Embed presentation
Download as PPSX, PPTX

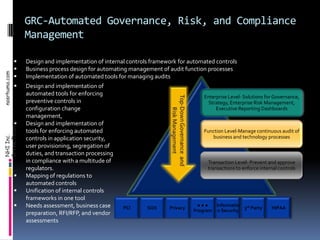
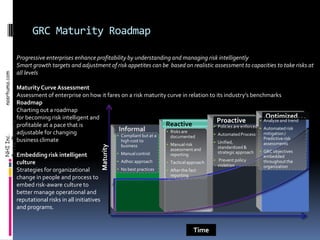
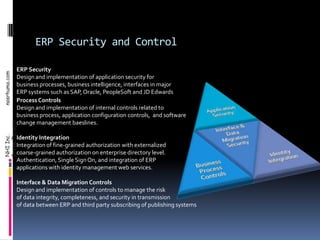
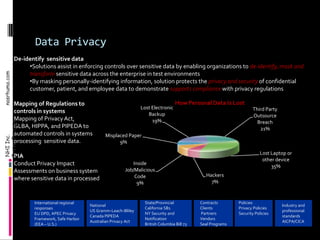

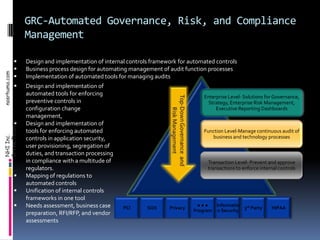
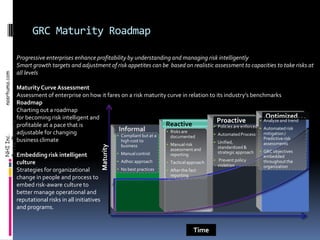
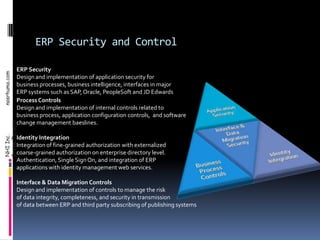
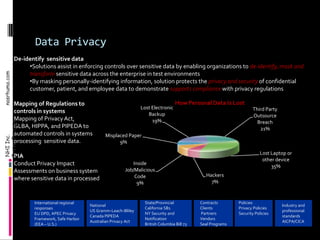
Nasrhuma Inc. provides services related to governance, risk management, and compliance (GRC). This includes: 1) Design and implementation of automated internal controls frameworks, business processes, and tools. 2) Information security services related to regulations like HIPAA, PCI, and SOX. 3) Top-down governance and risk management including maturity assessments, roadmaps, and embedding a risk culture. 4) ERP security and controls for applications like SAP, Oracle, and PeopleSoft around areas like security, processes, and interfaces. 5) Data privacy services including de-identifying sensitive data, mapping regulations to controls, and conducting privacy impact assessments.