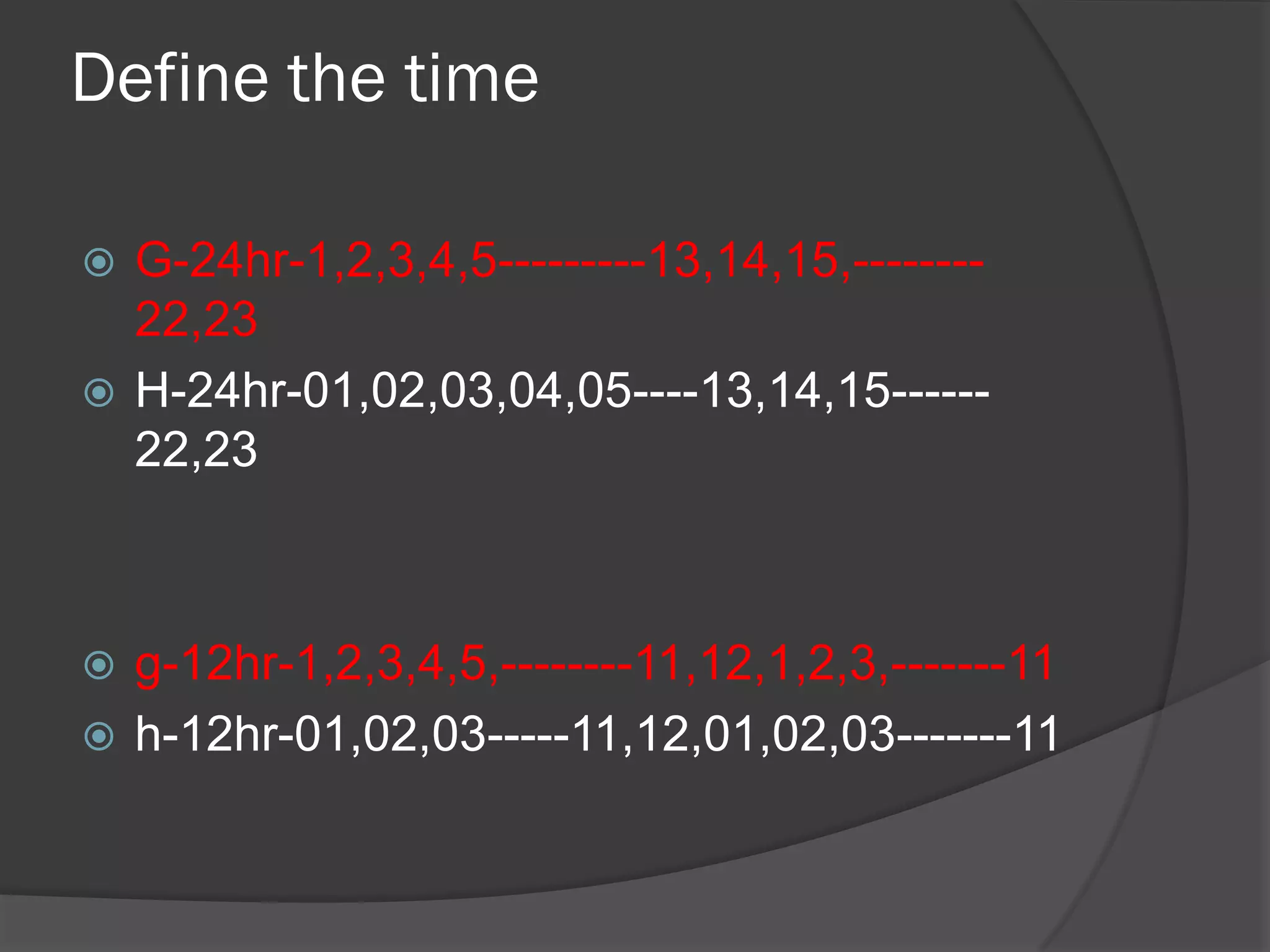
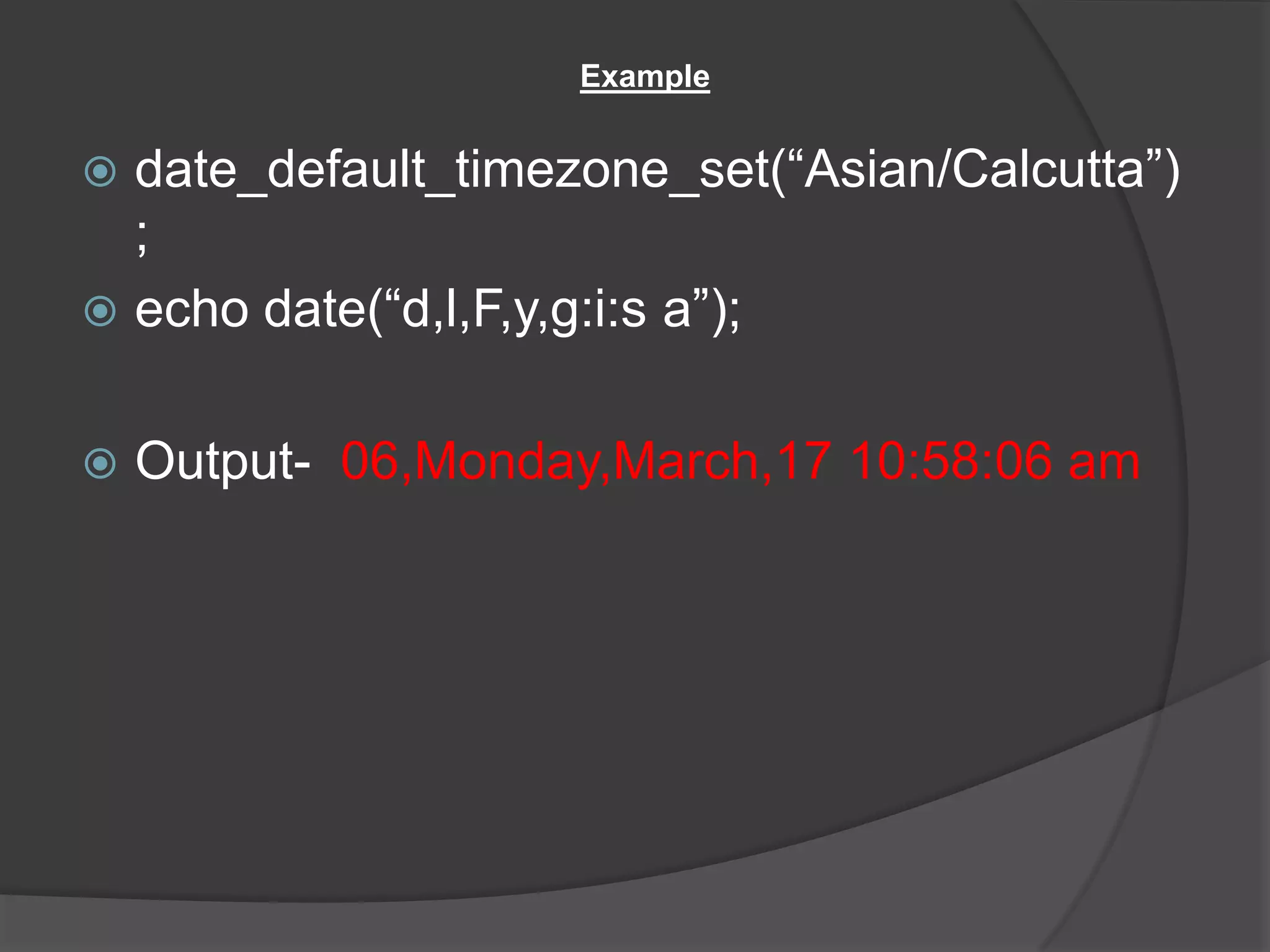
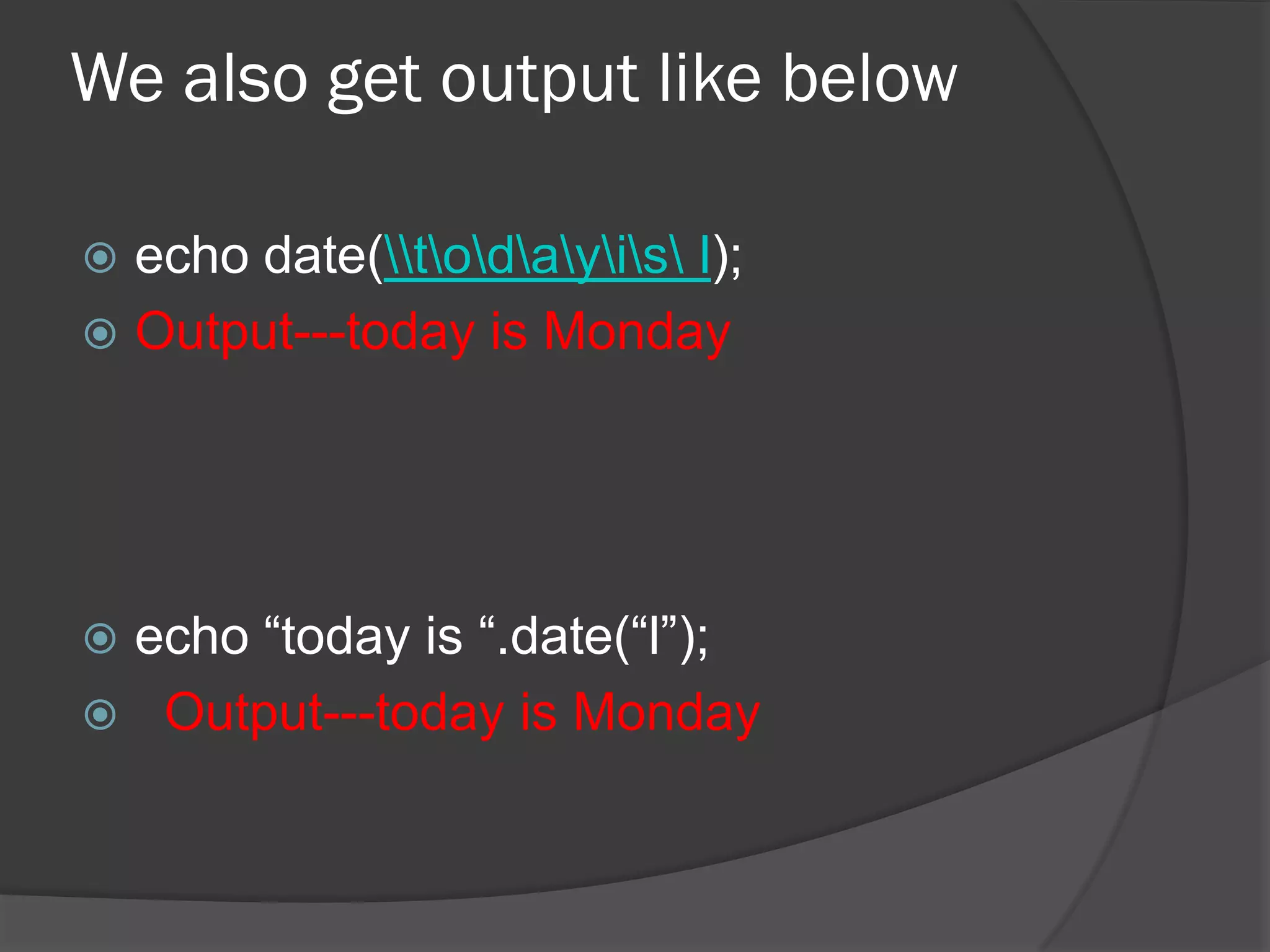
