Embed presentation

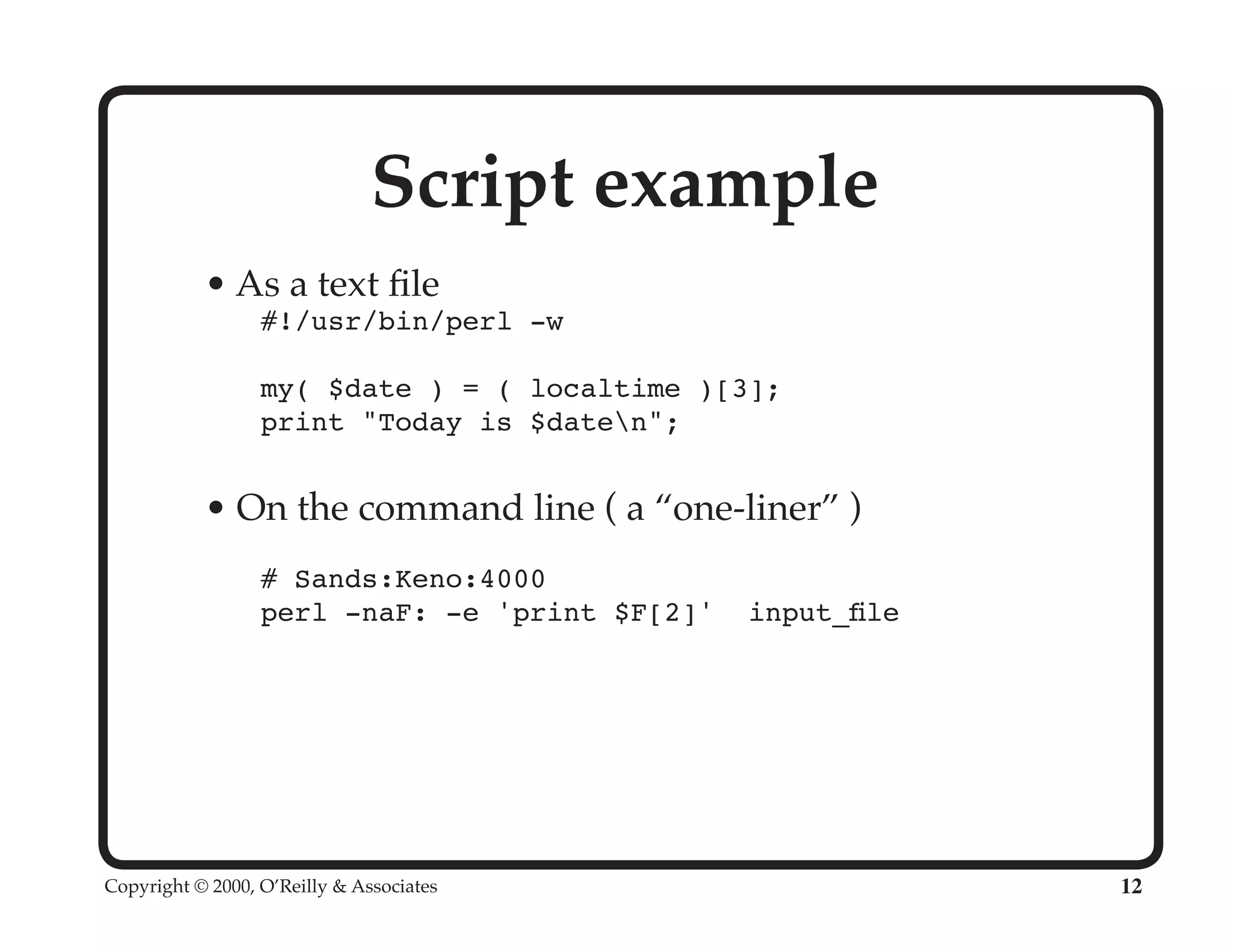
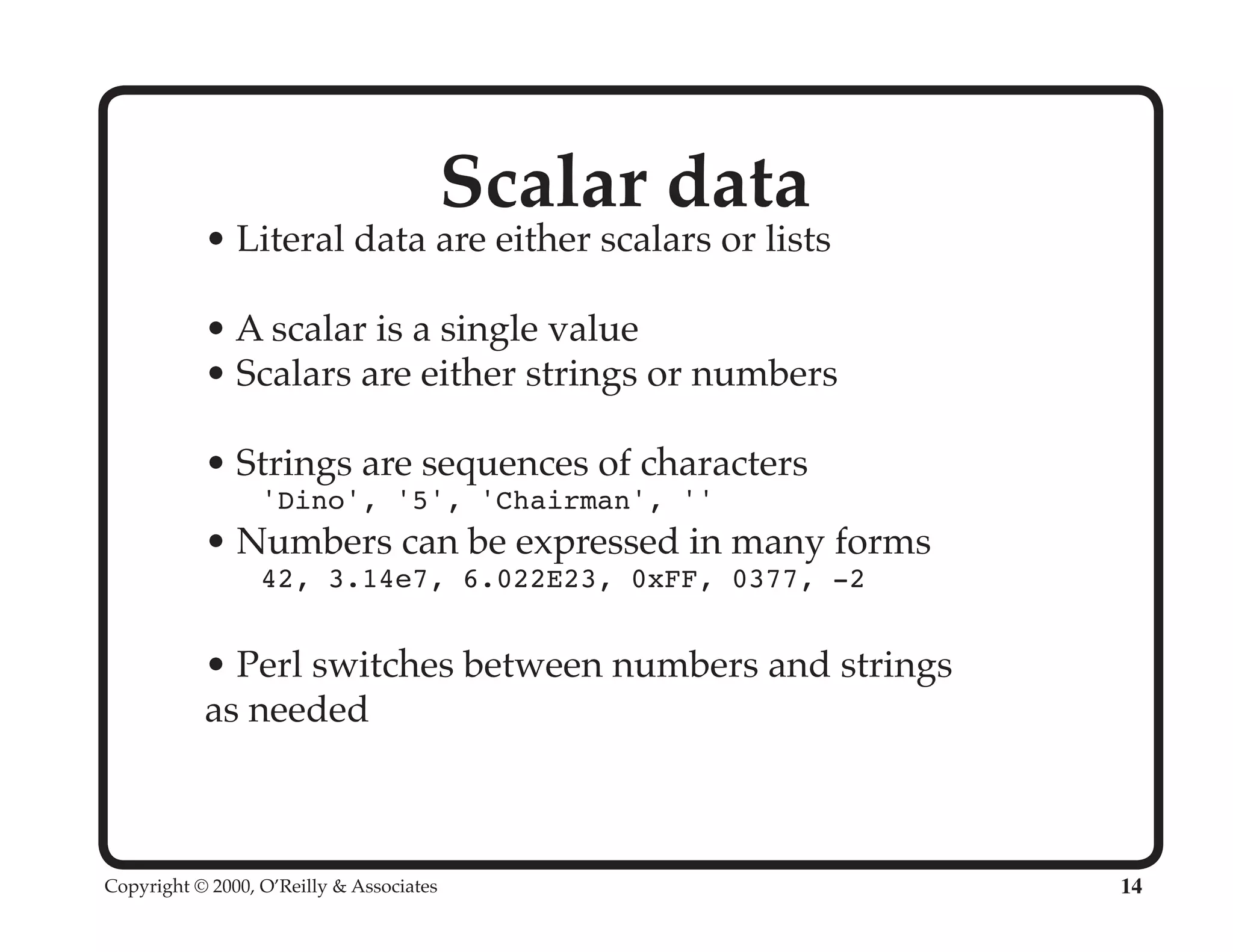
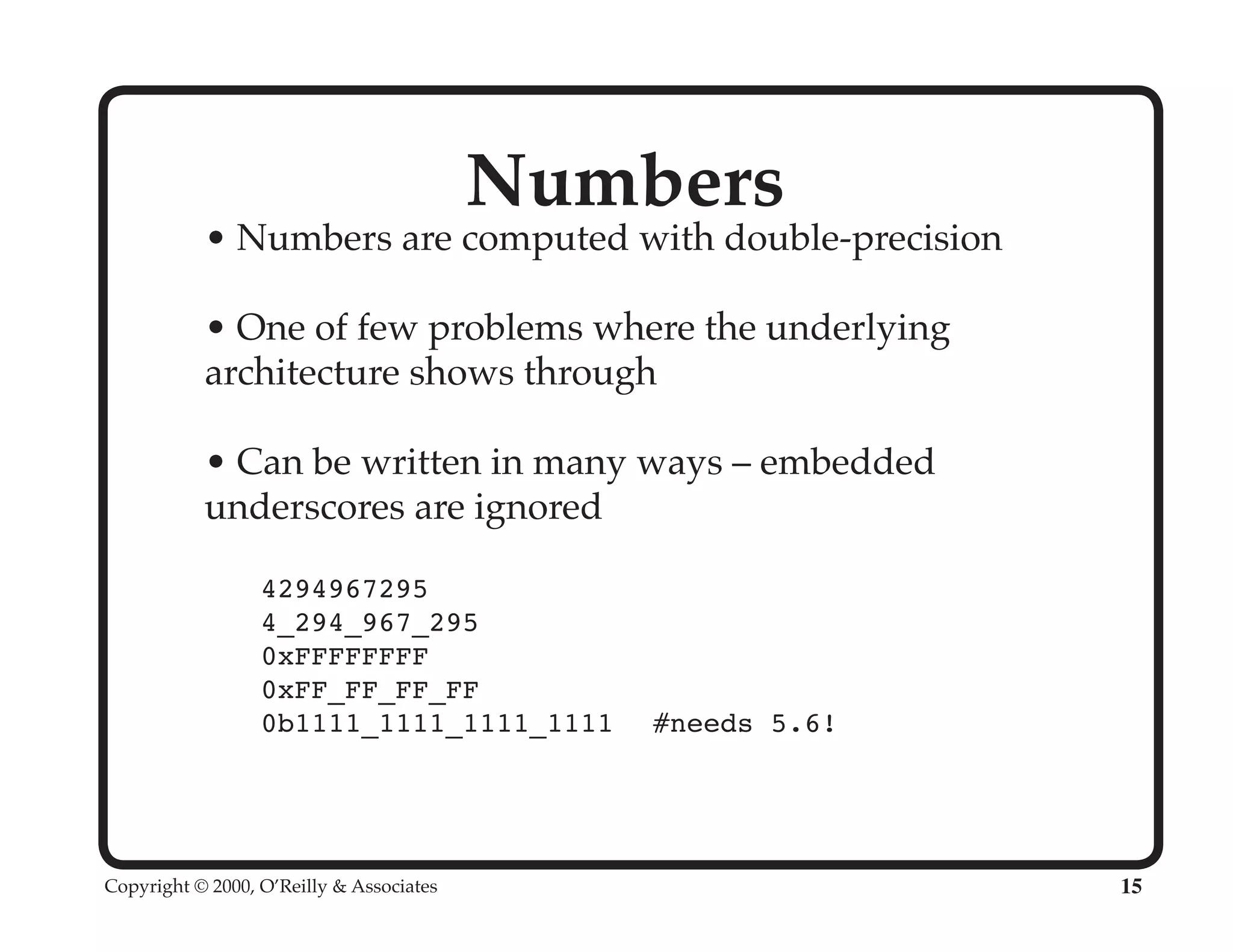
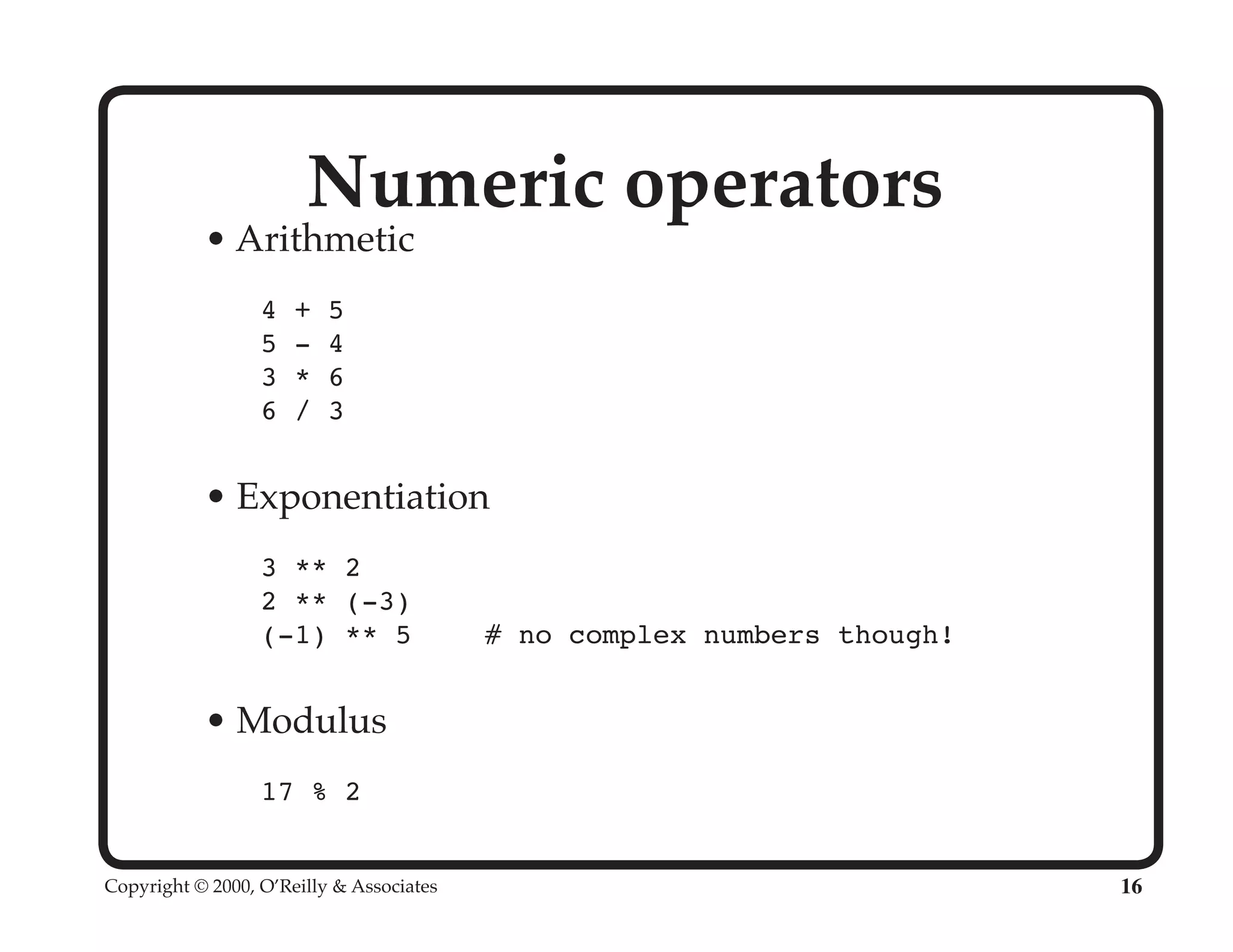
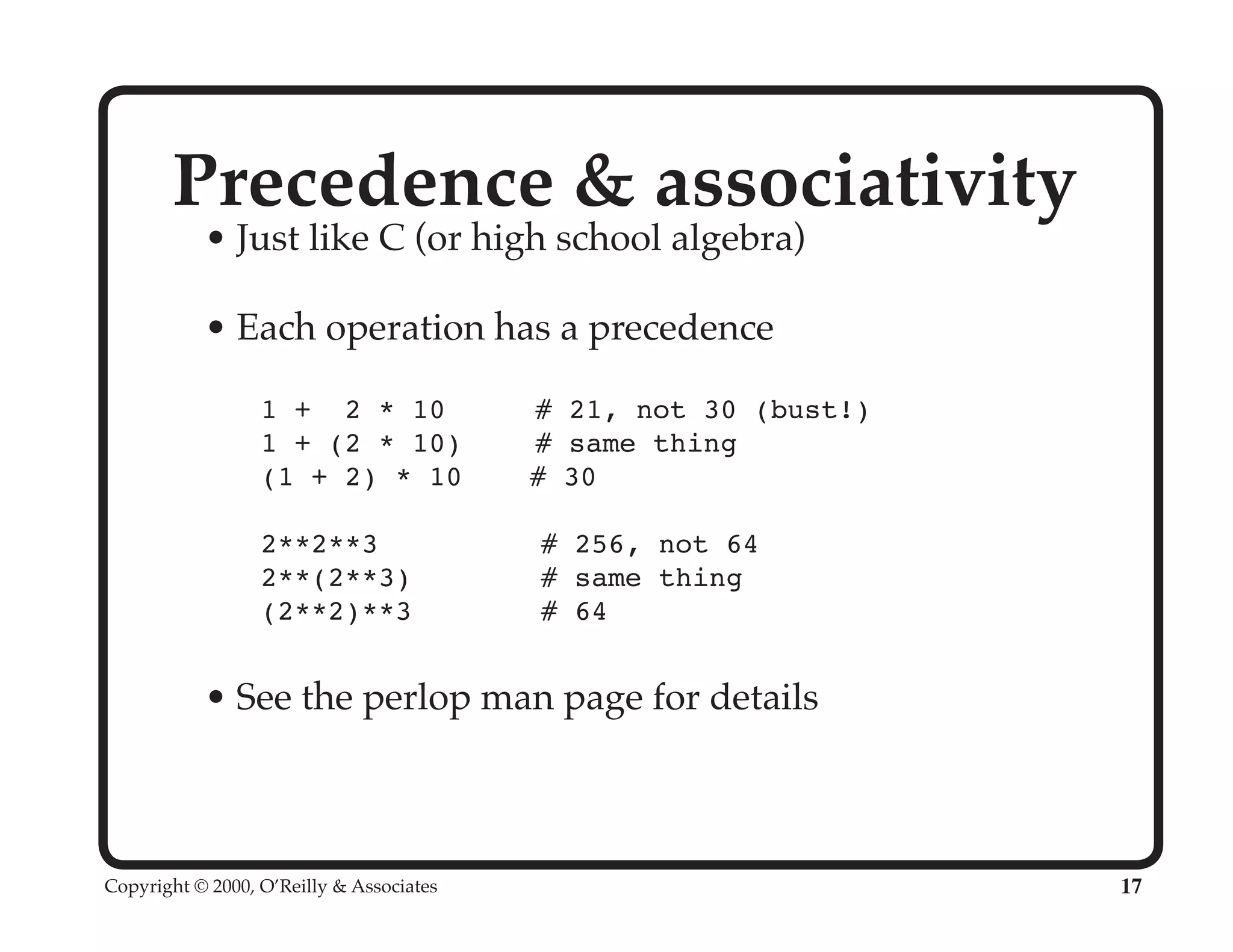
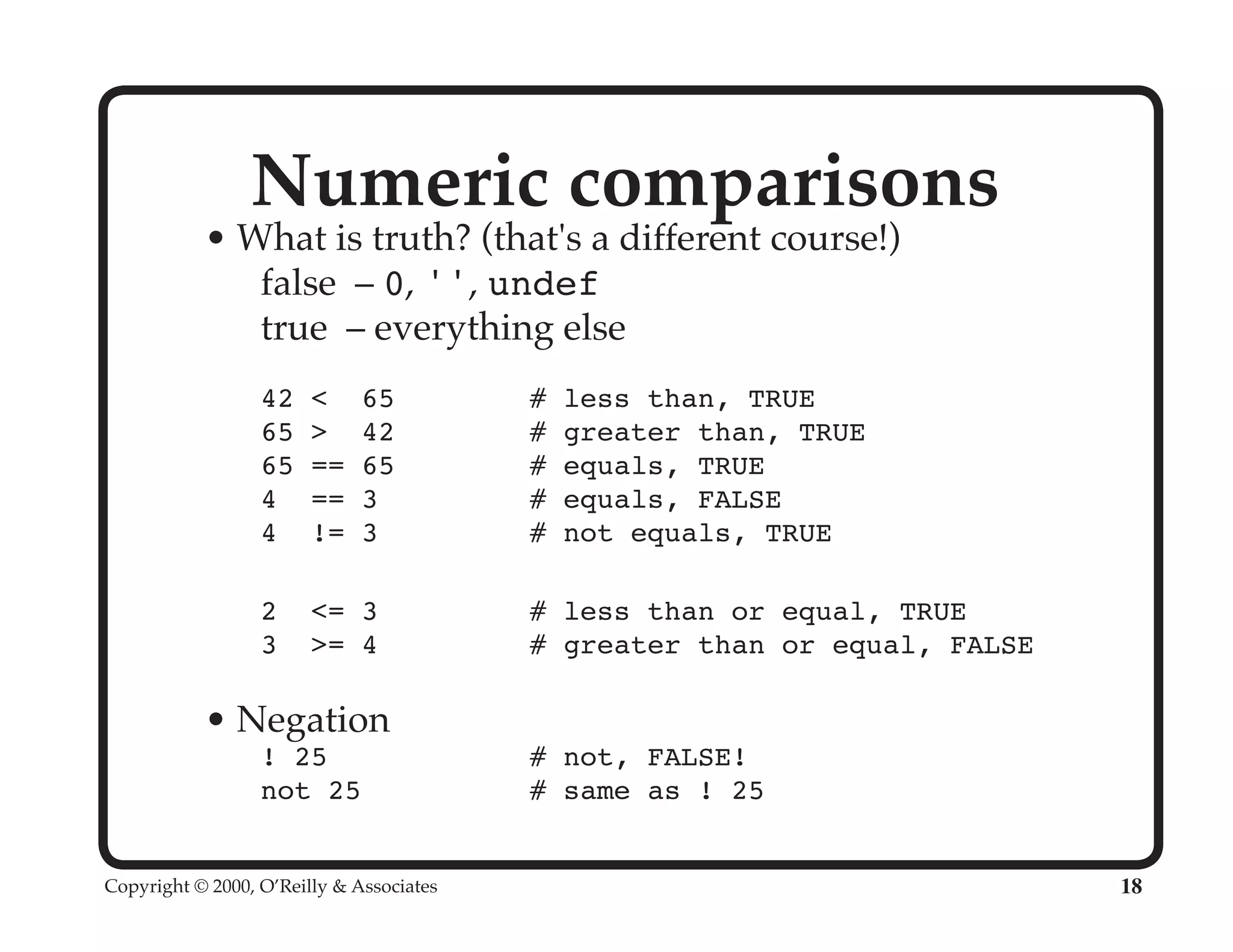
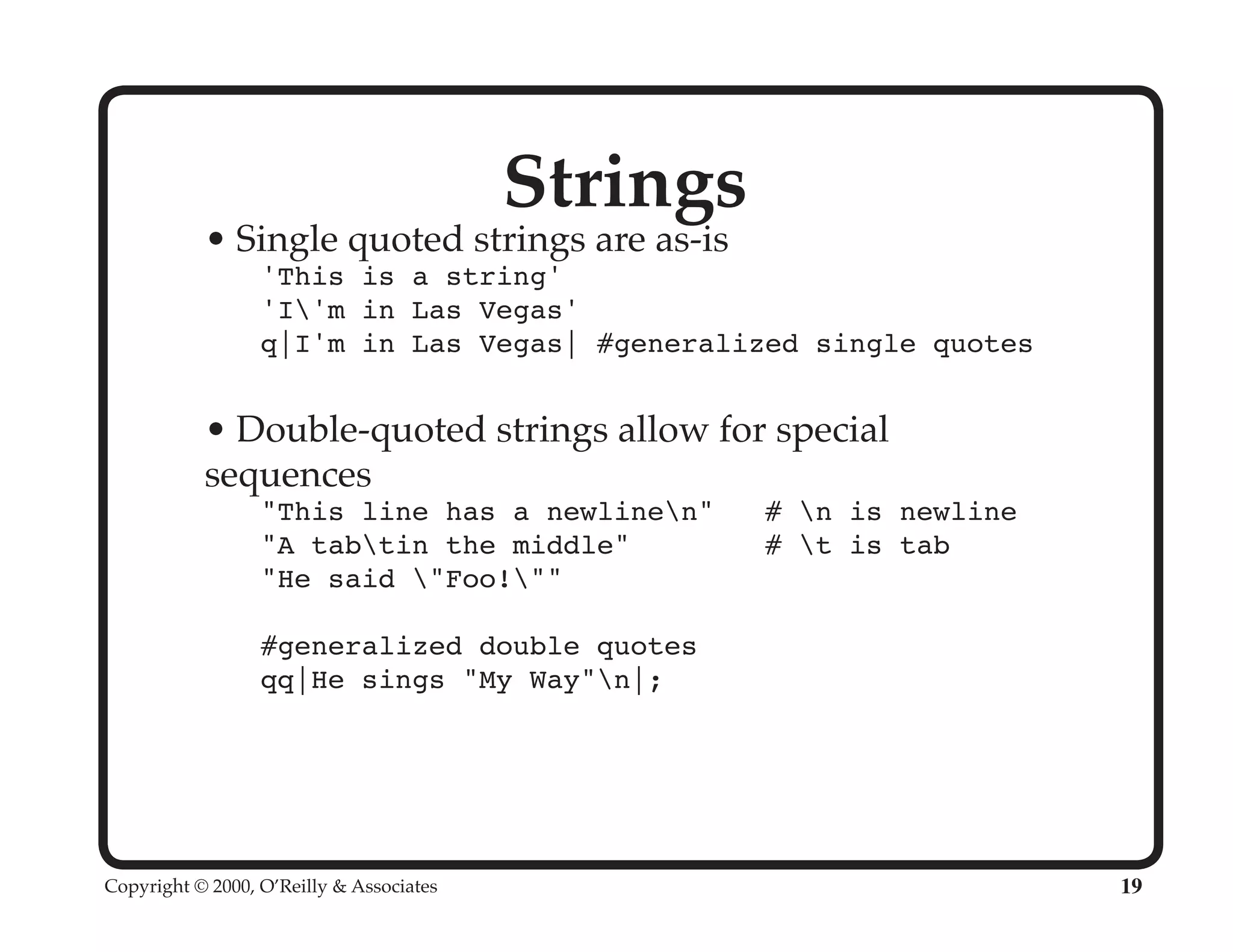
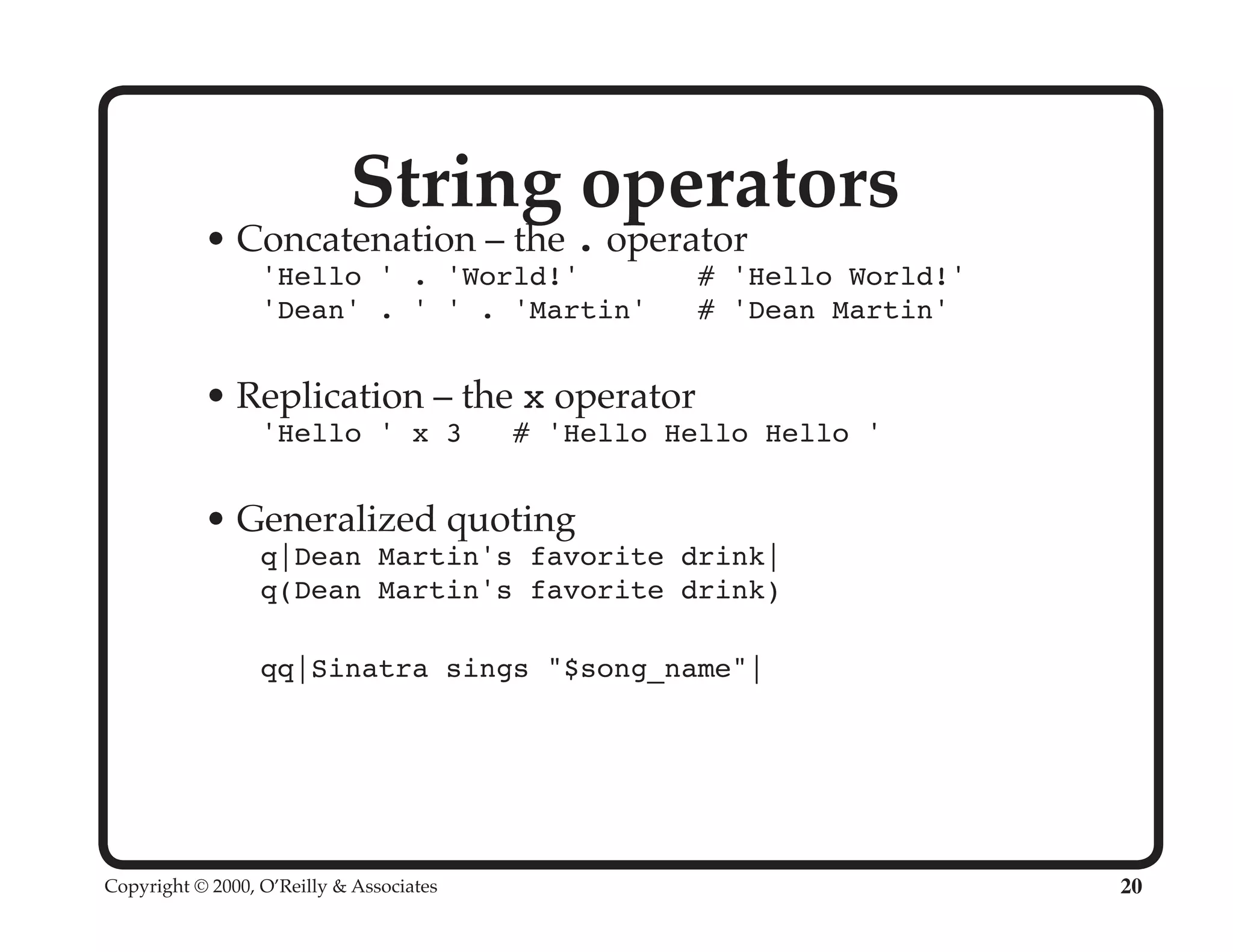
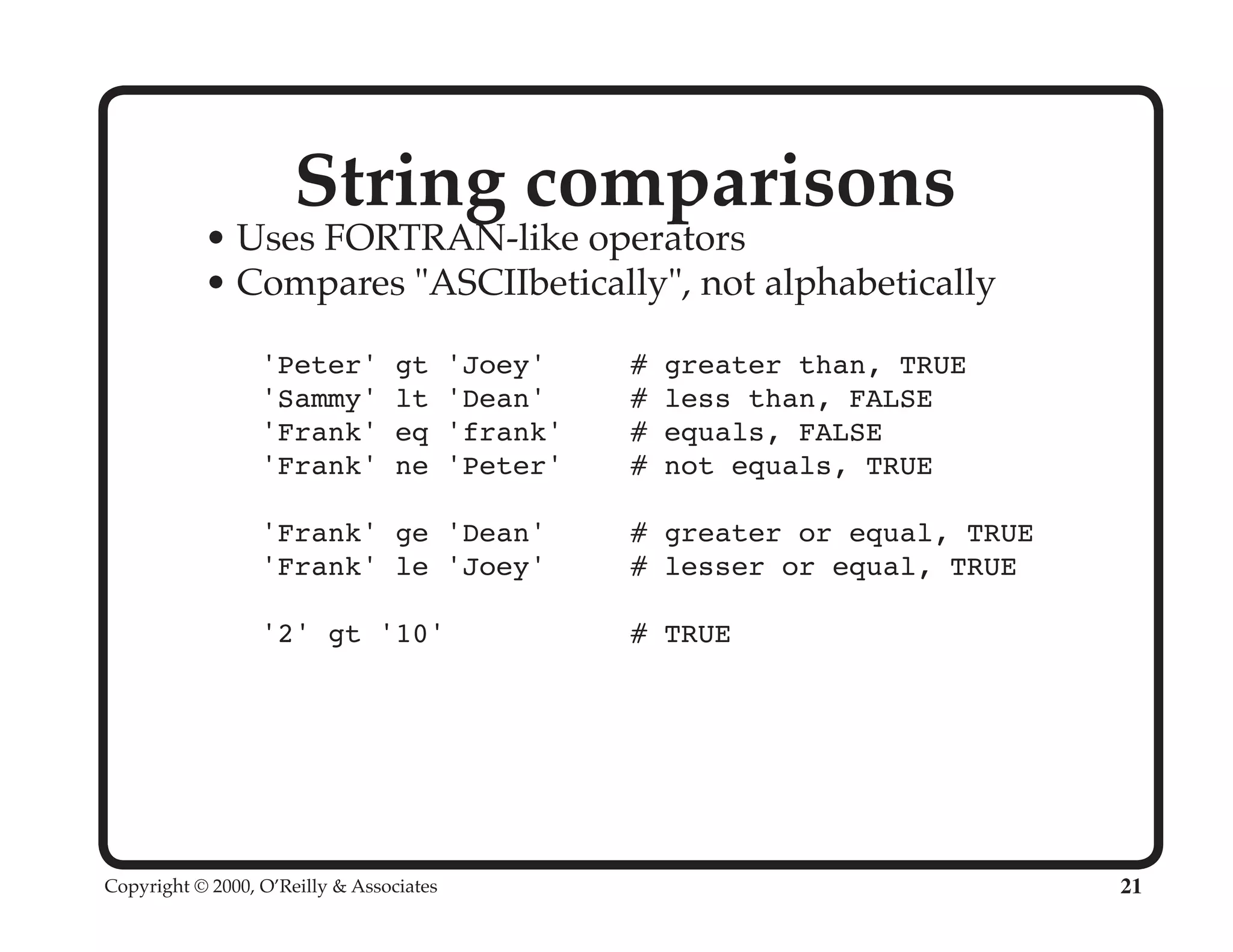
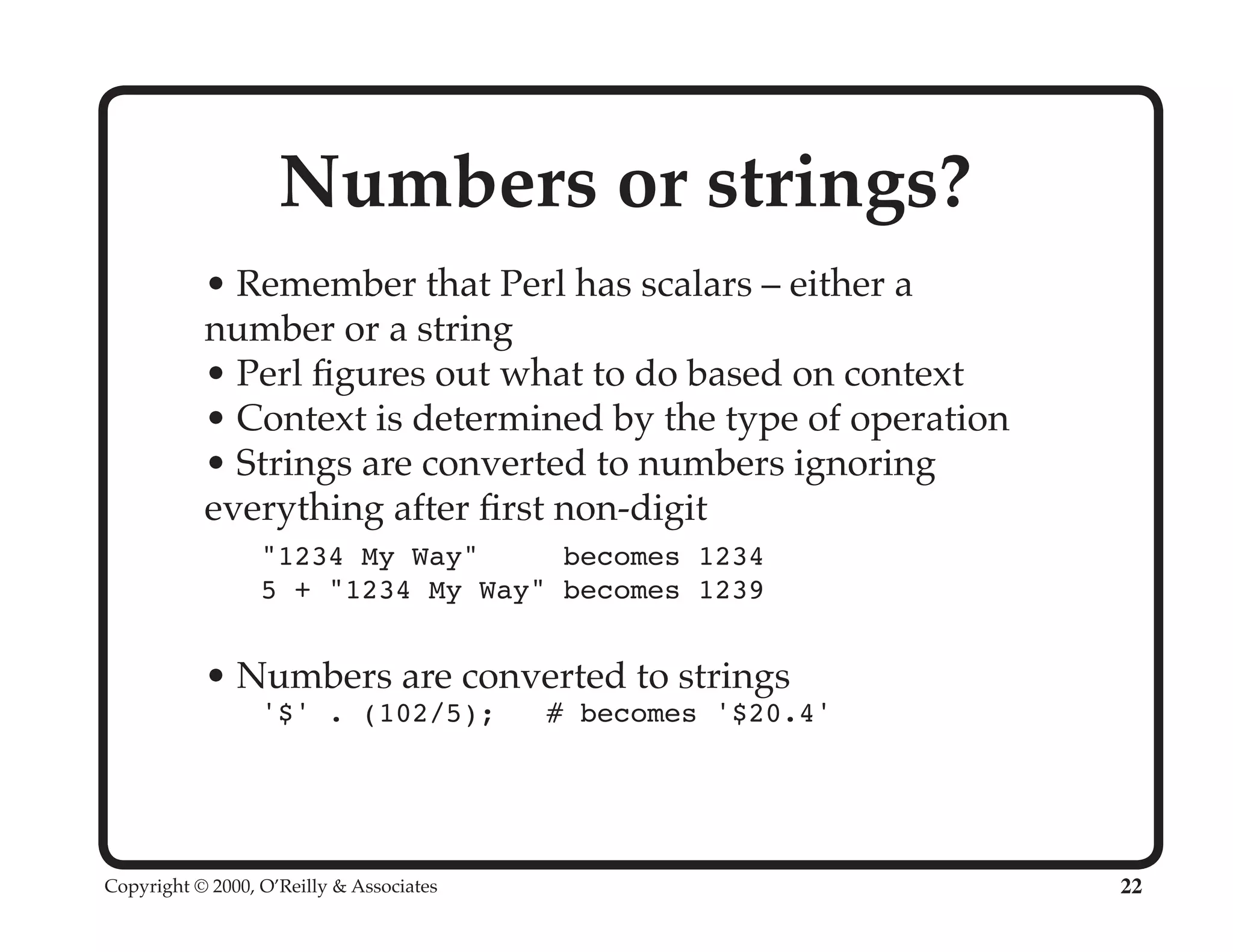
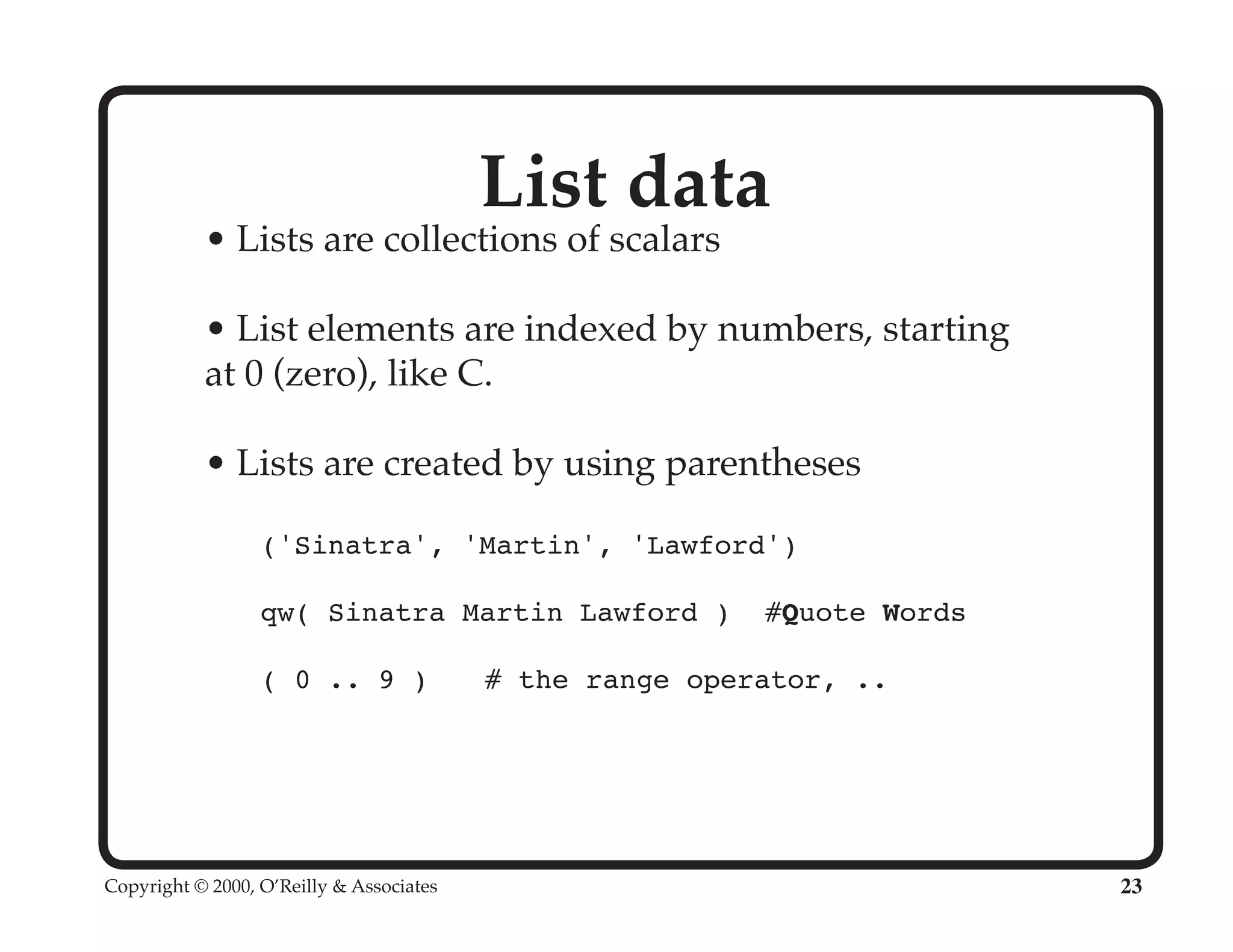
