Network or Perish
•Download as PPTX, PDF•
0 likes•198 views
As geeks we often get stranded in our cubes. This presentation gives you variety of ways in which you can Network, Network successfully and market yourself.
Report
Share
Report
Share
Recommended
Network or perish

As IT personnel, we tend to get boxed-in, stranded on our own little island. We fail to make people aware of our activities, both within our own organization and in our wider professional circles. Just like a shipwrecked captain waiting for the rescue boat on a desert island, if you fail to communicate, your career will be stuck with no possibility of progression. This presentation will show you how to leverage networking and self-marketing techniques that will allow you to set sail off the island and into new opportunities. http://wcompute.org/2012/05/19/review-of-sqlsaturday-142-network-or-perish/
Session Level: Beginner
Paresh Motiwala
Paresh Motiwala is a Microsoft SQL Database Administrator with Bingham McCutchen in Boston. He has presented SQL topics at various forums. Paresh engages in public speaking on a variety of topics and trains children in the same art. He also does occasional standup comedy. True to Paresh's networking passion, he can be contacted at , http://gplus.to/pareshmotiwala, pareshmotiwala@gmail.com amongst other ways as given below.
Why DBAs shun the use of tools

Over the past many years, I have only come across very limited DBAs who actually openly admit use of third party tools that make their lives easier. Otherwise most DBAs find pleasure in writing complex queries to do routine stuff like backups, maintenance, monitoring; you name it.
I would like to share my experience as a DBA, where I have used tools unashamedly to improve my productivity.
Hopefully after this session, you will find the same confidence in using third party tools. Then, use the time saved, to enhance your career.
Big data 101

This document provides an overview and introduction to big data concepts presented by Paresh Motiwala for the New England SQL Server group. The presentation covers sources of big data, privacy concerns, storing data in Hadoop, processing data with MapReduce, and using tools like R, Python, and Power BI for analysis and visualization. It defines key big data concepts like the 5 V's and discusses challenges like volume, variety and velocity of data. It also summarizes strategies for companies to develop their data and cloud capabilities.
Tempdb, More permanent than you think

The document discusses tempdb, a system database in SQL Server that is used to store temporary objects. It covers topics like restrictions on tempdb, what takes up space in tempdb such as queries and triggers, best practices for allocating and configuring tempdb files, using trace flags to improve performance, minimizing usage of tempdb to avoid contention, and tips for correctly configuring tempdb.
Tempdb3

Tempdb is more permanent than one may think. The document discusses various aspects of Tempdb including its birth and initial configuration, restrictions, what takes up space in Tempdb such as queries and triggers, performance improvements in SQL Server 2016 including new trace flags, best practices for configuring Tempdb such as number of files, minimizing Tempdb utilization, and tips for backing up and restoring Tempdb. The document provides an agenda for a training session on managing and optimizing Tempdb.
Copy data management

Do you know what Copy Data is? Do you know how it consumes your life? You should know, how 1TB of database can translate to almost 2PB. What if you have to restore these databases; at the drop of a hat. This chat helps you do it.
Copy data management

This document discusses copy data management and provides an overview of copy data. It defines copy data as copies of production databases used for disaster recovery, development/testing, business intelligence, and archiving. The document then discusses the challenges of "copy data sprawl" and compares various methods for obtaining copy data like replication, log shipping, mirroring, snapshots, and copy data virtualization. Key advantages and disadvantages of each method are provided. The document concludes with a bibliography and invitation for questions.
Georgia's Marsh and Swamp Habitat

The document describes the swamp and marsh habitat in southeast Georgia, focusing on the Okefenokee Swamp. It discusses how alligators, herons, pitcher plants, water lilies, and cypress trees are well-suited to thrive in the hot, humid climate with abundant fresh and brackish water. Key adaptations include coloration that provides camouflage, physical traits like webbed feet and bills that aid in movement through water and catching prey, and physiological adaptations like roots that can grow submerged or above water. The soft soil is nutrient-poor, so some plants obtain nutrients by trapping and digesting insects.
Recommended
Network or perish

