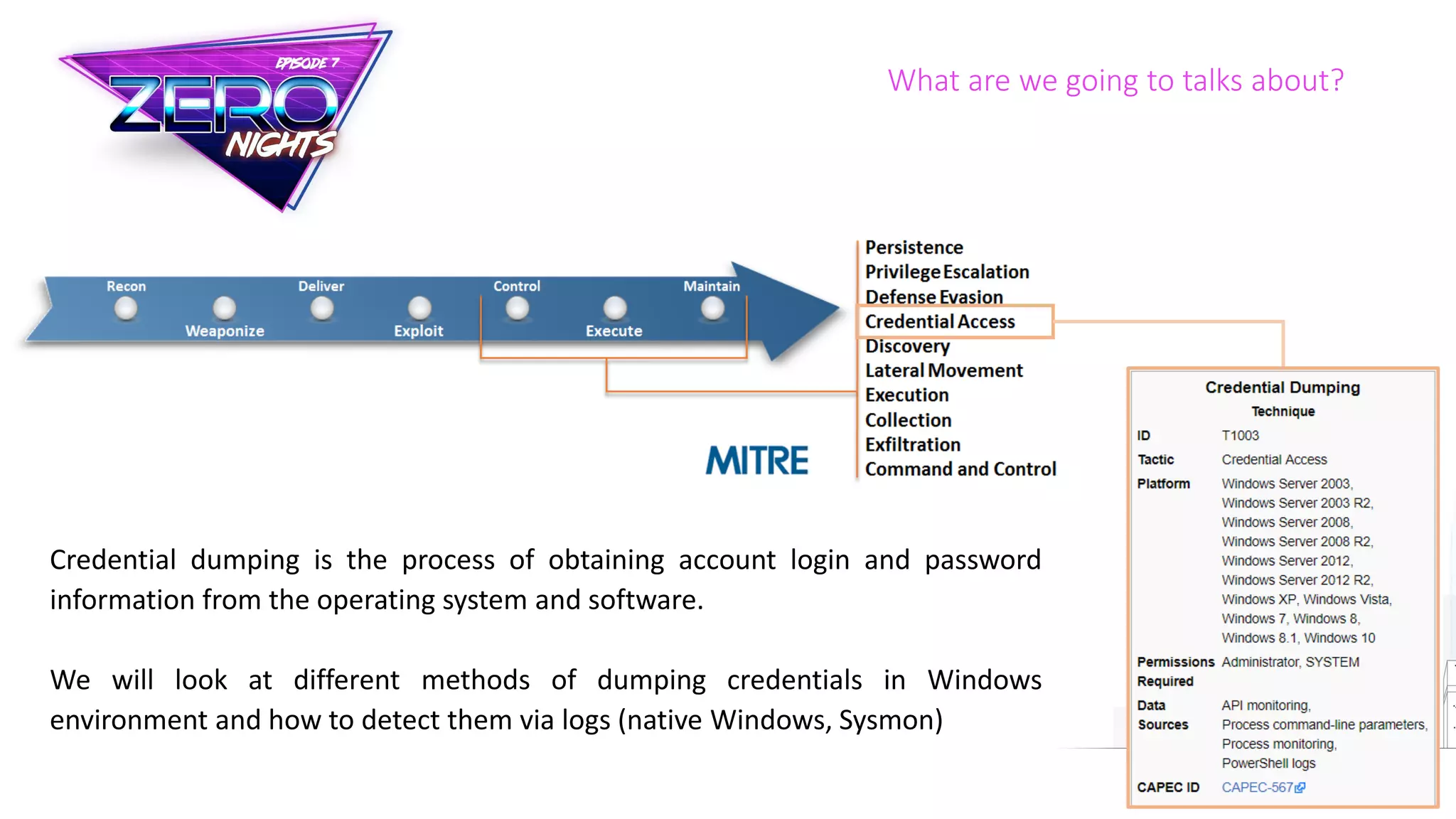