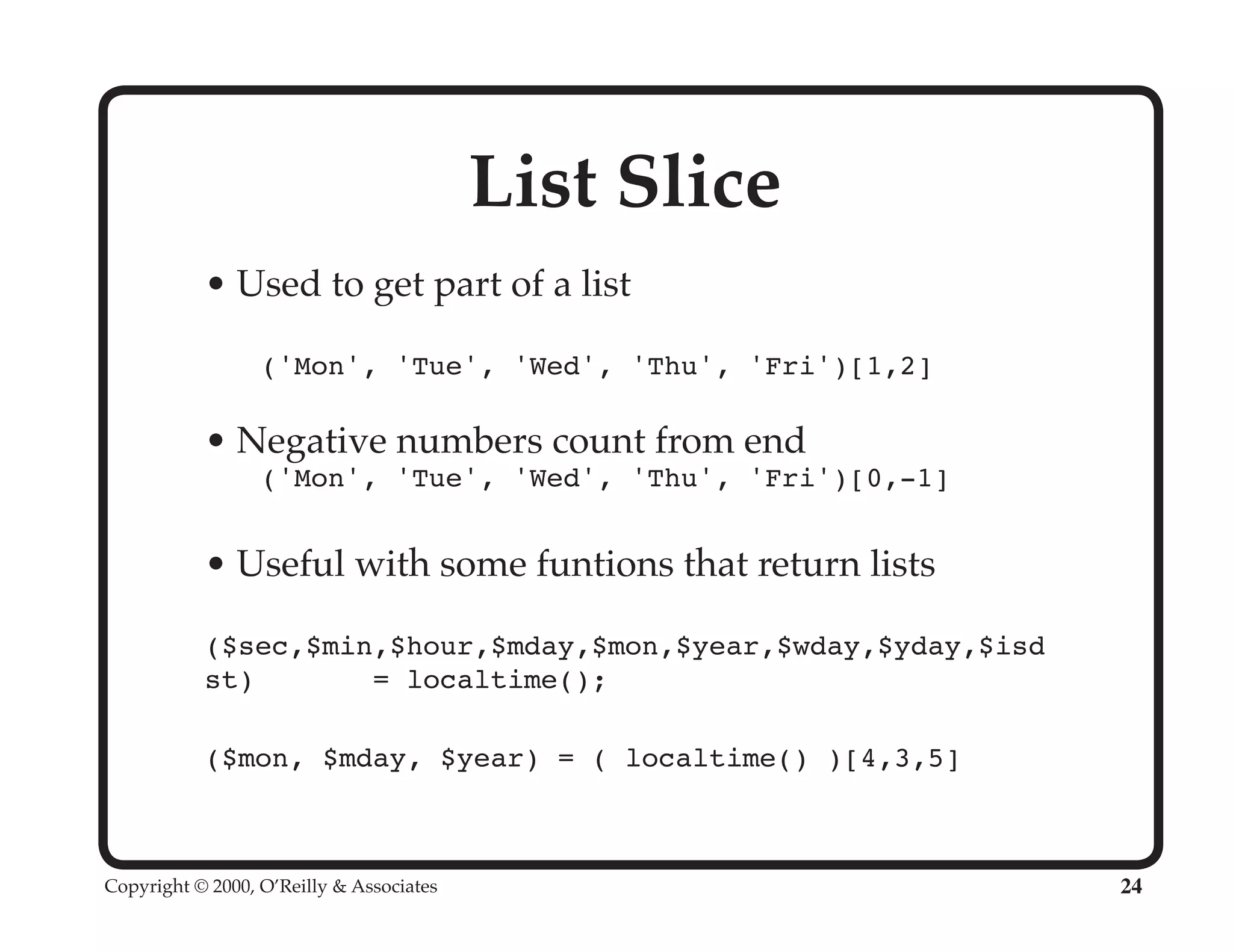
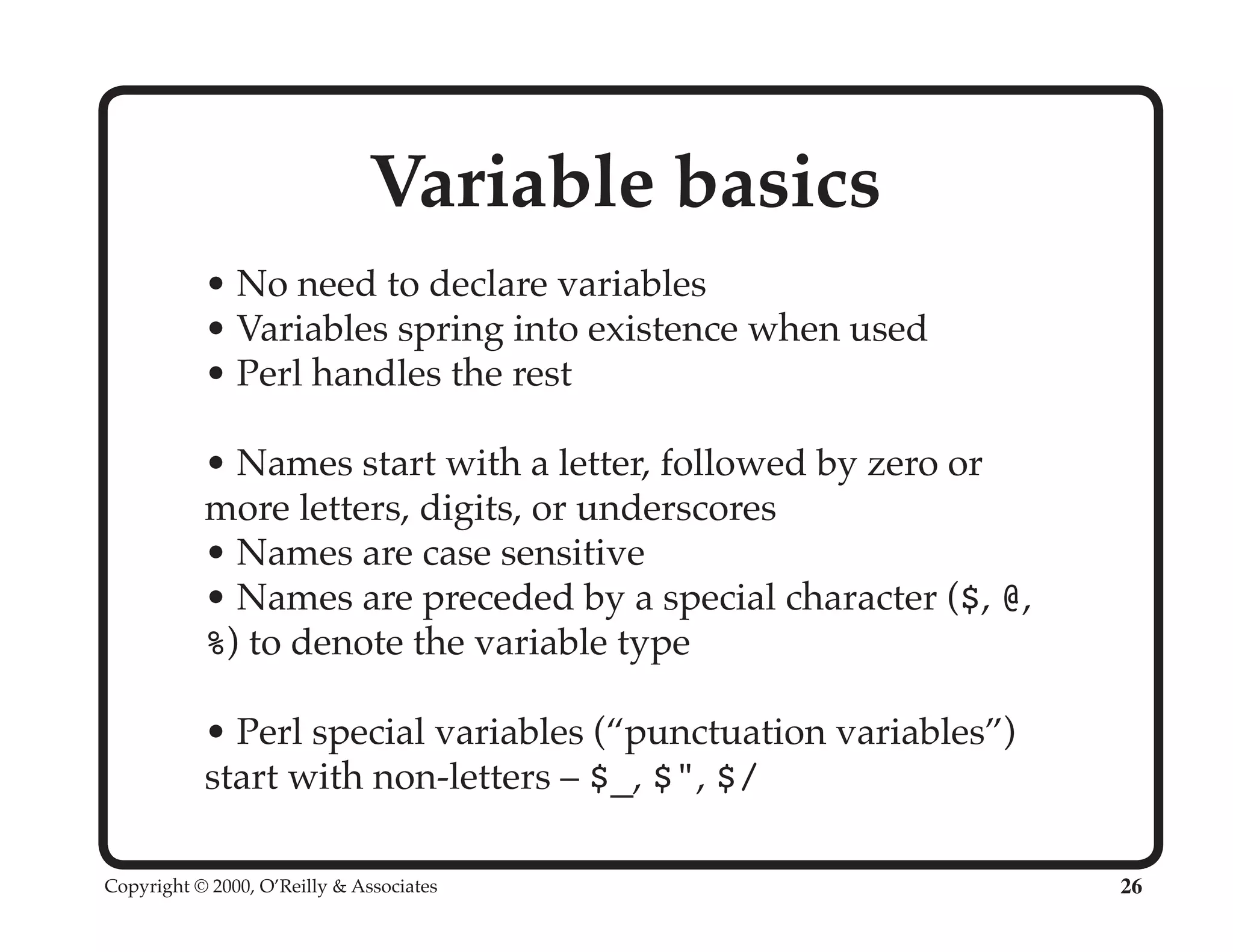
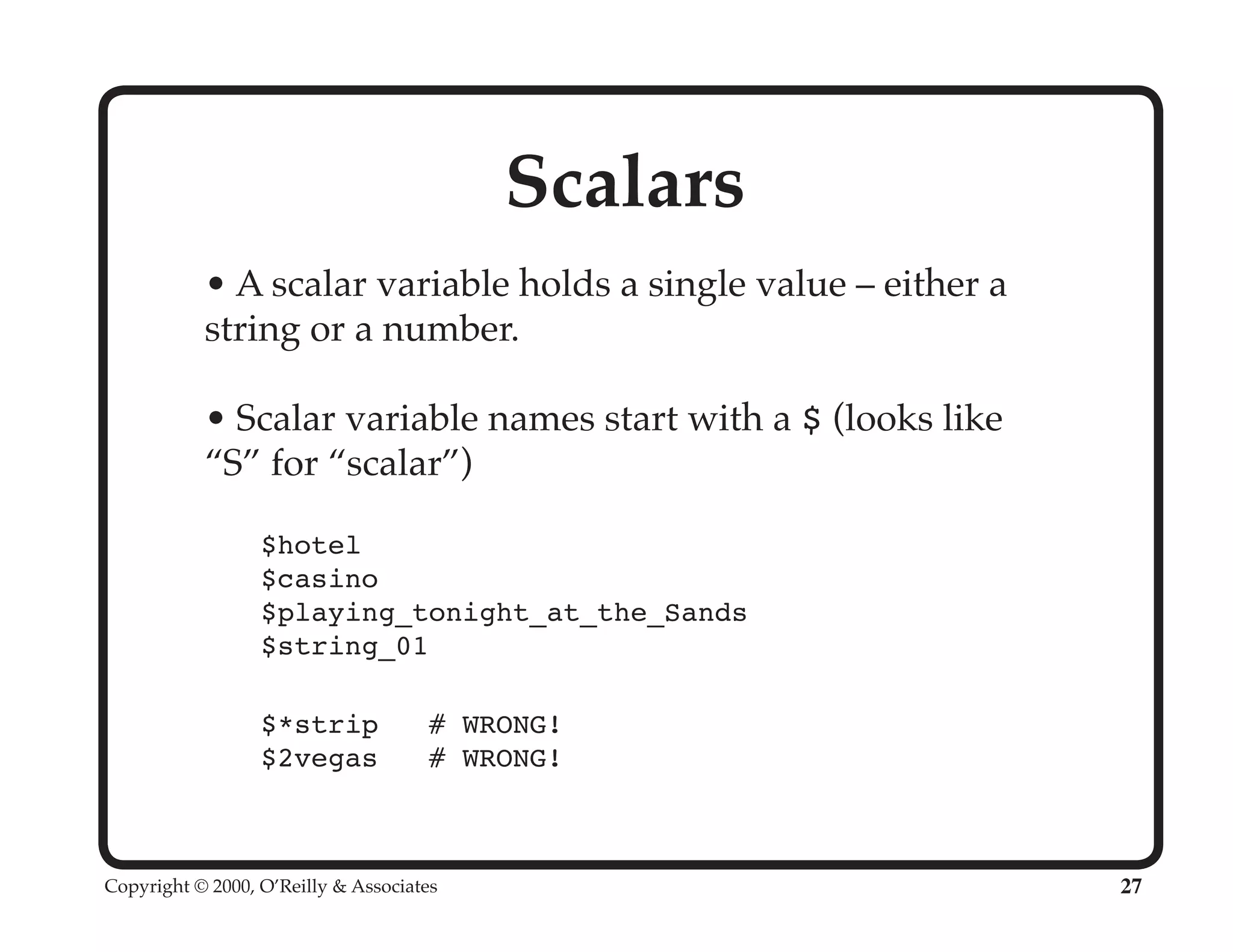
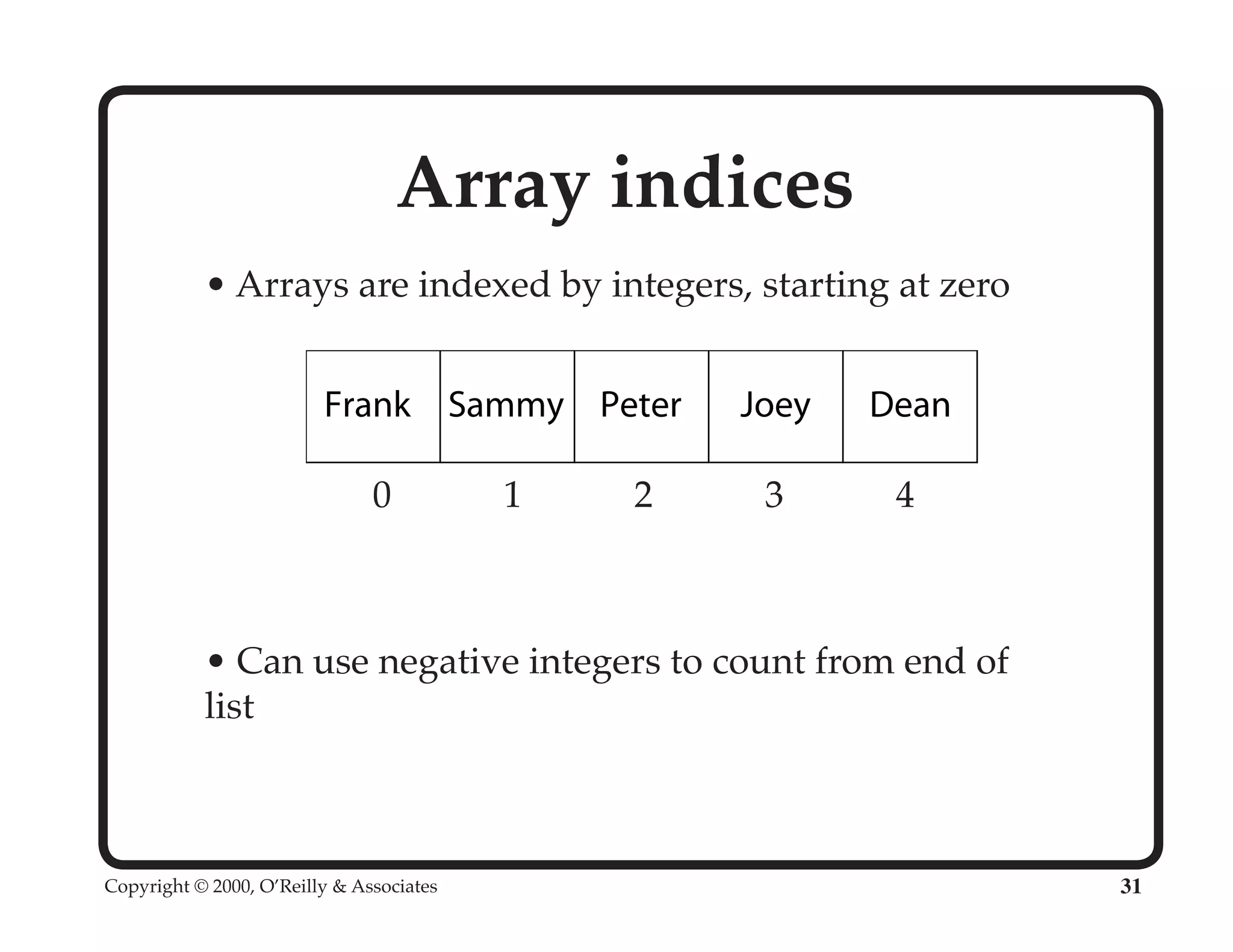
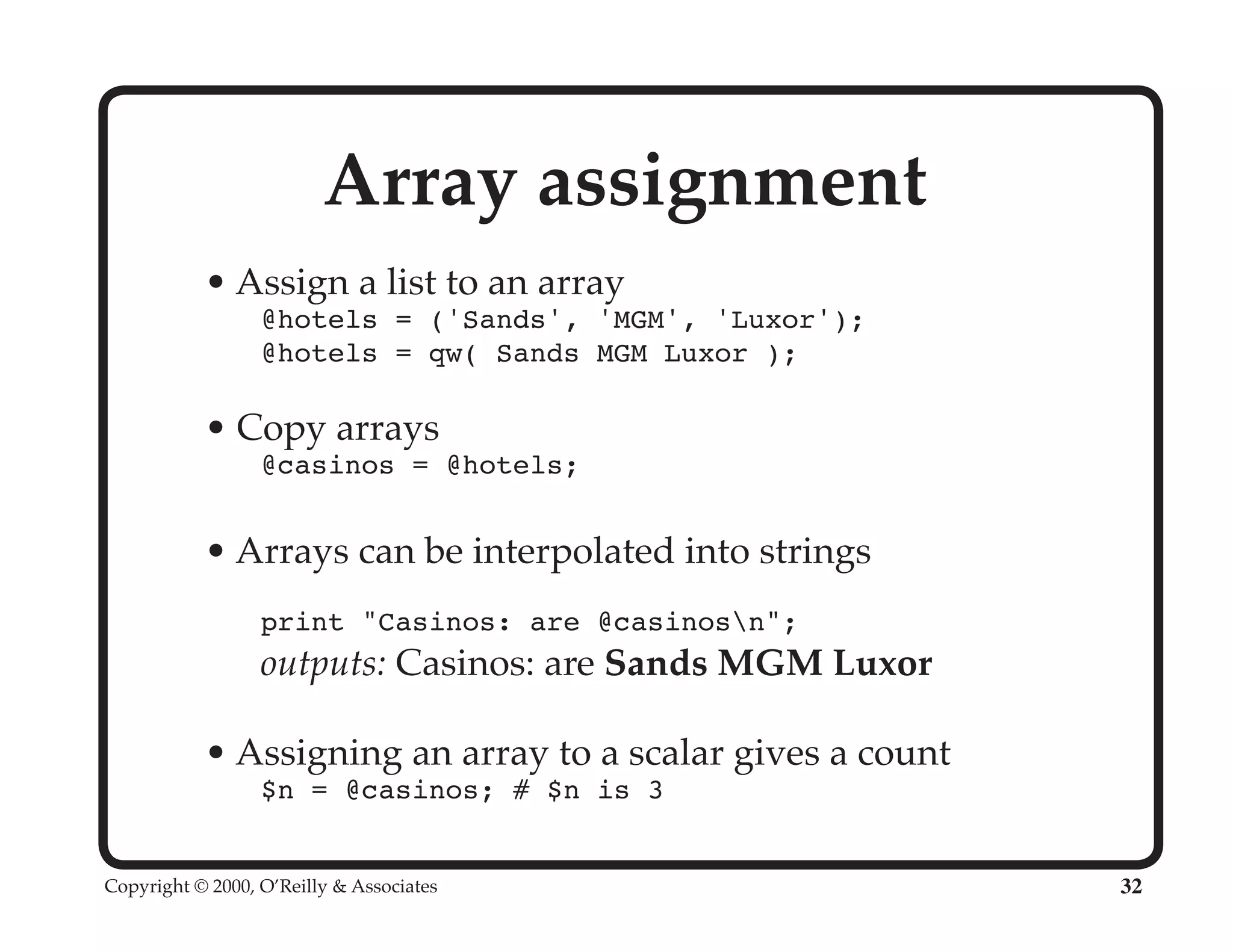
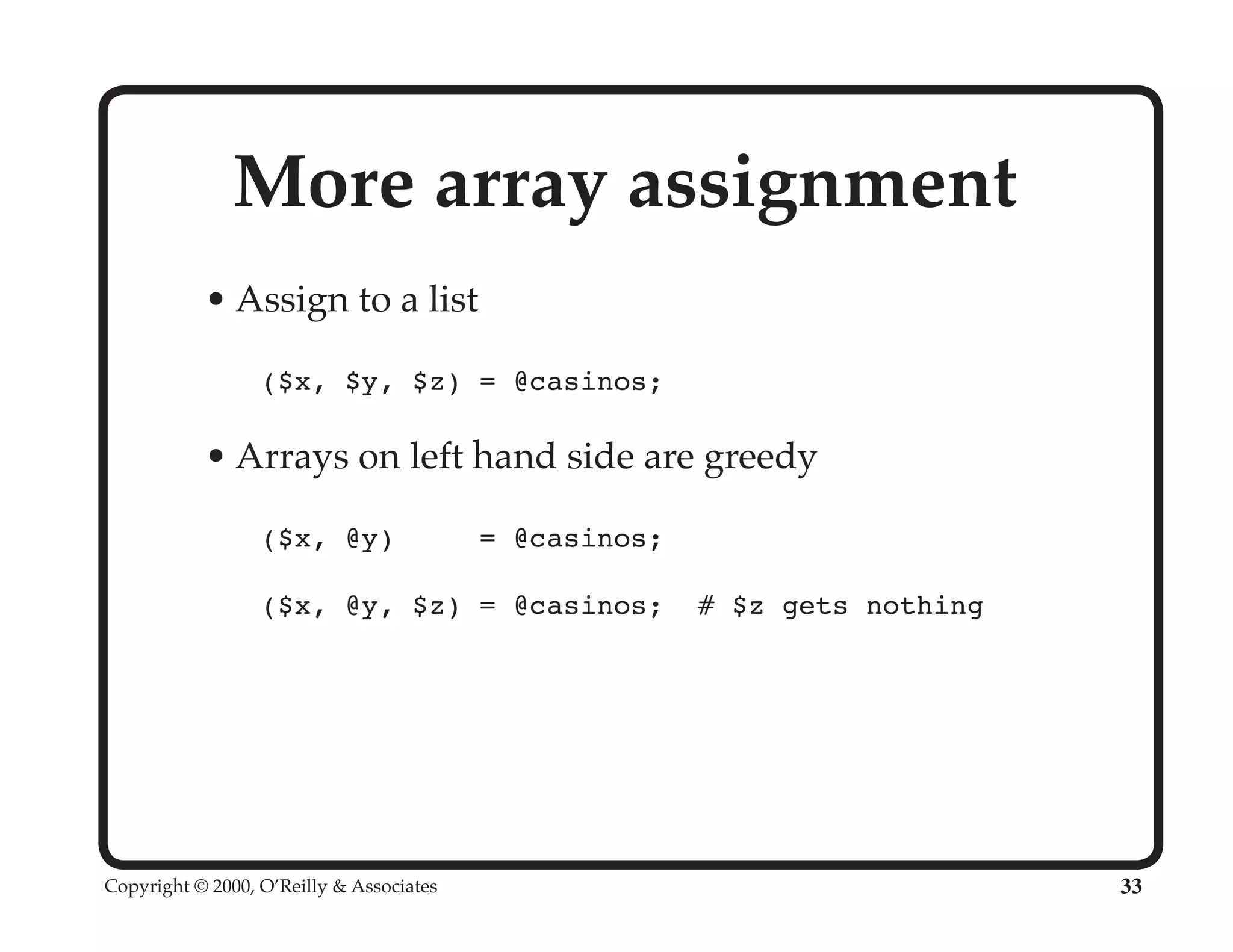
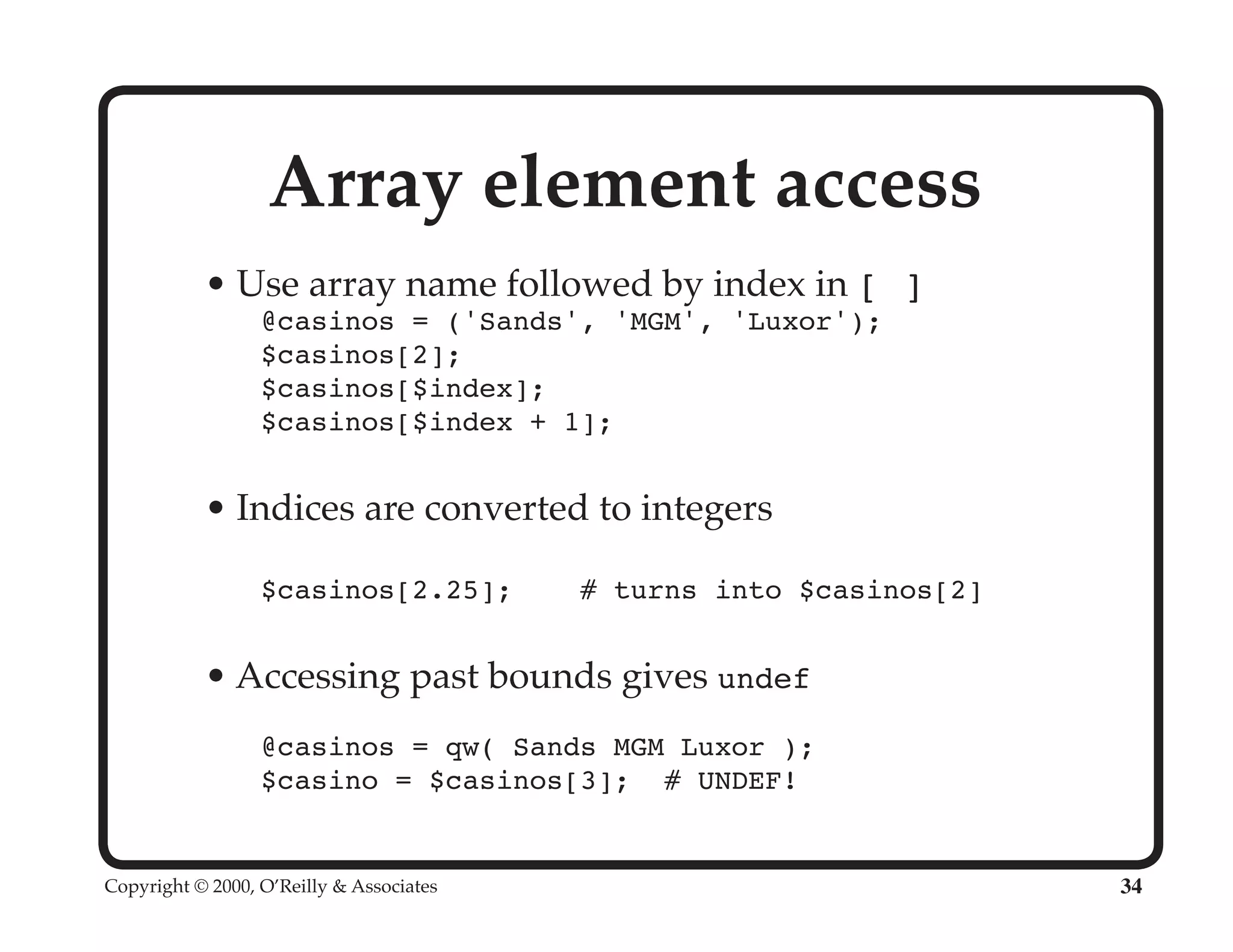
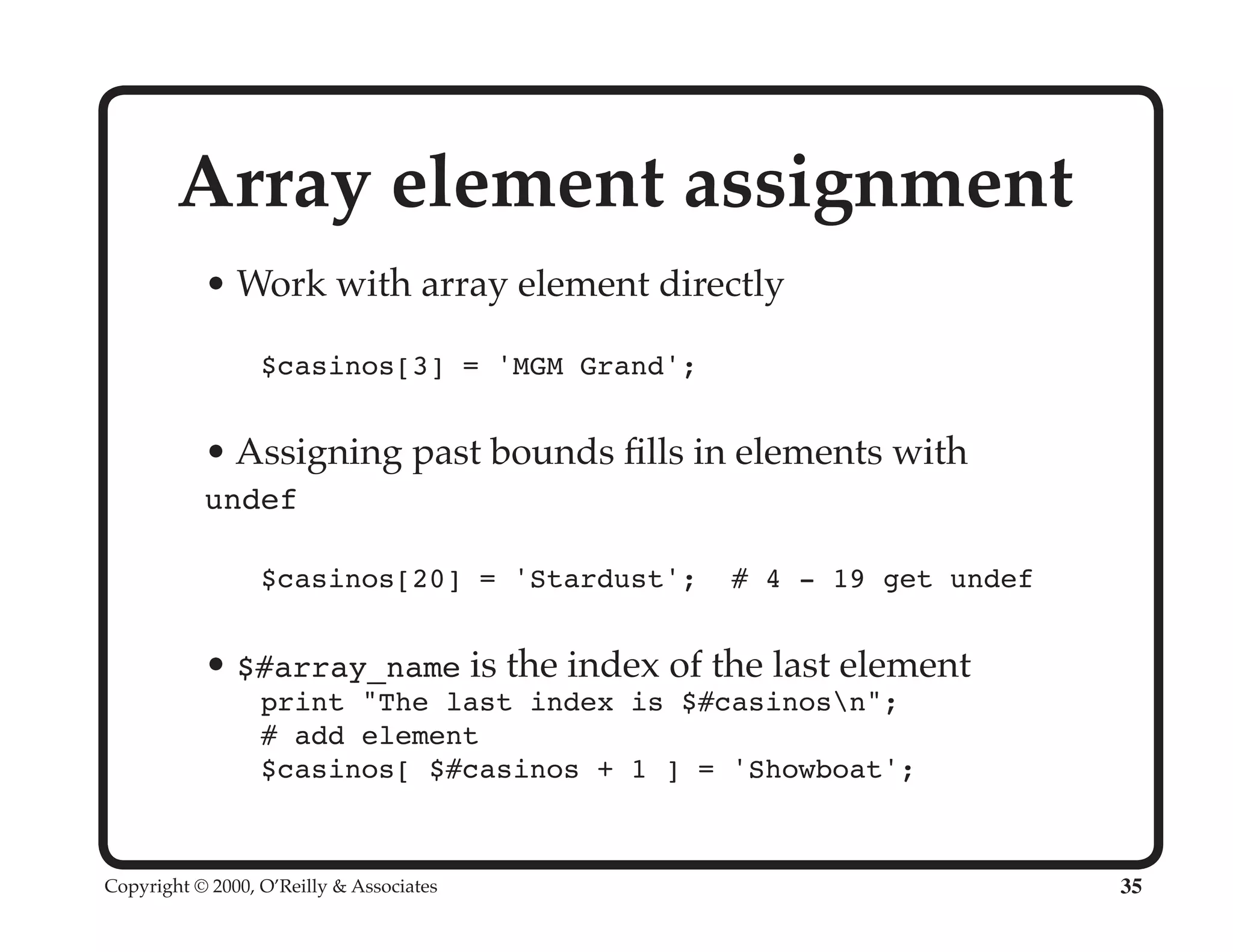
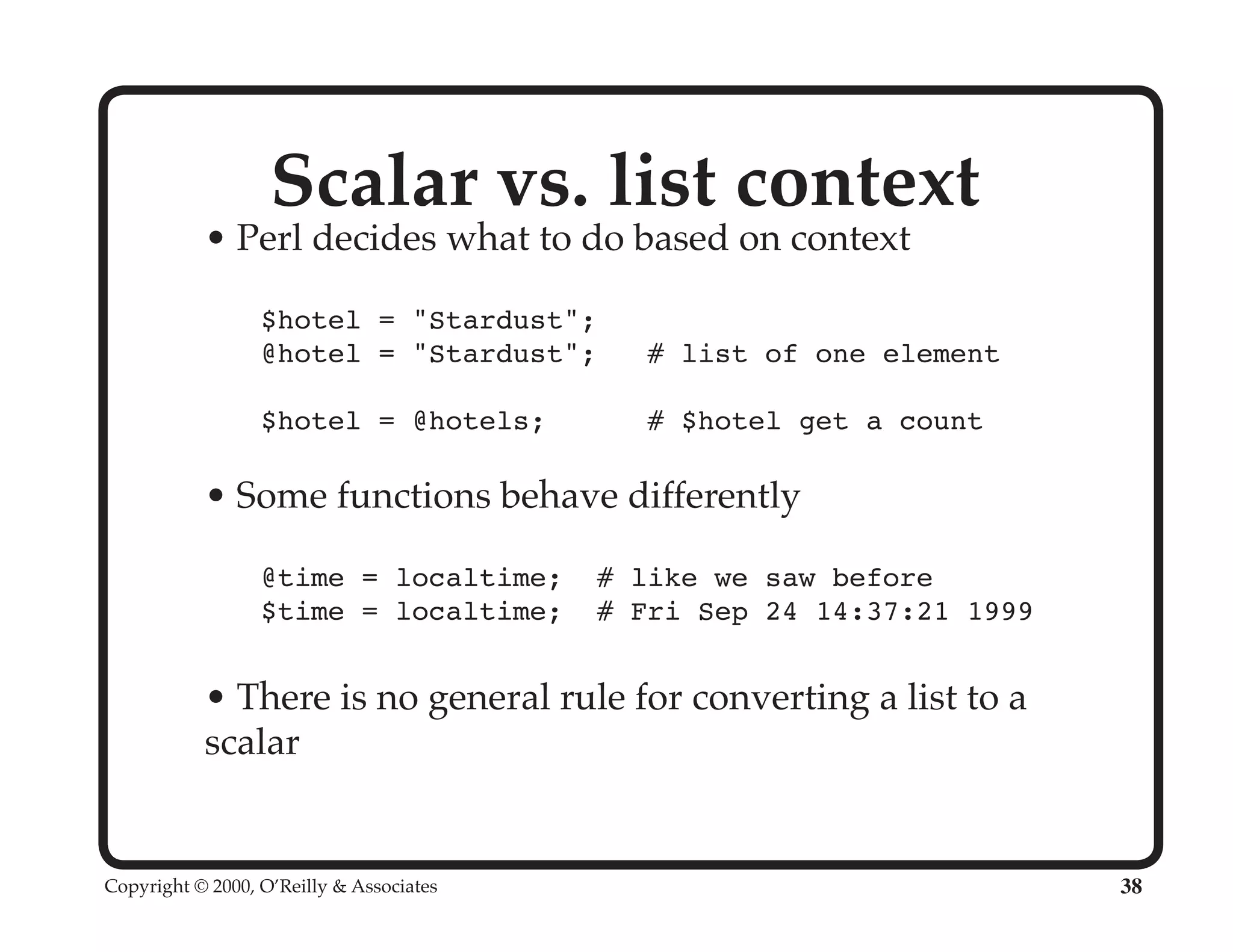
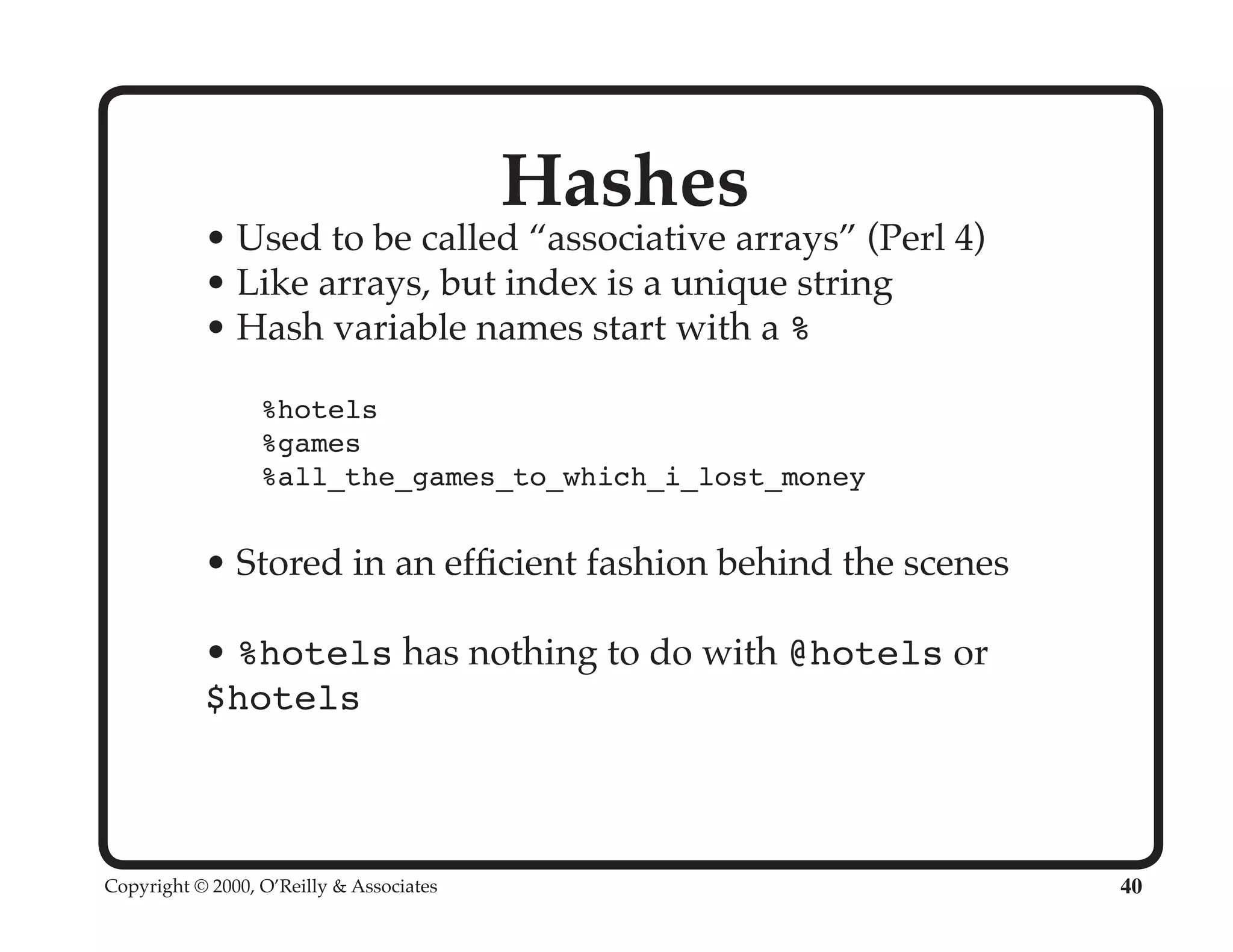
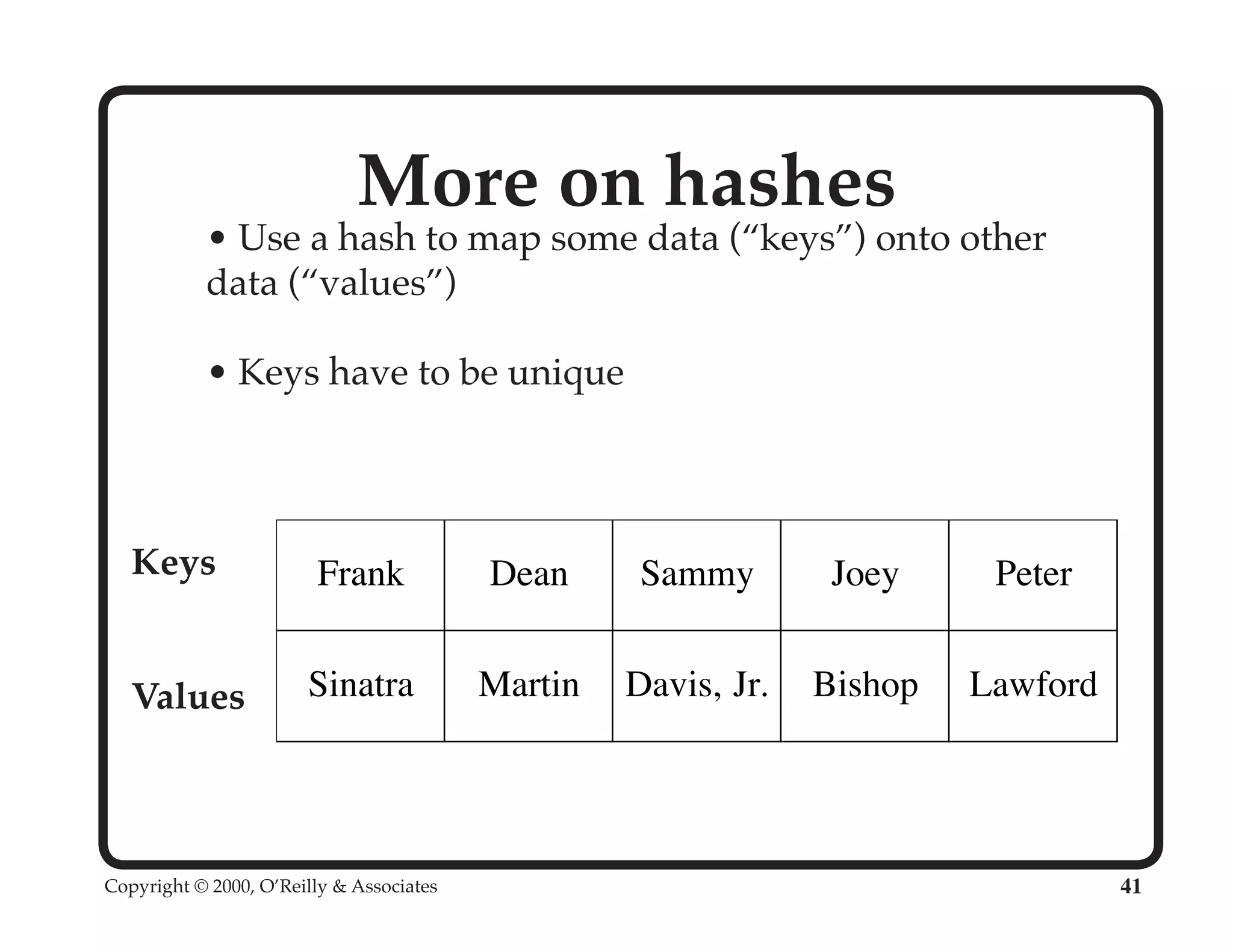
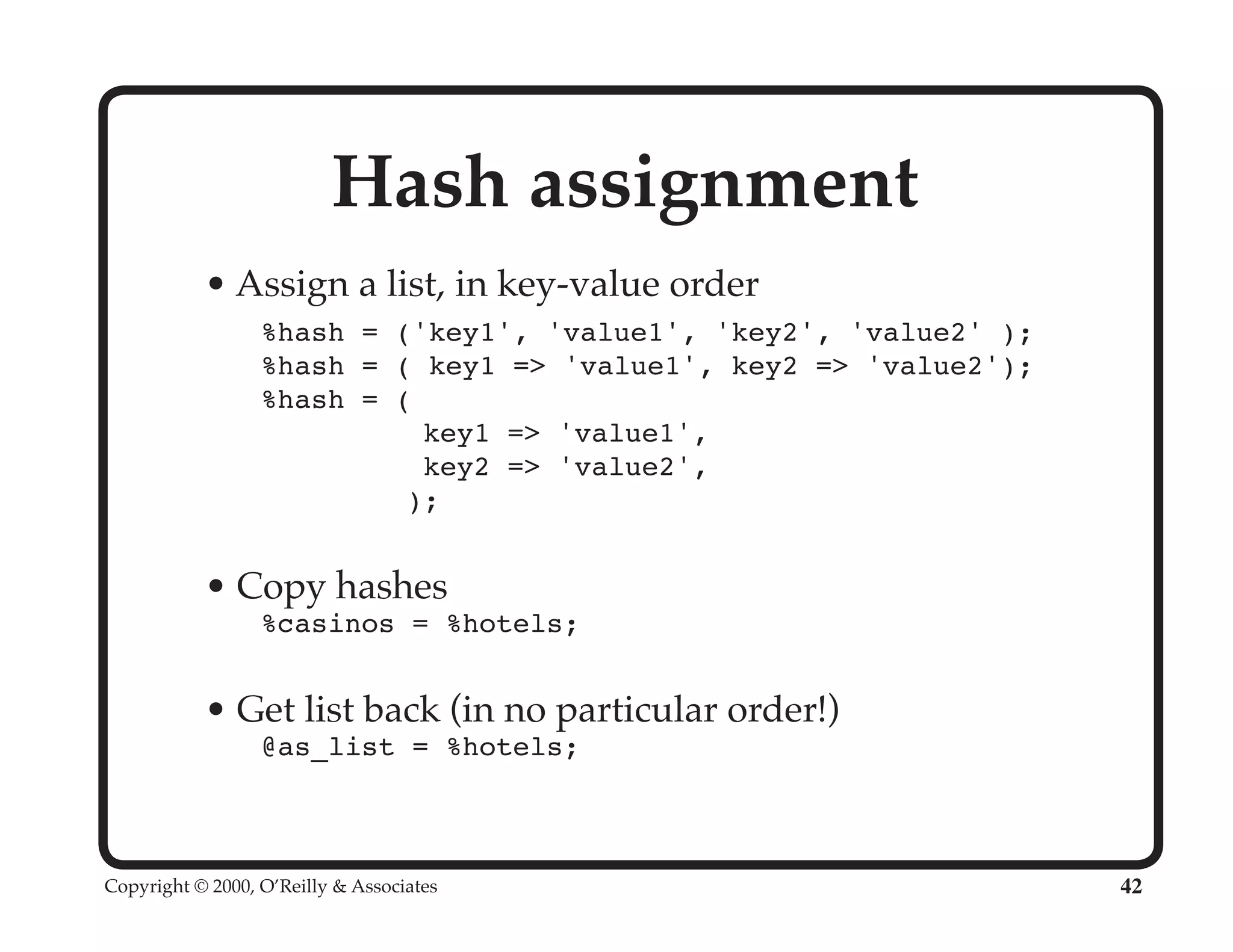