As IT personnel, we tend to get boxed-in, stranded on our own little island. We fail to make people aware of our activities, both within our own organization and in our wider professional circles. Just like a shipwrecked captain waiting for the rescue boat on a desert island, if you fail to communicate, your career will be stuck with no possibility of progression. This presentation will show you how to leverage networking and self-marketing techniques that will allow you to set sail off the island and into new opportunities. http://wcompute.org/2012/05/19/review-of-sqlsaturday-142-network-or-perish/
Session Level: Beginner
Paresh Motiwala
Paresh Motiwala is a Microsoft SQL Database Administrator with Bingham McCutchen in Boston. He has presented SQL topics at various forums. Paresh engages in public speaking on a variety of topics and trains children in the same art. He also does occasional standup comedy. True to Paresh's networking passion, he can be contacted at , http://gplus.to/pareshmotiwala, pareshmotiwala@gmail.com amongst other ways as given below.
Why DBAs shun the use of tools

Over the past many years, I have only come across very limited DBAs who actually openly admit use of third party tools that make their lives easier. Otherwise most DBAs find pleasure in writing complex queries to do routine stuff like backups, maintenance, monitoring; you name it.
I would like to share my experience as a DBA, where I have used tools unashamedly to improve my productivity.
Hopefully after this session, you will find the same confidence in using third party tools. Then, use the time saved, to enhance your career.
Big data 101

This document provides an overview and introduction to big data concepts presented by Paresh Motiwala for the New England SQL Server group. The presentation covers sources of big data, privacy concerns, storing data in Hadoop, processing data with MapReduce, and using tools like R, Python, and Power BI for analysis and visualization. It defines key big data concepts like the 5 V's and discusses challenges like volume, variety and velocity of data. It also summarizes strategies for companies to develop their data and cloud capabilities.
Tempdb, More permanent than you think

The document discusses tempdb, a system database in SQL Server that is used to store temporary objects. It covers topics like restrictions on tempdb, what takes up space in tempdb such as queries and triggers, best practices for allocating and configuring tempdb files, using trace flags to improve performance, minimizing usage of tempdb to avoid contention, and tips for correctly configuring tempdb.
Tempdb3

Tempdb is more permanent than one may think. The document discusses various aspects of Tempdb including its birth and initial configuration, restrictions, what takes up space in Tempdb such as queries and triggers, performance improvements in SQL Server 2016 including new trace flags, best practices for configuring Tempdb such as number of files, minimizing Tempdb utilization, and tips for backing up and restoring Tempdb. The document provides an agenda for a training session on managing and optimizing Tempdb.
Copy data management

Do you know what Copy Data is? Do you know how it consumes your life? You should know, how 1TB of database can translate to almost 2PB. What if you have to restore these databases; at the drop of a hat. This chat helps you do it.
Copy data management

This document discusses copy data management and provides an overview of copy data. It defines copy data as copies of production databases used for disaster recovery, development/testing, business intelligence, and archiving. The document then discusses the challenges of "copy data sprawl" and compares various methods for obtaining copy data like replication, log shipping, mirroring, snapshots, and copy data virtualization. Key advantages and disadvantages of each method are provided. The document concludes with a bibliography and invitation for questions.
Georgia's Marsh and Swamp Habitat

The document describes the swamp and marsh habitat in southeast Georgia, focusing on the Okefenokee Swamp. It discusses how alligators, herons, pitcher plants, water lilies, and cypress trees are well-suited to thrive in the hot, humid climate with abundant fresh and brackish water. Key adaptations include coloration that provides camouflage, physical traits like webbed feet and bills that aid in movement through water and catching prey, and physiological adaptations like roots that can grow submerged or above water. The soft soil is nutrient-poor, so some plants obtain nutrients by trapping and digesting insects.
PENETRATION TESTING FROM A HOT TUB TIME MACHINE

This presentation discusses penetration testing techniques from an unconventional perspective. It advocates for intelligence gathering and footprinting before scanning or exploitation to have a more effective assessment. Specific techniques discussed include using open source intelligence gathering on internal and external systems to develop profiles and target lists. Footprinting activities within the network focus on enumeration of users, shares, services and other details to identify vulnerable systems rather than broad scanning. The presentation provides examples of exploiting old vulnerabilities in applications like Citrix and weaknesses in administration interfaces. It emphasizes continuing post-exploitation activities like privilege escalation and lateral movement within compromised systems to fully evaluate security.
Systems Administrator As A Career

