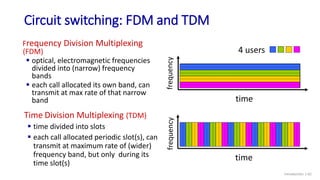
The document outlines a Computer Networks course, highlighting the objectives, key terminologies, technologies, protocols, and various network topologies. It discusses the structure of the internet, the role of different networking devices like routers and switches, and the principles of data communication. Key concepts such as wired and wireless media, communication protocols, and different types of network topologies including bus, star, ring, and tree are also covered.


















































































![Internet history
Introduction: 1-84
early 1990s: ARPAnet
decommissioned
1991: NSF lifts restrictions on
commercial use of NSFnet
(decommissioned, 1995)
early 1990s: Web
• hypertext [Bush 1945, Nelson 1960’s]
• HTML, HTTP: Berners-Lee
• 1994: Mosaic, later Netscape
• late 1990s: commercialization of the
Web
late 1990s – 2000s:
more killer apps: instant
messaging, P2P file sharing
network security to forefront
est. 50 million host, 100 million+
users
backbone links running at Gbps
1990, 2000s: commercialization, the Web, new applications](https://image.slidesharecdn.com/lec-01introduction-240427141144-4e8455c2/85/Lec-01-Introduction-Computer-Networks-84-320.jpg)