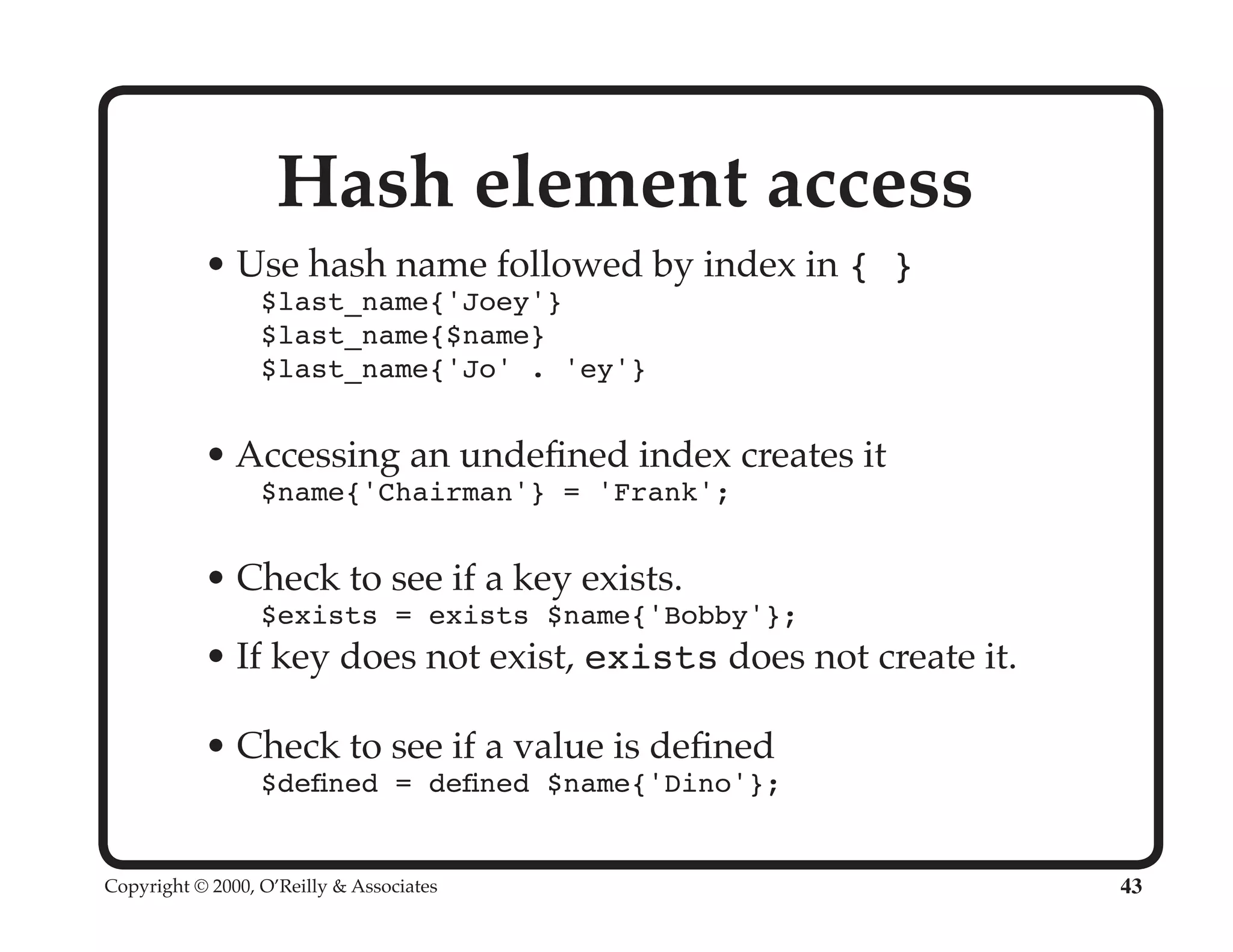
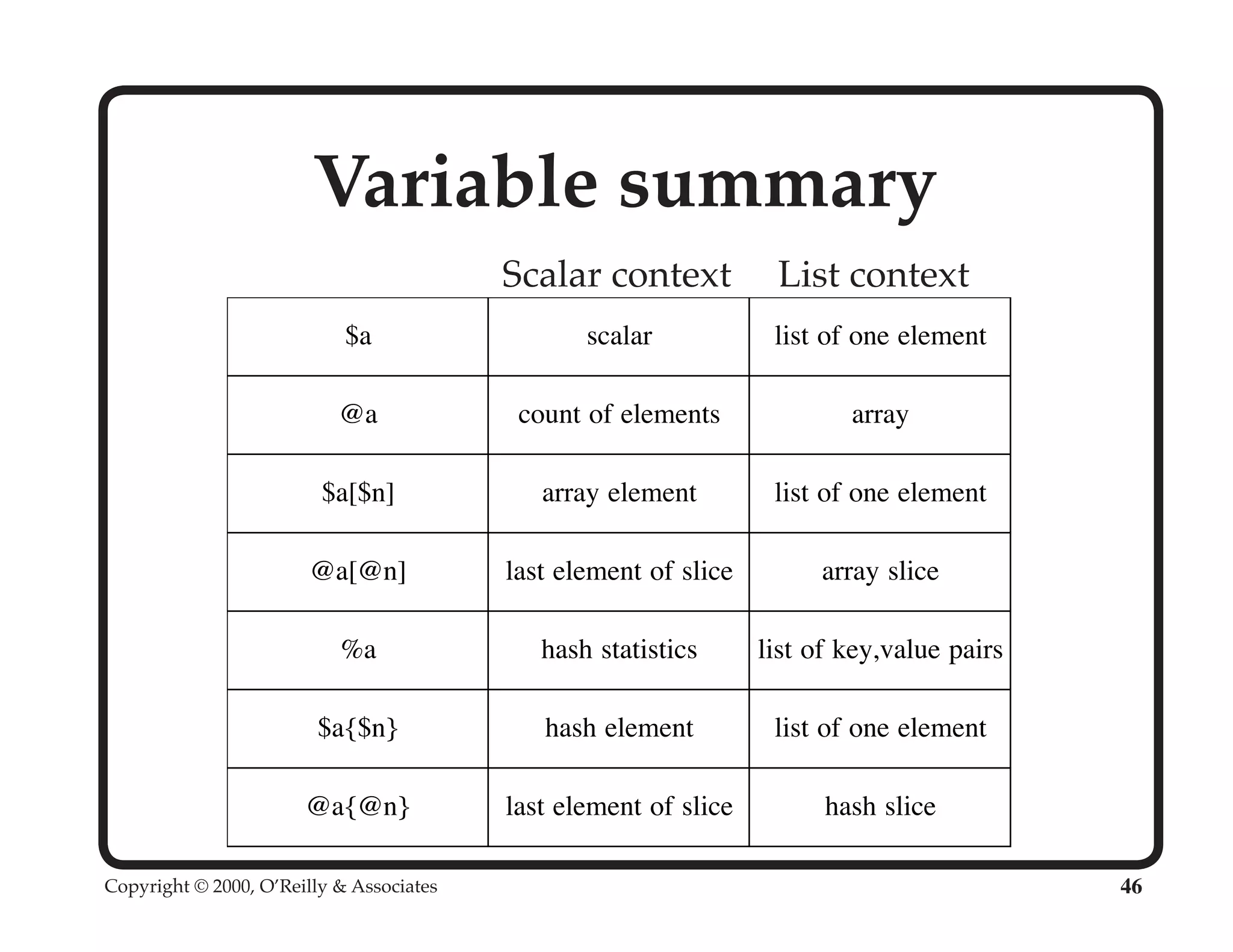
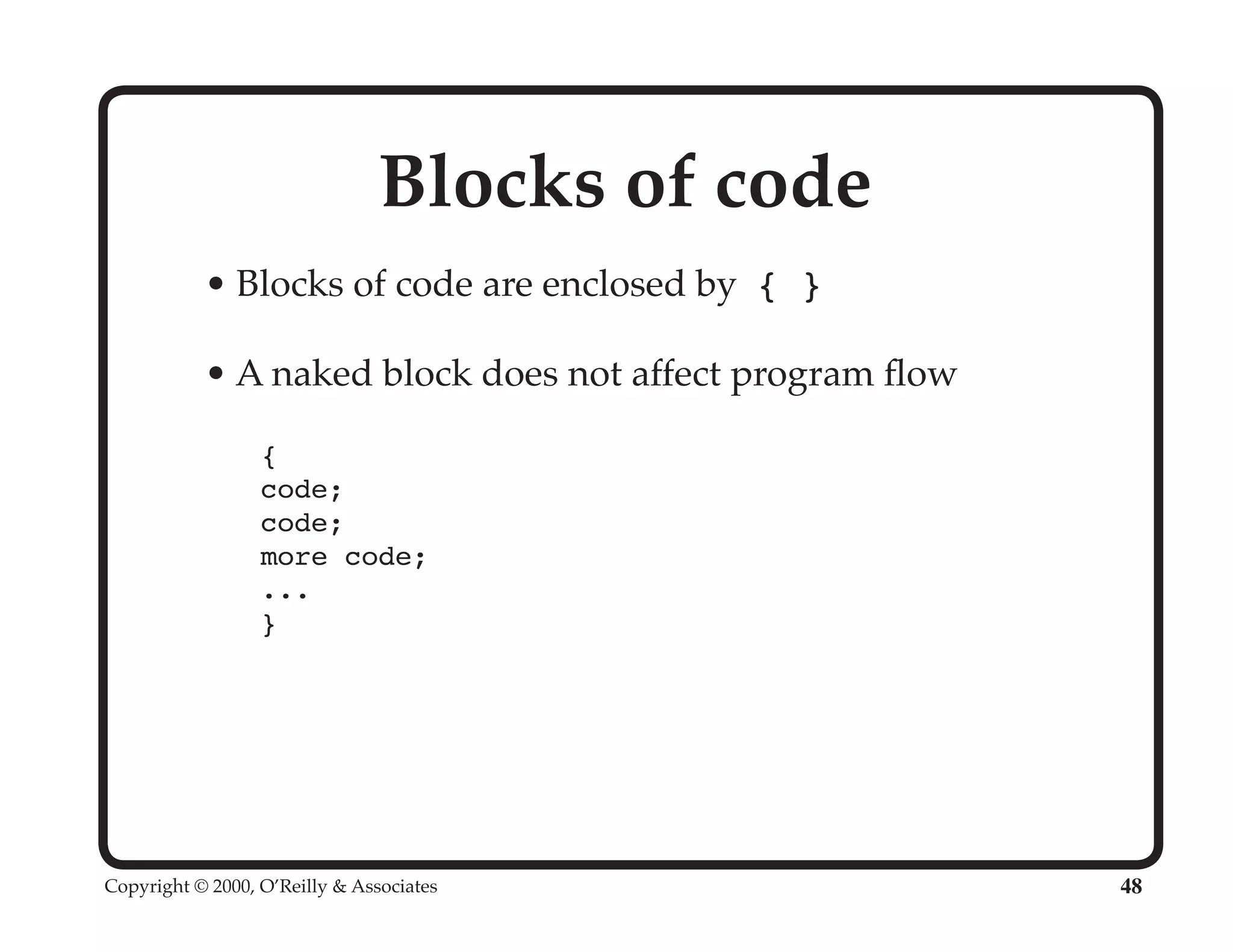
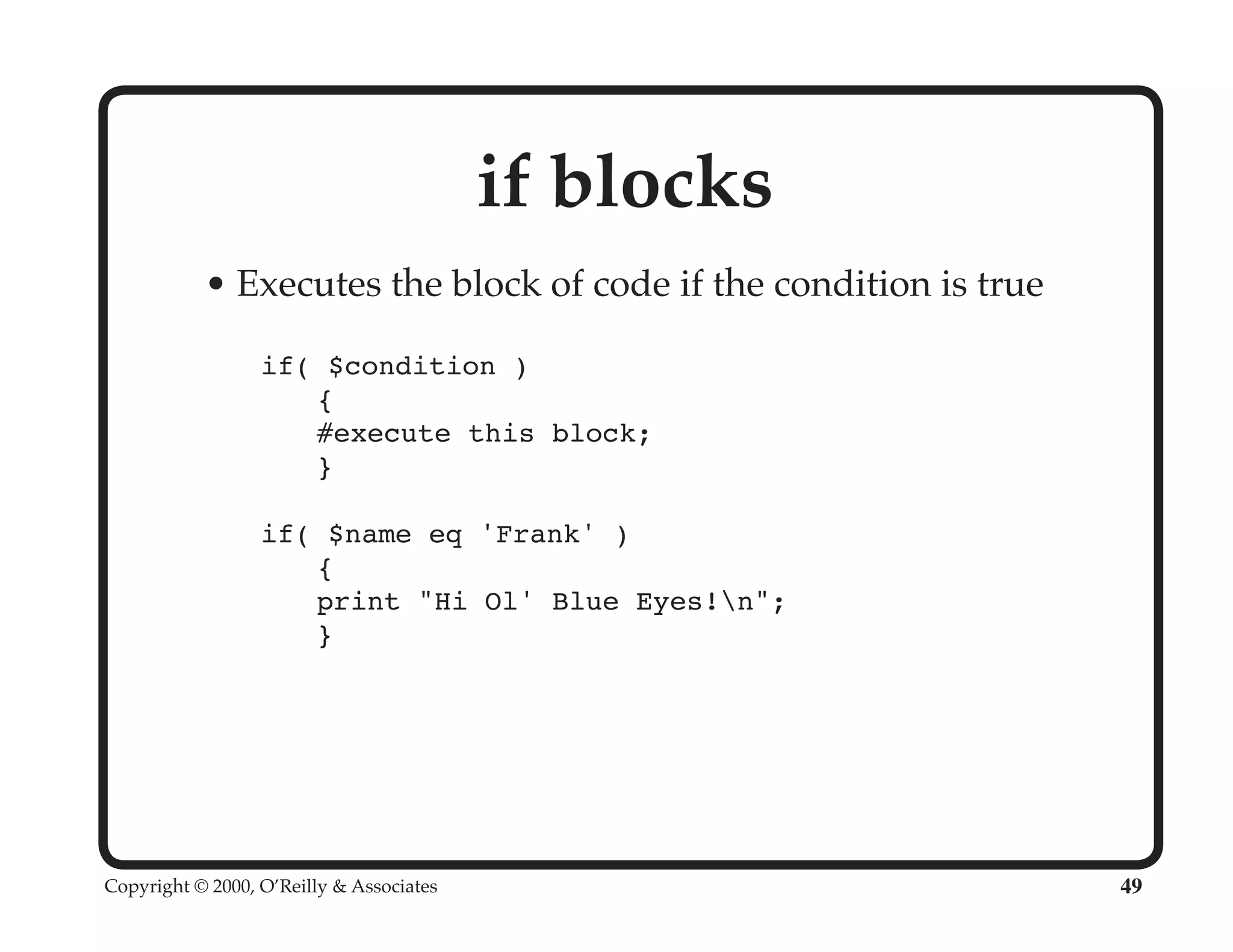
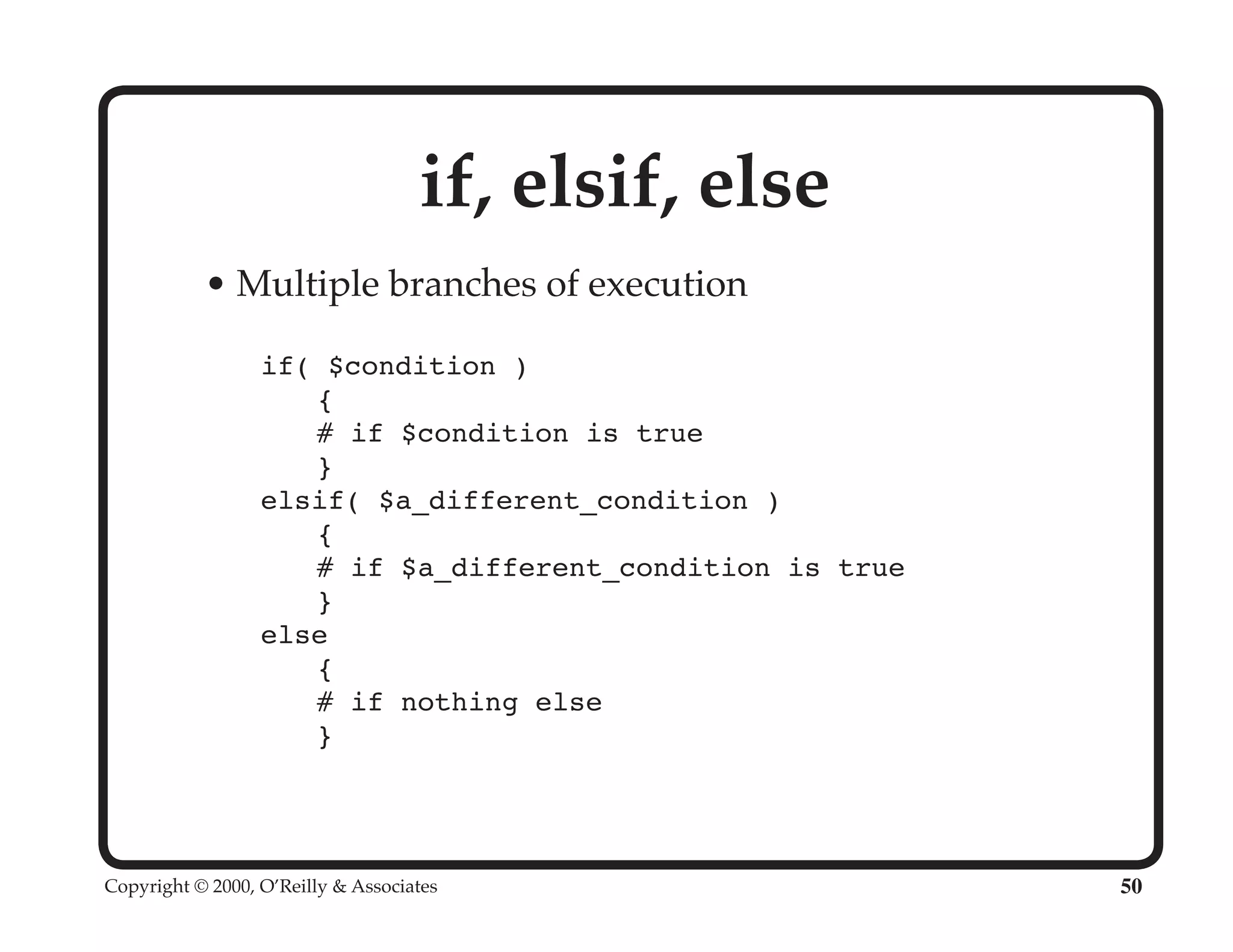
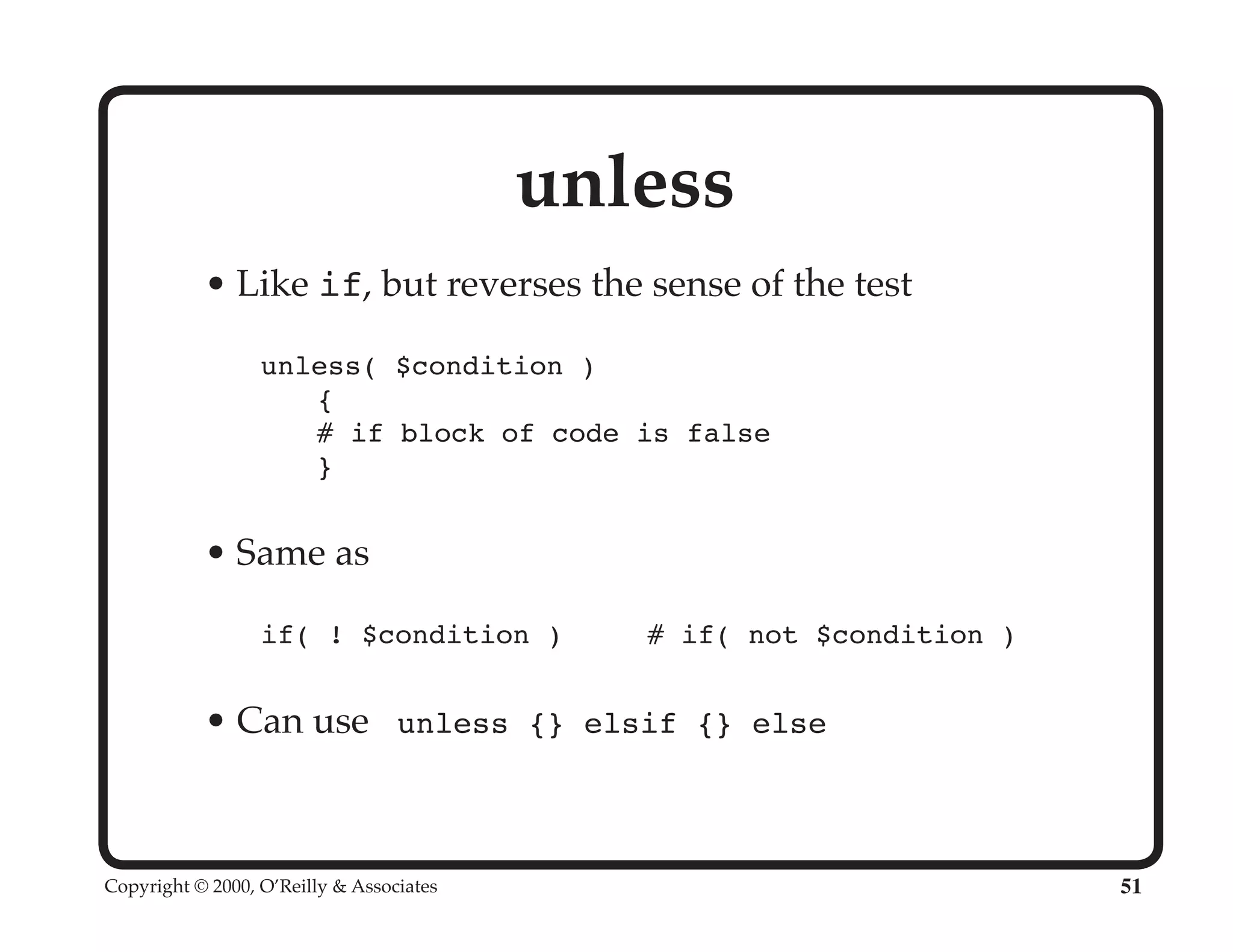
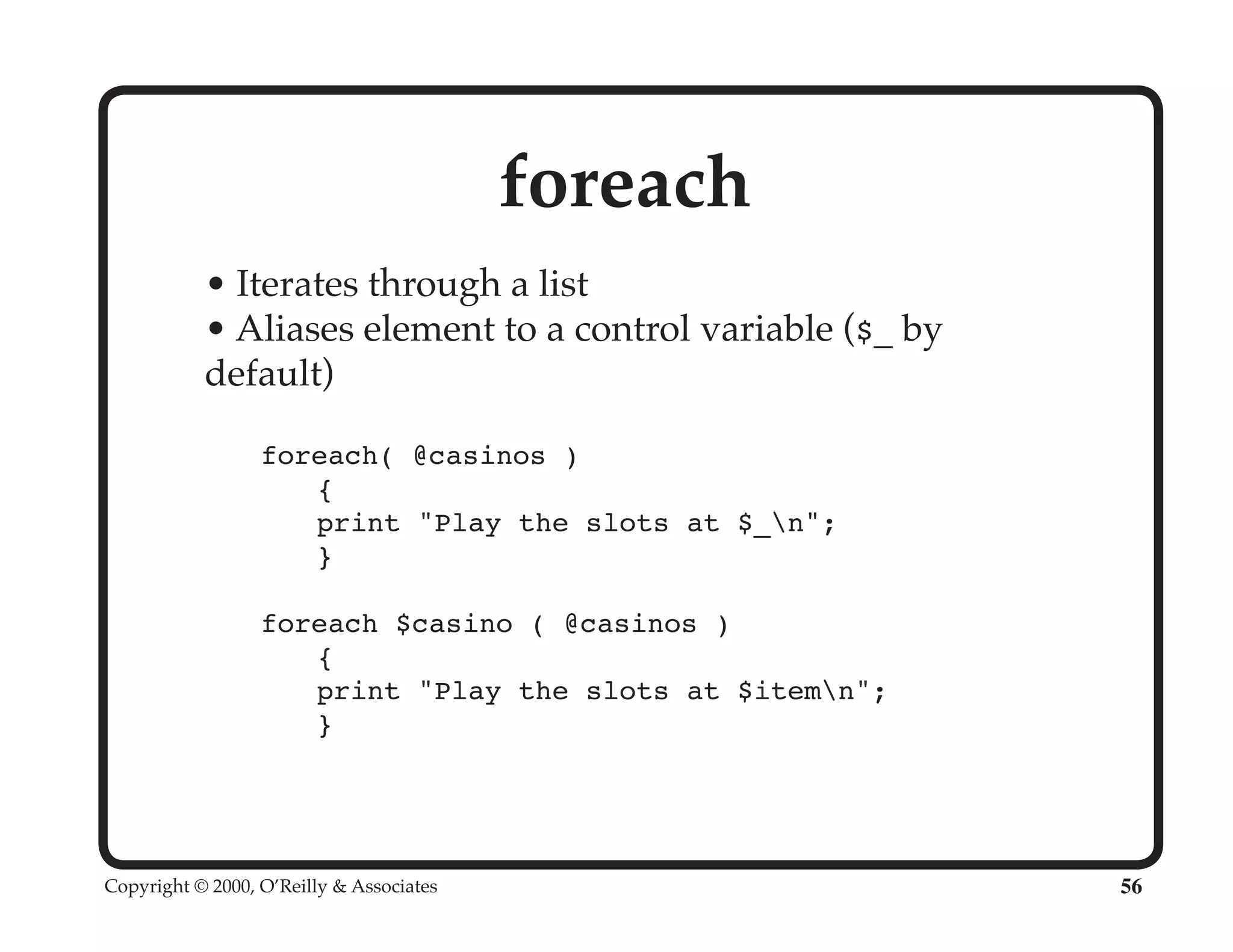
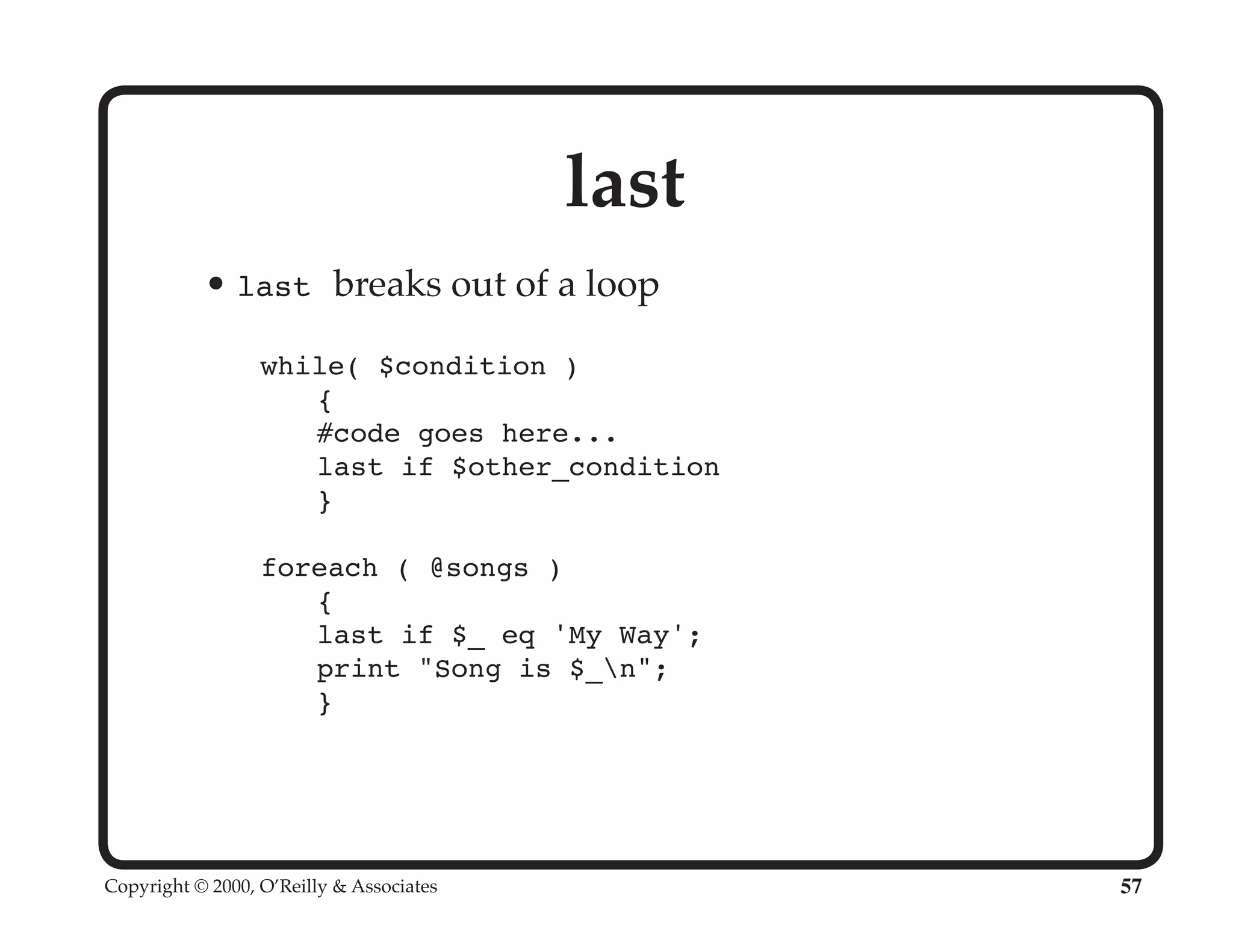
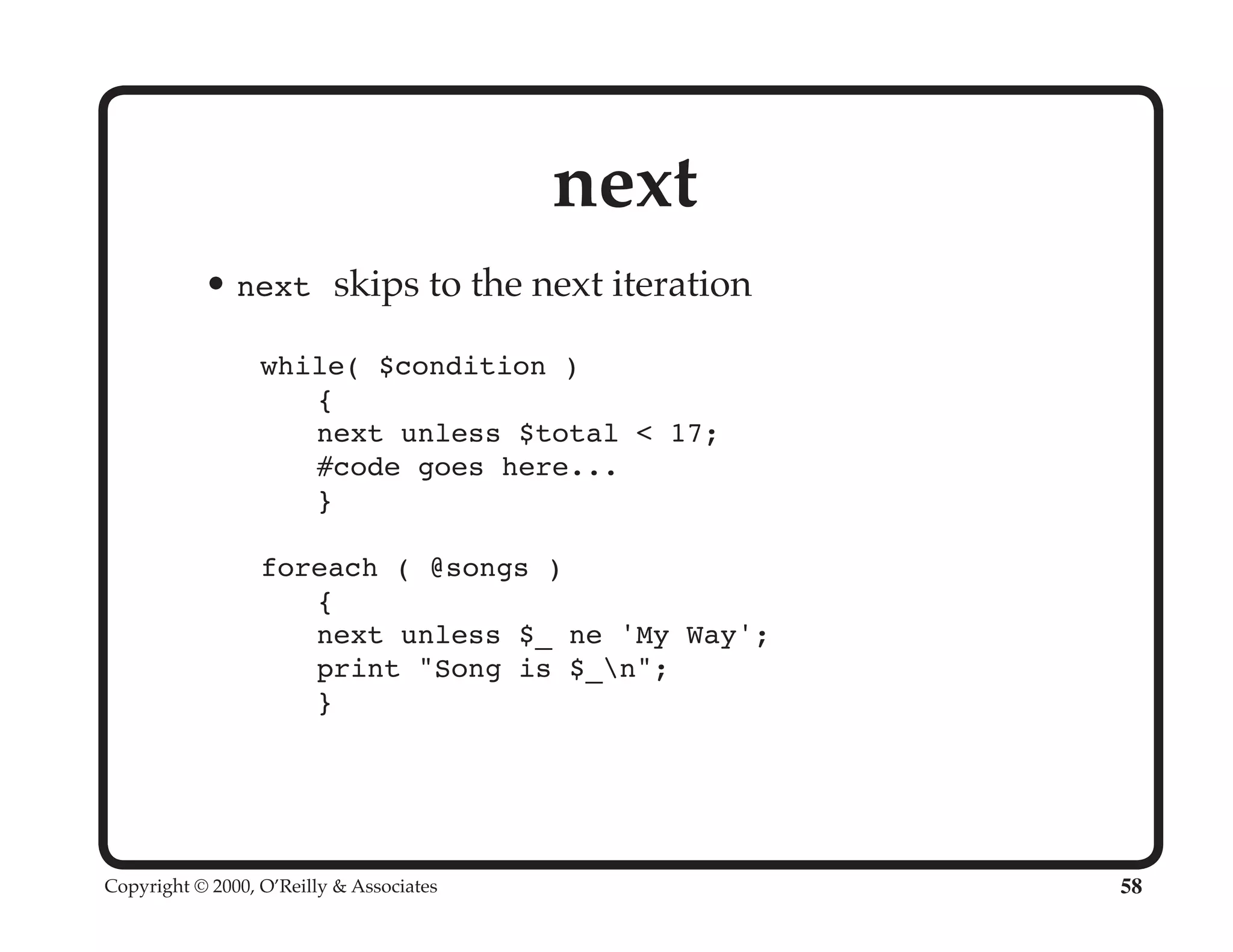
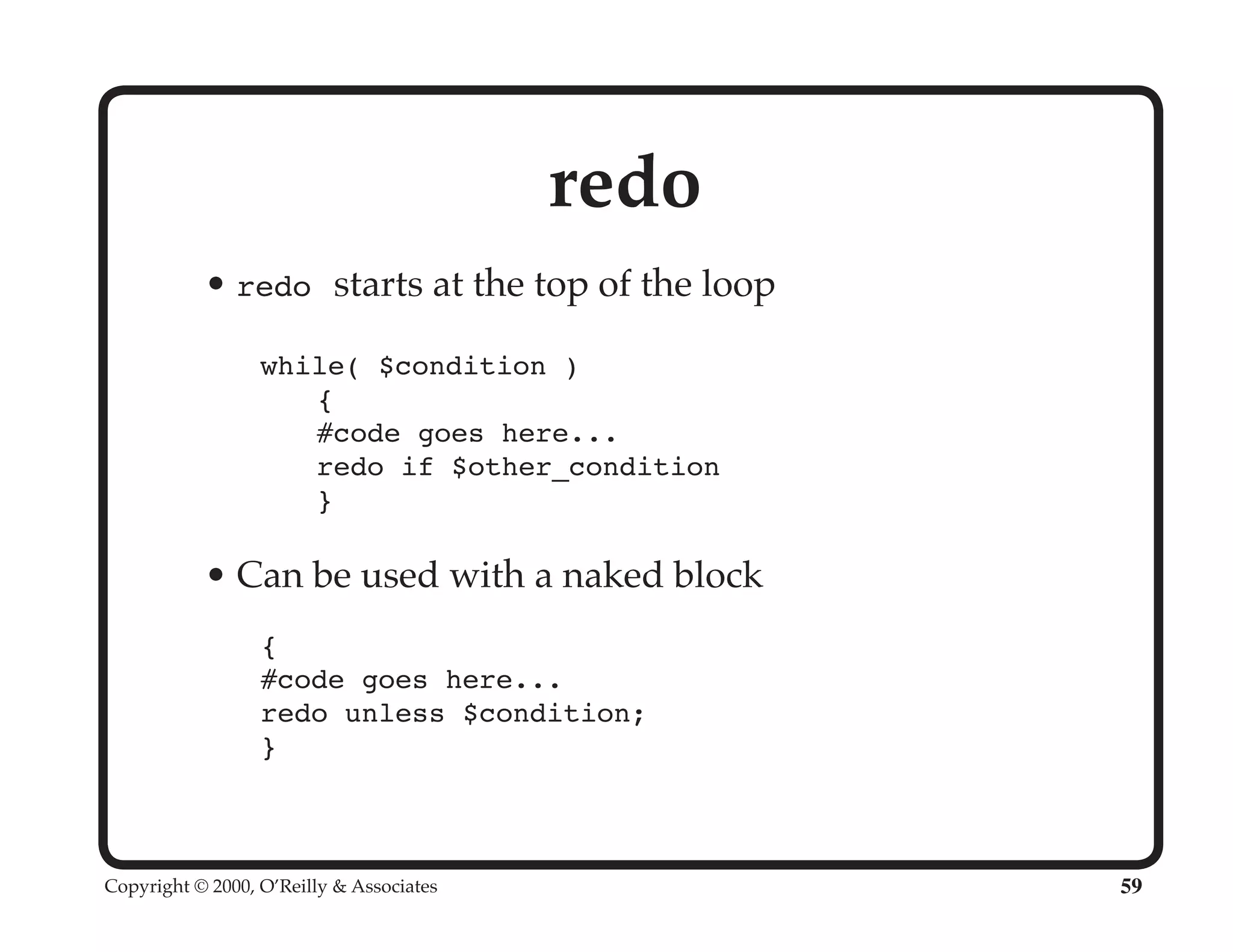
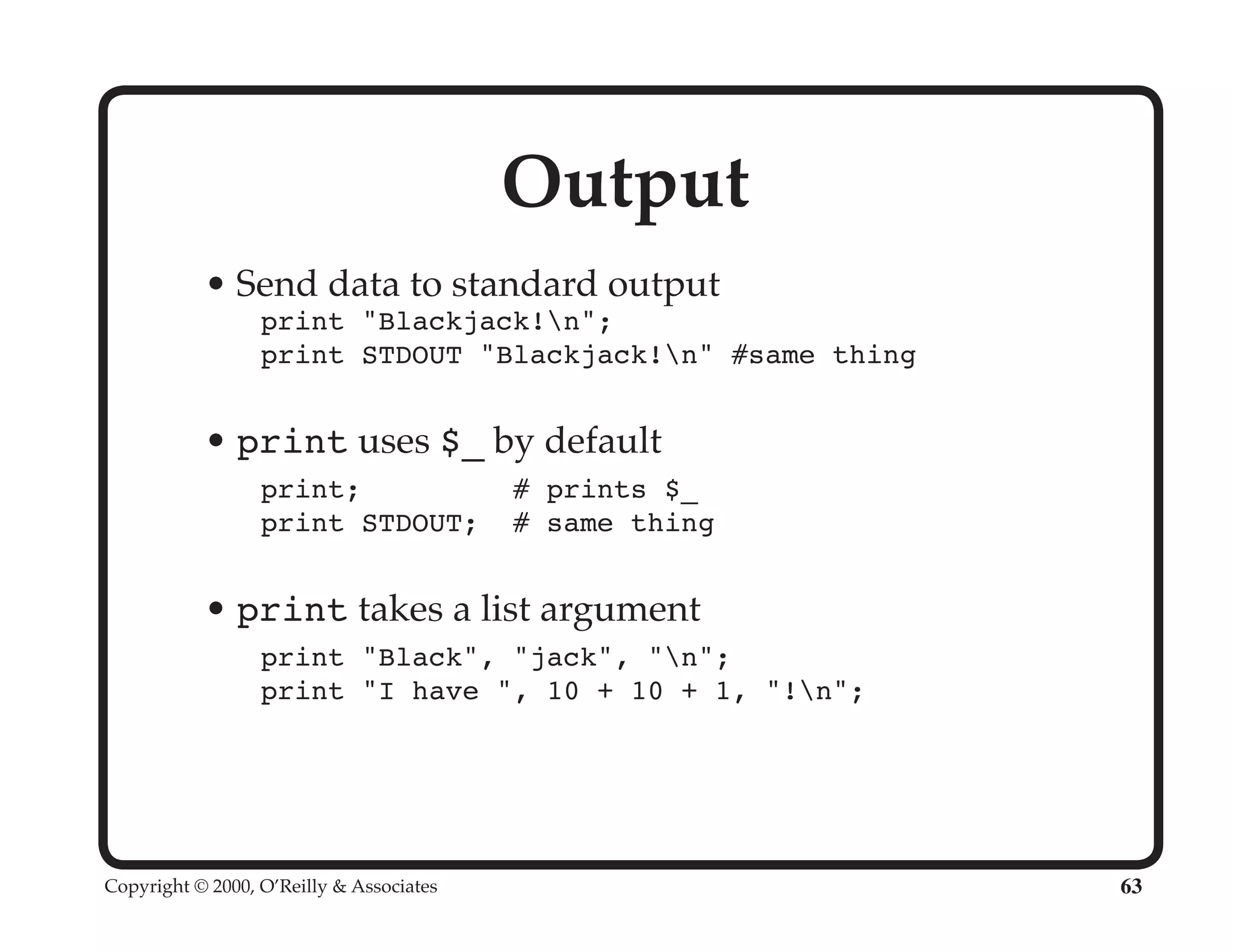