Matt Arnilo S. Baluyos graduated with a BS in Computer Science and works as a Systems Administrator for an Australian telecommunications company. A typical day involves technical support, provisioning new servers and services, monitoring infrastructure, and research projects. As a SysAd, it is important to be trustworthy, reliable, responsive, document everything, backup regularly, automate repetitive tasks, and continuously learn. The career offers challenges, opportunities to learn, feeling of purpose when issues are resolved, and potential for travel and compensation.
NotaCon 2011 - Networking for Pentesters

This document provides introductions and background information for two presenters, JP Bourget and Rob Fuller, for a presentation on networking for pentesters. JP Bourget has a background in IT, computer security and information assurance. He currently works in network and security management and also teaches networking and security classes. Rob Fuller has 10 years experience in information security and IT, including work as a network attack operator and penetration tester. The presentation agenda includes topics like networking, information operations, vulnerability hunting, exploitation, persistence and pivoting.
Scale-Free Organizations: A Sober View, Some History, and How to Make One

Most organizations use a primarily hierarchical organization structure to organize their scaled populations. These organizations cannot be agile without adding additional connections between interdependent nodes. Hubs and scale-free networks offer a solution, and we find them in traditional structures usually associated with peripheral or vestigial concerns.
Password Management

A discussion of the problems with password security and how to make your passwords more secure. Also, we debunk some common myths about what makes a good password. (This was originally part one of a three part presentation on the need for and use of password managers.)
Applying Machine Learning to Network Security Monitoring - BayThreat 2013

Video (at YouTube) - http://bit.ly/19TNSTF
Big Data Security Analytics, Data Science and Machine Learning are a few of the new buzzwords that have invaded out industry of late. Most of what we hear are promises of an unicorn-laden, silver-bullet panacea by heavy-handed marketing folks, evoking an expected pushback from the most enlightened members of our community.
This talk will help parse what we as a community need to know and understand about these concepts and help understand where the technical details and actual capabilities of those concepts and also where they fail and how they can be exploited and fooled by an attacker.
The talk will also share results of the author's current ongoing research (on MLSec Project) of applying machine learning techniques to information secuirty monitoring.
Hunt for the red DA

Part one of the DA trilogy
Presented at BSides 2017 Edinburgh presentation
The Hunt For The Red DA by Neil Lines https://youtu.be/pYErty7a5M8
Black opspki 2

This document summarizes Dan Kaminsky's talk on the weaknesses of the X.509 public key infrastructure (PKI) system. Kaminsky argues that X.509 cannot adequately exclude unauthorized certificate authorities, delegate authority without pain, or protect against cryptographic vulnerabilities like insecure hashing functions still in use. Specifically, he notes one of Verisign's root certificates is self-signed using the insecure MD2 hashing algorithm, allowing for the potential creation of a malicious intermediate certificate using a preimage attack.
Corp Web Risks and Concerns

The document discusses various risks facing organizations with a web presence and provides recommendations to address those risks. It identifies issues such as security vulnerabilities, privacy concerns, social media risks, and analytics inaccuracies. It recommends that organizations conduct security audits, monitor their websites for hackability, disclose any required information, and stay aware of their site's performance, uptime, and what search engines are indexing about them.
Investigating Using the Dark Web

Most investigators turn to Google and common social media platforms such as Facebook and Twitter to conduct research for their investigations. However, much of the Internet is inaccessible through simple searches, and criminals are increasingly turning to the dark web to conduct illicit business.
The dark web is anonymous and requires a special browser to access and some knowledge of how to navigate it safely. However, used properly, it can be a valuable source of information for investigators. It’s worthwhile for every investigator to develop the skills and knowledge to mine this treasure trove of dark data.
Join Chad Los Schumacher, investigator and researcher at iThreat Cyber Group, as he leads participants on an exploration of investigations in the dark web.
Webinar attendees will learn:
What the dark web is and how it fits into the rest of the worldwide web
What can be found on the dark web
How to get to the dark web using Tor and other browsers
How to locate common hubs and resources on the dark web and explore what they have to offer
How to bring leads from the dark web to the surface in an investigation
Big data in the cloud - Shekhar Vemuri

Big Data and the Cloud discusses how big data and cloud computing can be combined. It provides examples of how Amazon Web Services products like S3, EC2, EMR, and Redshift can be used together in a data pipeline to store log files, run analytics via MapReduce jobs, and store summarized results. The cloud allows on-demand flexibility but costs must be carefully managed.
Getting involved in network security