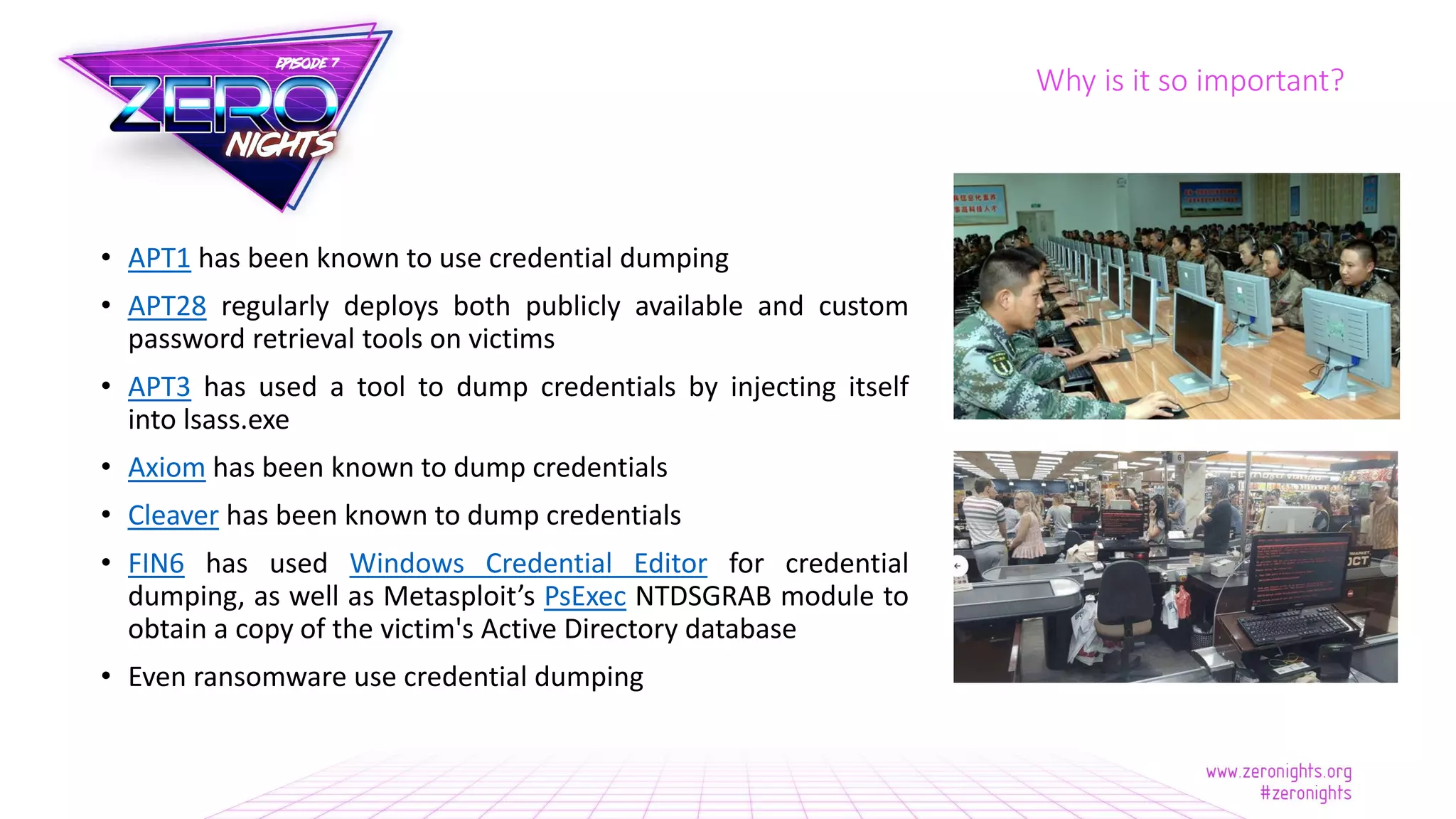
