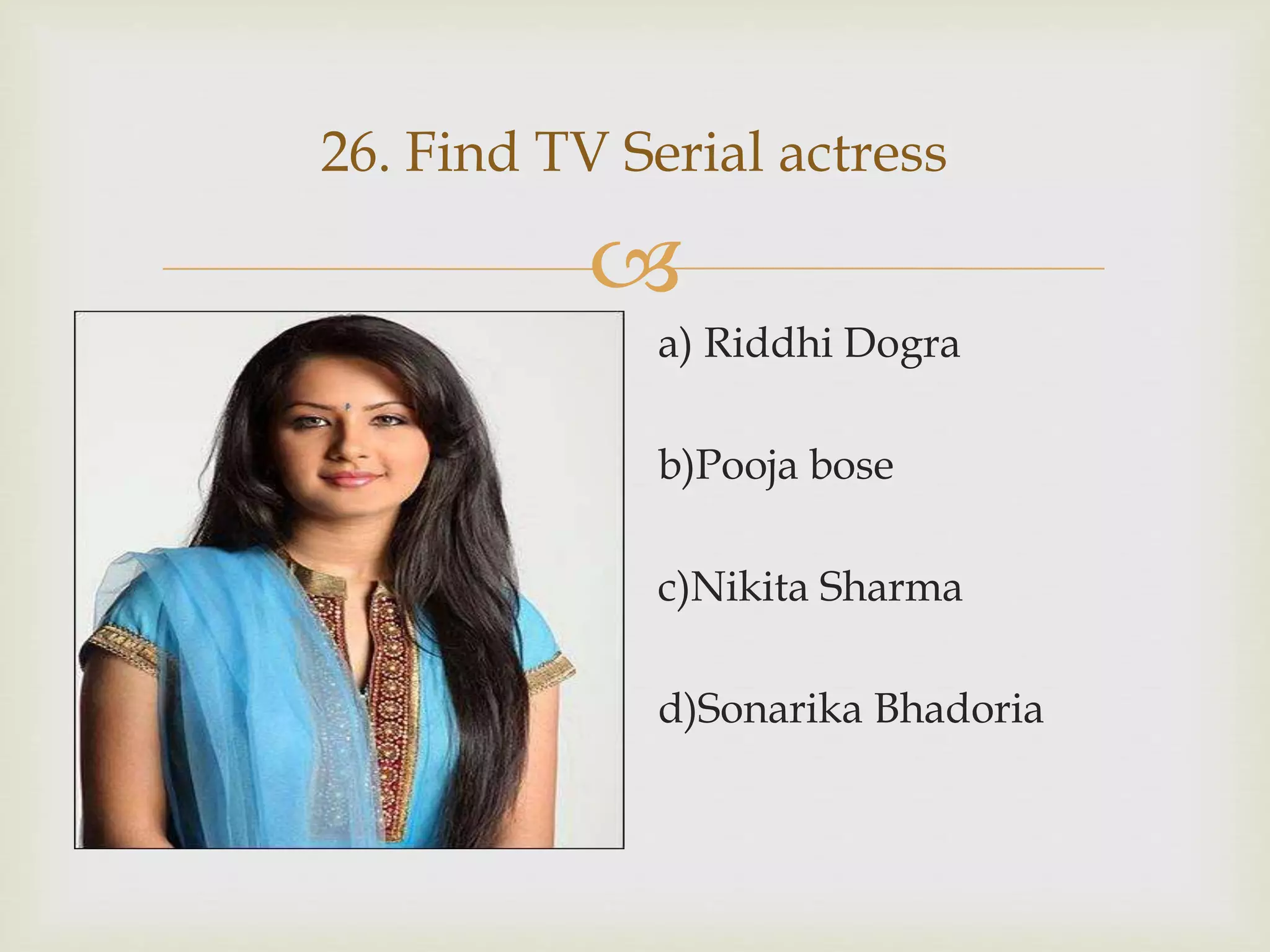
This document contains 35 multiple choice questions related to Bollywood movies, actors, actresses, songs and awards. The questions cover topics like identifying movies that certain songs or scenes appeared in, naming actors and actresses and their roles, recalling years important awards were won, and basic plot points about famous films and characters.