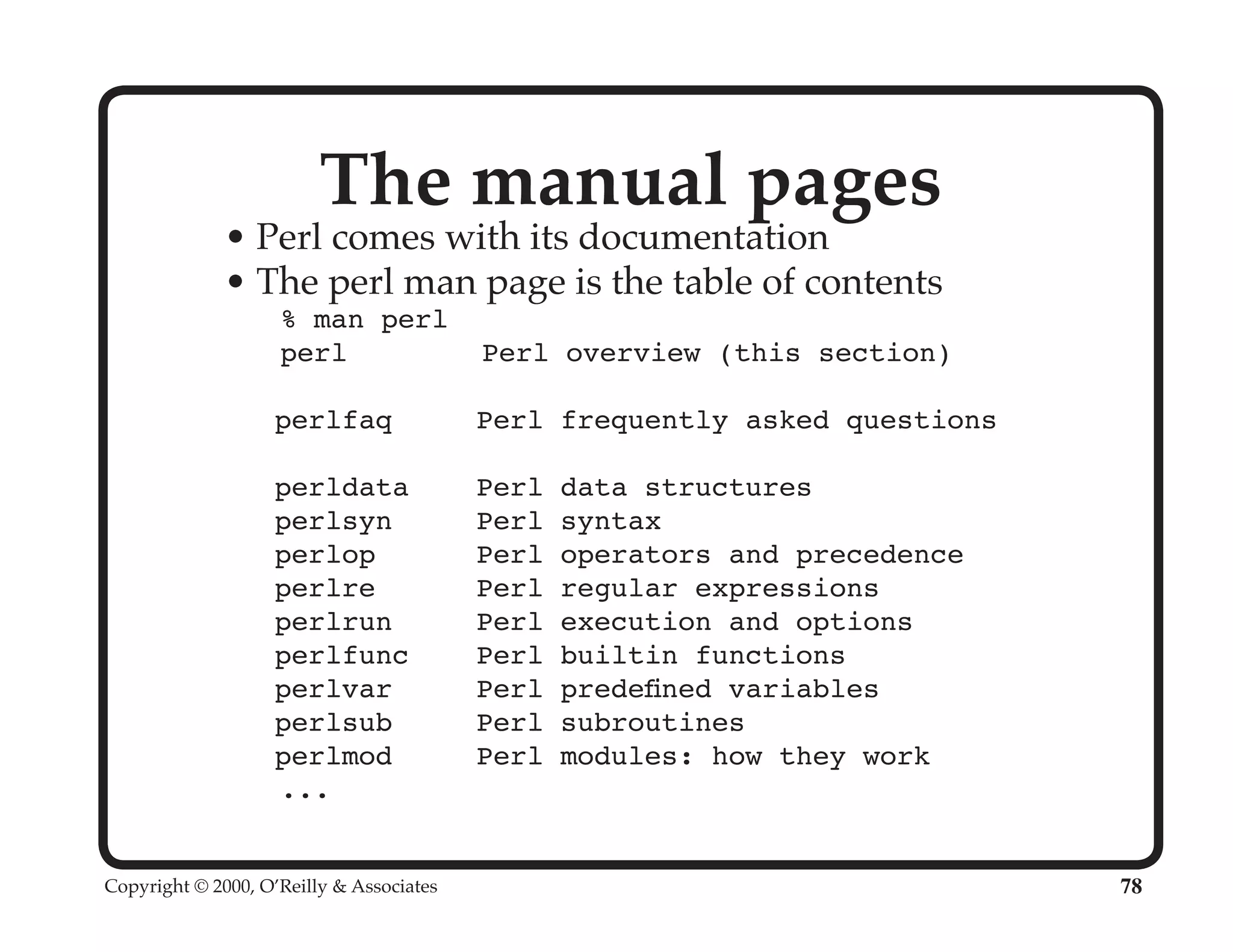
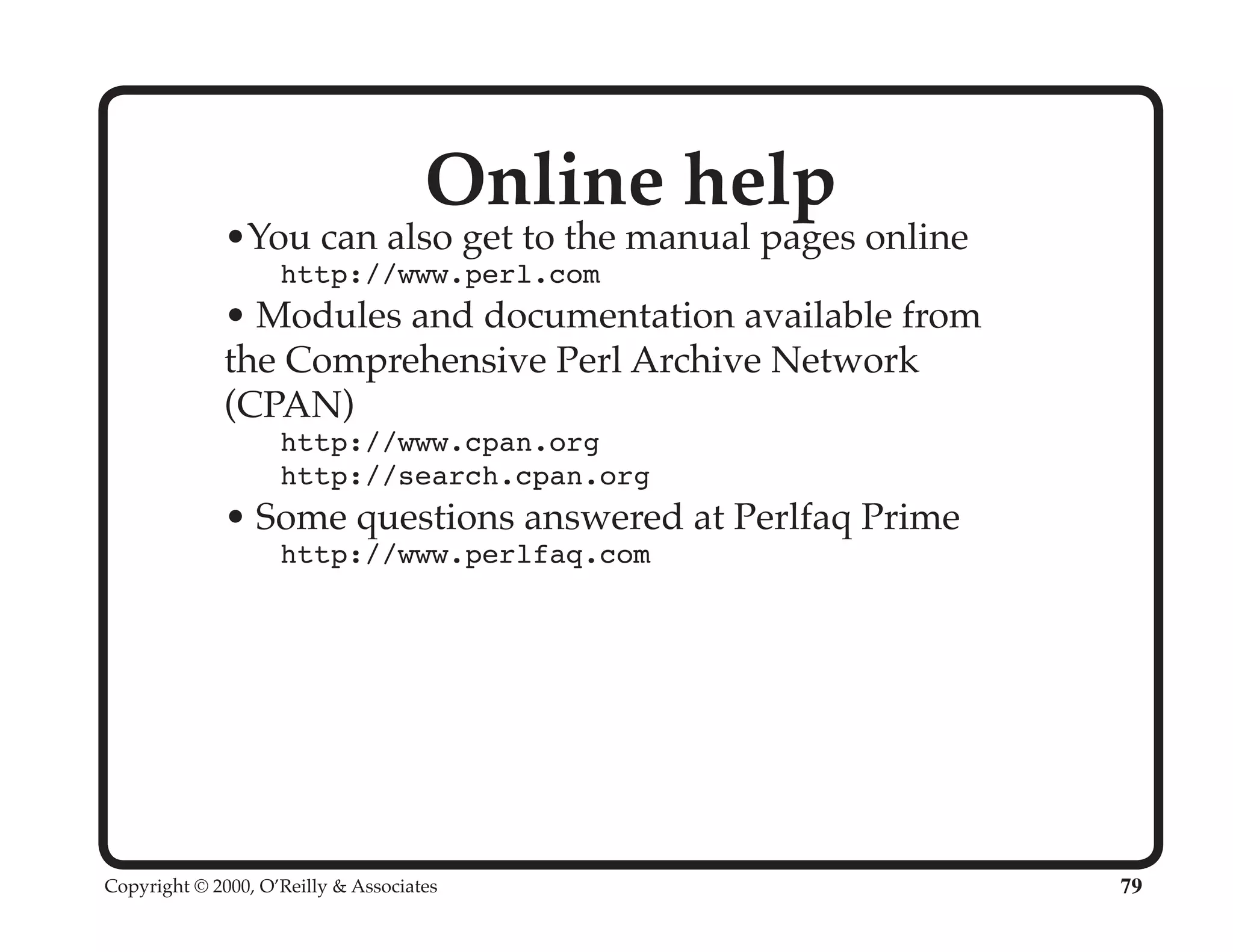

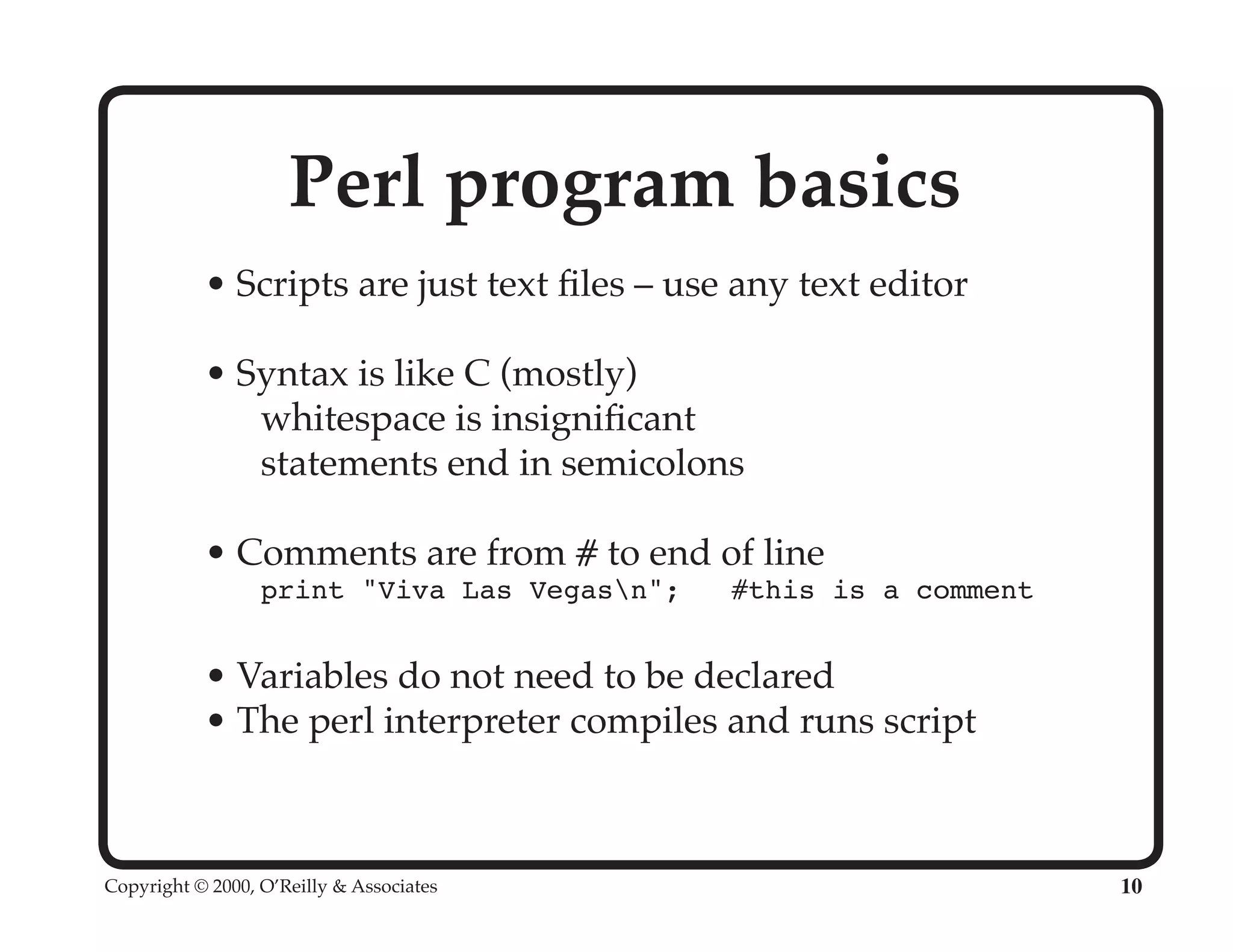
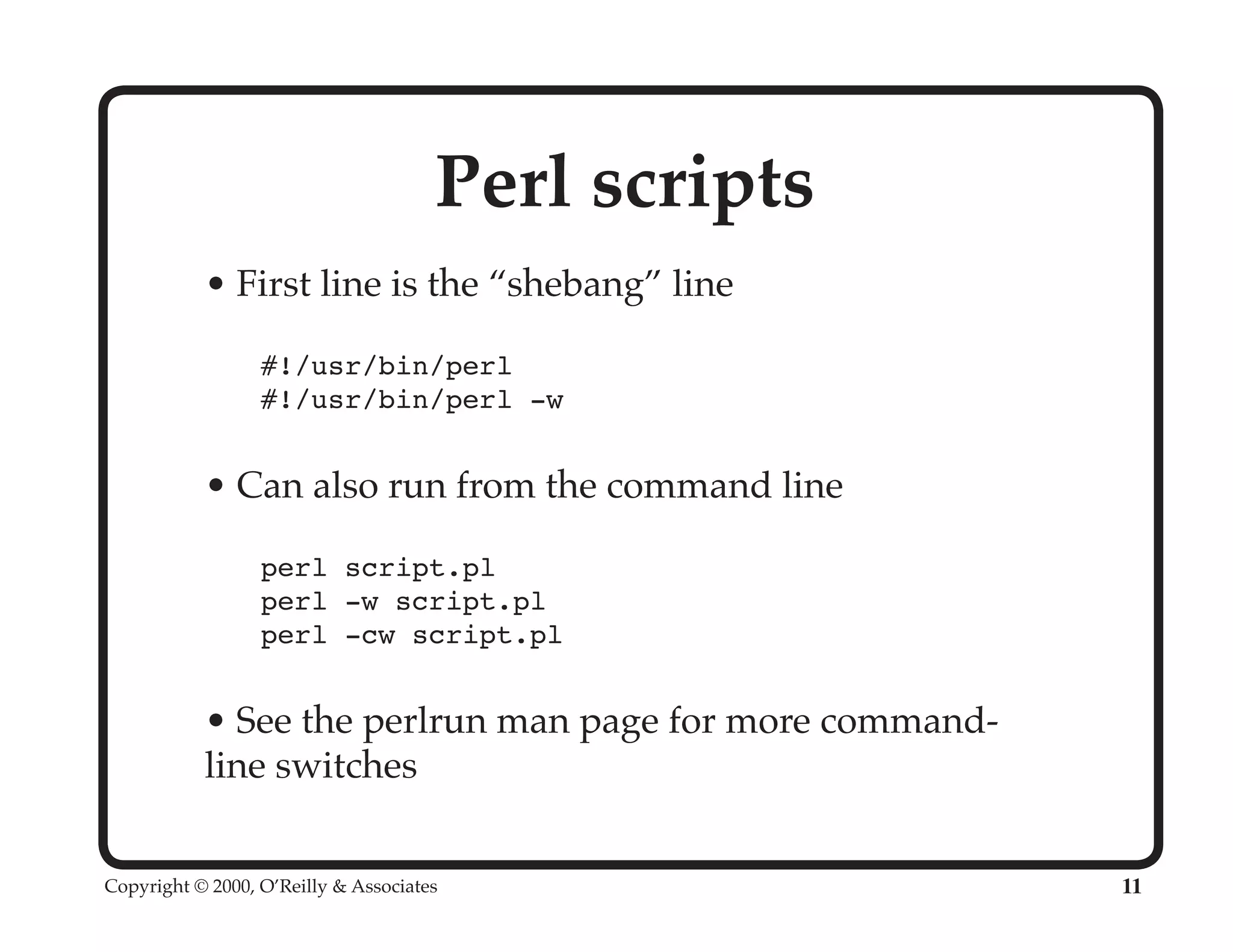
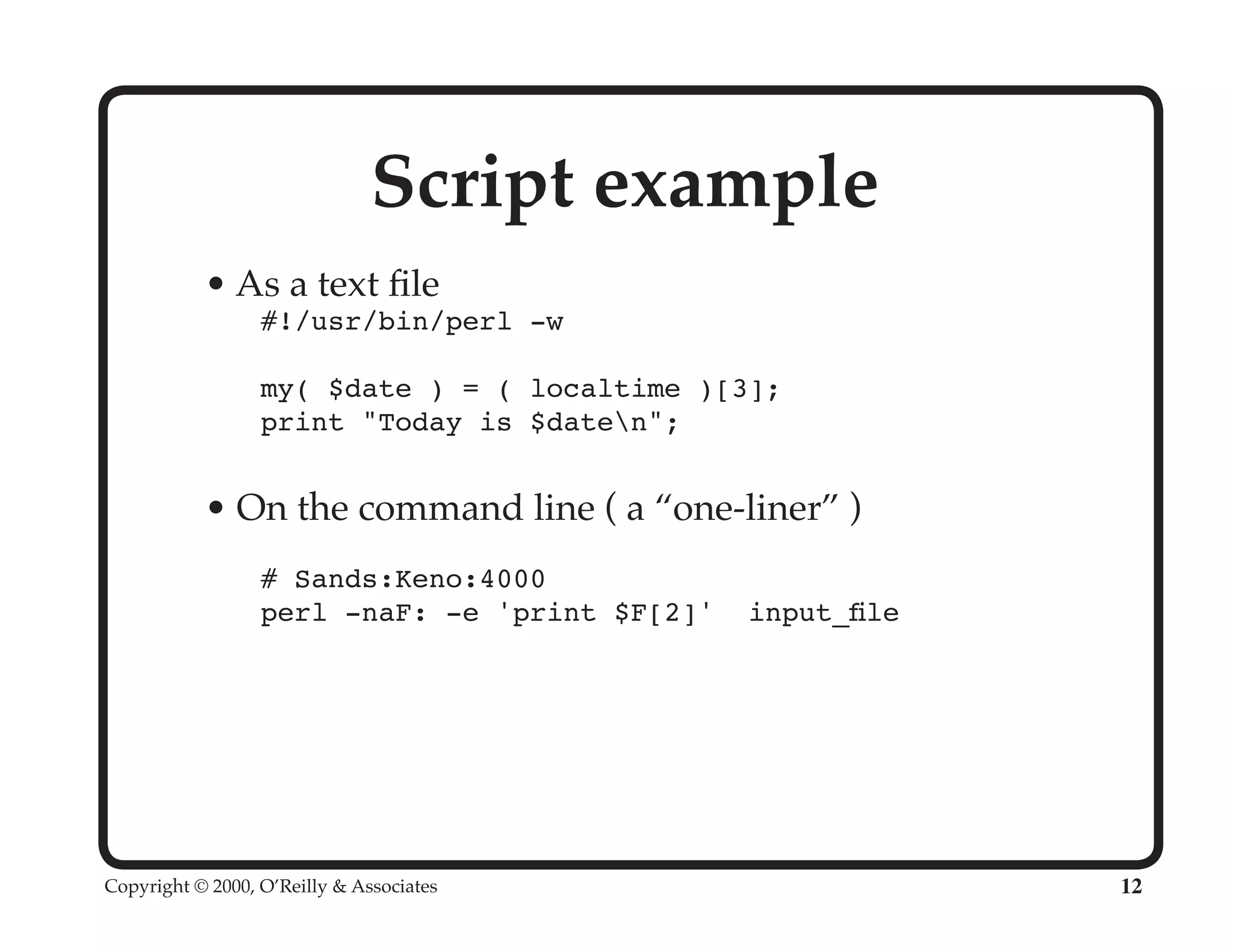
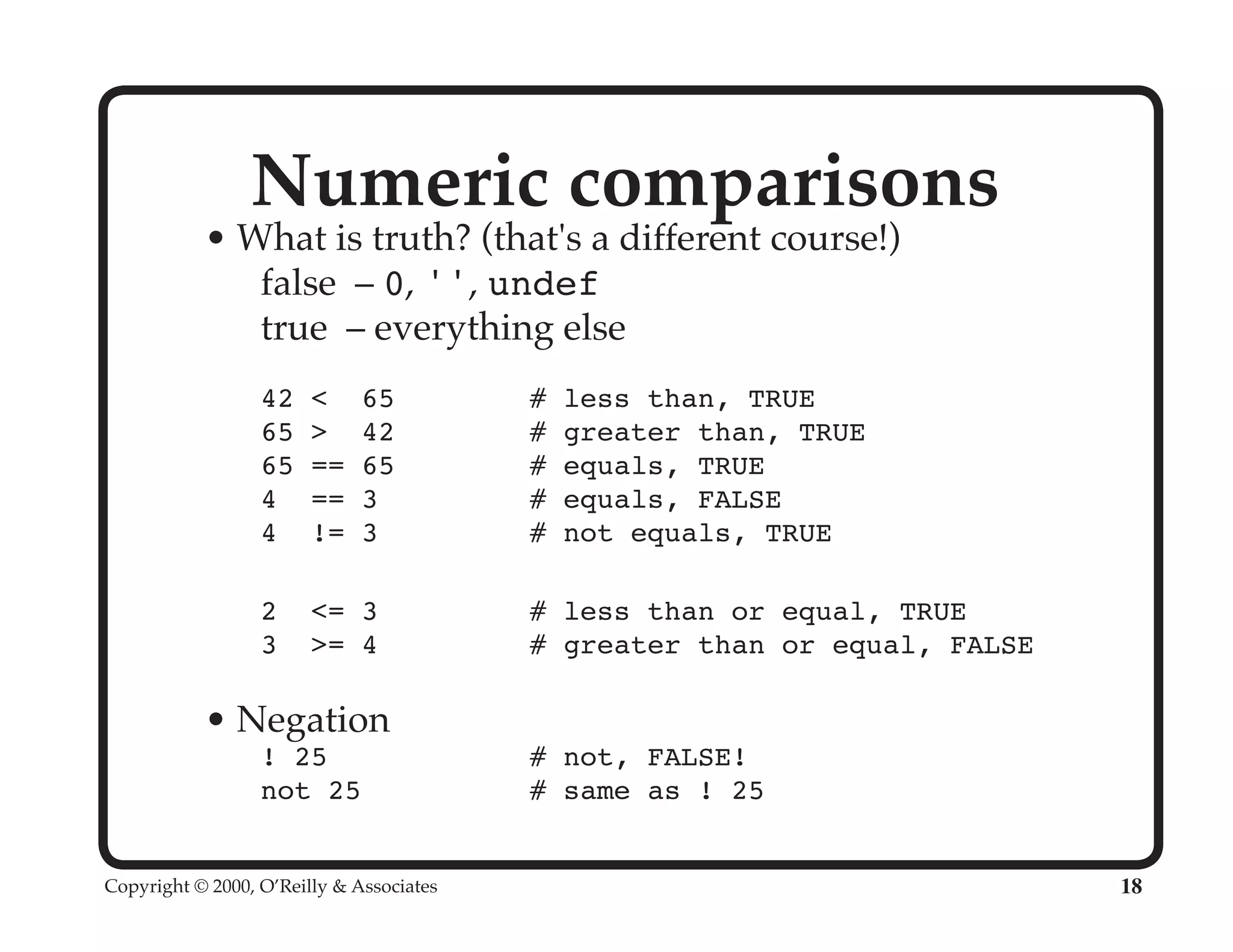
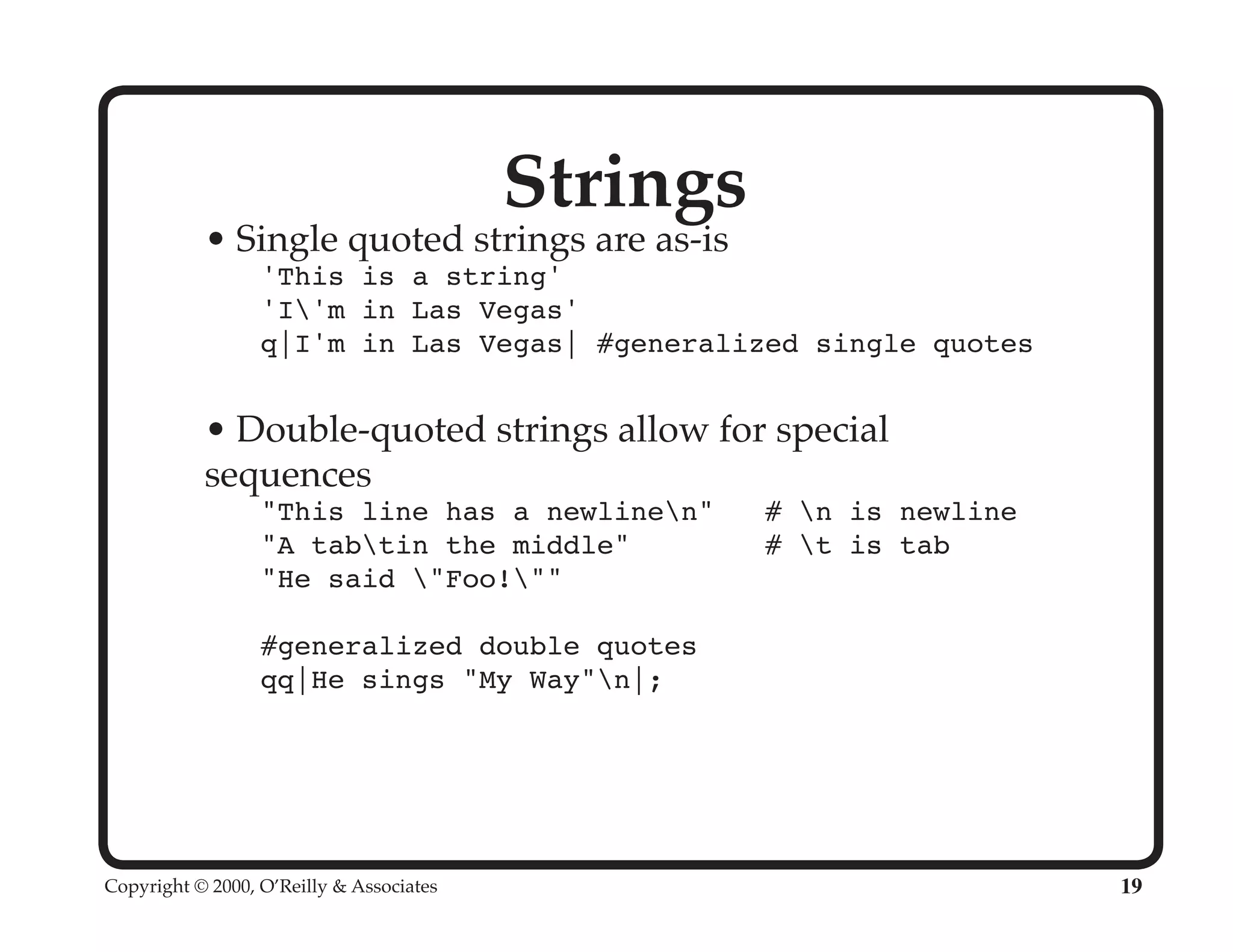
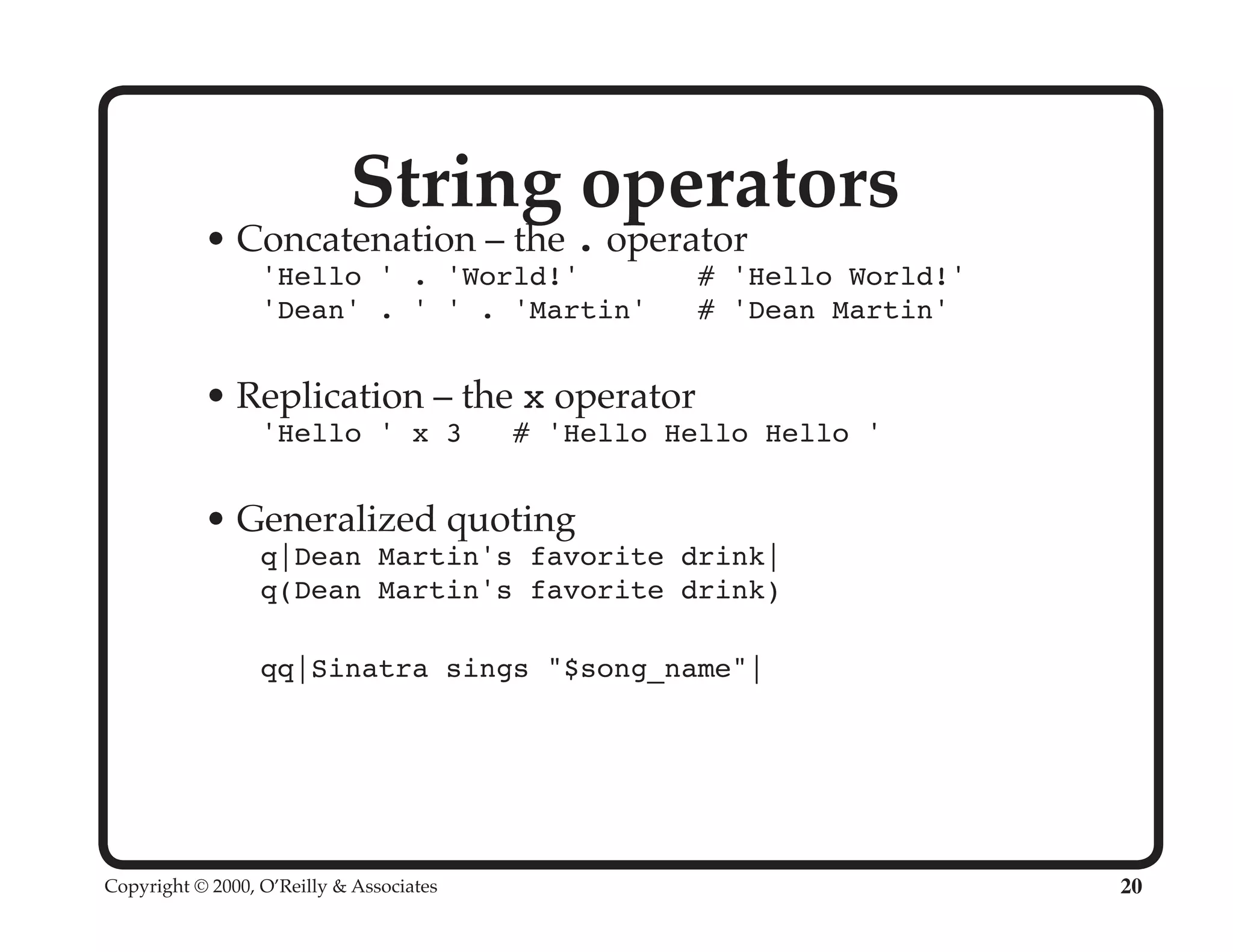
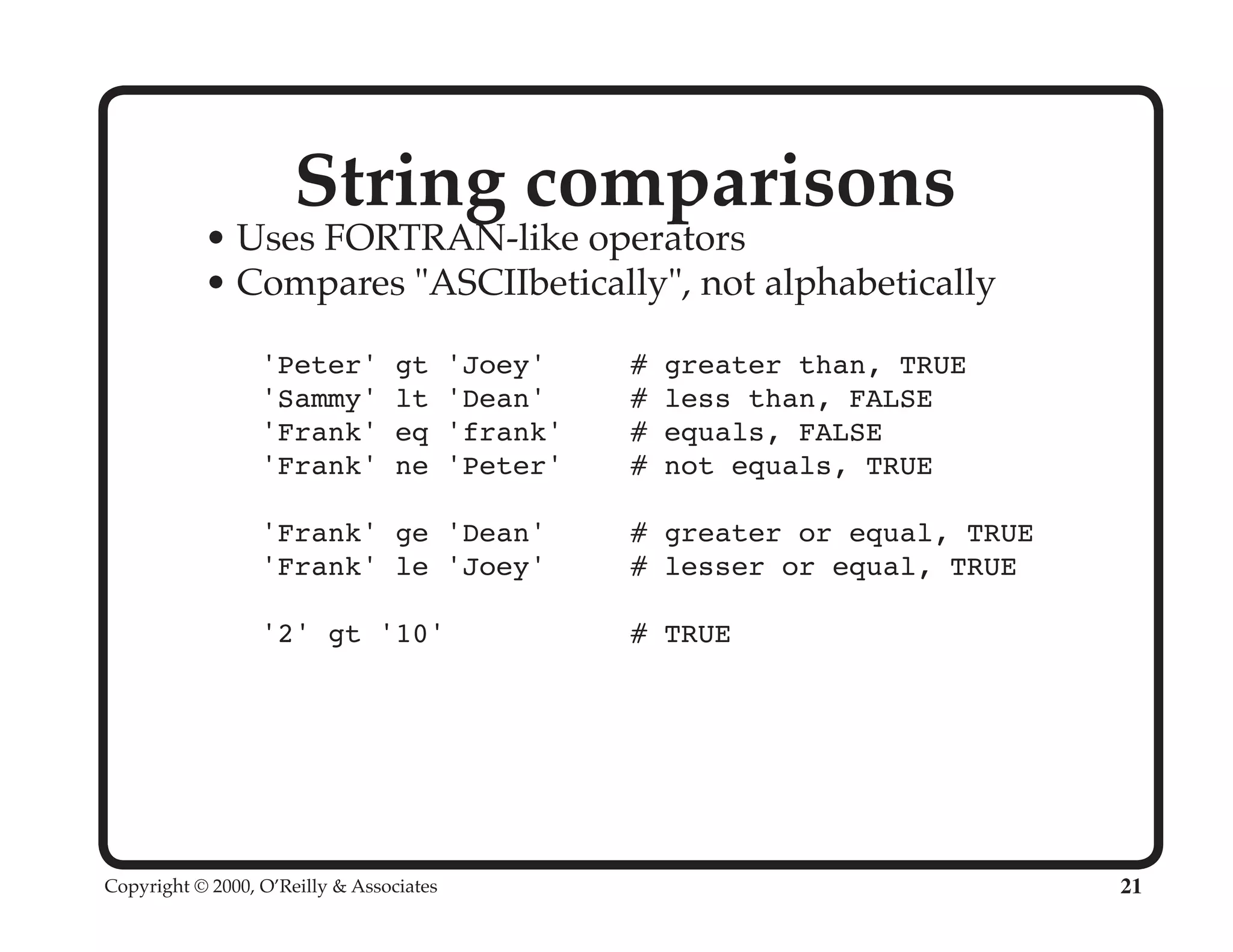
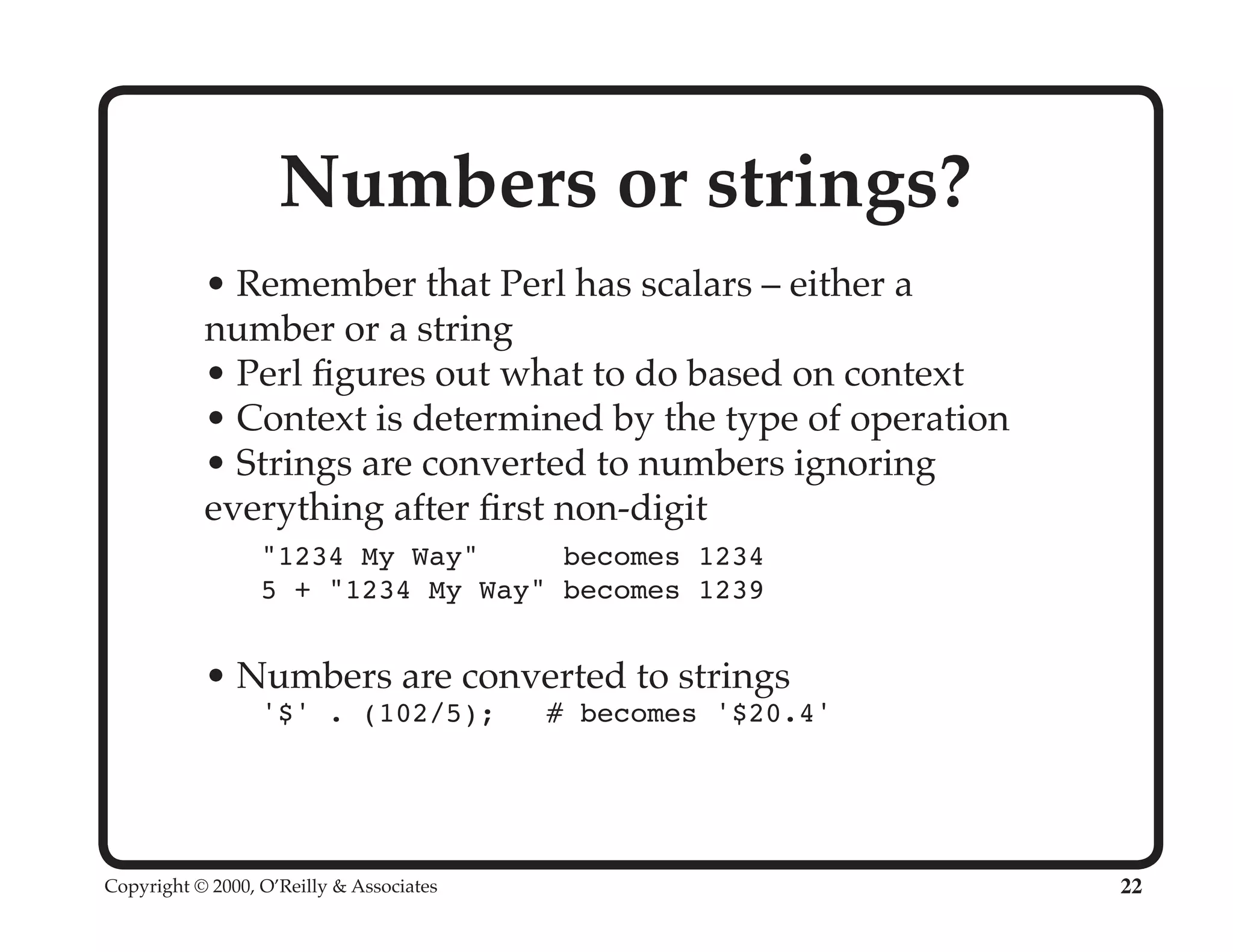
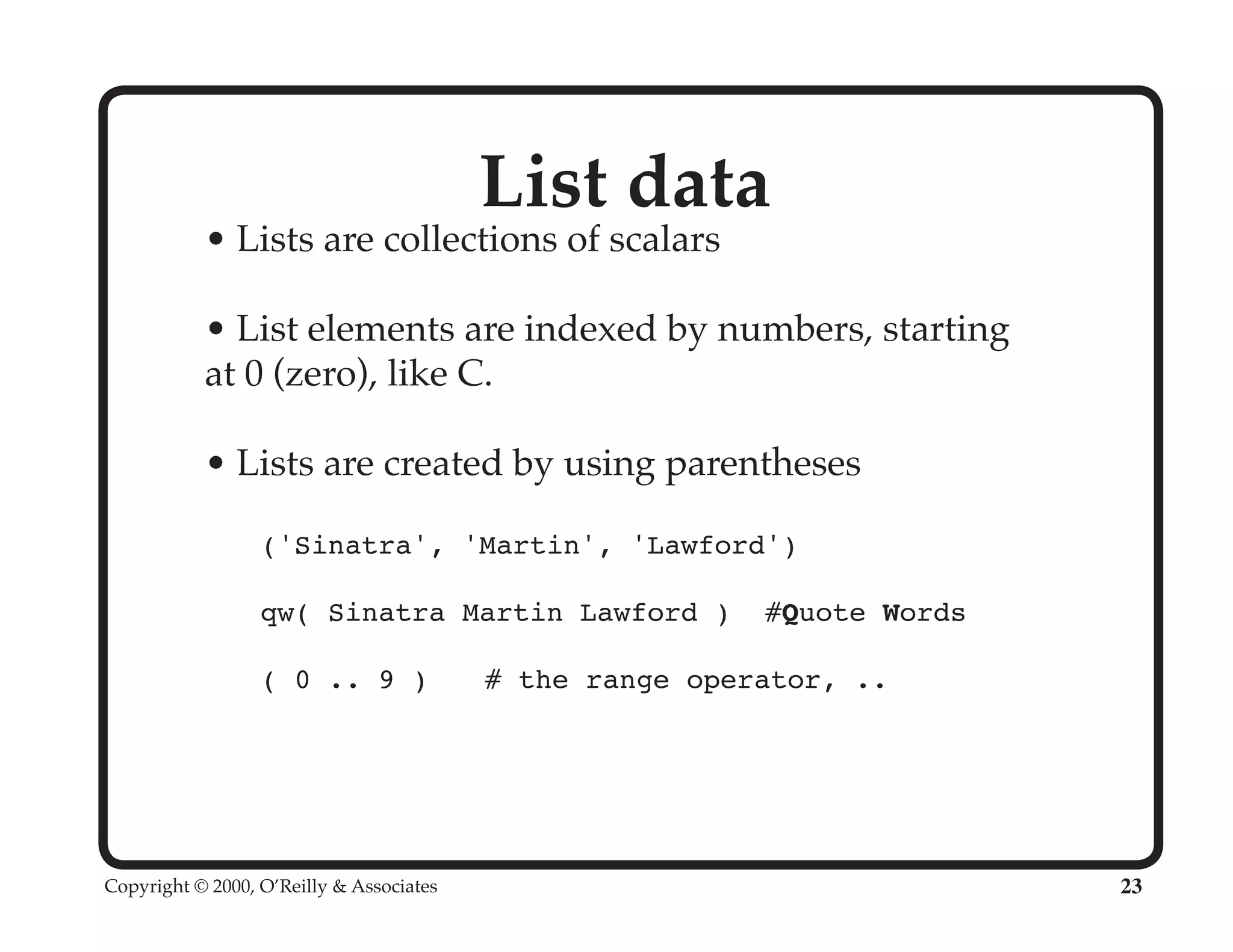
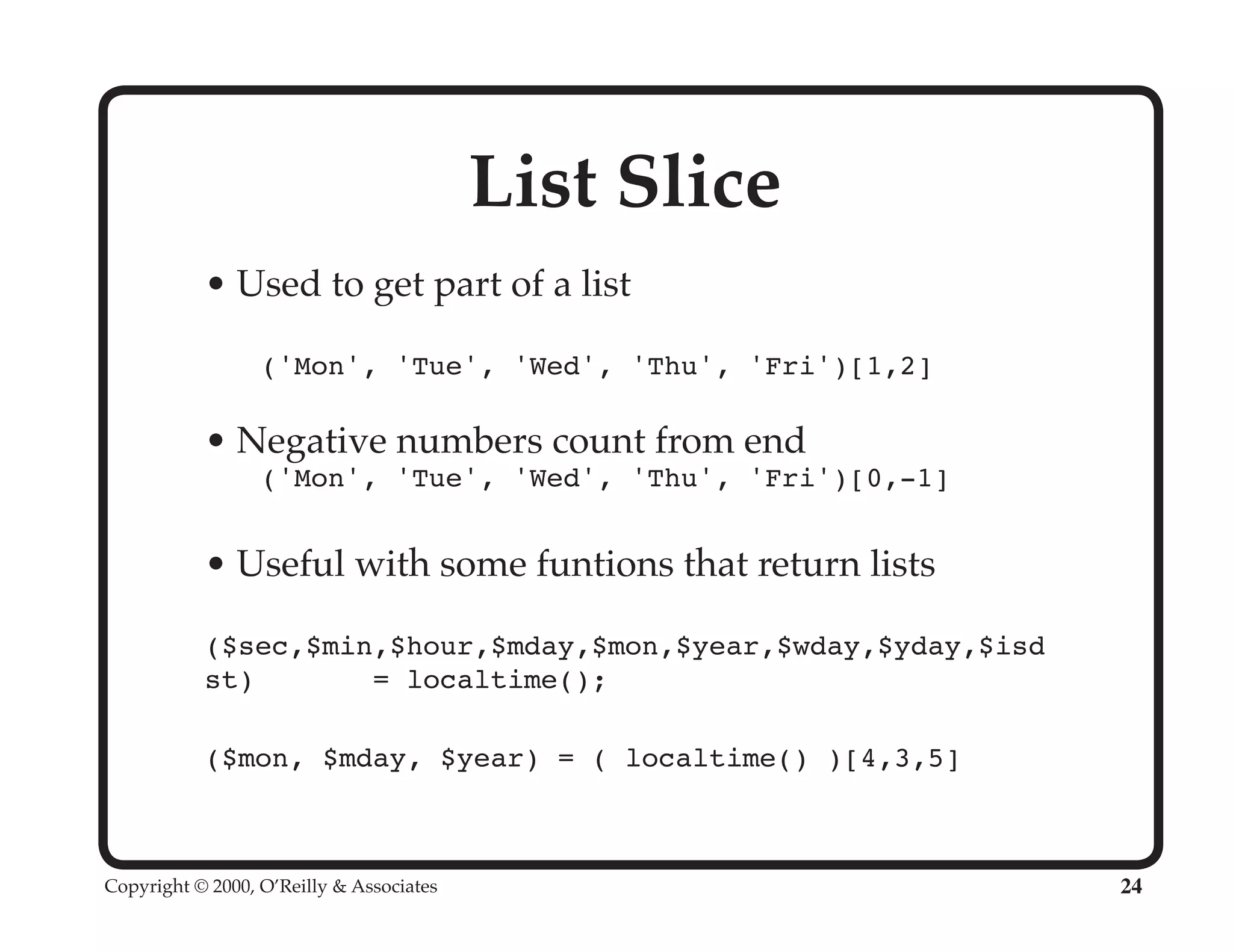