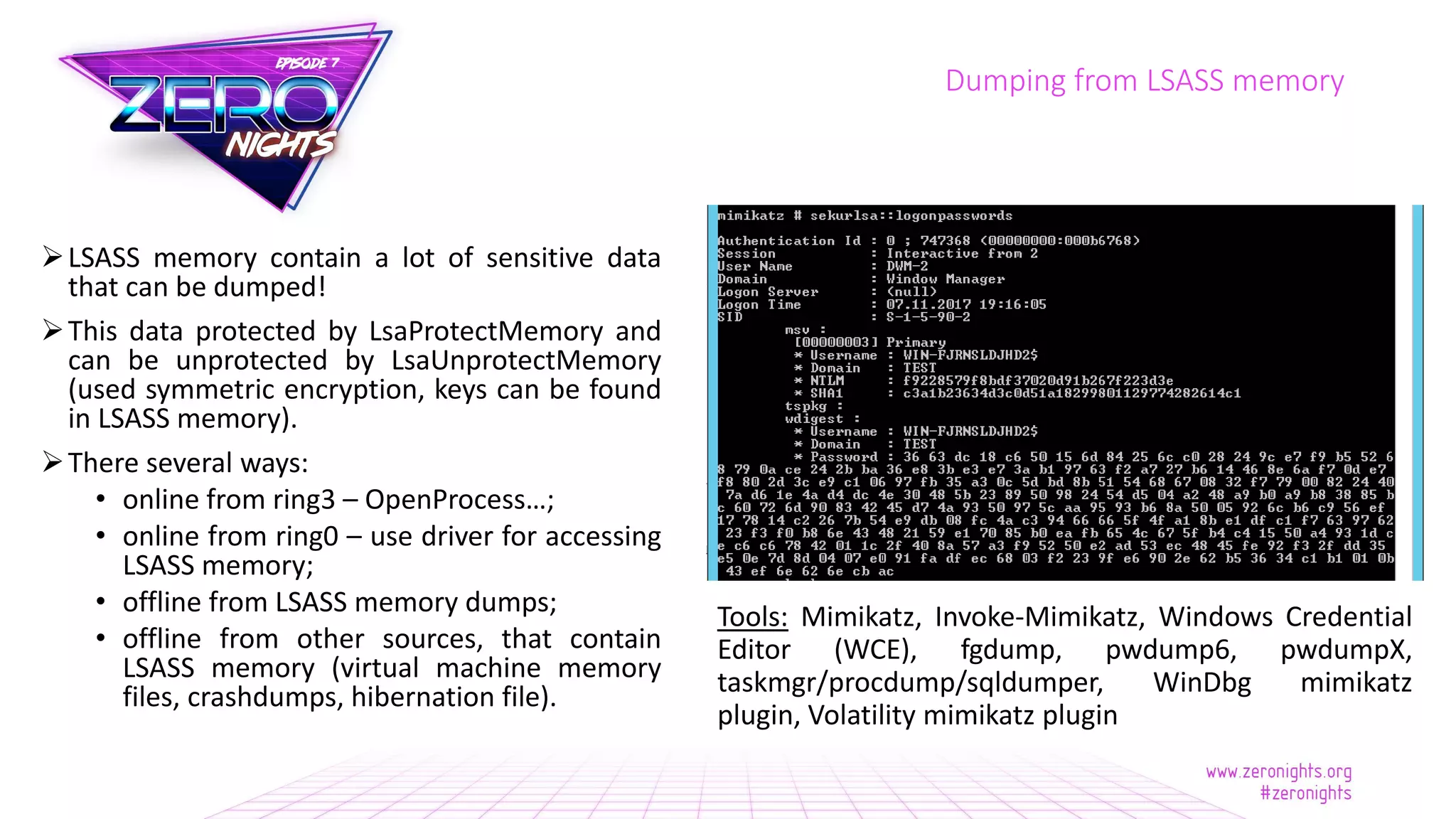