This document provides advice for getting involved in network security. It recommends gaining skills through hands-on experience with tools like BackTrack and Metasploitable, blogging about projects, listening to security podcasts, and participating in security challenges. It also suggests using skills by finding problems with other people's research and tools. Finally, it advises talking to people in the security field, attending local meetups, and asking professors about contacts and internships. The overall goals are to continuously build practical skills and make connections in the industry.
Idiots guide to setting up a data science team

Some nuggets of how I started the data science practice at Gale Partners on a budget. Presented at the Toronto Hadoop Users Group (THUG) in April, 2015.
Web 2.0 for ACU

The document introduces the concept of Web 2.0, which emphasizes easy and instant publishing that allows users to connect ideas. Web 2.0 shifts software to the cloud and focuses on people rather than code. It discusses how Web 2.0 changes formal learning spaces to be more informal and collaborative, moving from a "sage on stage" model to peer learning. The document provides 10 things to try with Web 2.0 technologies like sharing content online, using instant messaging, blogging, and customizing homepages.
PyData Texas 2015 Keynote

This document summarizes Peter Wang's keynote speech at PyData Texas 2015. It begins by looking back at the history and growth of PyData conferences over the past 3 years. It then discusses some of the main data science challenges companies currently face. The rest of the speech focuses on the role of Python in data science, how the technology landscape has evolved, and PyData's mission to empower scientists to explore, analyze, and share their data.
Big Data Rampage

Presentation for the 45 min. + QA talk I gave at HIIT seminar on 13 May 2013 for local data science researchers.
Testing in Legacy: from Rags to Riches by Taras Slipets

In this presentation I'd like to share practical experience and techniques that were used for modernization and maintaining 10+ years old legacy system: pitfalls that we've faced during that process and conclusions that we'd made when we've successfully finished updating mission.
Testing in Legacy: From Rags to Riches

The document describes the experience of improving a legacy system that was 11 years old and written in Java 1.4 without frameworks or documentation. The key steps taken included: setting up testing environments; modeling the domain, workflows and database; conducting peer reviews; adding unit and integration tests; refactoring using patterns like template method and strategy; automating deployment; and adding new features where possible. Lessons learned included not underestimating classical techniques, being agile, and sharing knowledge through documentation. In the end, the improvements resulted in a system with reduced maintenance pain and an automated build pipeline.
A Technical Dive into Defensive Trickery

This document discusses various techniques for improving security and making it easier to deploy. It begins by introducing Dan Kaminsky and the goal of challenging assumptions. It then discusses how security is often hard to implement due to challenges like DDoS attacks being hard to remediate, TLS being difficult to deploy properly, and data loss prevention during attacks. The document proposes several solutions to these challenges, including Overflowd to help trace DDoS attacks, JFE to automatically provision TLS for all network services, and Ratelock to enforce access policies like rate limits in the cloud even if servers are compromised. It argues that moving enforcement to the cloud can improve security. The document concludes by noting that running code safely through sandboxing is also difficult but
Osint

This document discusses open source intelligence (OSINT) and how it can be used to gather information from publicly available sources to produce actionable intelligence. It provides examples of how OSINT can be used for corporate security purposes like finding breaches, leaked credentials, or rogue employees. It also lists several tools that can be used for OSINT like Robtex, PassiveRecon, Maltego, GeoStalker, and FBStalker. It notes that while OSINT is not always actively used by penetration testers, it can provide valuable information when applied to a real pentest. The document emphasizes that OSINT is more than just manual data gathering and that understanding what attackers know about an organization is important.
More Related Content
Similar to Network or Perish
PENETRATION TESTING FROM A HOT TUB TIME MACHINE

This presentation discusses penetration testing techniques from an unconventional perspective. It advocates for intelligence gathering and footprinting before scanning or exploitation to have a more effective assessment. Specific techniques discussed include using open source intelligence gathering on internal and external systems to develop profiles and target lists. Footprinting activities within the network focus on enumeration of users, shares, services and other details to identify vulnerable systems rather than broad scanning. The presentation provides examples of exploiting old vulnerabilities in applications like Citrix and weaknesses in administration interfaces. It emphasizes continuing post-exploitation activities like privilege escalation and lateral movement within compromised systems to fully evaluate security.
Systems Administrator As A Career