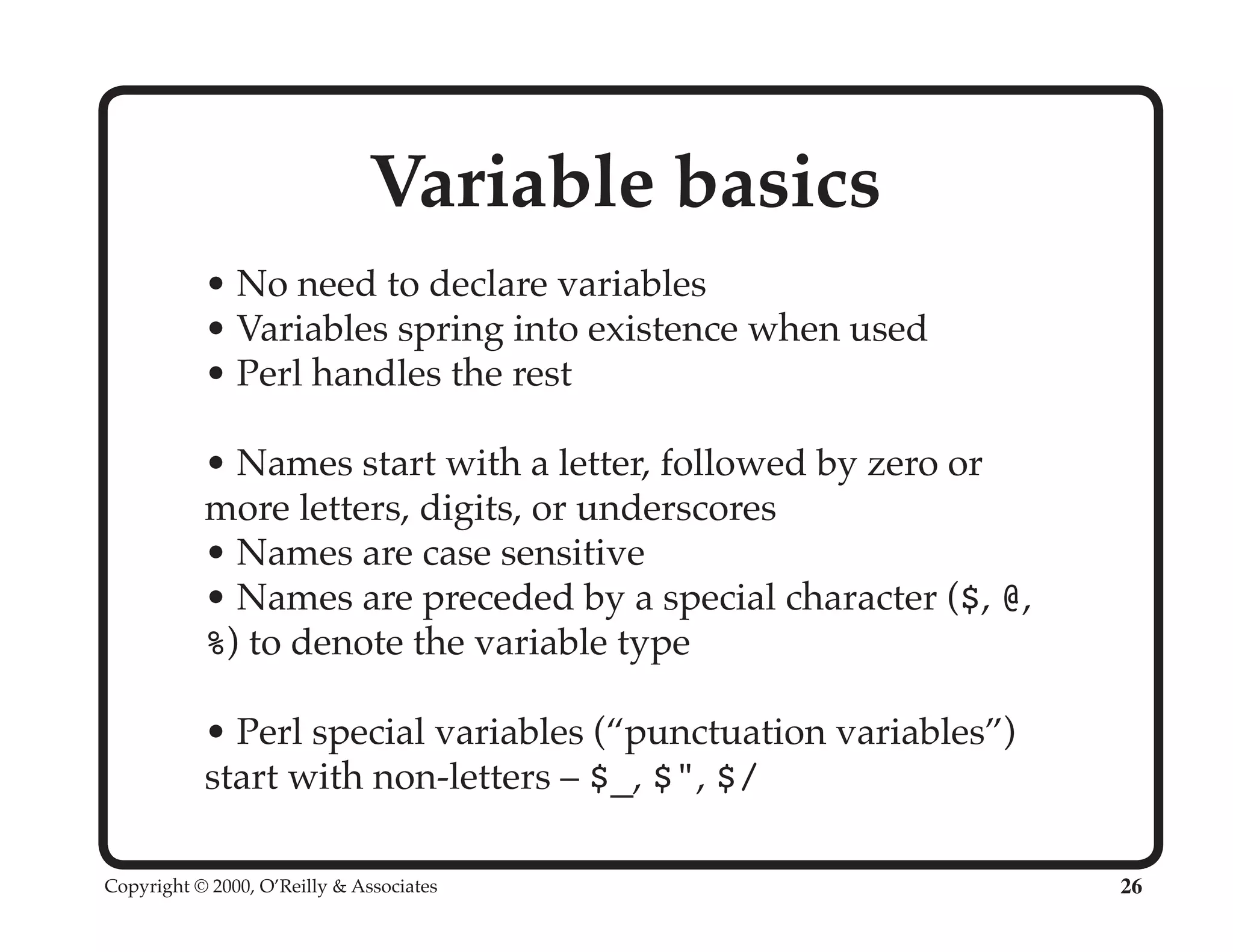
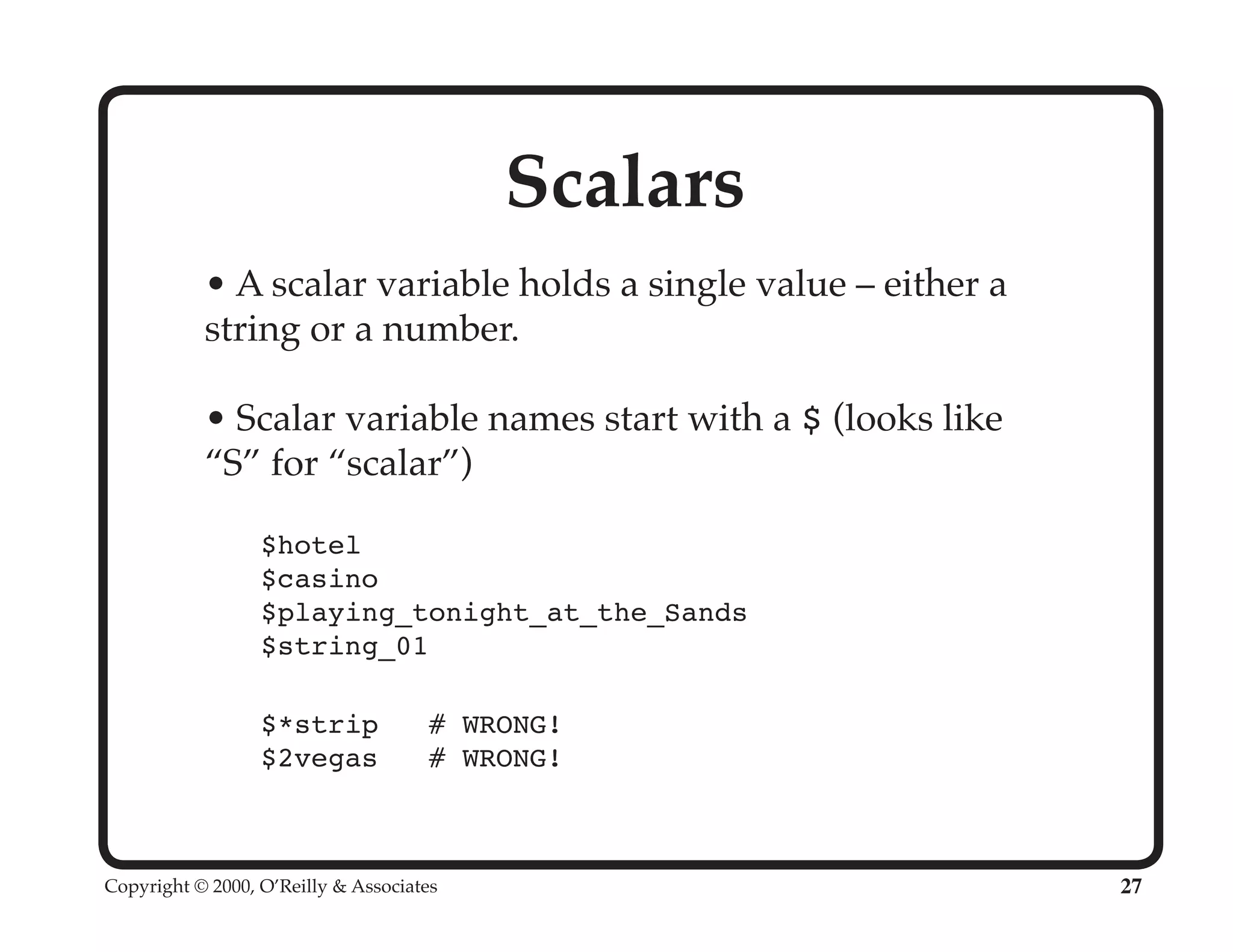
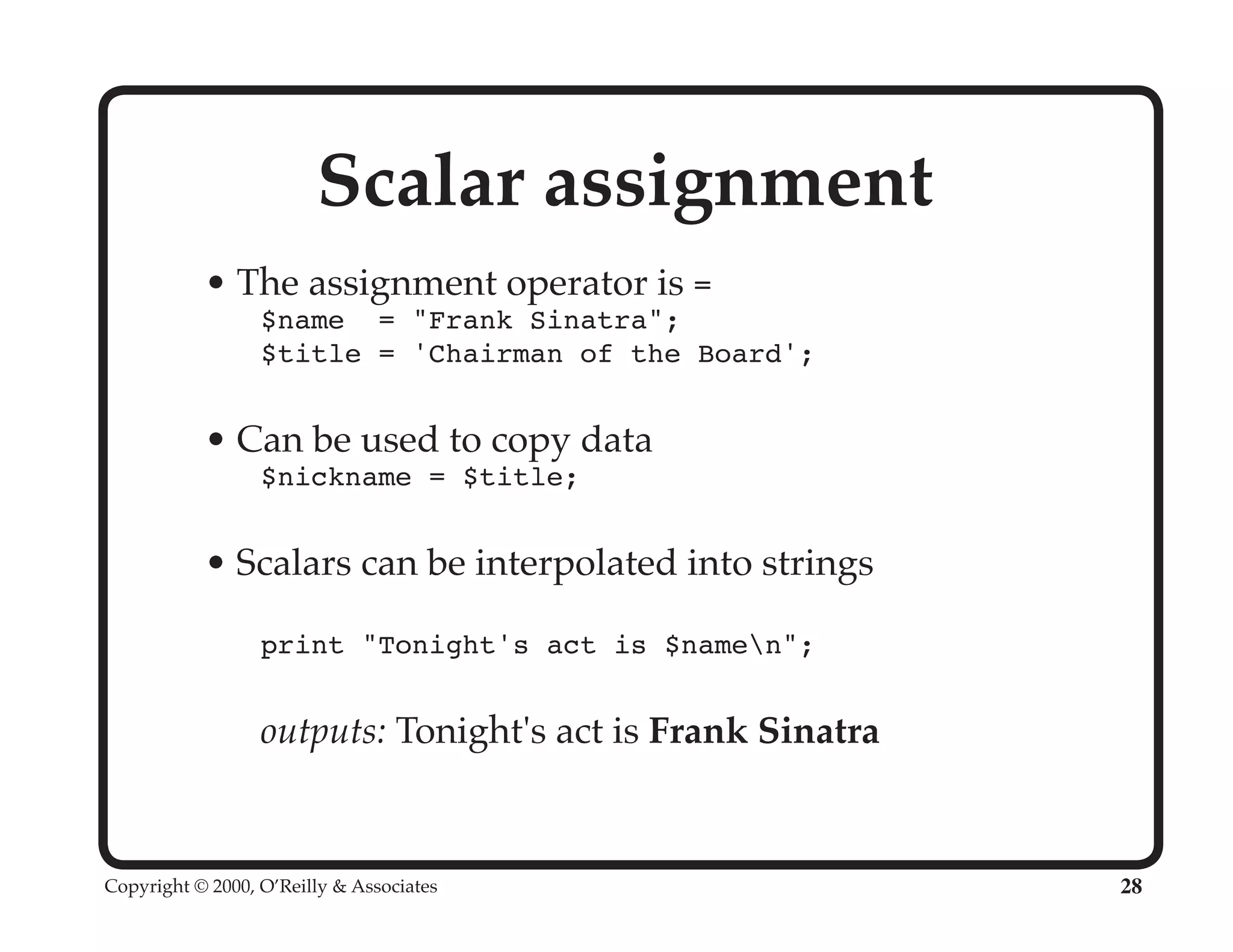
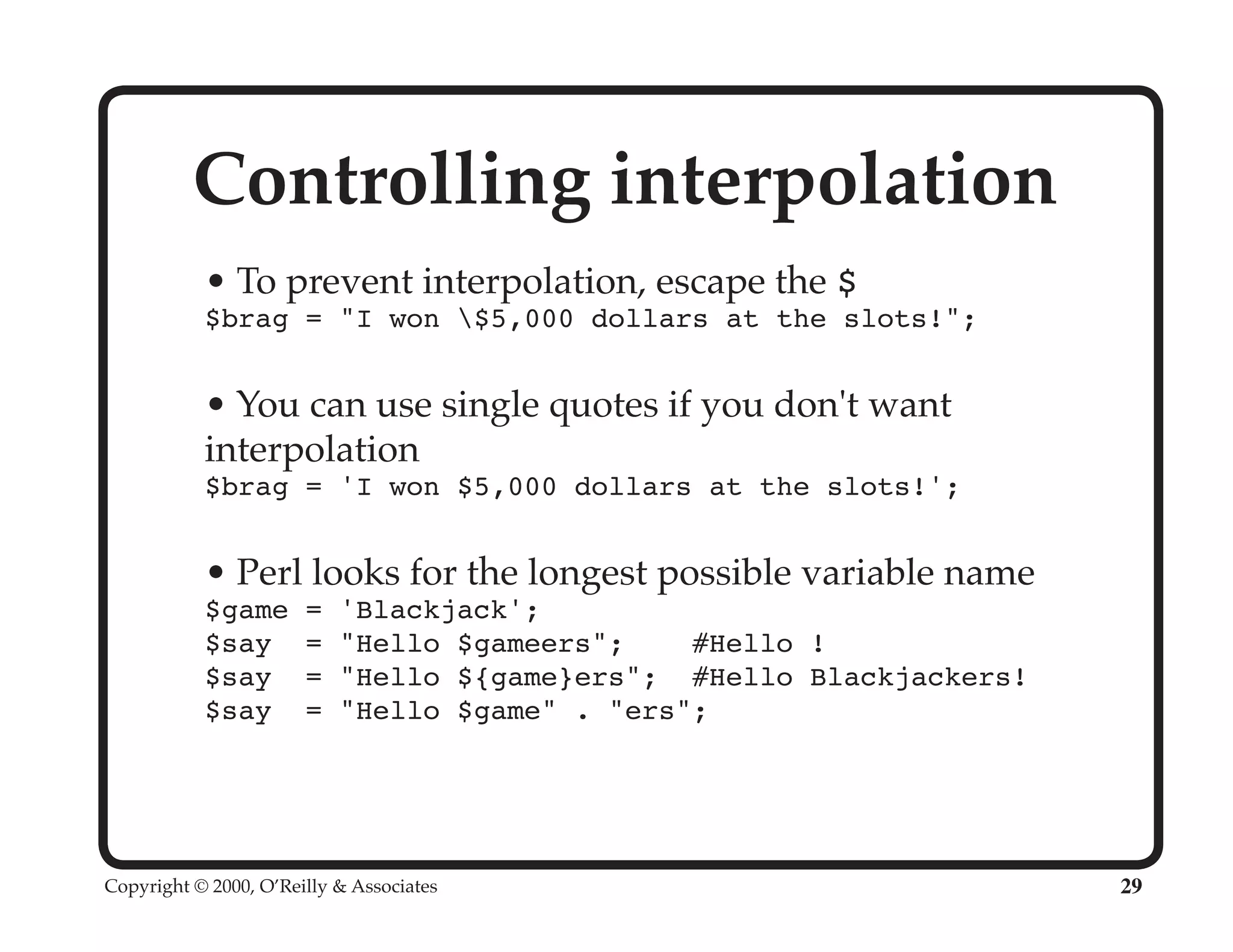
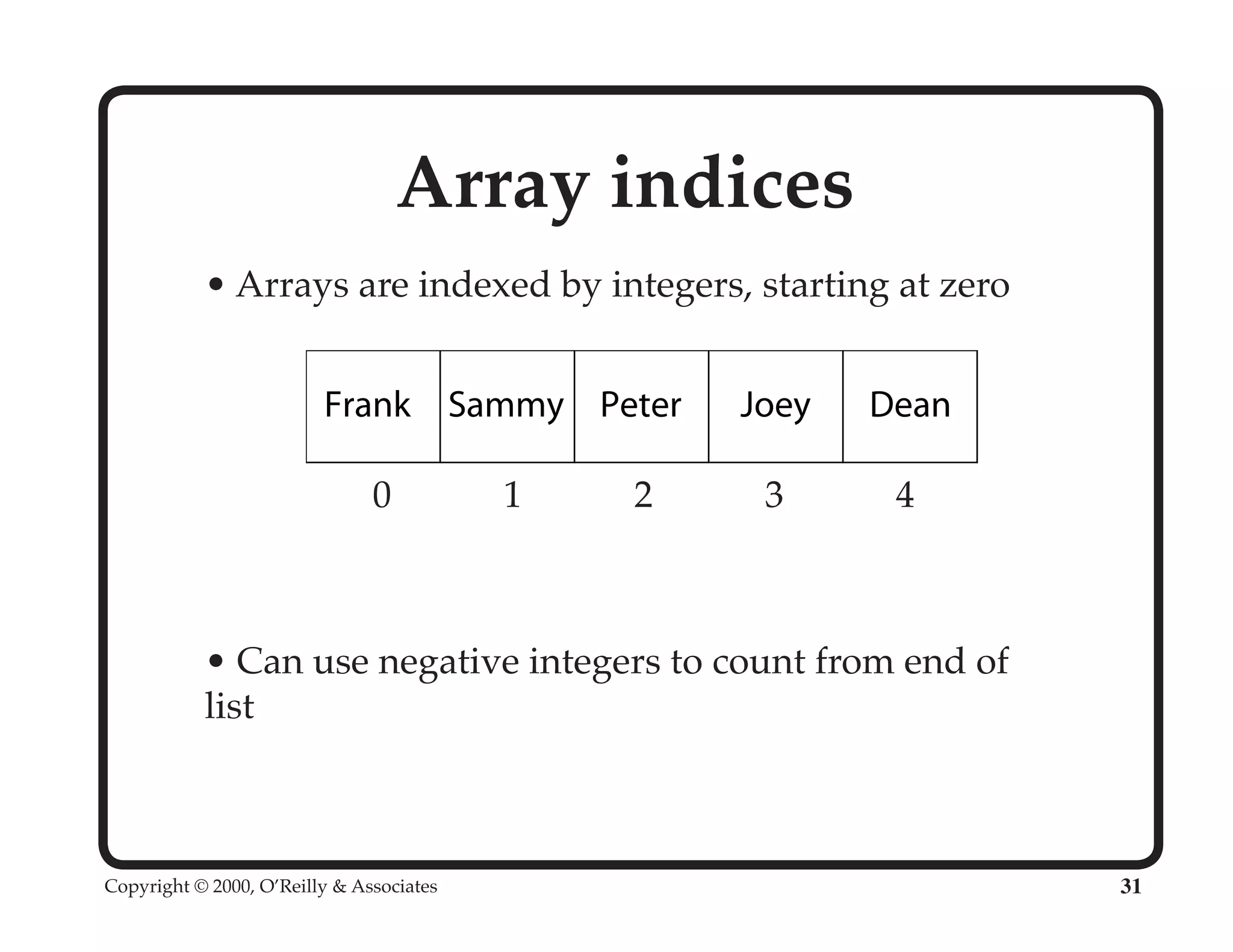
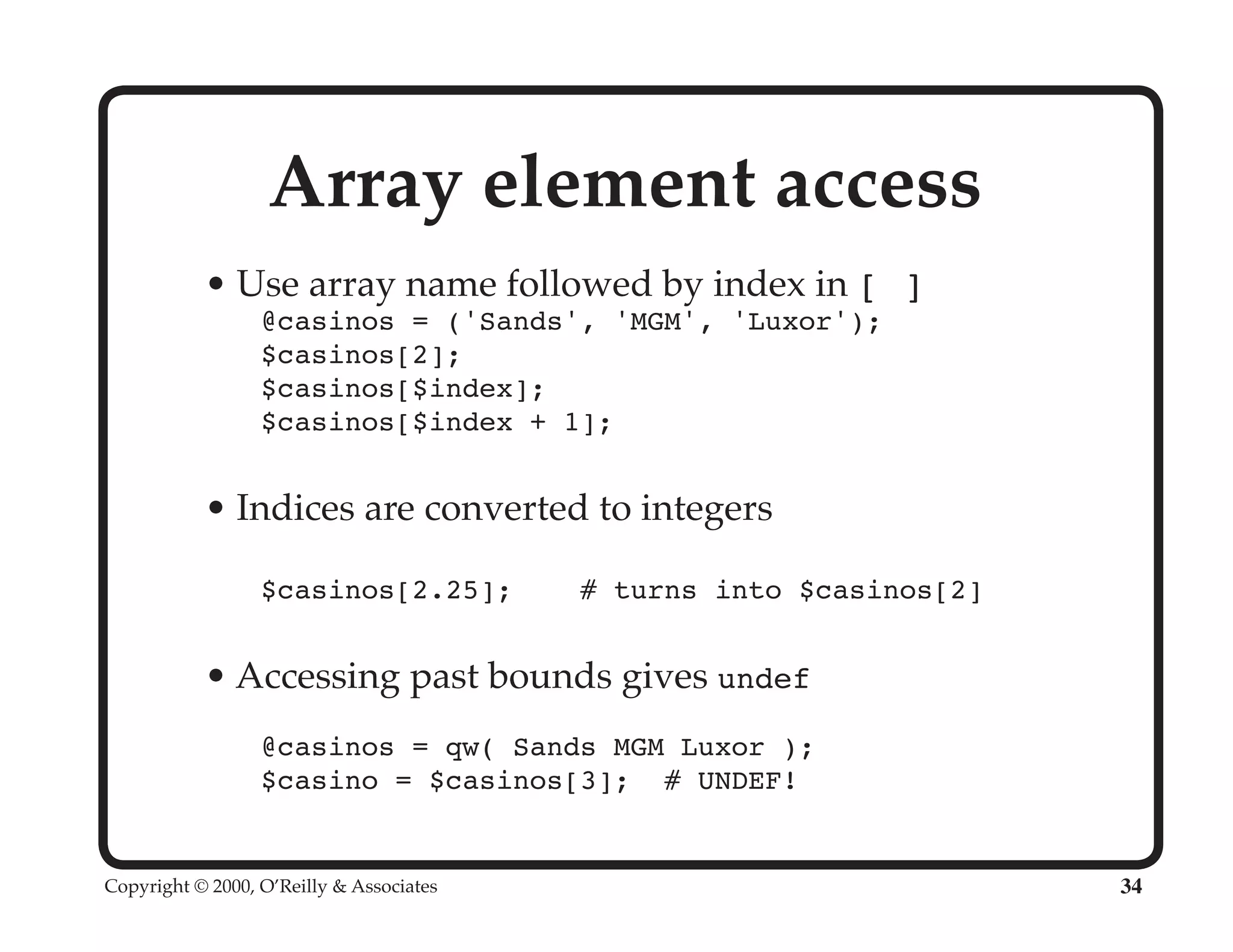
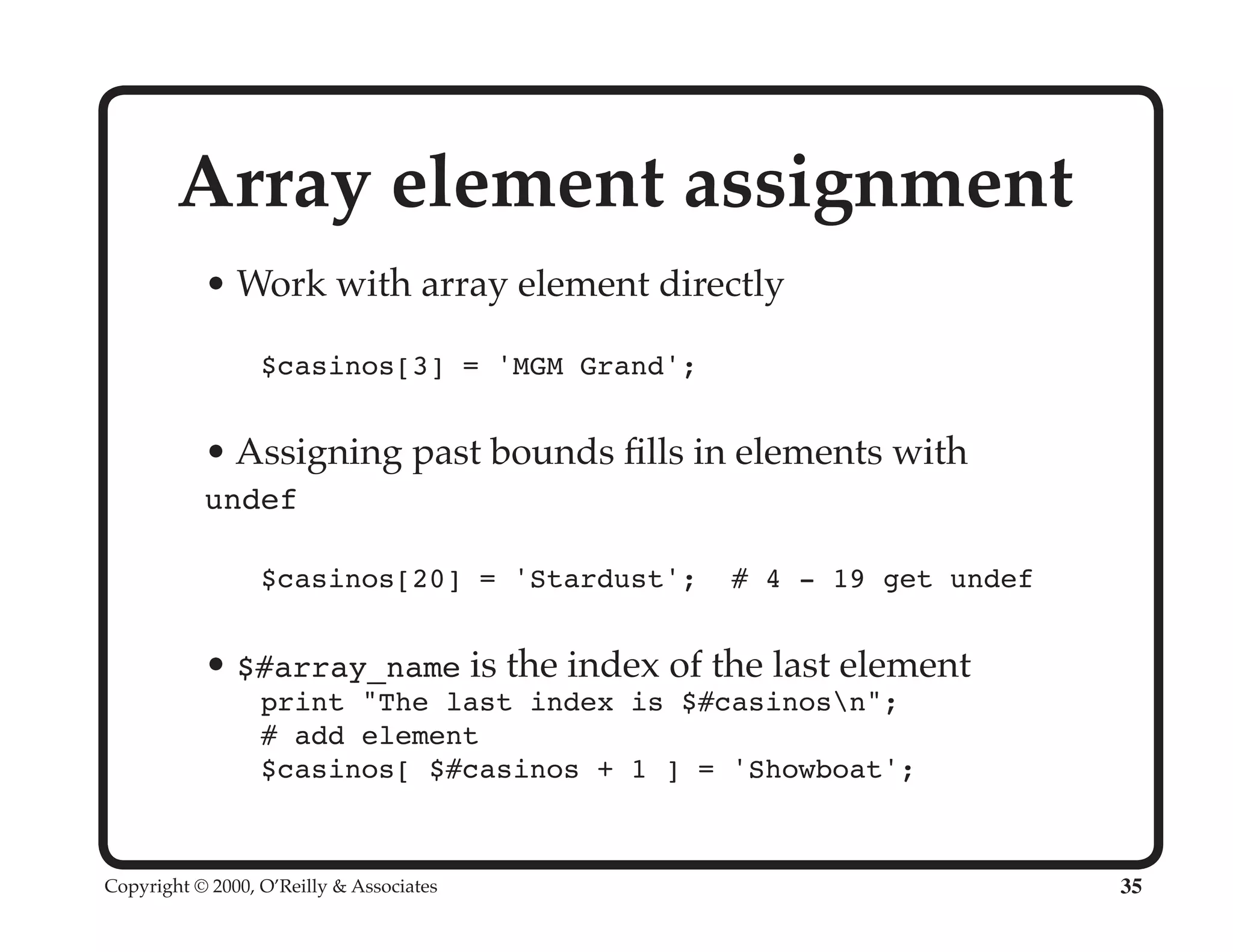
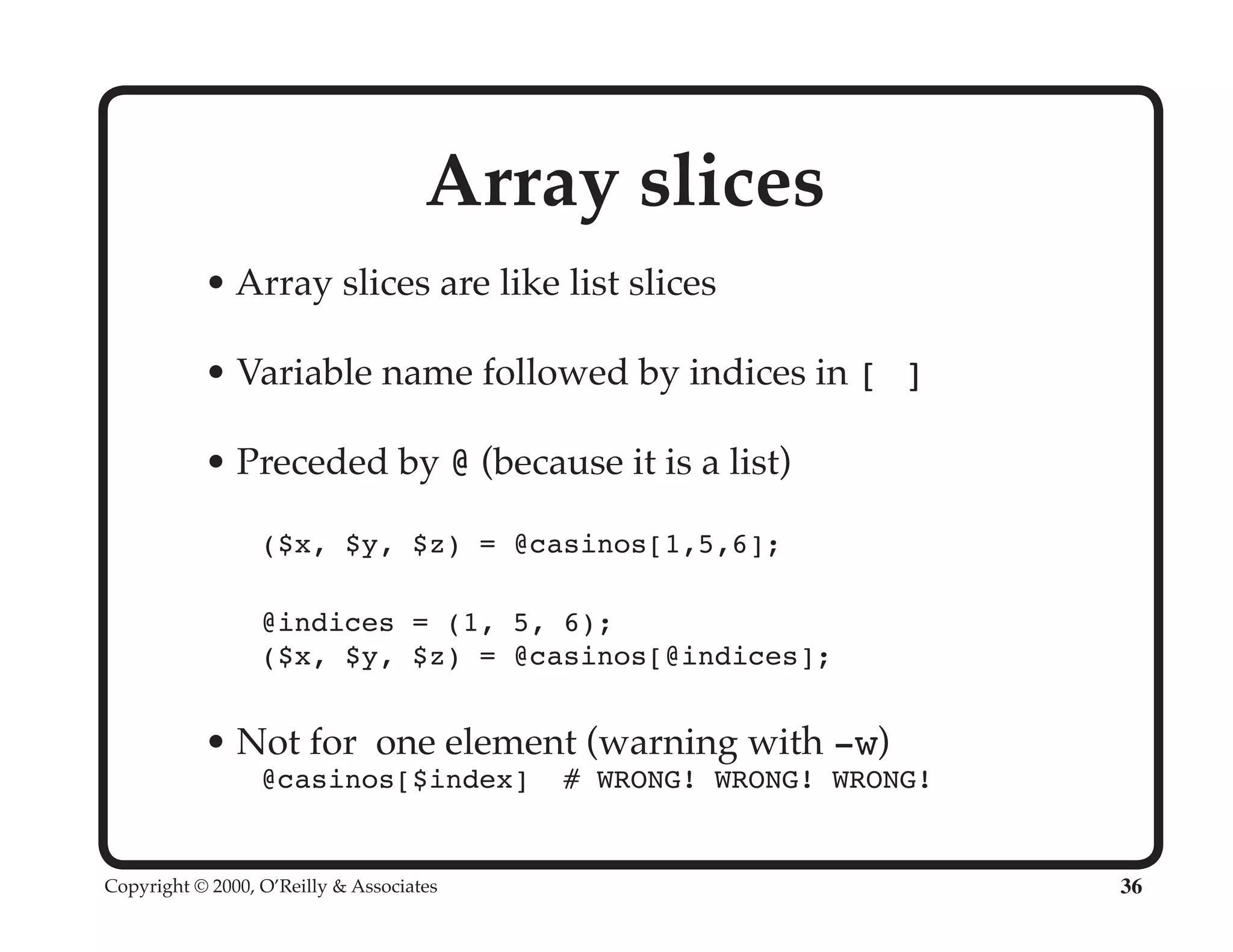
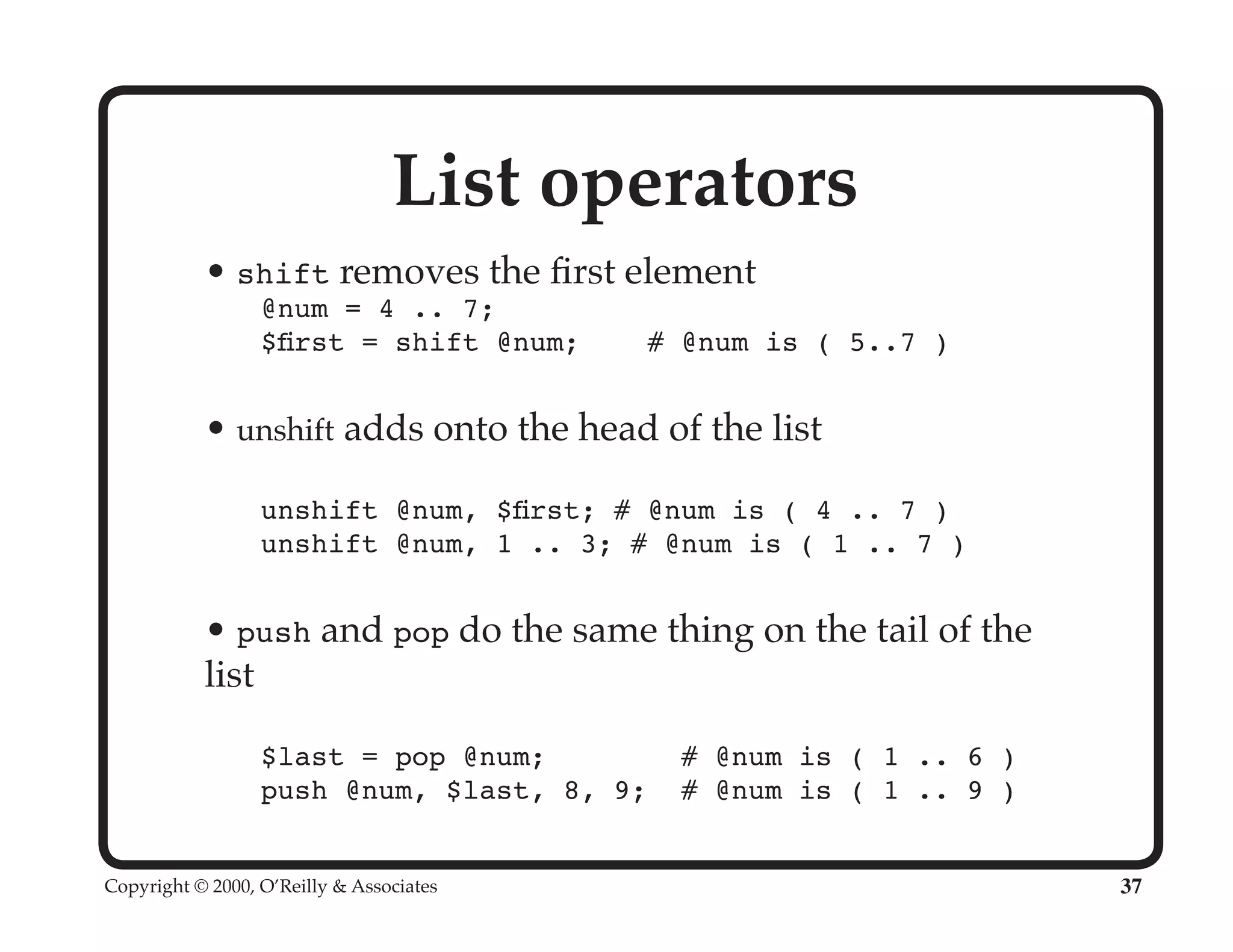
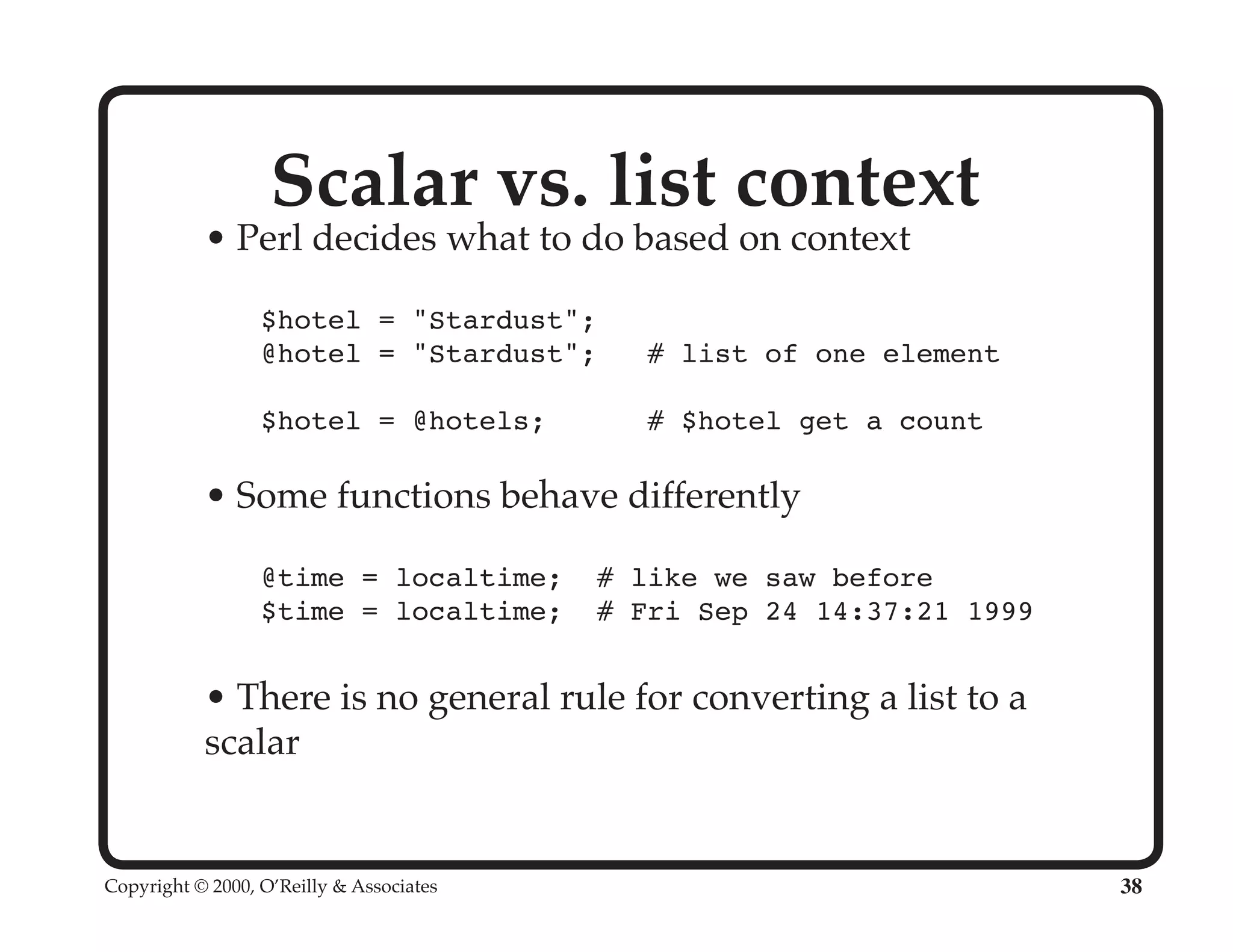
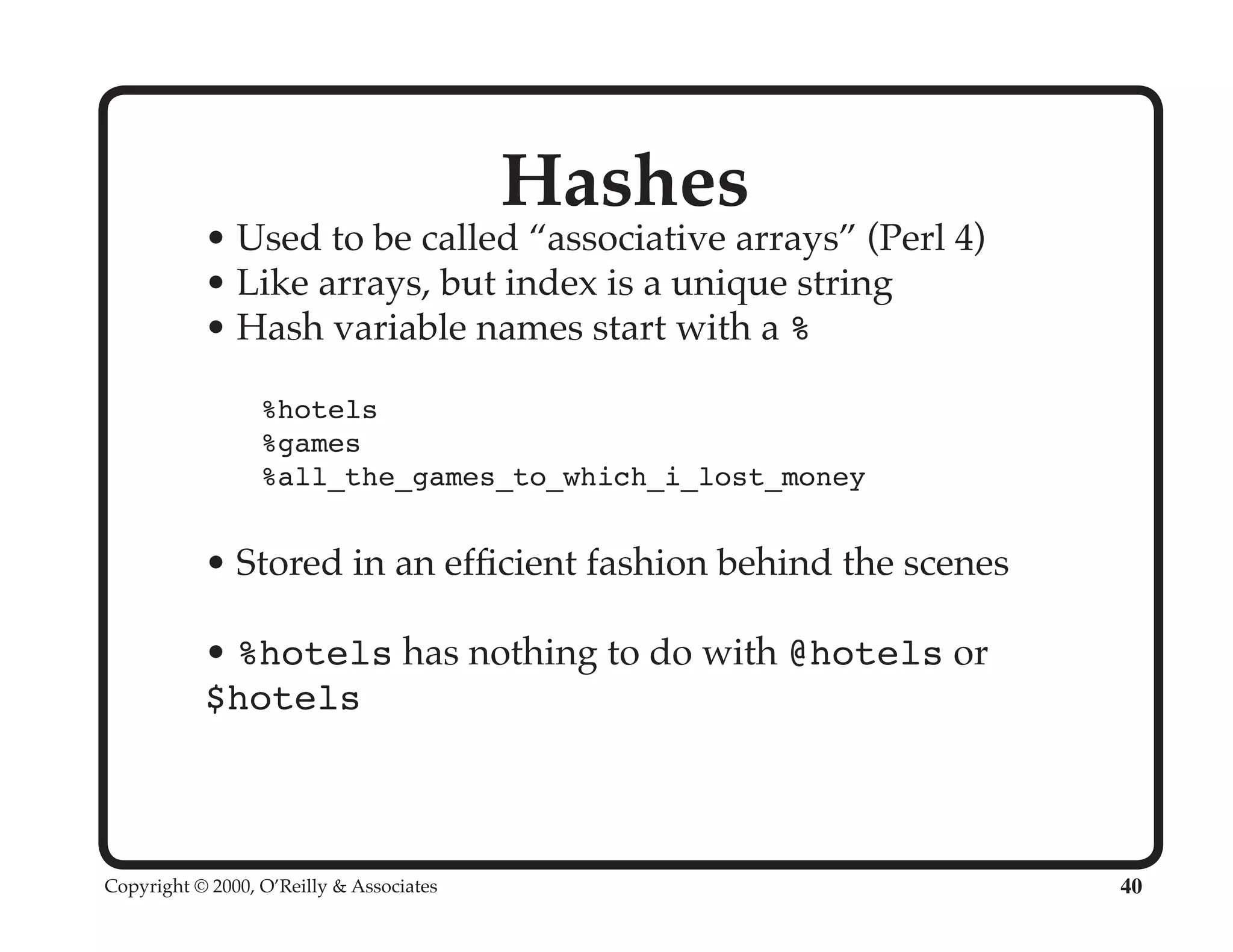
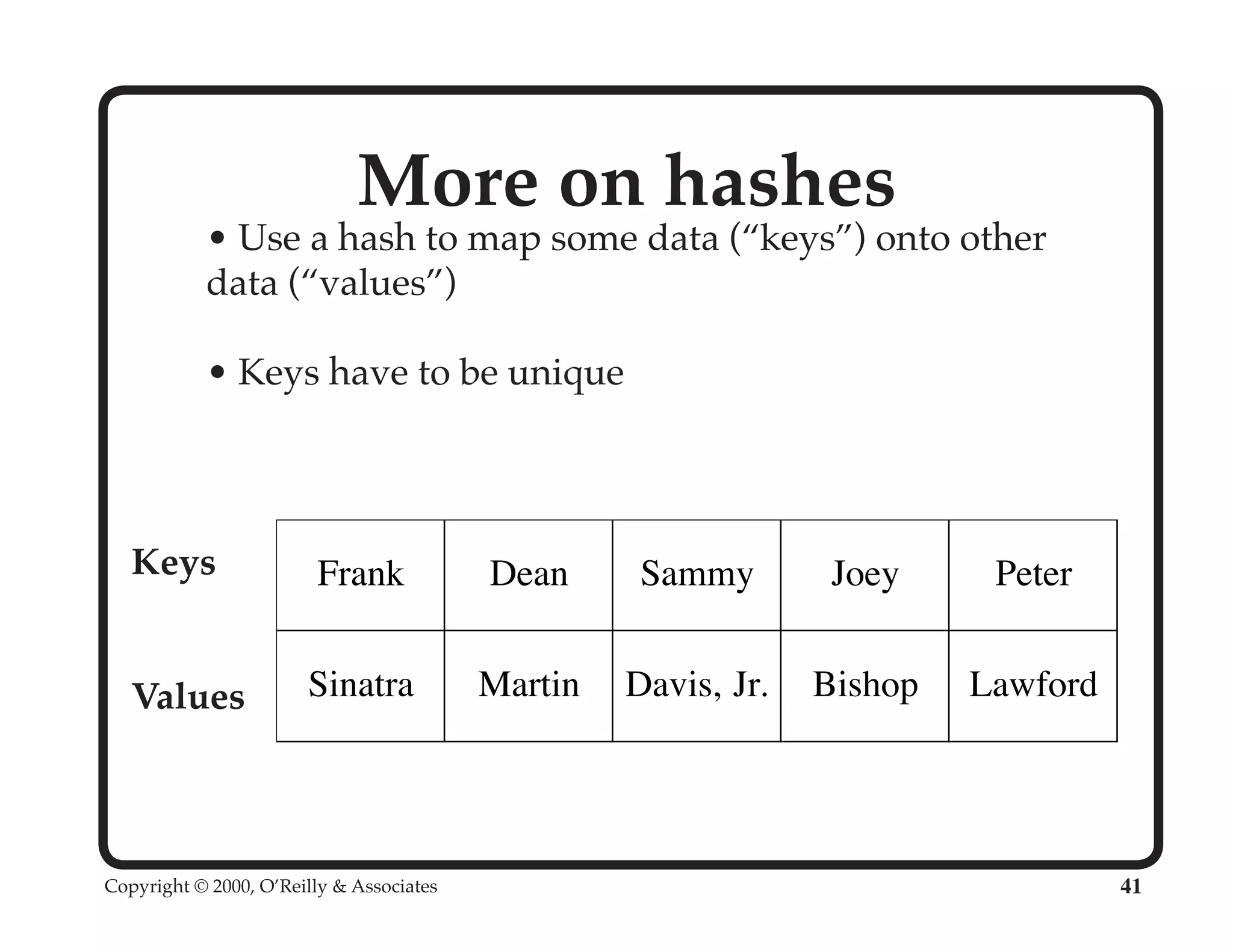