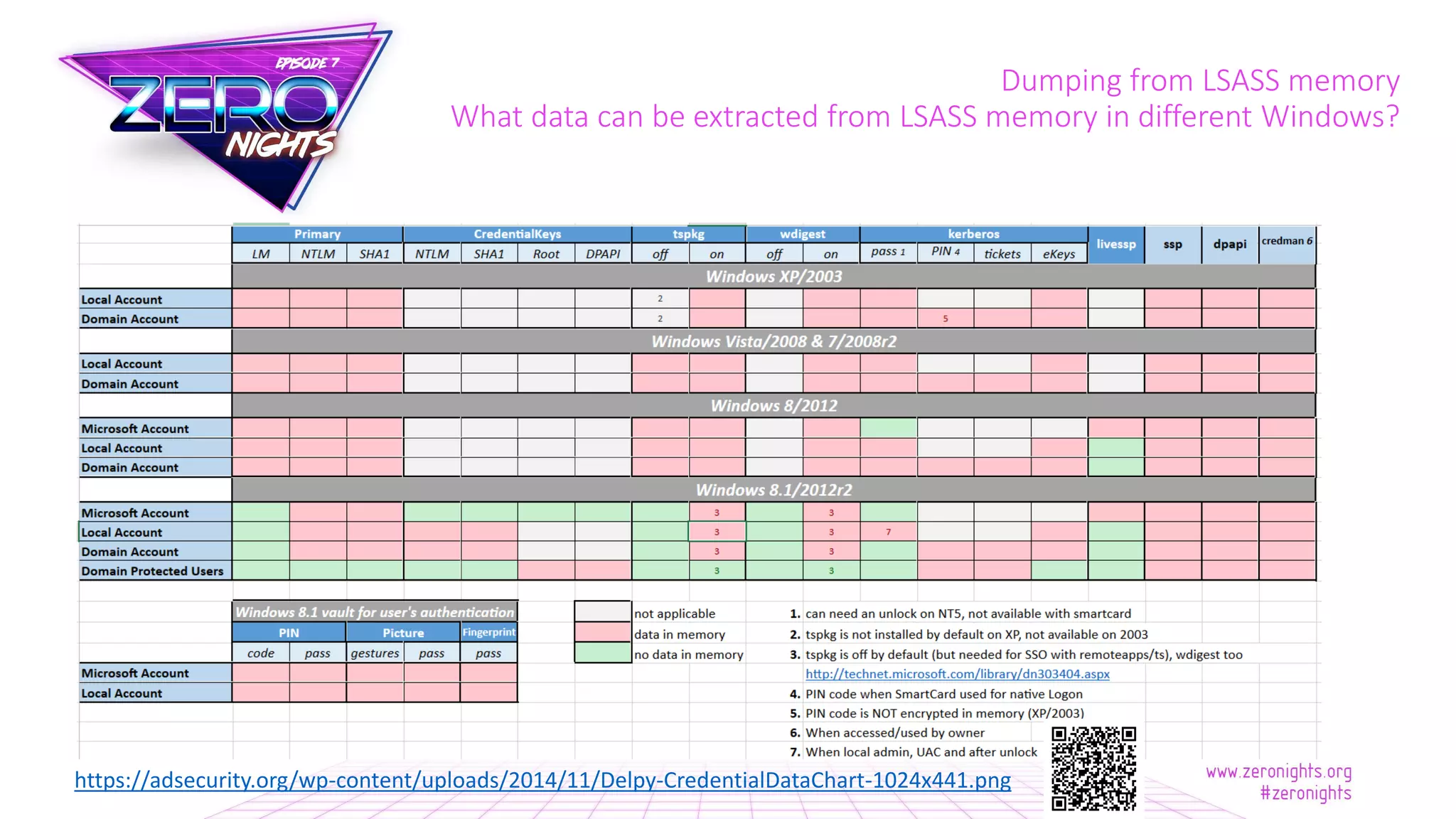