Matt Arnilo S. Baluyos graduated with a BS in Computer Science and works as a Systems Administrator for an Australian telecommunications company. A typical day involves technical support, provisioning new servers and services, monitoring infrastructure, and research projects. As a SysAd, it is important to be trustworthy, reliable, responsive, document everything, backup regularly, automate repetitive tasks, and continuously learn. The career offers challenges, opportunities to learn, feeling of purpose when issues are resolved, and potential for travel and compensation.
NotaCon 2011 - Networking for Pentesters

This document provides introductions and background information for two presenters, JP Bourget and Rob Fuller, for a presentation on networking for pentesters. JP Bourget has a background in IT, computer security and information assurance. He currently works in network and security management and also teaches networking and security classes. Rob Fuller has 10 years experience in information security and IT, including work as a network attack operator and penetration tester. The presentation agenda includes topics like networking, information operations, vulnerability hunting, exploitation, persistence and pivoting.
Scale-Free Organizations: A Sober View, Some History, and How to Make One

Most organizations use a primarily hierarchical organization structure to organize their scaled populations. These organizations cannot be agile without adding additional connections between interdependent nodes. Hubs and scale-free networks offer a solution, and we find them in traditional structures usually associated with peripheral or vestigial concerns.
Password Management

A discussion of the problems with password security and how to make your passwords more secure. Also, we debunk some common myths about what makes a good password. (This was originally part one of a three part presentation on the need for and use of password managers.)
Applying Machine Learning to Network Security Monitoring - BayThreat 2013

Video (at YouTube) - http://bit.ly/19TNSTF
Big Data Security Analytics, Data Science and Machine Learning are a few of the new buzzwords that have invaded out industry of late. Most of what we hear are promises of an unicorn-laden, silver-bullet panacea by heavy-handed marketing folks, evoking an expected pushback from the most enlightened members of our community.
This talk will help parse what we as a community need to know and understand about these concepts and help understand where the technical details and actual capabilities of those concepts and also where they fail and how they can be exploited and fooled by an attacker.
The talk will also share results of the author's current ongoing research (on MLSec Project) of applying machine learning techniques to information secuirty monitoring.
Hunt for the red DA

Part one of the DA trilogy
Presented at BSides 2017 Edinburgh presentation
The Hunt For The Red DA by Neil Lines https://youtu.be/pYErty7a5M8
Black opspki 2

This document summarizes Dan Kaminsky's talk on the weaknesses of the X.509 public key infrastructure (PKI) system. Kaminsky argues that X.509 cannot adequately exclude unauthorized certificate authorities, delegate authority without pain, or protect against cryptographic vulnerabilities like insecure hashing functions still in use. Specifically, he notes one of Verisign's root certificates is self-signed using the insecure MD2 hashing algorithm, allowing for the potential creation of a malicious intermediate certificate using a preimage attack.
Corp Web Risks and Concerns

The document discusses various risks facing organizations with a web presence and provides recommendations to address those risks. It identifies issues such as security vulnerabilities, privacy concerns, social media risks, and analytics inaccuracies. It recommends that organizations conduct security audits, monitor their websites for hackability, disclose any required information, and stay aware of their site's performance, uptime, and what search engines are indexing about them.
Investigating Using the Dark Web

Most investigators turn to Google and common social media platforms such as Facebook and Twitter to conduct research for their investigations. However, much of the Internet is inaccessible through simple searches, and criminals are increasingly turning to the dark web to conduct illicit business.
The dark web is anonymous and requires a special browser to access and some knowledge of how to navigate it safely. However, used properly, it can be a valuable source of information for investigators. It’s worthwhile for every investigator to develop the skills and knowledge to mine this treasure trove of dark data.
Join Chad Los Schumacher, investigator and researcher at iThreat Cyber Group, as he leads participants on an exploration of investigations in the dark web.
Webinar attendees will learn:
What the dark web is and how it fits into the rest of the worldwide web
What can be found on the dark web
How to get to the dark web using Tor and other browsers
How to locate common hubs and resources on the dark web and explore what they have to offer
How to bring leads from the dark web to the surface in an investigation
Big data in the cloud - Shekhar Vemuri