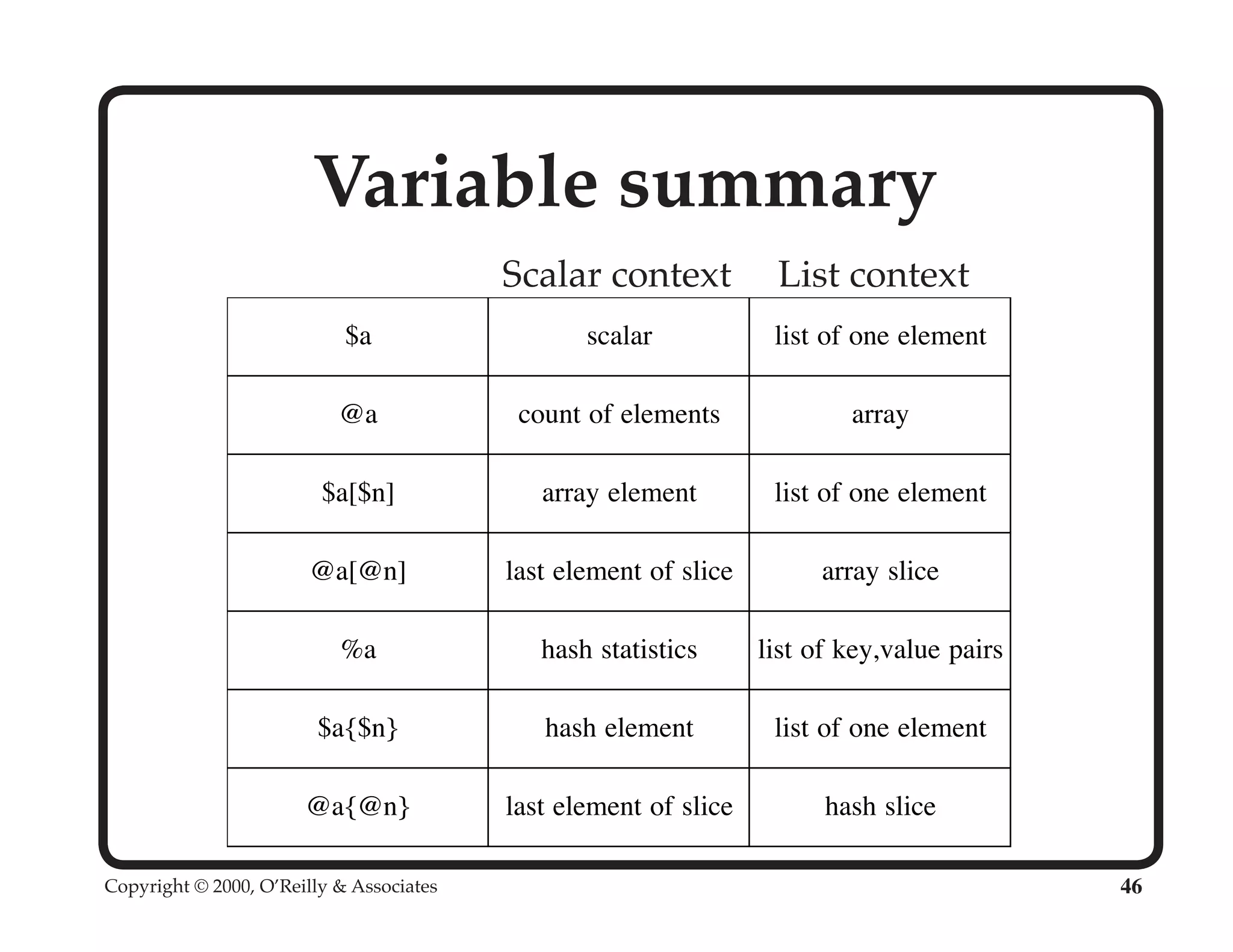
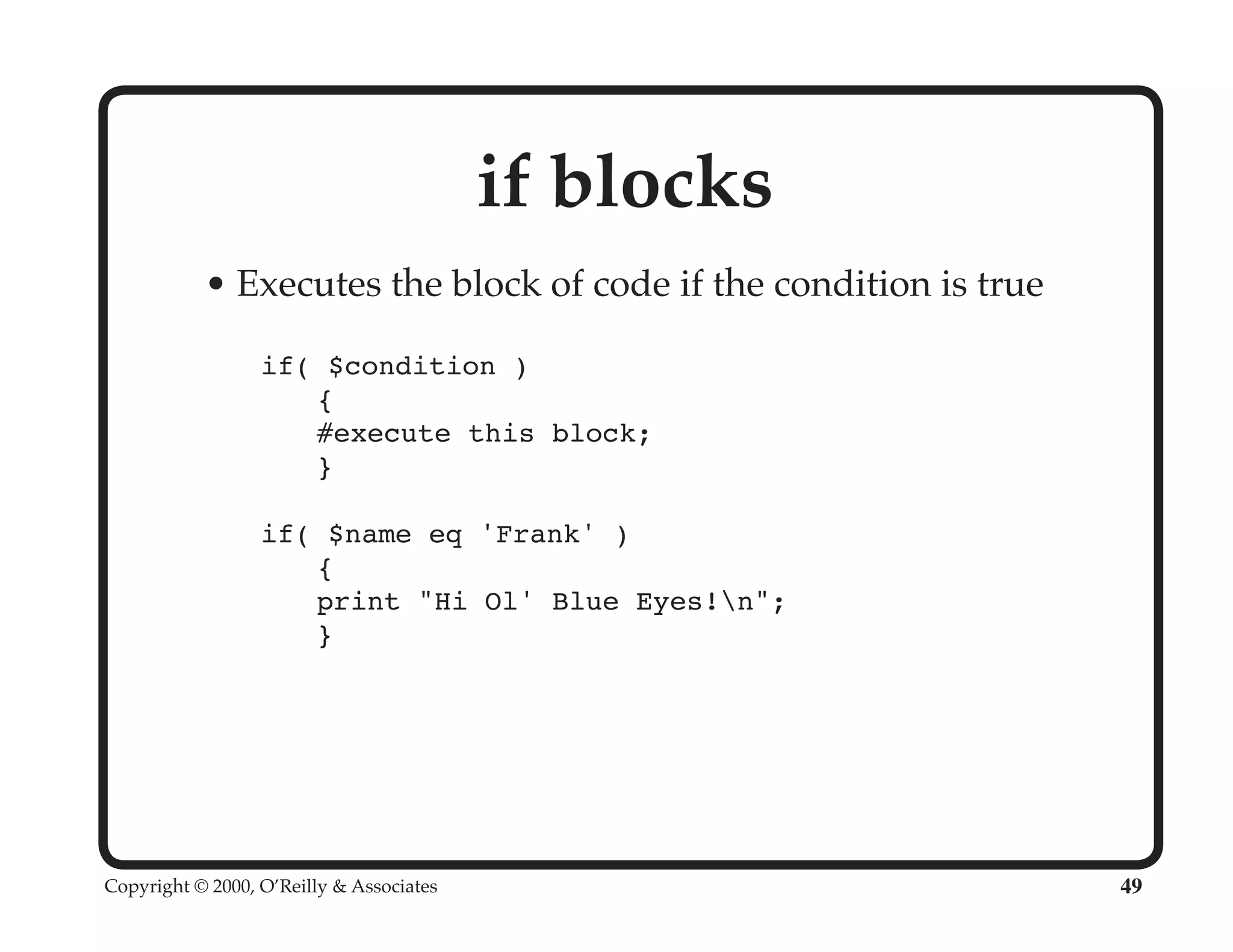
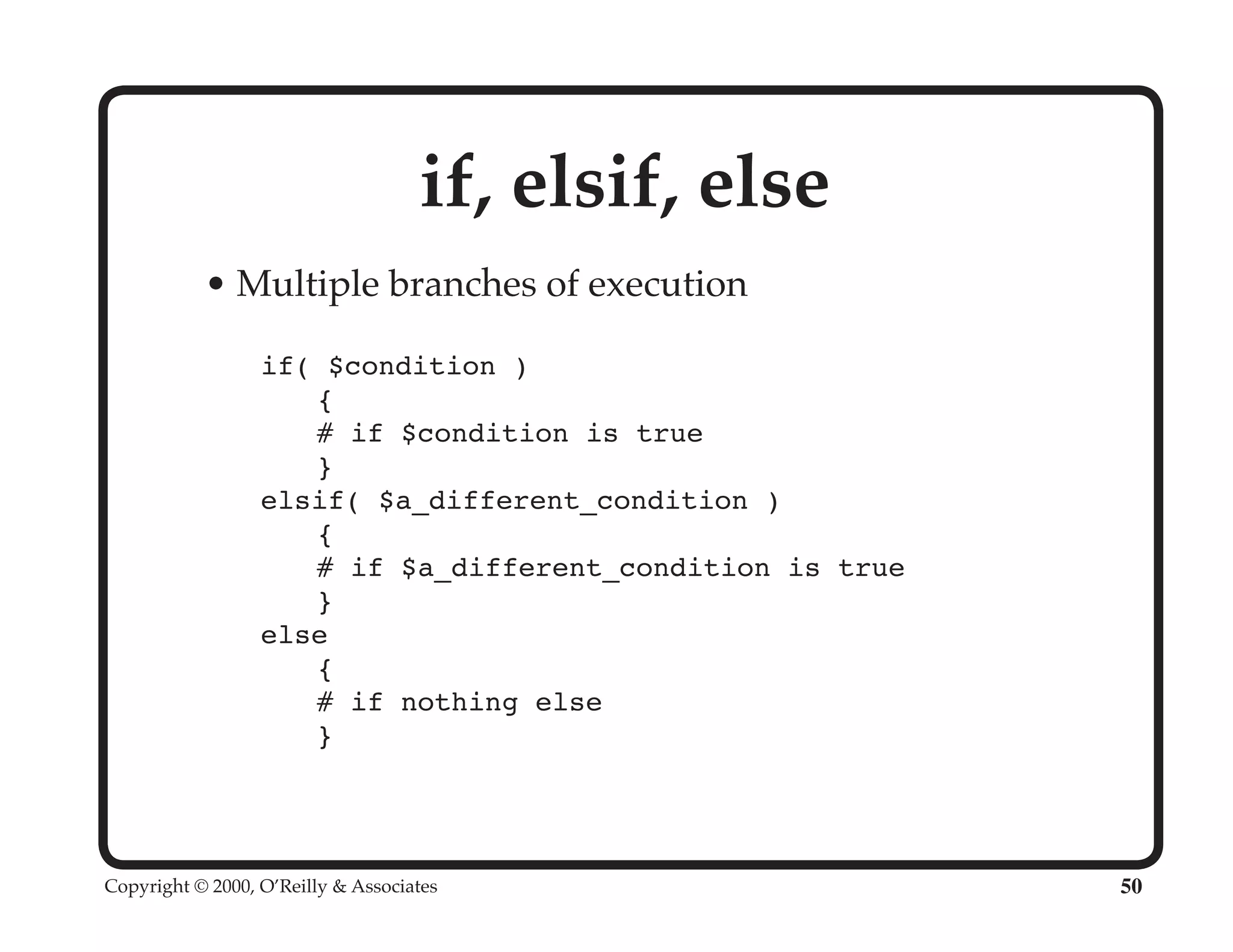
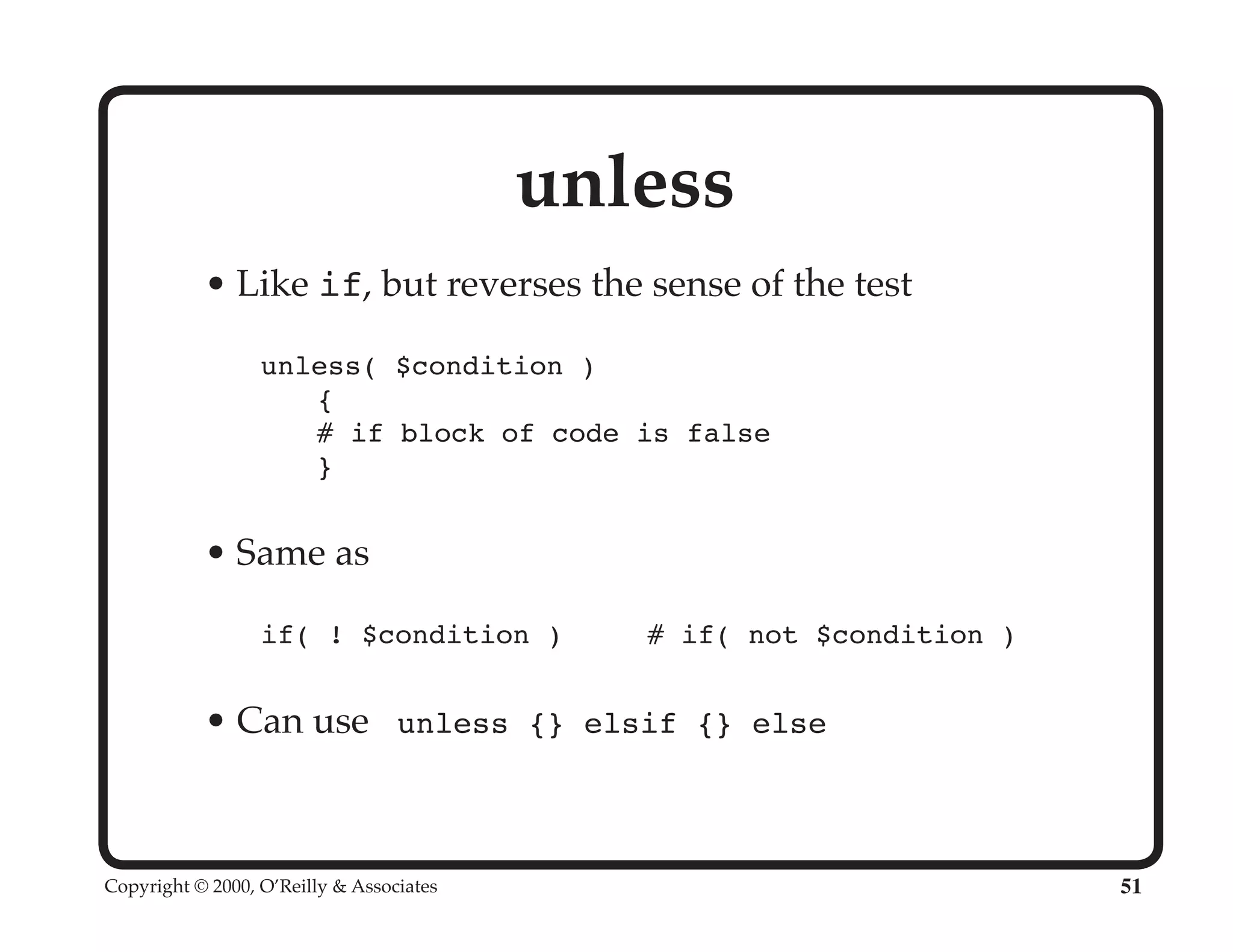
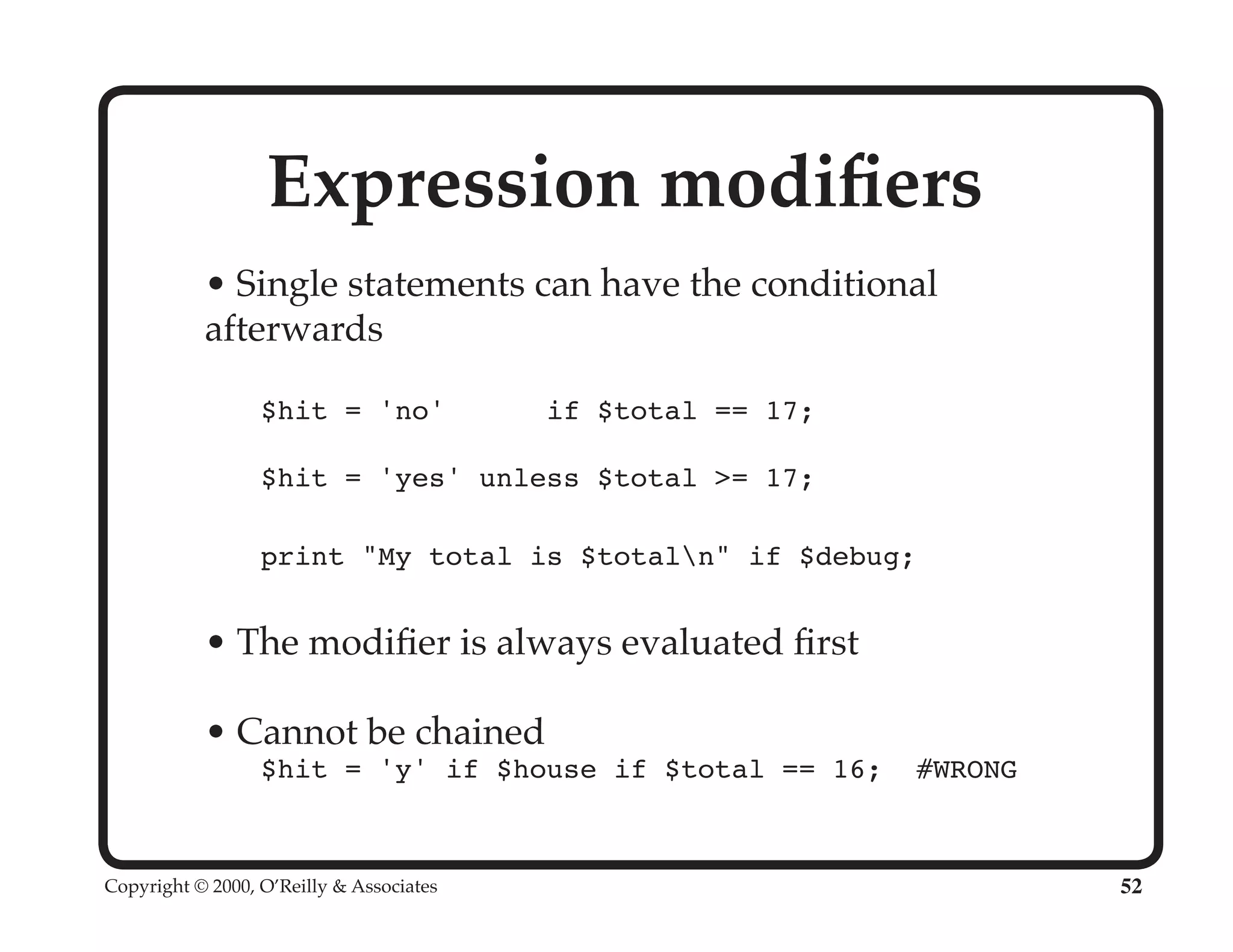
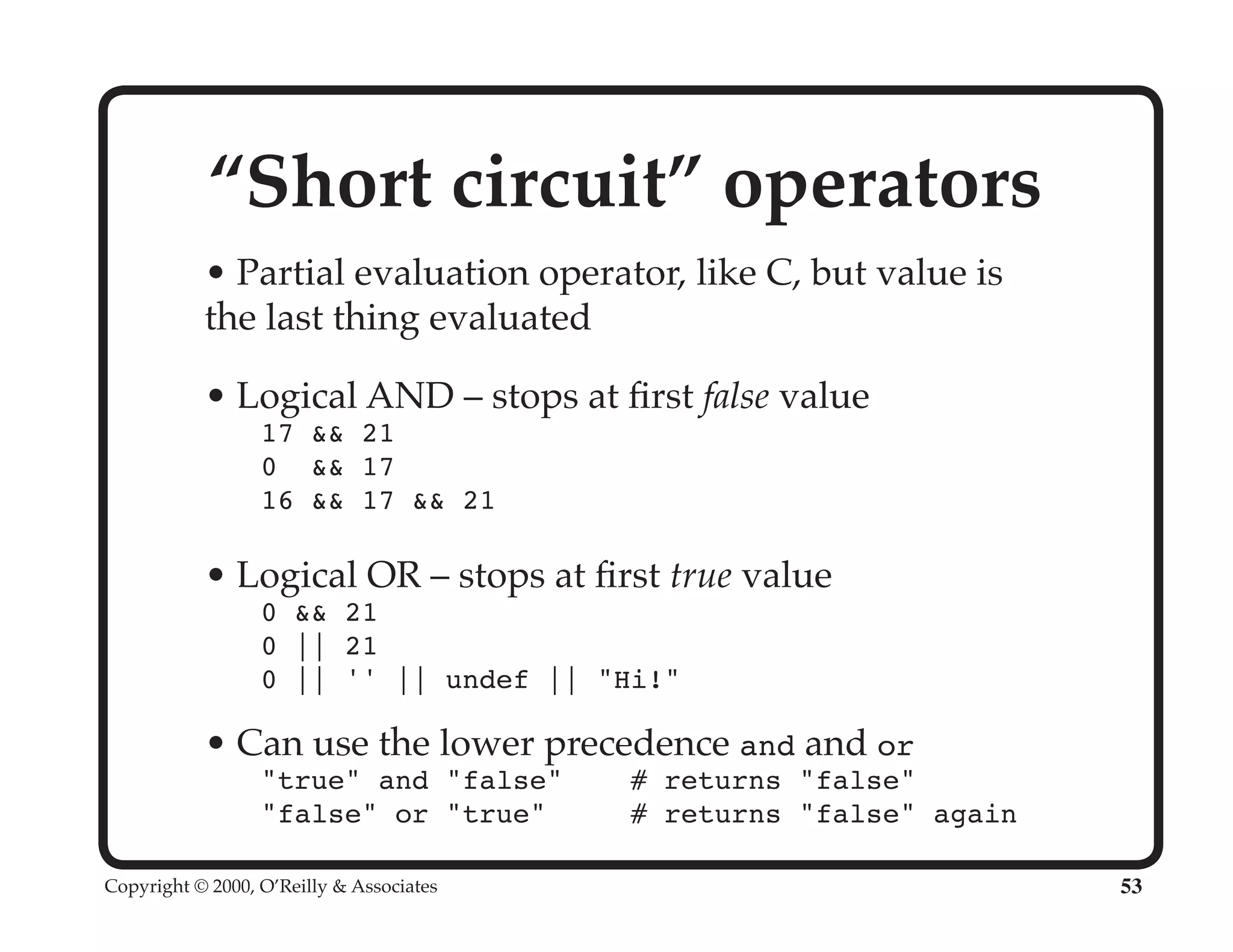
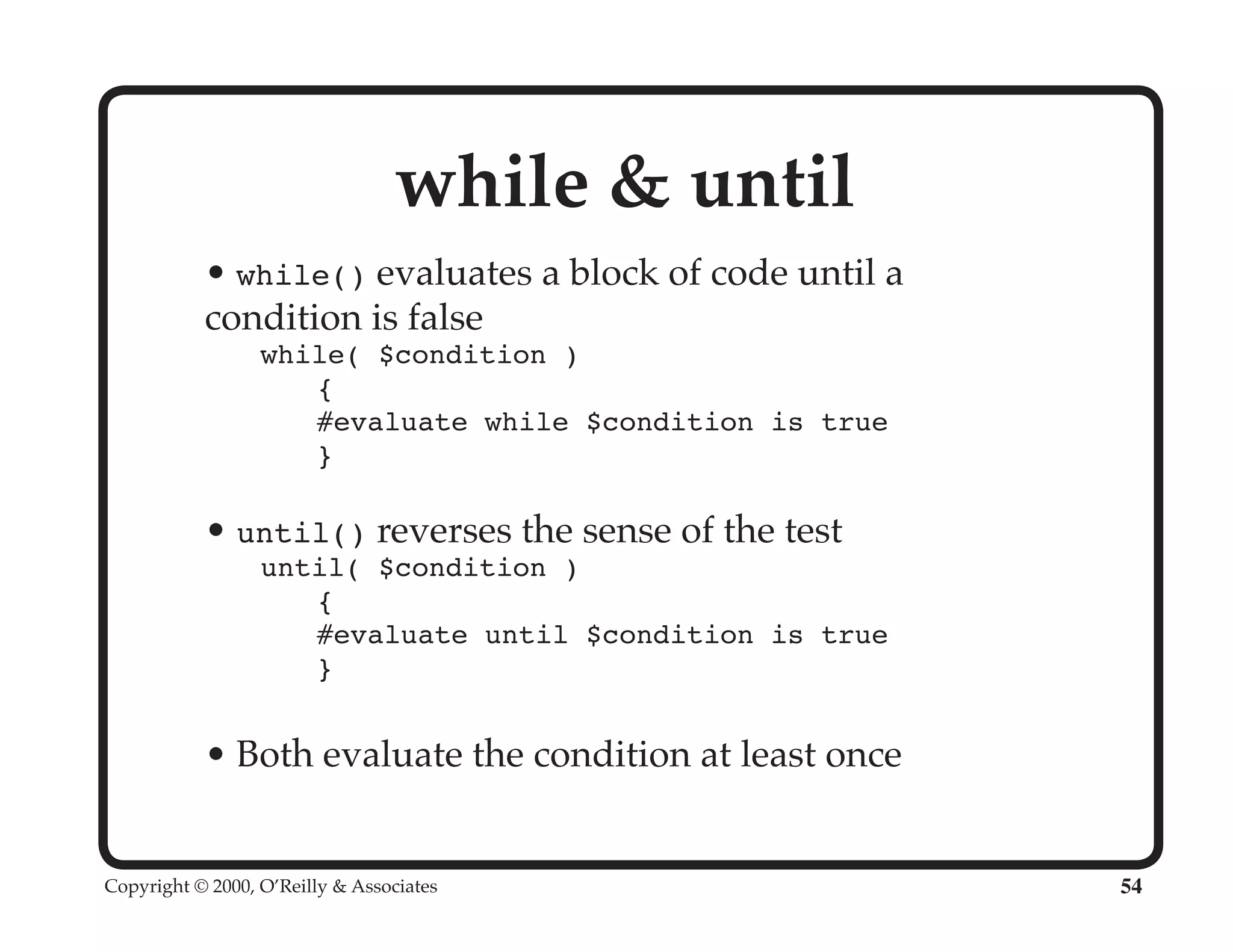
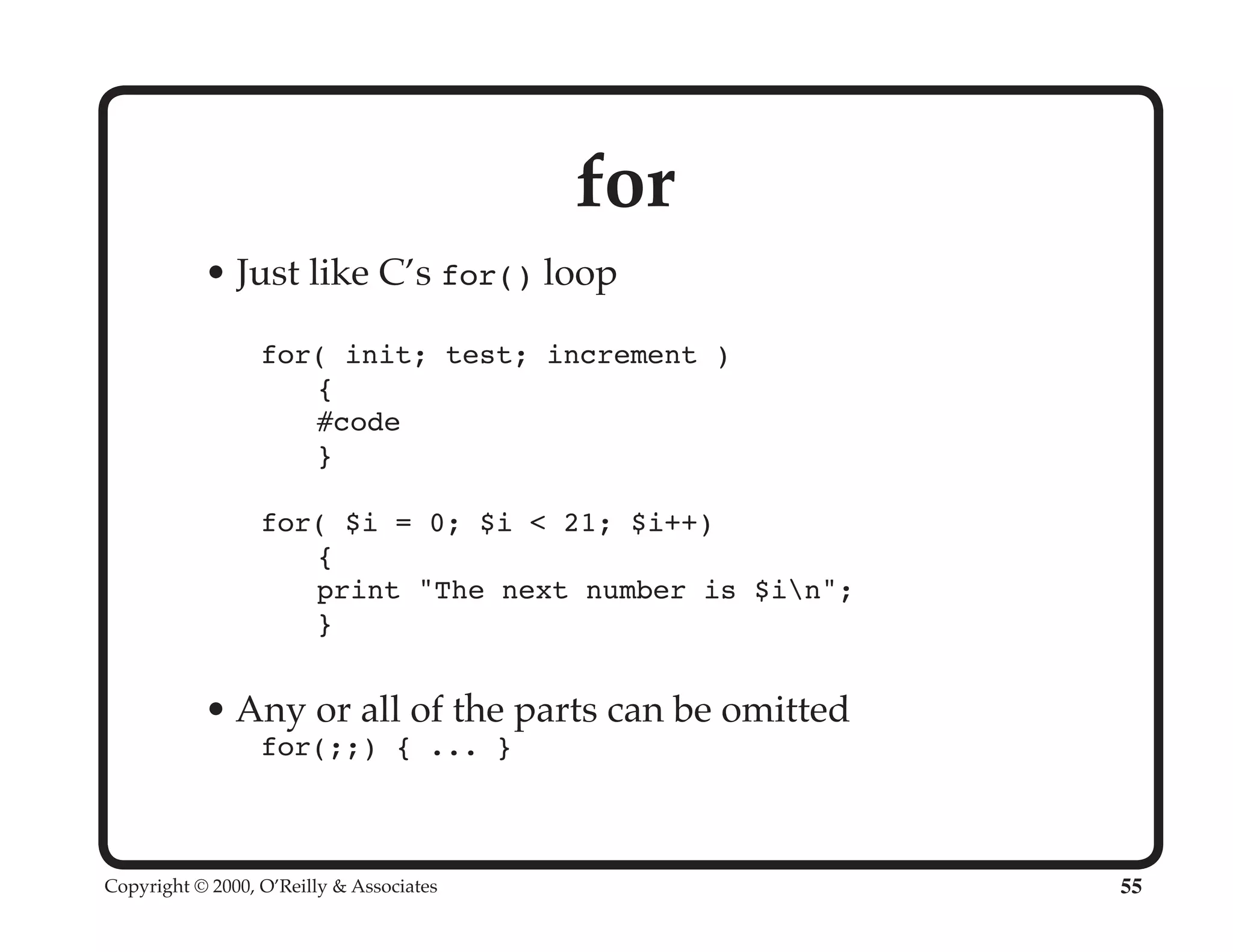
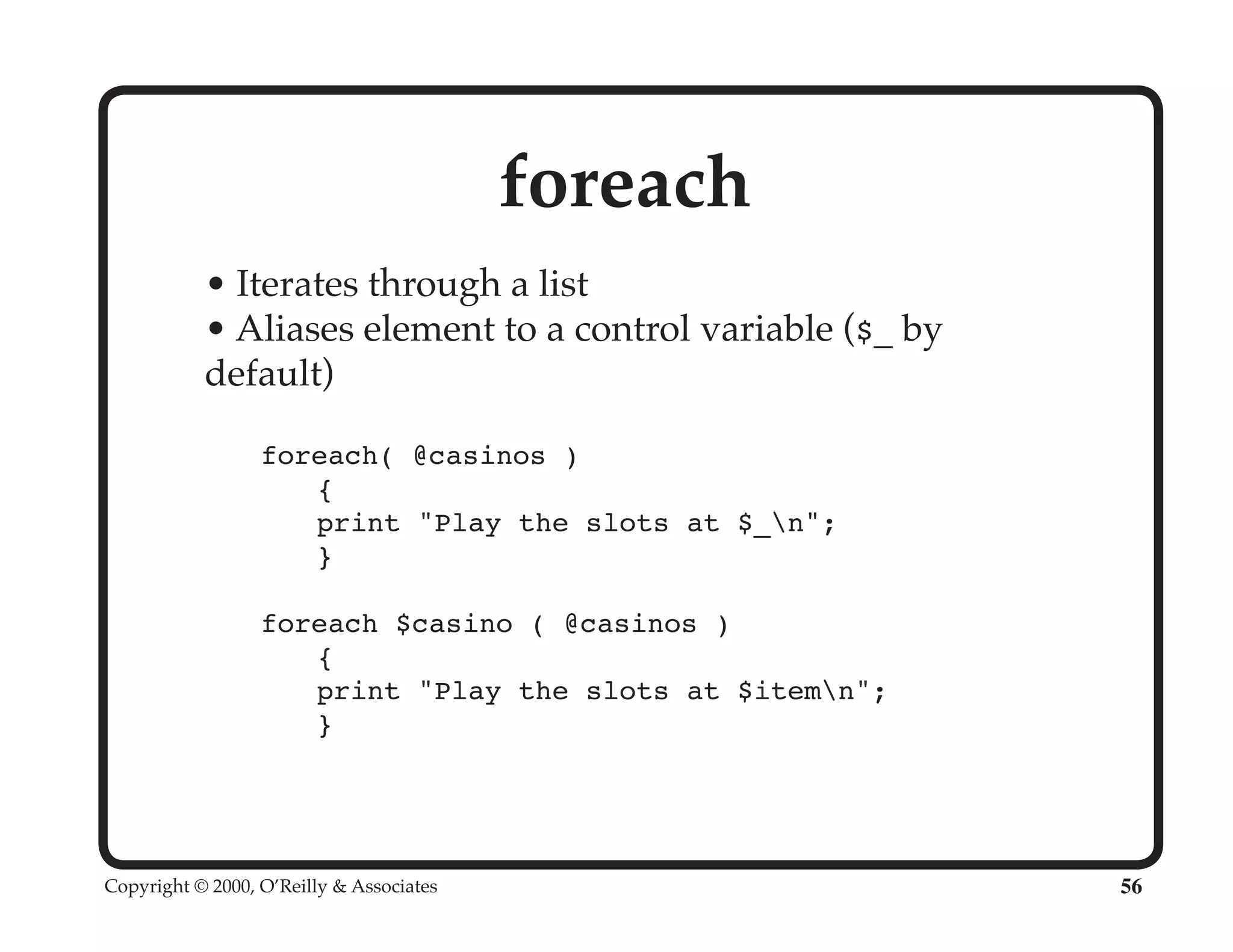
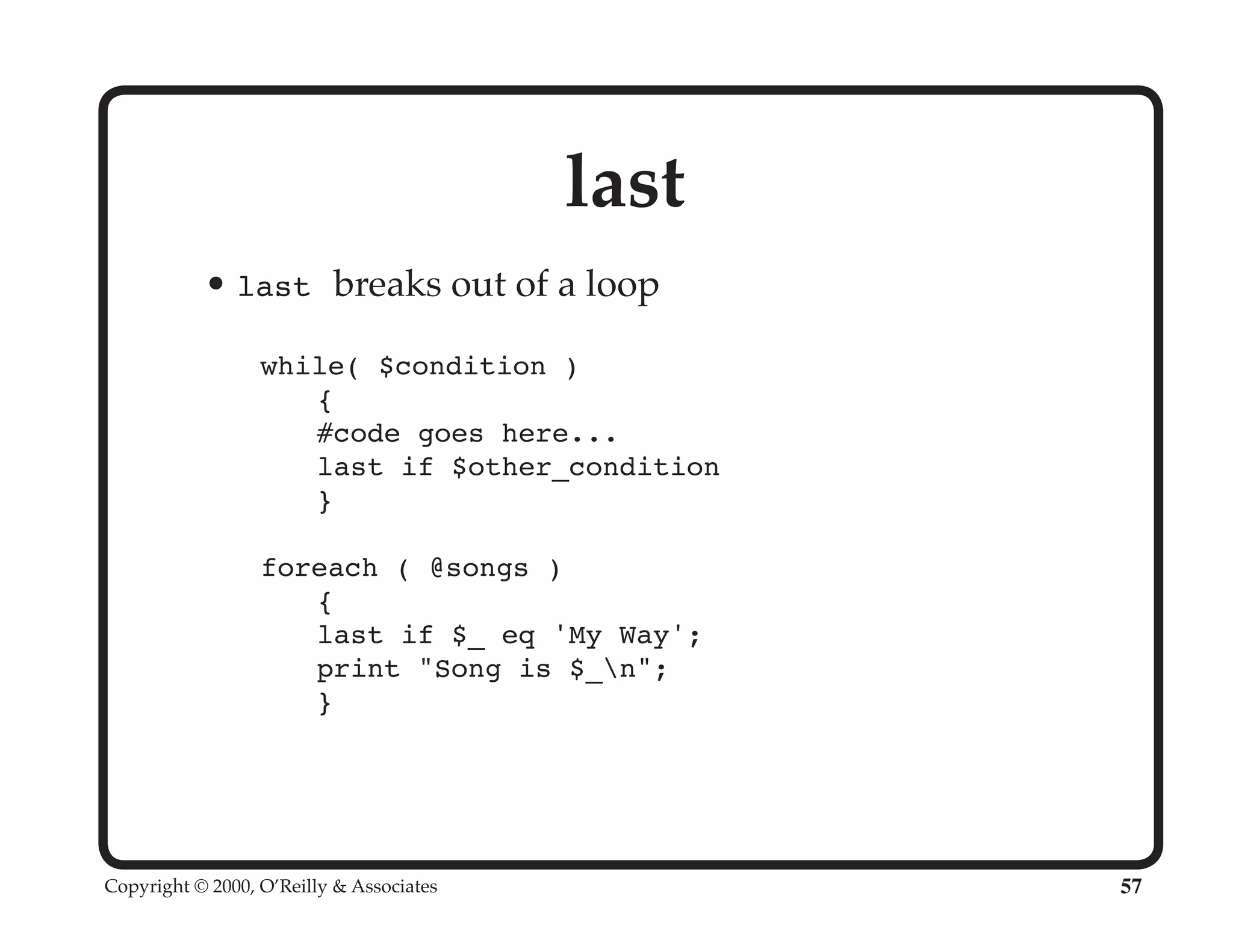
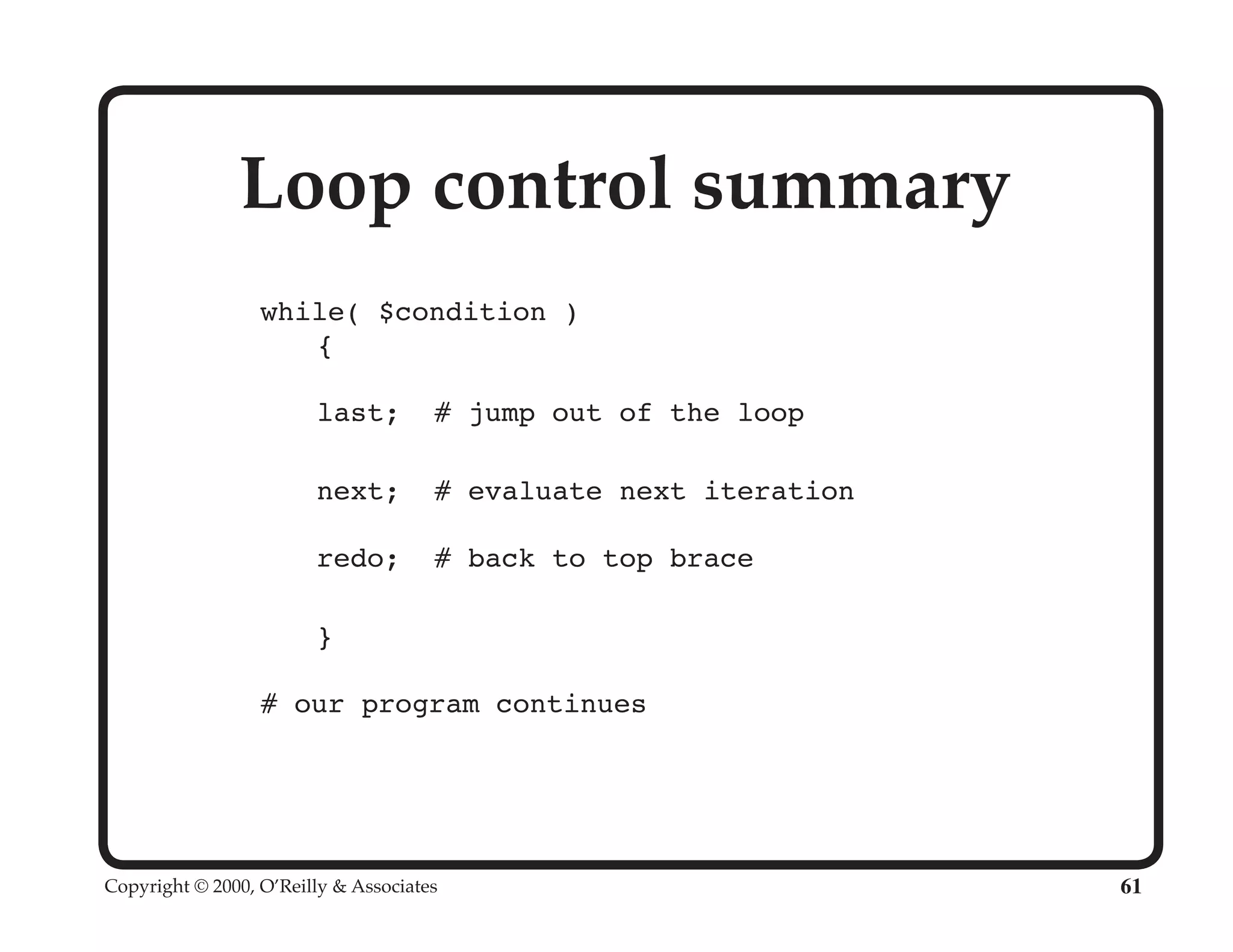