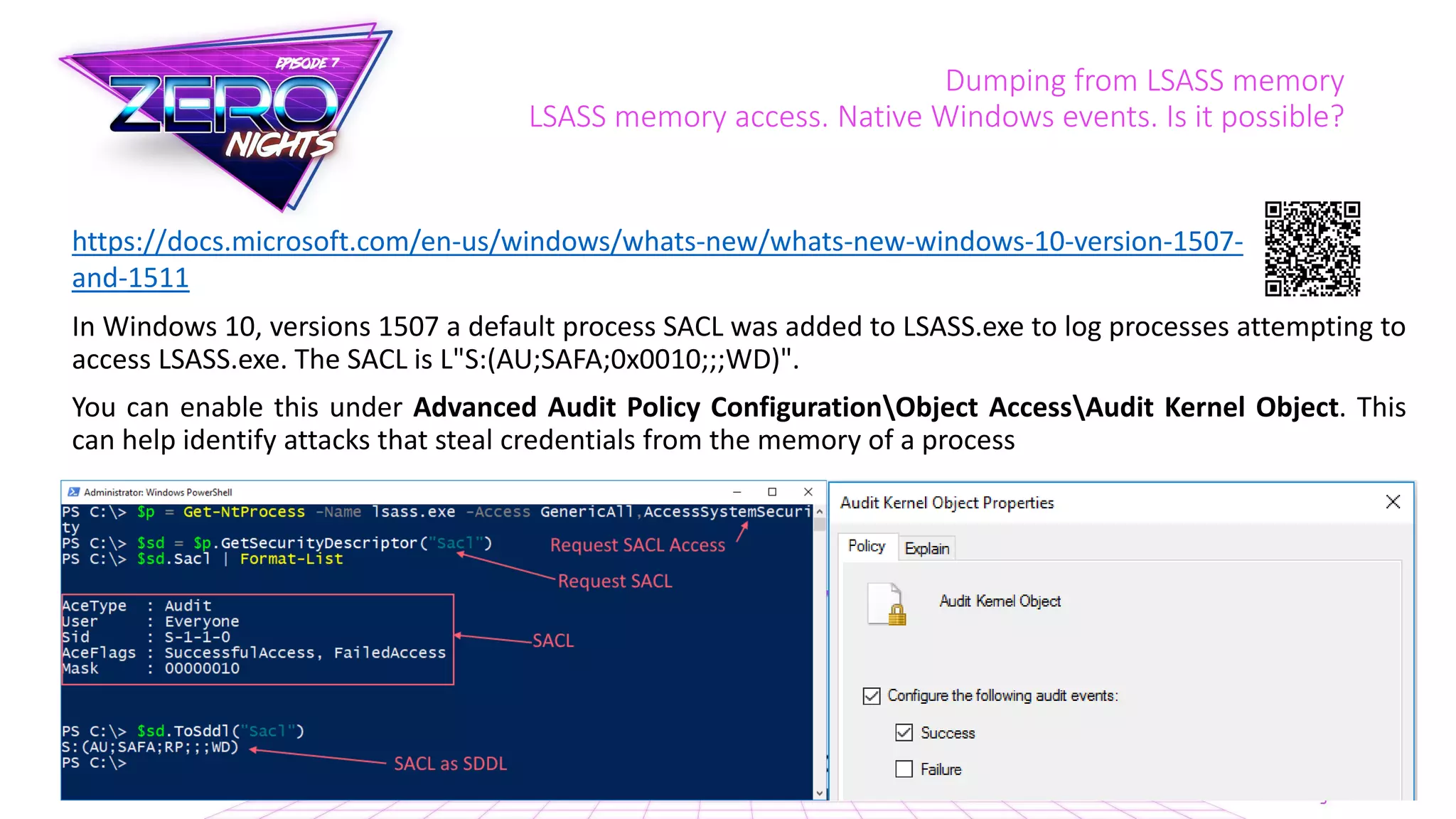