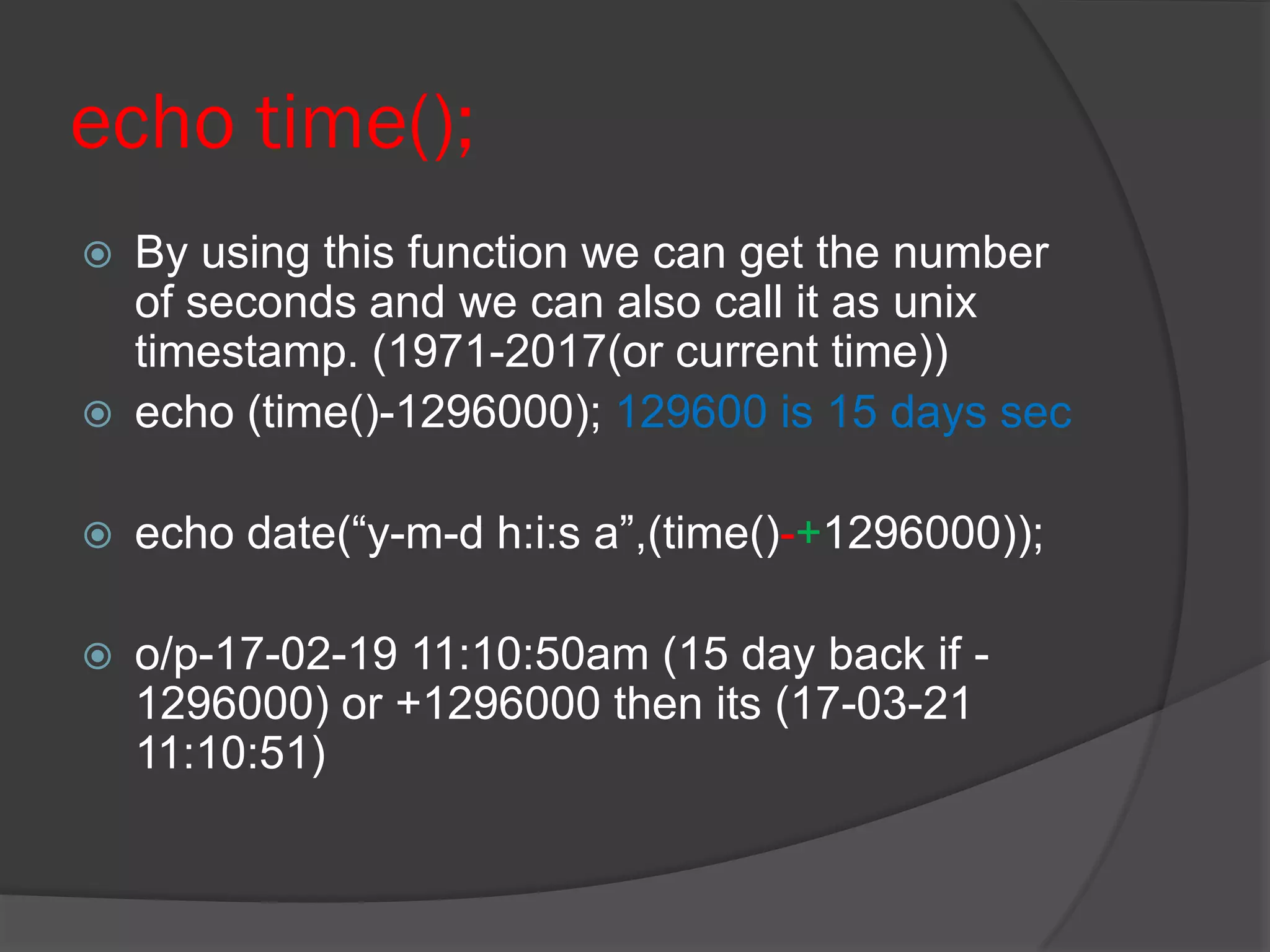
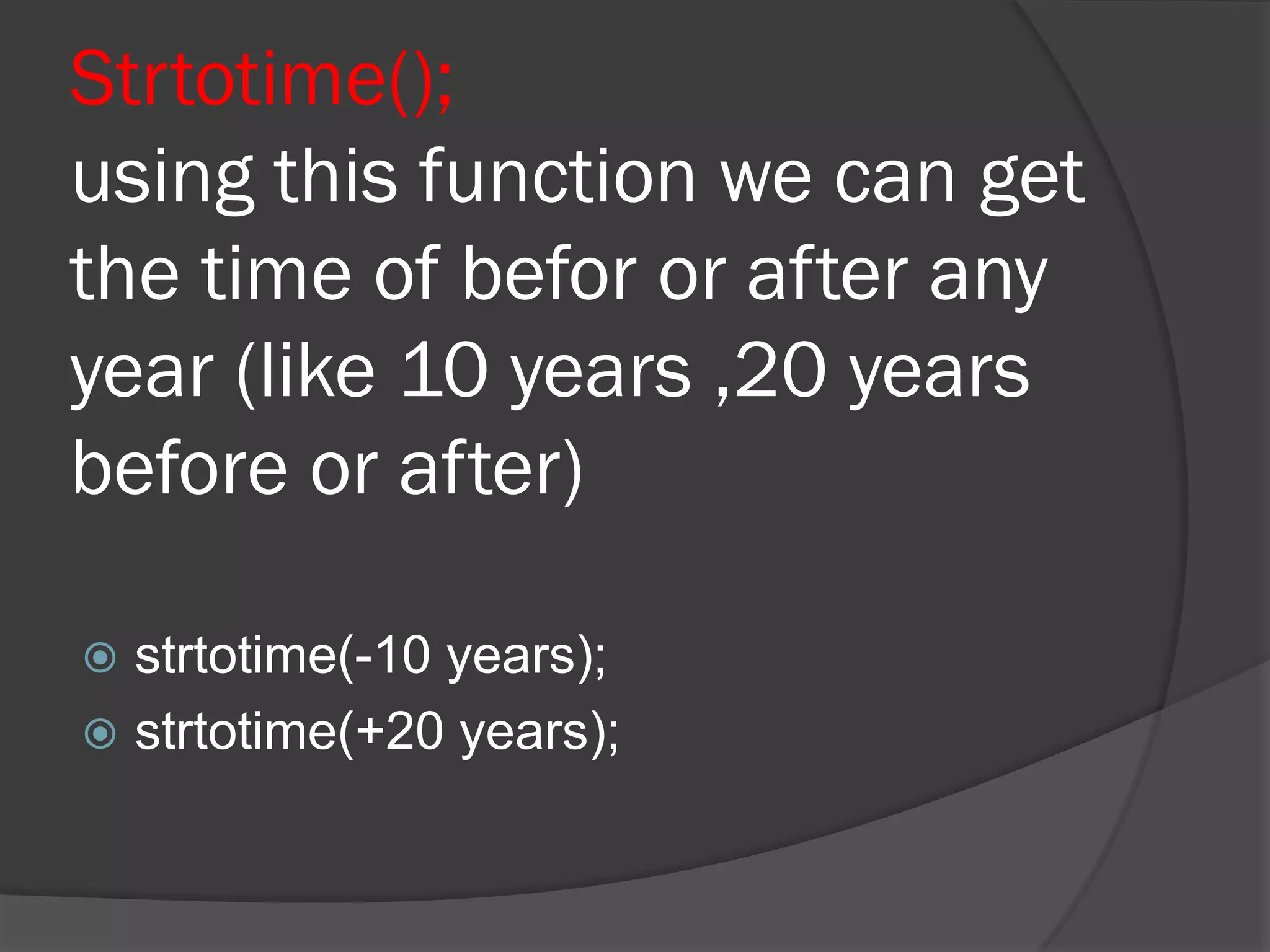
