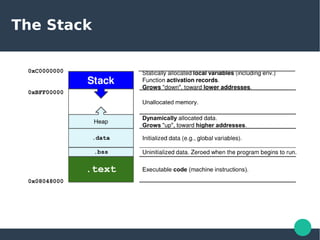
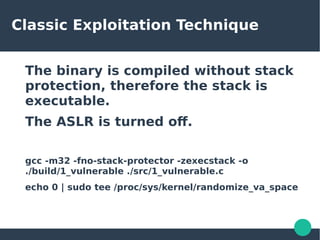
This document discusses the reverse engineering of Linux binaries, focusing on exploitation techniques like return-oriented programming (ROP) and shellcode execution. It provides essential knowledge on tools like GDB and Pedal, assembly language, and various Linux binary protections, including ASLR, NX, and stack canaries. The author, Arcangelo Saracino, is a computer science student who emphasizes the importance of C and Python in cybersecurity and reverse engineering practices.