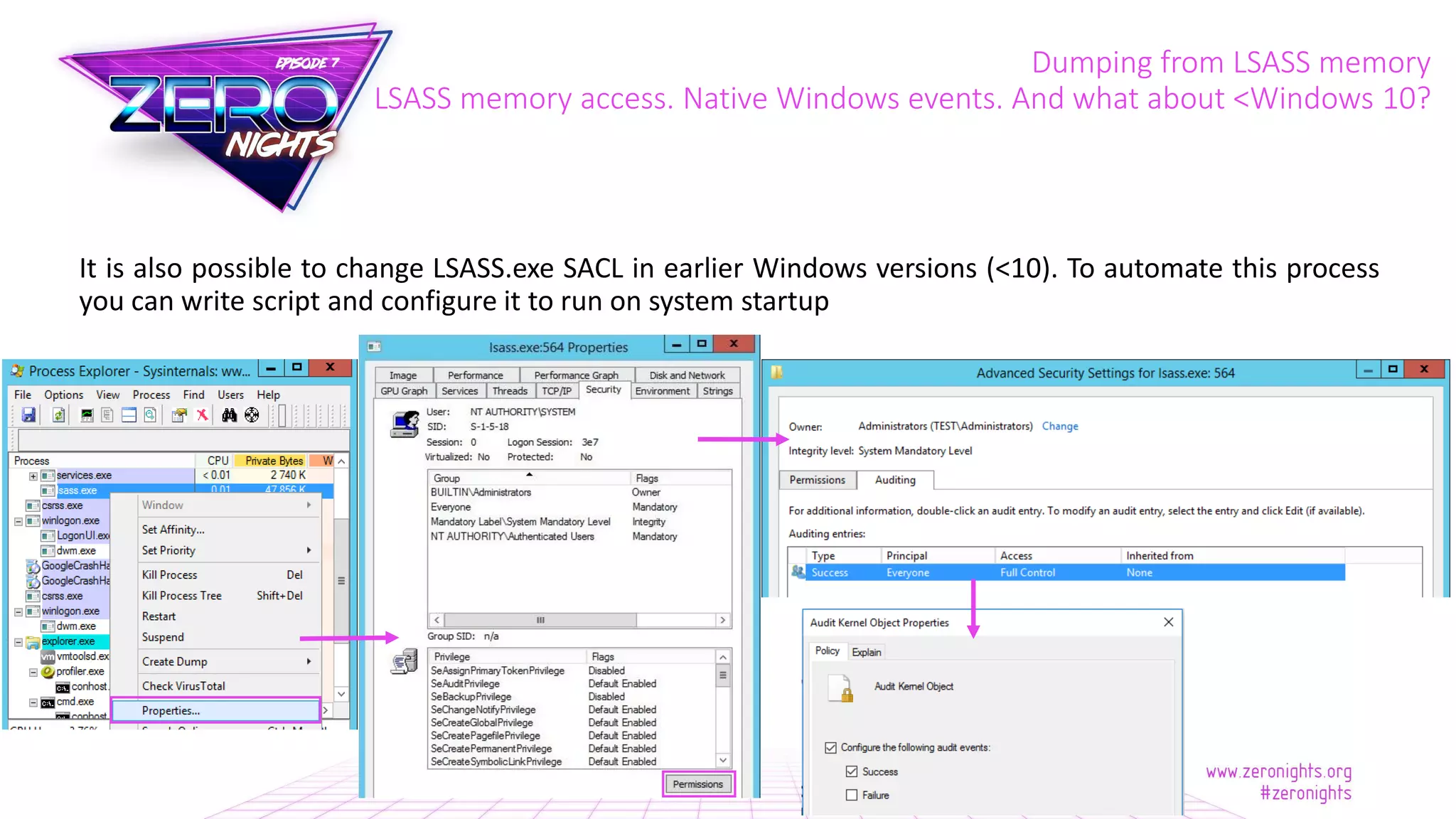
