linear type #3Manually introduce linear type #3Manually introduce linear type #3Manually introduce linear type #3Manually introduce linear type #3
☆ you can rite safe application:☆ you can rite safe application:☆ you can rite safe application:☆ you can rite safe application:☆ you can rite safe application:
$�vi�main.dats$�vi�main.dats$�vi�main.dats$�vi�main.dats$�vi�main.dats
#include�"share/atspre_define.hats"
#include�"share/atspre_staload.hats"
staload�STRING�=�"libats/libc/SATS/string.sats"
staload�"example_welltyped.sats"
fun�my_fopen�(file:�string,�mode:�string):
����[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
��val�(pffp�│�fp)�=�fun_c2ats_fopen(file,�mode)
��val�()�=�assertloc(fp�>�0)
��val�ret�=�(pffp�│�fp)
}
//�continue...
#include�"share/atspre_define.hats"
#include�"share/atspre_staload.hats"
staload�STRING�=�"libats/libc/SATS/string.sats"
staload�"example_welltyped.sats"
fun�my_fopen�(file:�string,�mode:�string):
����[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
��val�(pffp�│�fp)�=�fun_c2ats_fopen(file,�mode)
��val�()�=�assertloc(fp�>�0)
��val�ret�=�(pffp�│�fp)
}
//�continue...
#include�"share/atspre_define.hats"
#include�"share/atspre_staload.hats"
staload�STRING�=�"libats/libc/SATS/string.sats"
staload�"example_welltyped.sats"
fun�my_fopen�(file:�string,�mode:�string):
����[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
��val�(pffp�│�fp)�=�fun_c2ats_fopen(file,�mode)
��val�()�=�assertloc(fp�>�0)
��val�ret�=�(pffp�│�fp)
}
//�continue...
#include�"share/atspre_define.hats"
#include�"share/atspre_staload.hats"
staload�STRING�=�"libats/libc/SATS/string.sats"
staload�"example_welltyped.sats"
fun�my_fopen�(file:�string,�mode:�string):
����[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
��val�(pffp�│�fp)�=�fun_c2ats_fopen(file,�mode)
��val�()�=�assertloc(fp�>�0)
��val�ret�=�(pffp�│�fp)
}
//�continue...
#include�"share/atspre_define.hats"
#include�"share/atspre_staload.hats"
staload�STRING�=�"libats/libc/SATS/string.sats"
staload�"example_welltyped.sats"
fun�my_fopen�(file:�string,�mode:�string):
[l:agz]�(type_c2ats_FILE@l�│�ptr(l))�=�ret�where�{
val�(pffp�│�fp)�=�fun_c2ats_fopen(file,�mode)
val�()�=�assertloc(fp�>�0)
val�ret�=�(pffp�│�fp)
}
//�continue...](https://image.slidesharecdn.com/20170308ppl2017c2ats-170309080325/75/Poster-Generate-ATS-interface-from-C-code-and-introduce-linear-type-23-2048.jpg)