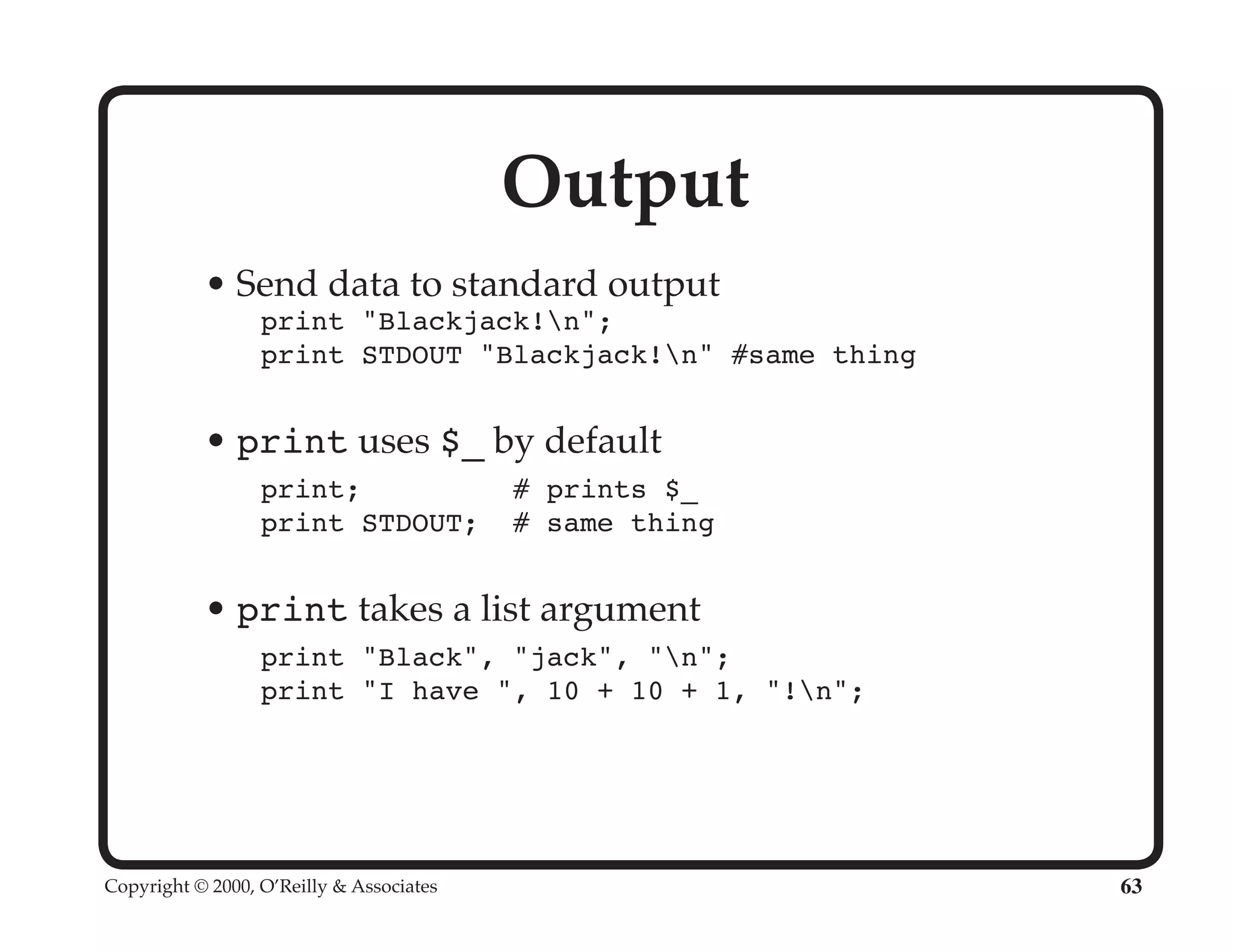
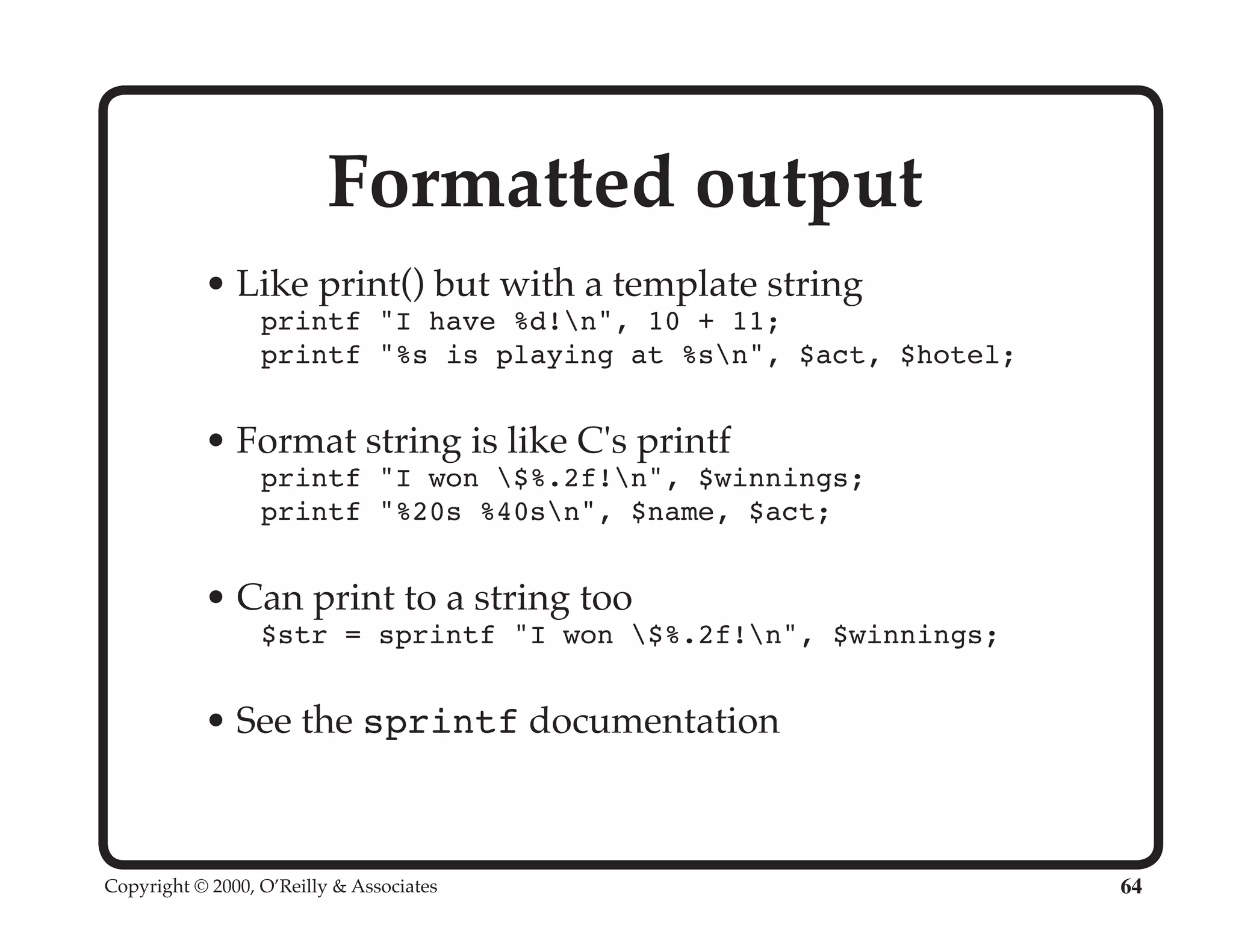
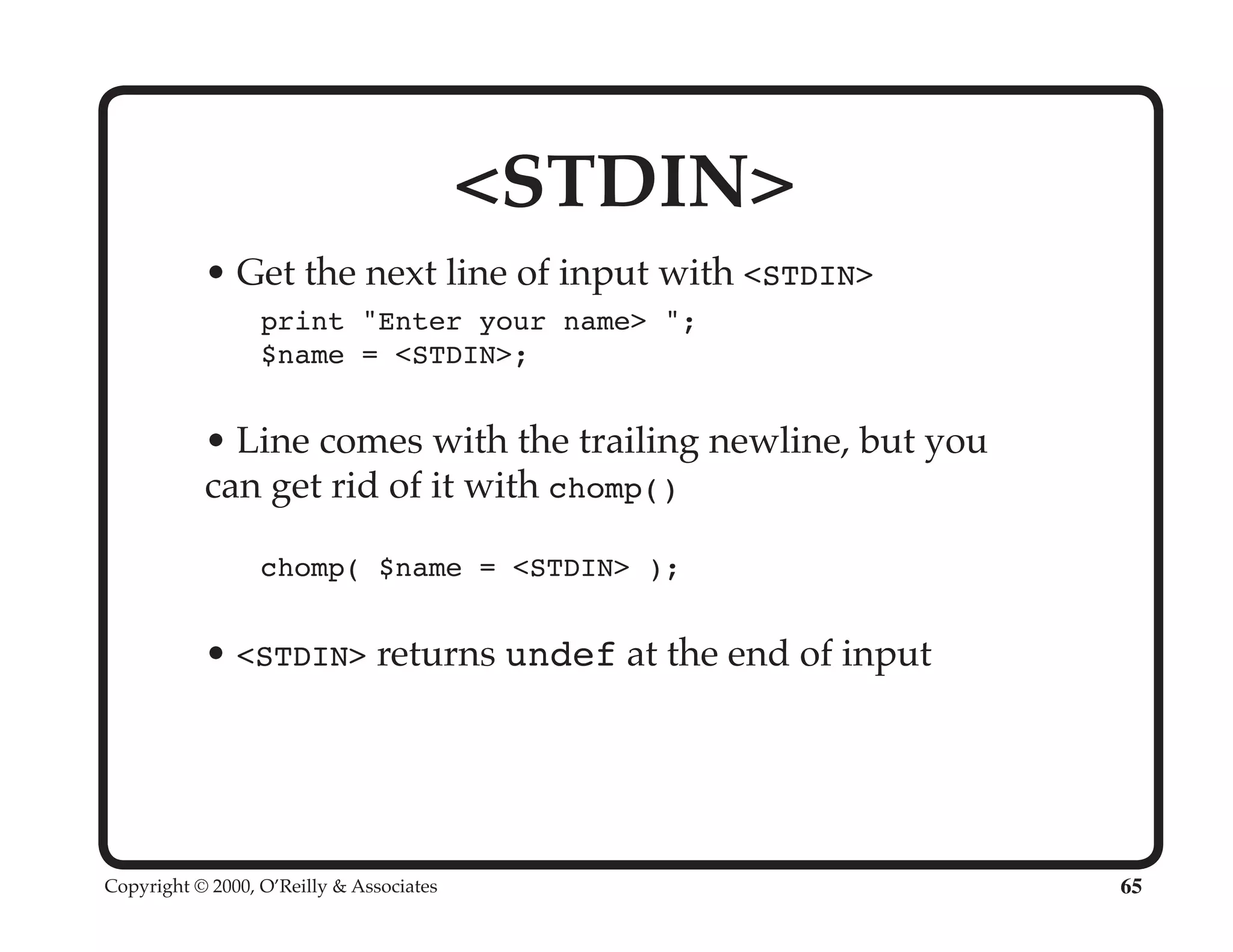
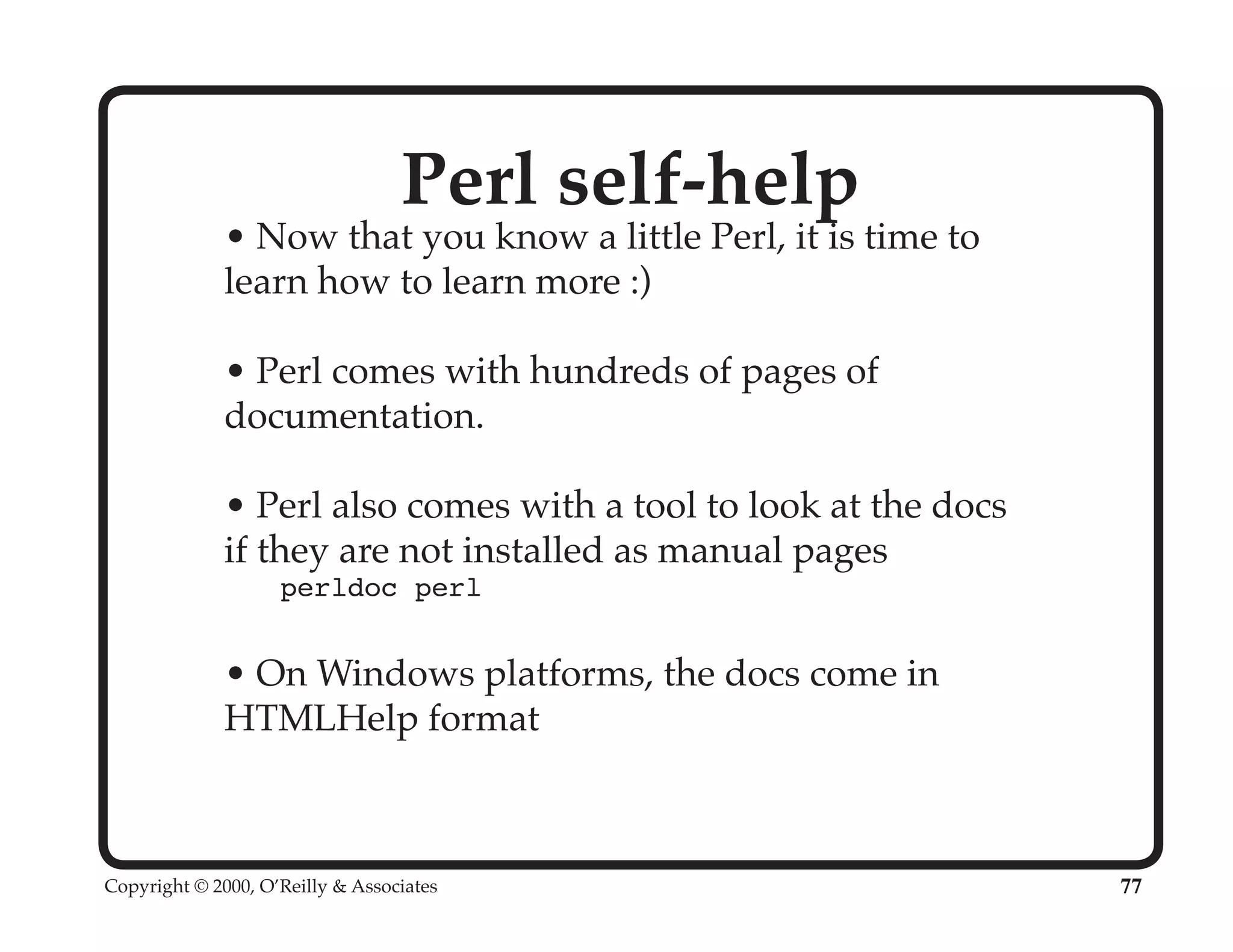
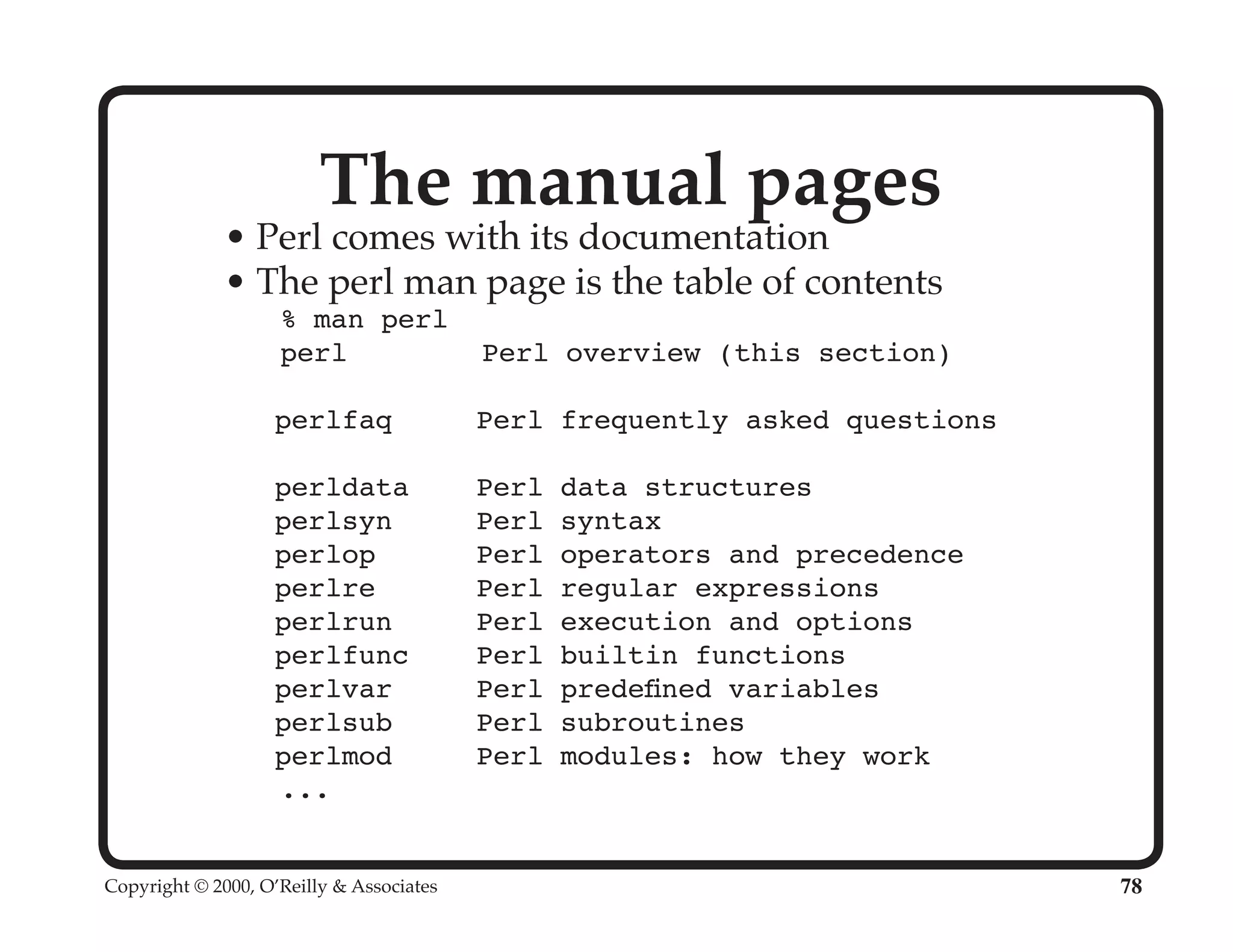
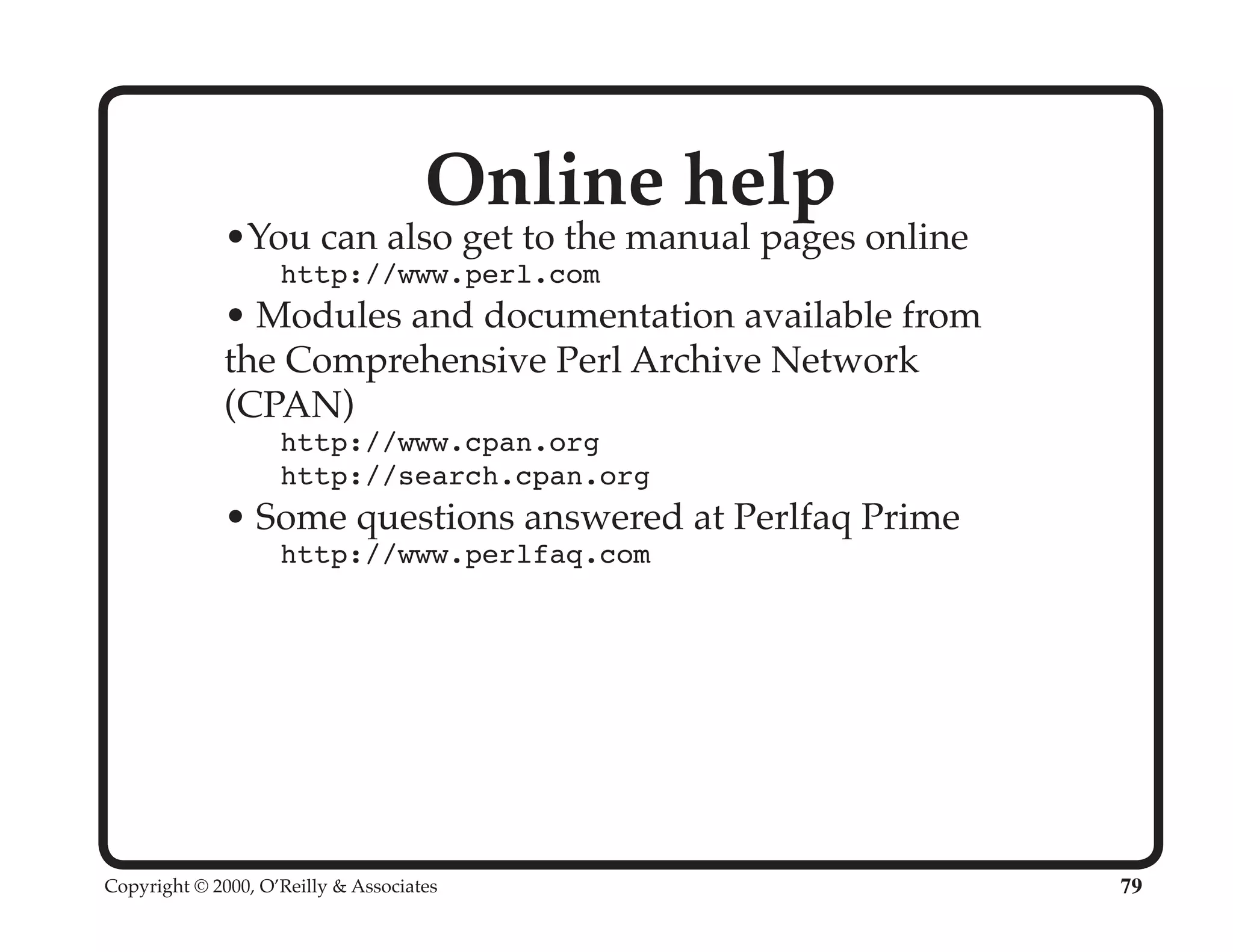
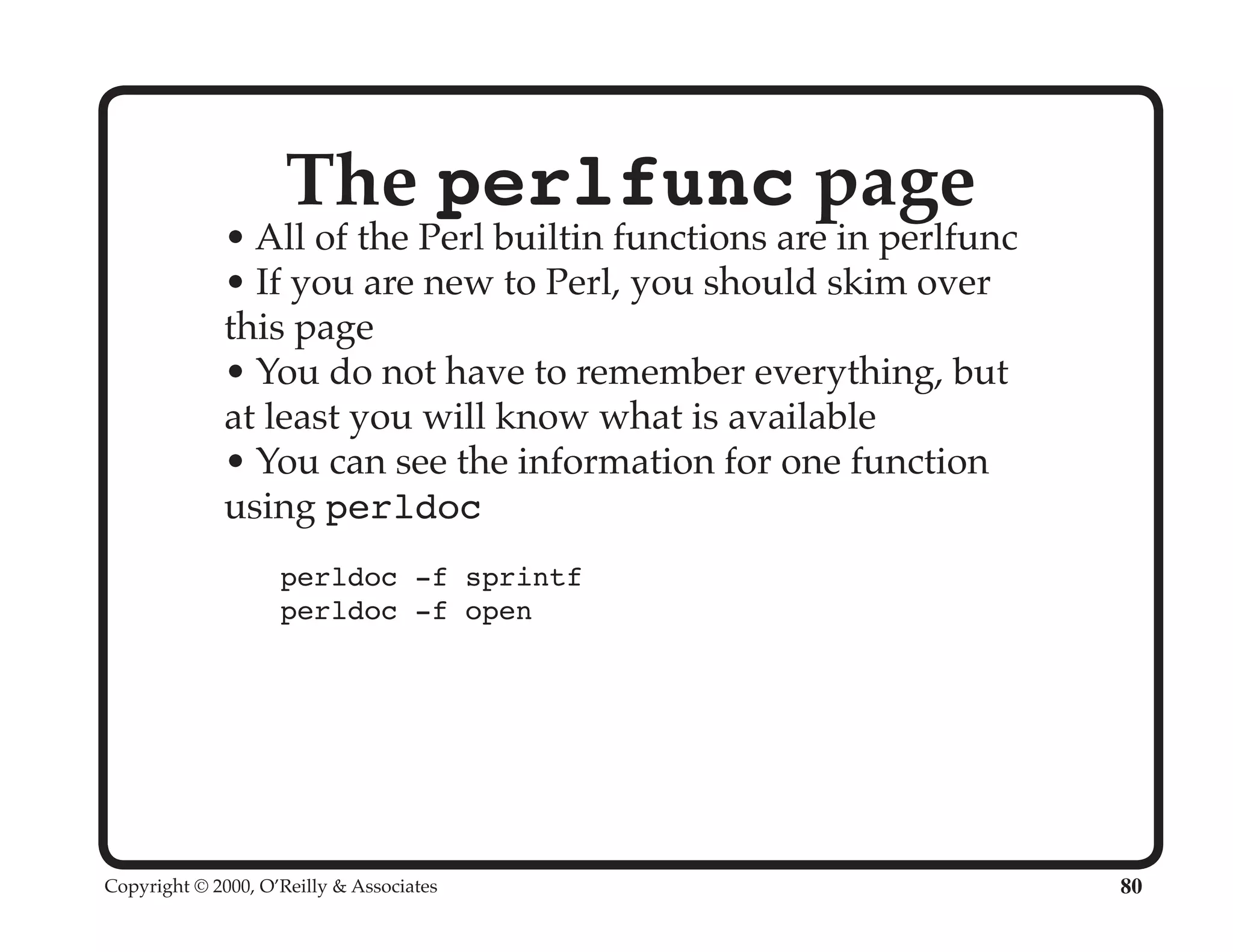
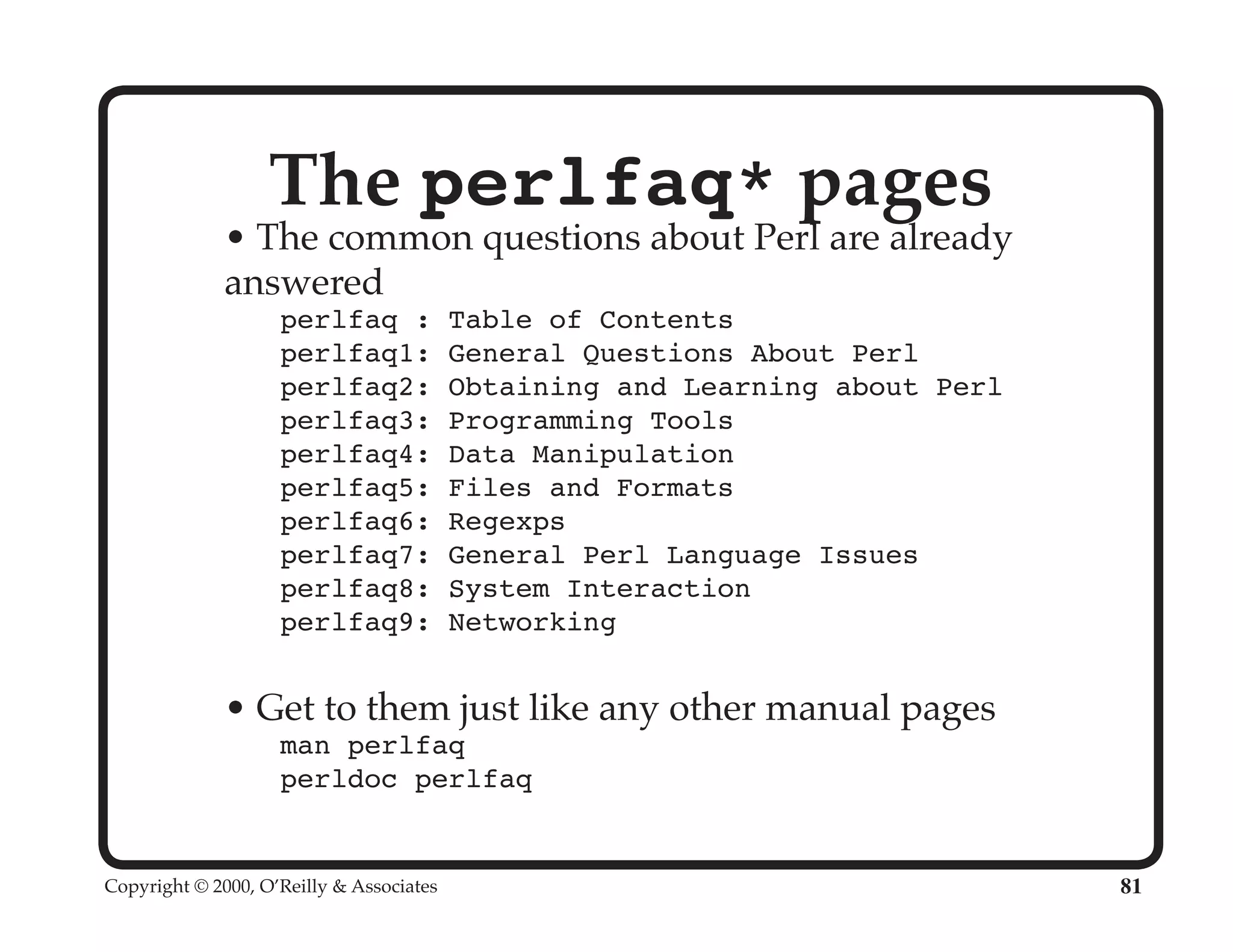
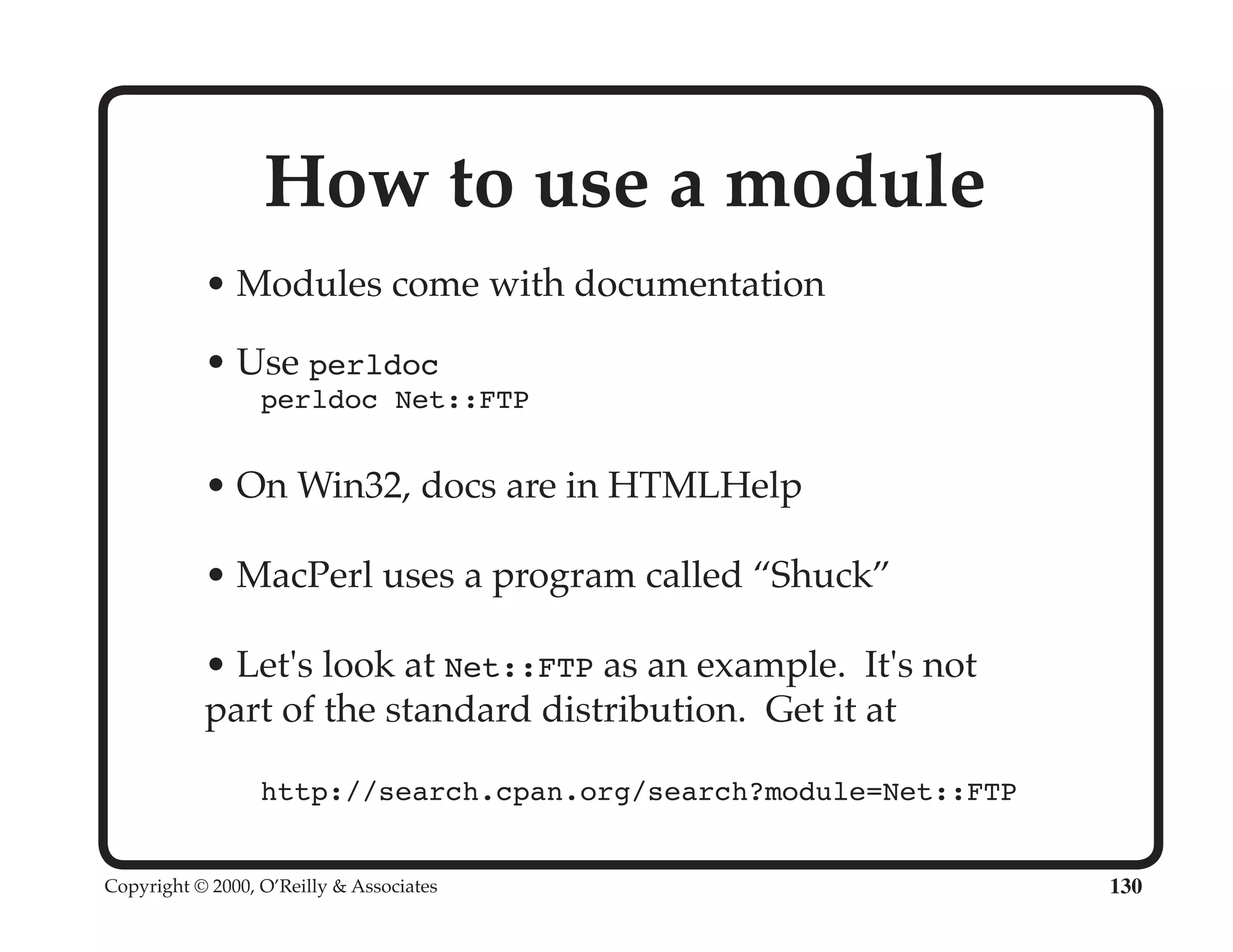
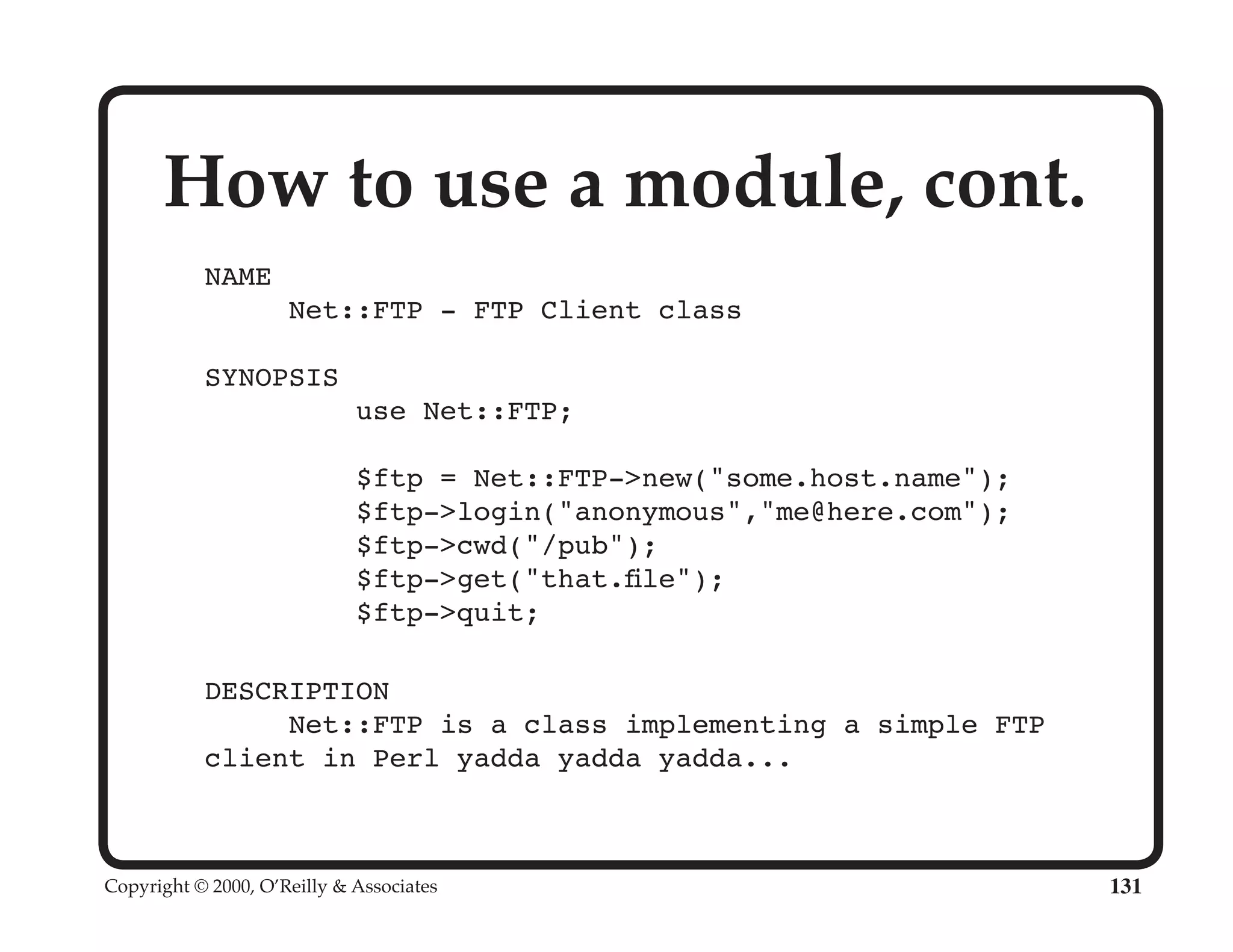
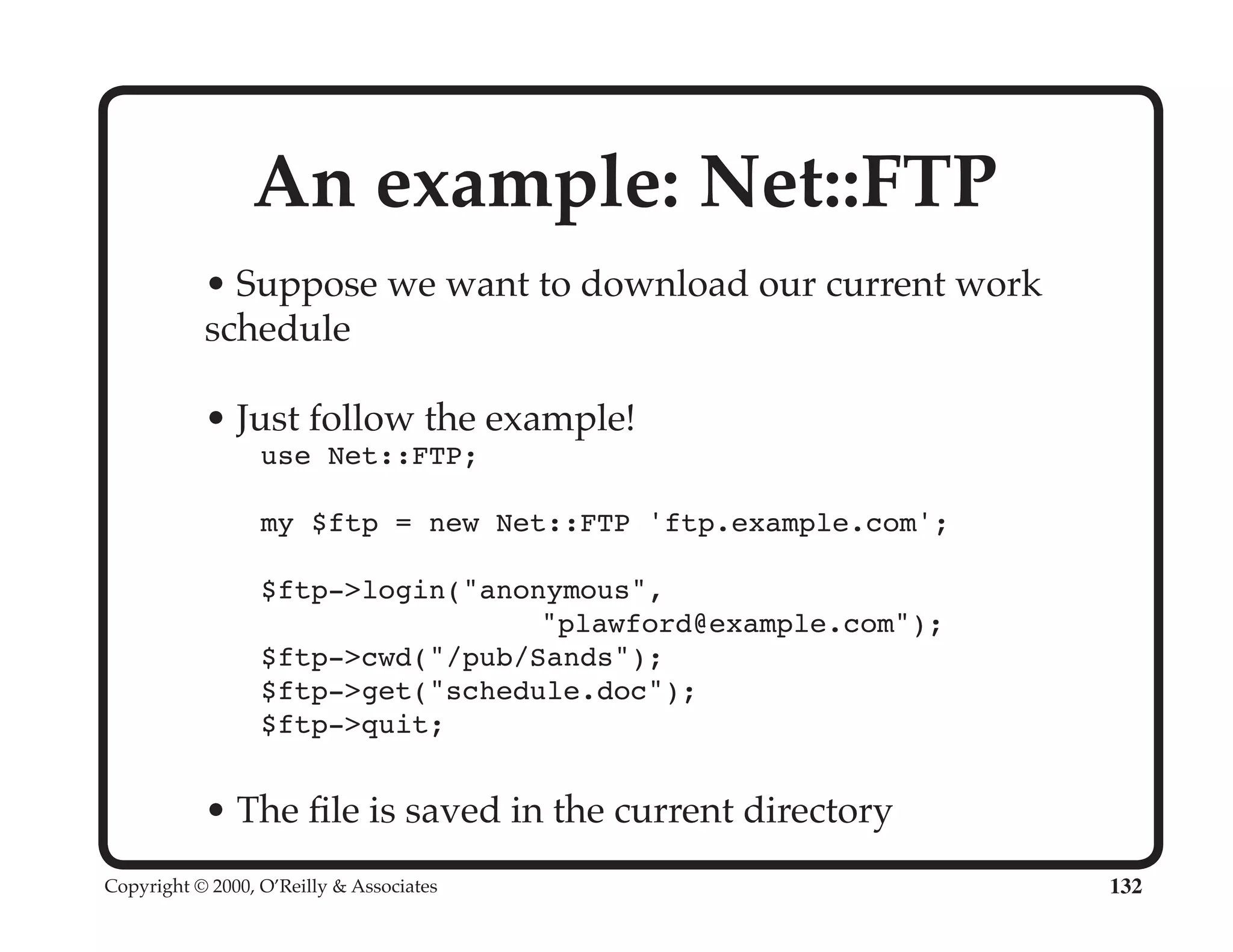
This document provides an overview and introduction to the Perl programming language. It discusses what Perl is, its history and origins, why it is useful, how to get and install Perl, where to find Perl documentation and information, the basics of Perl scripts and programs, Perl data types including scalars, numbers, strings, lists and arrays, variables, and control structures. The document is intended to give attendees of a two-day Perl University course a brief tour and foundation in the Perl language to build upon.