Big Data and the Cloud discusses how big data and cloud computing can be combined. It provides examples of how Amazon Web Services products like S3, EC2, EMR, and Redshift can be used together in a data pipeline to store log files, run analytics via MapReduce jobs, and store summarized results. The cloud allows on-demand flexibility but costs must be carefully managed.
Getting involved in network security

This document provides advice for getting involved in network security. It recommends gaining skills through hands-on experience with tools like BackTrack and Metasploitable, blogging about projects, listening to security podcasts, and participating in security challenges. It also suggests using skills by finding problems with other people's research and tools. Finally, it advises talking to people in the security field, attending local meetups, and asking professors about contacts and internships. The overall goals are to continuously build practical skills and make connections in the industry.
Idiots guide to setting up a data science team

Some nuggets of how I started the data science practice at Gale Partners on a budget. Presented at the Toronto Hadoop Users Group (THUG) in April, 2015.
Web 2.0 for ACU

The document introduces the concept of Web 2.0, which emphasizes easy and instant publishing that allows users to connect ideas. Web 2.0 shifts software to the cloud and focuses on people rather than code. It discusses how Web 2.0 changes formal learning spaces to be more informal and collaborative, moving from a "sage on stage" model to peer learning. The document provides 10 things to try with Web 2.0 technologies like sharing content online, using instant messaging, blogging, and customizing homepages.
PyData Texas 2015 Keynote

This document summarizes Peter Wang's keynote speech at PyData Texas 2015. It begins by looking back at the history and growth of PyData conferences over the past 3 years. It then discusses some of the main data science challenges companies currently face. The rest of the speech focuses on the role of Python in data science, how the technology landscape has evolved, and PyData's mission to empower scientists to explore, analyze, and share their data.
Big Data Rampage

Presentation for the 45 min. + QA talk I gave at HIIT seminar on 13 May 2013 for local data science researchers.
Testing in Legacy: from Rags to Riches by Taras Slipets

In this presentation I'd like to share practical experience and techniques that were used for modernization and maintaining 10+ years old legacy system: pitfalls that we've faced during that process and conclusions that we'd made when we've successfully finished updating mission.
Testing in Legacy: From Rags to Riches

The document describes the experience of improving a legacy system that was 11 years old and written in Java 1.4 without frameworks or documentation. The key steps taken included: setting up testing environments; modeling the domain, workflows and database; conducting peer reviews; adding unit and integration tests; refactoring using patterns like template method and strategy; automating deployment; and adding new features where possible. Lessons learned included not underestimating classical techniques, being agile, and sharing knowledge through documentation. In the end, the improvements resulted in a system with reduced maintenance pain and an automated build pipeline.
A Technical Dive into Defensive Trickery

This document discusses various techniques for improving security and making it easier to deploy. It begins by introducing Dan Kaminsky and the goal of challenging assumptions. It then discusses how security is often hard to implement due to challenges like DDoS attacks being hard to remediate, TLS being difficult to deploy properly, and data loss prevention during attacks. The document proposes several solutions to these challenges, including Overflowd to help trace DDoS attacks, JFE to automatically provision TLS for all network services, and Ratelock to enforce access policies like rate limits in the cloud even if servers are compromised. It argues that moving enforcement to the cloud can improve security. The document concludes by noting that running code safely through sandboxing is also difficult but
Osint

This document discusses open source intelligence (OSINT) and how it can be used to gather information from publicly available sources to produce actionable intelligence. It provides examples of how OSINT can be used for corporate security purposes like finding breaches, leaked credentials, or rogue employees. It also lists several tools that can be used for OSINT like Robtex, PassiveRecon, Maltego, GeoStalker, and FBStalker. It notes that while OSINT is not always actively used by penetration testers, it can provide valuable information when applied to a real pentest. The document emphasizes that OSINT is more than just manual data gathering and that understanding what attackers know about an organization is important.
Similar to Network or Perish (20)
Scale-Free Organizations: A Sober View, Some History, and How to Make One

Scale-Free Organizations: A Sober View, Some History, and How to Make One
Applying Machine Learning to Network Security Monitoring - BayThreat 2013

Applying Machine Learning to Network Security Monitoring - BayThreat 2013
Testing in Legacy: from Rags to Riches by Taras Slipets

