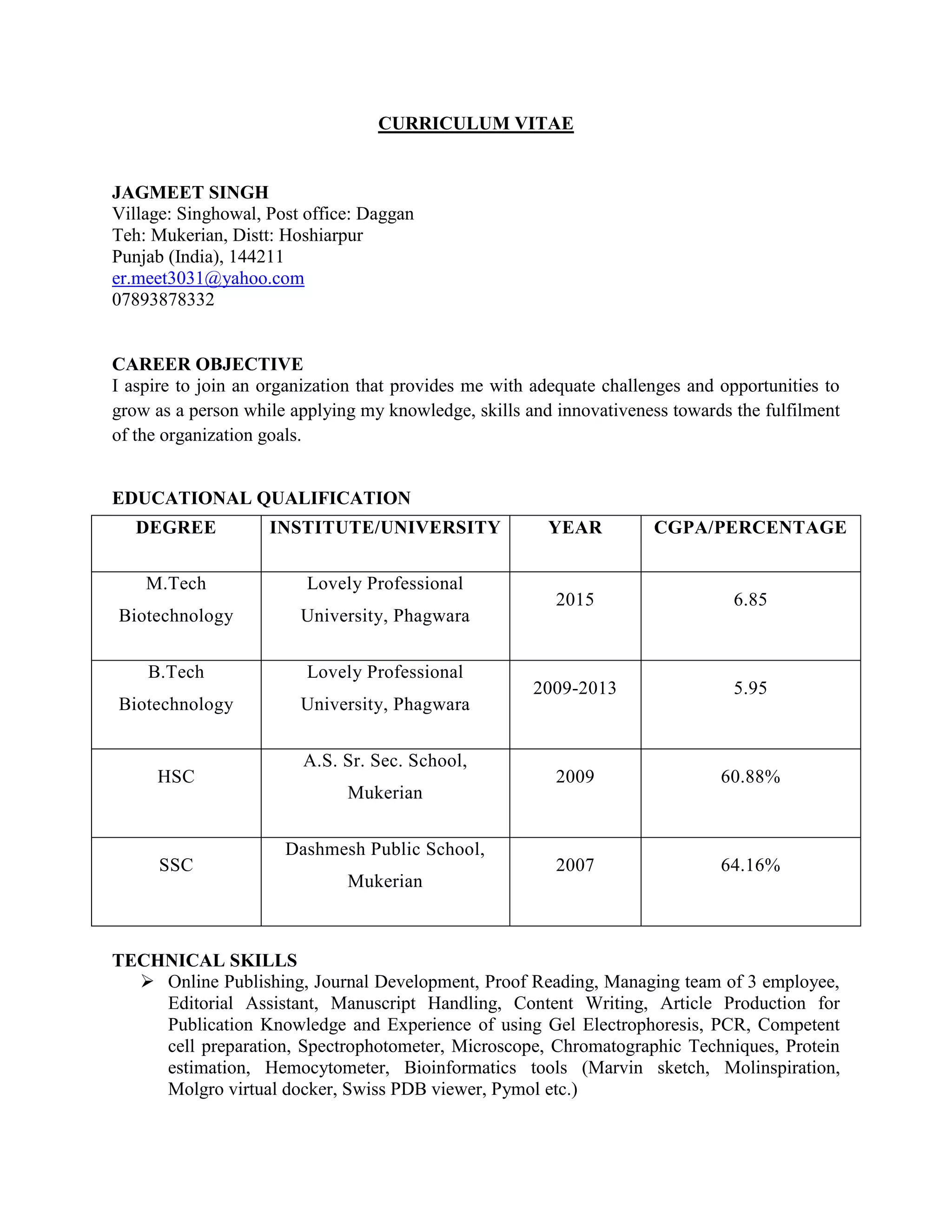
Jagmeet Singh is a biotechnology graduate with an M.Tech from Lovely Professional University, seeking a challenging position to utilize his skills and knowledge. He has experience as an Associate Managing Editor and has worked on projects related to biodiesel and bioethanol production. His technical skills include various laboratory techniques, content writing, and proficiency in bioinformatics tools, alongside strong interpersonal skills.