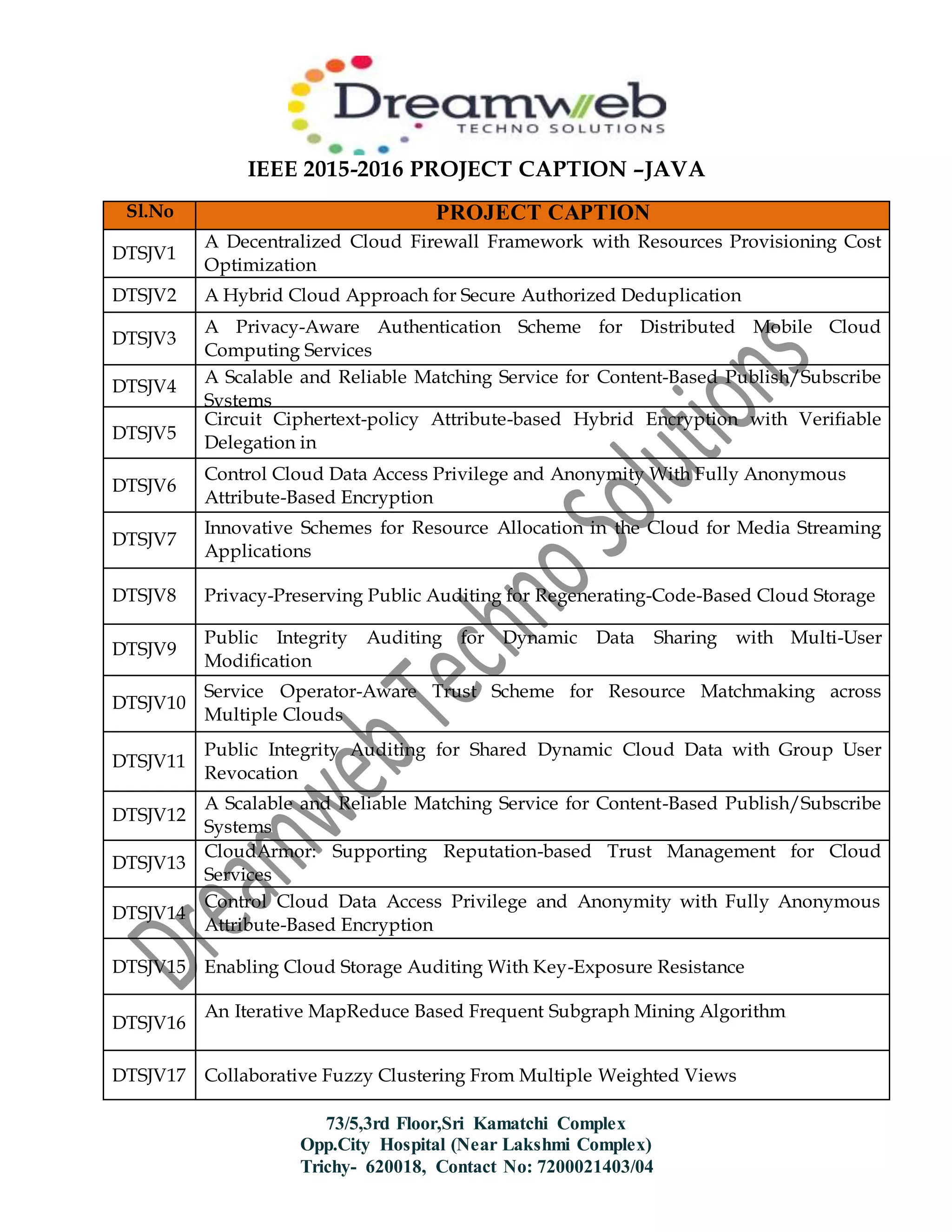
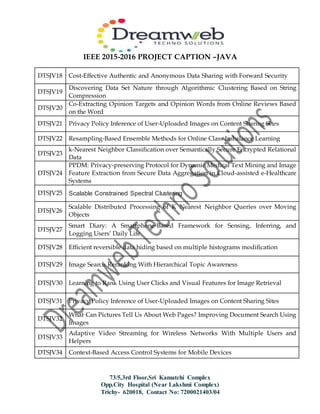
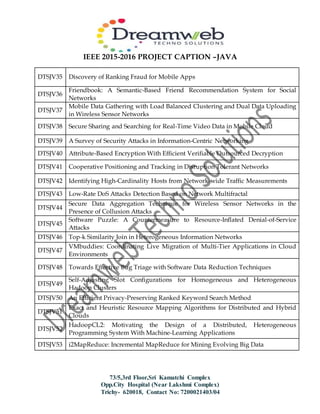
The document lists a series of project captions associated with the IEEE 2015-2016 initiative, mainly focusing on various cloud computing techniques and security measures. Projects include decentralized cloud firewalls, privacy-aware authentication schemes, resource allocation for media streaming, and context-based access control systems for mobile devices. The document serves as a comprehensive overview of innovative solutions in computer science, particularly in cloud technologies and data security.