Testing in Legacy: from Rags to Riches by Taras Slipets
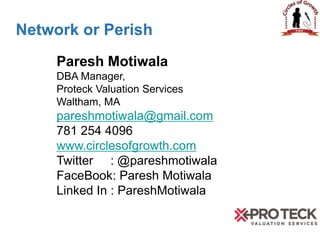
Network or Perish
- 1. Network or Perish Paresh Motiwala DBA Manager, Proteck Valuation Services Waltham, MA pareshmotiwala@gmail.com 781 254 4096 www.circlesofgrowth.com Twitter : @pareshmotiwala FaceBook: Paresh Motiwala Linked In : PareshMotiwala
- 2. Network or Perish Other Topics: • Setting up your own BI Infrastructure • SQL Best Practices • From DBA to PM in 75 minutes • Copy Data Management • SSRS • SSIS • Why are DBAs afraid of tools? • Digital Forensics • Database Forensics • Discrimination • Time Management
- 4. FAMILY FUED Network Or Perish
- 5. Why Not Network? Network Or Perish
- 6. X X X X X X FOSSIL 21 SHELLS 12 JARASSIC 13 EONS 5 My boss will think.. 3 SEDIMENT 2 LAYERS 2 DX 1 5) X X X X X X 4) X X X X X X 3) X X X X X X 2) X X X X X X 1) X X X X X XNo Time (you know how it is) 43 I don’t give a sh*t 25 But, I have a job 13 Waste of time 11 I feel exposed 9 Network Or Perish 43 000
- 7. In our spare time? Network Or Perish
- 8. X X X X X X FOSSIL 21 SHELLS 12 JARASSIC 13 EONS 5 PERIOD 3 SEDIMENT 2 LAYERS 2 DX 1 5) X X X X X X 4) X X X X X X 3) X X X X X X 2) X X X X X X 1) X X X X X XGo drink in a bar 43 Watch TV 24 What spare time? 13 Watch movies 11 Play Video Games 9 Network Or Perish 43 000
- 9. Network Or Perish • Small Story---a Company goes on cruise
- 10. Network Or Perish • Small Story --- Get marooned
- 11. Network Or Perish • Small Story--- After a year, The Finance Team
- 12. Network Or Perish • Small Story --- After a year, The Marketing Team
- 13. Network Or Perish • Small Story - After a year, IT staff
- 14. Network Or Perish • Visit to the zoo
- 15. Network Or Perish • Protocols • Seven Deadly Myths of Networking. • Tools for Networking. • In Person Networking. • Marketing Yourself.
- 16. Network Or Perish • TCP/IP, Routers, NAT, Shared Memory? • Talk Less, Listen More • Don’t Sell • Show Up
- 17. Network Or Perish • Seven Deadly Myths of Networking 1. Networking means meeting as many people as you can. 2. Networking means telling people about your business whenever you get a chance. 3. Networking should start when you're job- hunting. 4. Networking is for schmoozers/brown nosers. 5. Networking is a waste of time. 6. Networking is expensive. 7. Networking is phony.
- 18. Network Or Perish • Tools • Linked In – Connected, SlideShare, Jobs, • Twitter - Lists • Facebook – Groups, Glassdoors, Pages • Blogs – Meaningful Rants • Forums – SQL Team, SQL Server Central • Google + • Snapchat • Whatsapp • Other….
- 19. Network Or Perish • In Person Networking • Volunteering • Community • Church/Place of religion • Professional groups(SSUG, Developers, PASS...) • Chambers of commerce • Sports • Meeting newer people • Your fellow commuters • Person sitting next to you at lunch table • RENs • Your Community • Sports • Old job/college reunions
- 20. Network Or Perish • Marketing Yourself • Late night work: 2 AM Emails • Presentations/Tech Talks • LinkedIn/Facebook/Tweet/Blog • Share mini successes • Corporate Citizenship • Water cooler conversations
- 21. Network Or Perish • Summary: • Don’t become islands • Declare your mini victories • Connect and stay connected • Always carry your business cards • Think outside the cube • Don’t become like these or • Discussions, Q&A
- 22. Network Or Perish • Disclaimers • No Oracle DBAs were hurt in the making of this presentation • All Characters in the small story are fictitious • You must be nuts to believe in the figures of the Family Feud • You don’t have to be tall, dark and good looking like me to effectively network
- 23. Network Or Perish THANK YOU Paresh Motiwala for President 2016