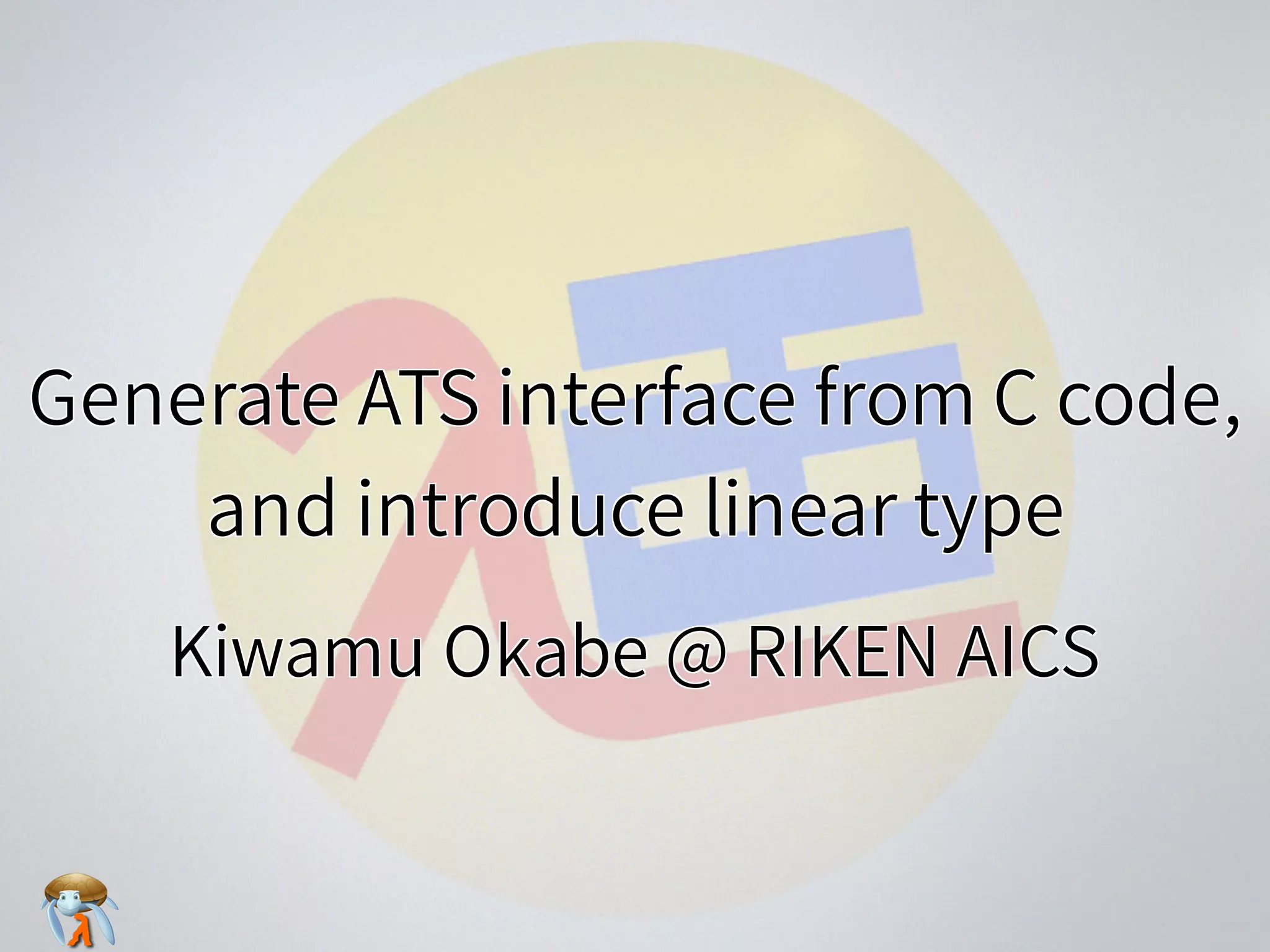
![Manually introduce linear type #4Manually introduce linear type #4Manually introduce linear type #4Manually introduce linear type #4Manually introduce linear type #4
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
����[m:nat�│�m�<=�n]�(size_t(m),�strnptr(m))�=�ret�where�{
��implement{}�string_tabulate$fopr(s)�=�'_'
��val�buf_strnptr�=�string_tabulate(len)
��val�buf_ptr�=�strnptr2ptr(buf_strnptr)
��val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
��val�r�=�fun_c2ats_fread(pffp�│�buf_strnptr,�i2sz(1),�len,�fp)
��val�ret�=�(r,�buf_strnptr)
}
//�continue...
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
����[m:nat�│�m�<=�n]�(size_t(m),�strnptr(m))�=�ret�where�{
��implement{}�string_tabulate$fopr(s)�=�'_'
��val�buf_strnptr�=�string_tabulate(len)
��val�buf_ptr�=�strnptr2ptr(buf_strnptr)
��val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
��val�r�=�fun_c2ats_fread(pffp�│�buf_strnptr,�i2sz(1),�len,�fp)
��val�ret�=�(r,�buf_strnptr)
}
//�continue...
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
����[m:nat�│�m�<=�n]�(size_t(m),�strnptr(m))�=�ret�where�{
��implement{}�string_tabulate$fopr(s)�=�'_'
��val�buf_strnptr�=�string_tabulate(len)
��val�buf_ptr�=�strnptr2ptr(buf_strnptr)
��val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
��val�r�=�fun_c2ats_fread(pffp�│�buf_strnptr,�i2sz(1),�len,�fp)
��val�ret�=�(r,�buf_strnptr)
}
//�continue...
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
����[m:nat�│�m�<=�n]�(size_t(m),�strnptr(m))�=�ret�where�{
��implement{}�string_tabulate$fopr(s)�=�'_'
��val�buf_strnptr�=�string_tabulate(len)
��val�buf_ptr�=�strnptr2ptr(buf_strnptr)
��val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
��val�r�=�fun_c2ats_fread(pffp�│�buf_strnptr,�i2sz(1),�len,�fp)
��val�ret�=�(r,�buf_strnptr)
}
//�continue...
fun�my_fread�{l:agz}{n:nat}
����(pffp:�!type_c2ats_FILE@l�│�fp:�ptr(l),�len:�size_t(n)):
[m:nat�│�m�<=�n]�(size_t(m),�strnptr(m))�=�ret�where�{
implement{}�string_tabulate$fopr(s)�=�'_'
val�buf_strnptr�=�string_tabulate(len)
val�buf_ptr�=�strnptr2ptr(buf_strnptr)
val�_�=�$STRING.memset_unsafe(buf_ptr,�0,�len)
val�r�=�fun_c2ats_fread(pffp�│�buf_strnptr,�i2sz(1),�len,�fp)
val�ret�=�(r,�buf_strnptr)
}
//�continue...](https://image.slidesharecdn.com/20170308ppl2017c2ats-170309080325/75/Poster-Generate-ATS-interface-from-C-code-and-introduce-linear-type-24-2048.jpg)