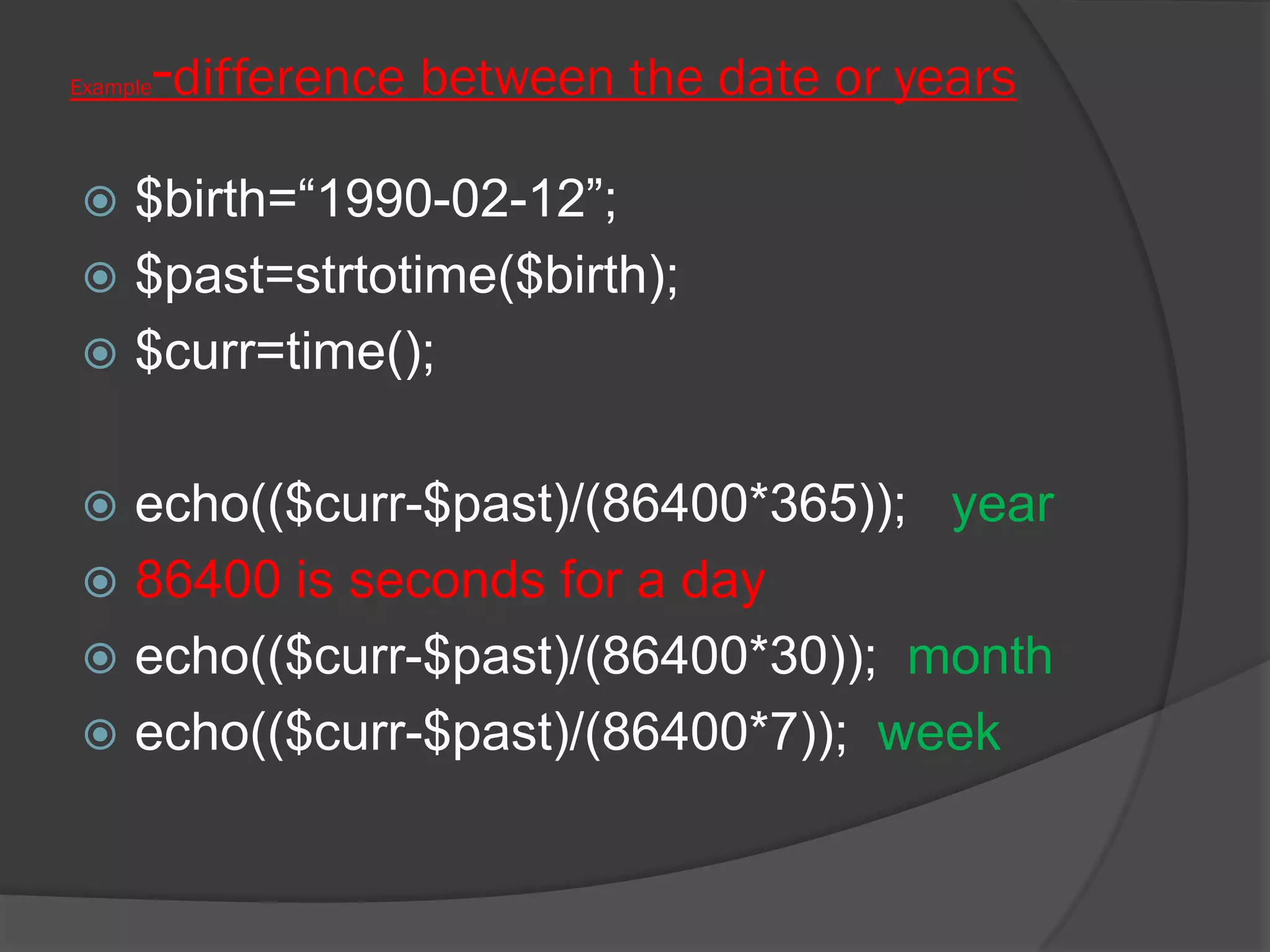
The document outlines various functions in PHP for handling date and time, including setting the timezone, formatting output, and calculating time differences. Key functions mentioned include date_default_timezone_set(), date(), time(), and strtotime(). It provides examples of how to use these functions to display the current date and time, as well as perform calculations involving past and future dates.