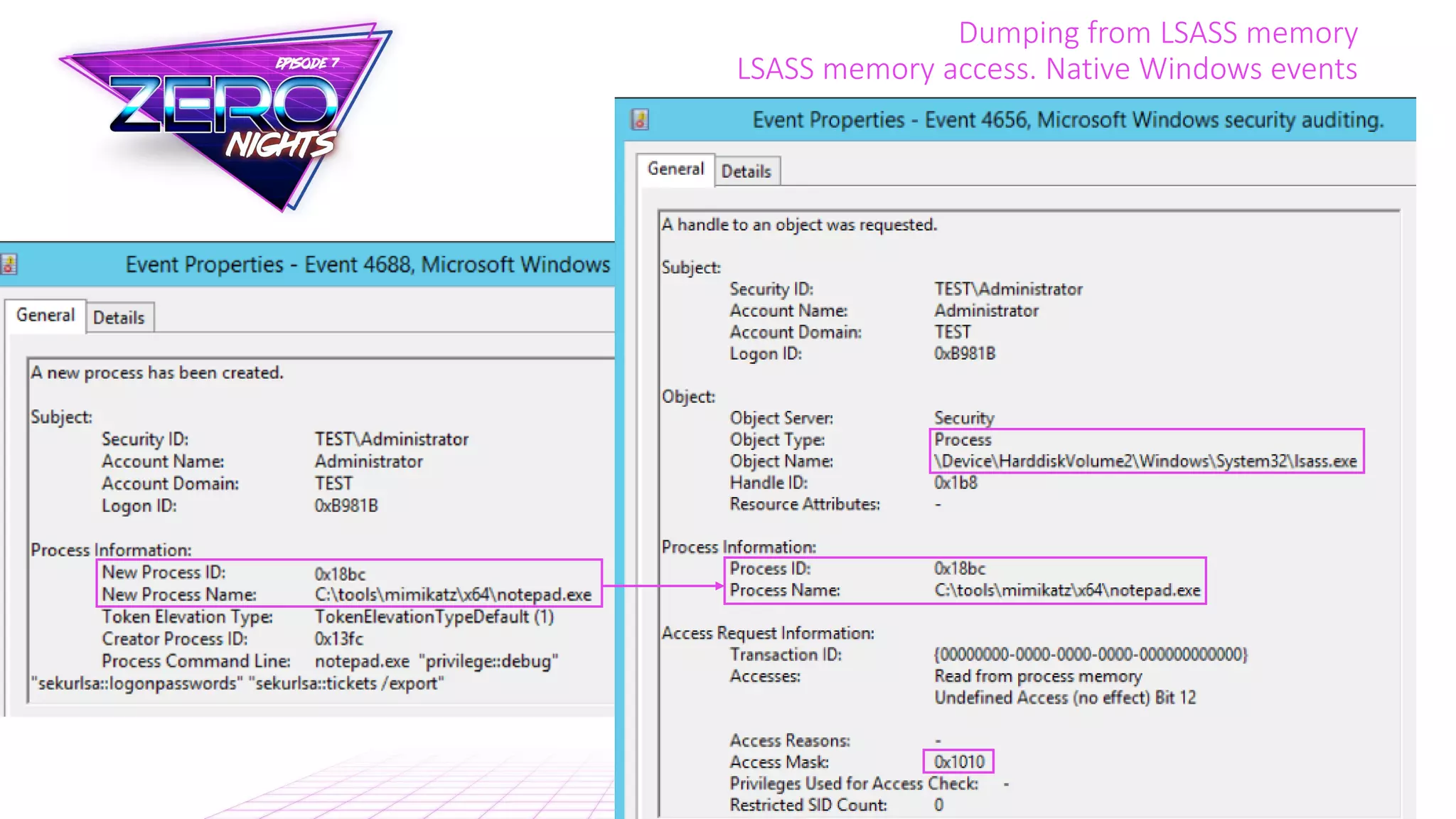
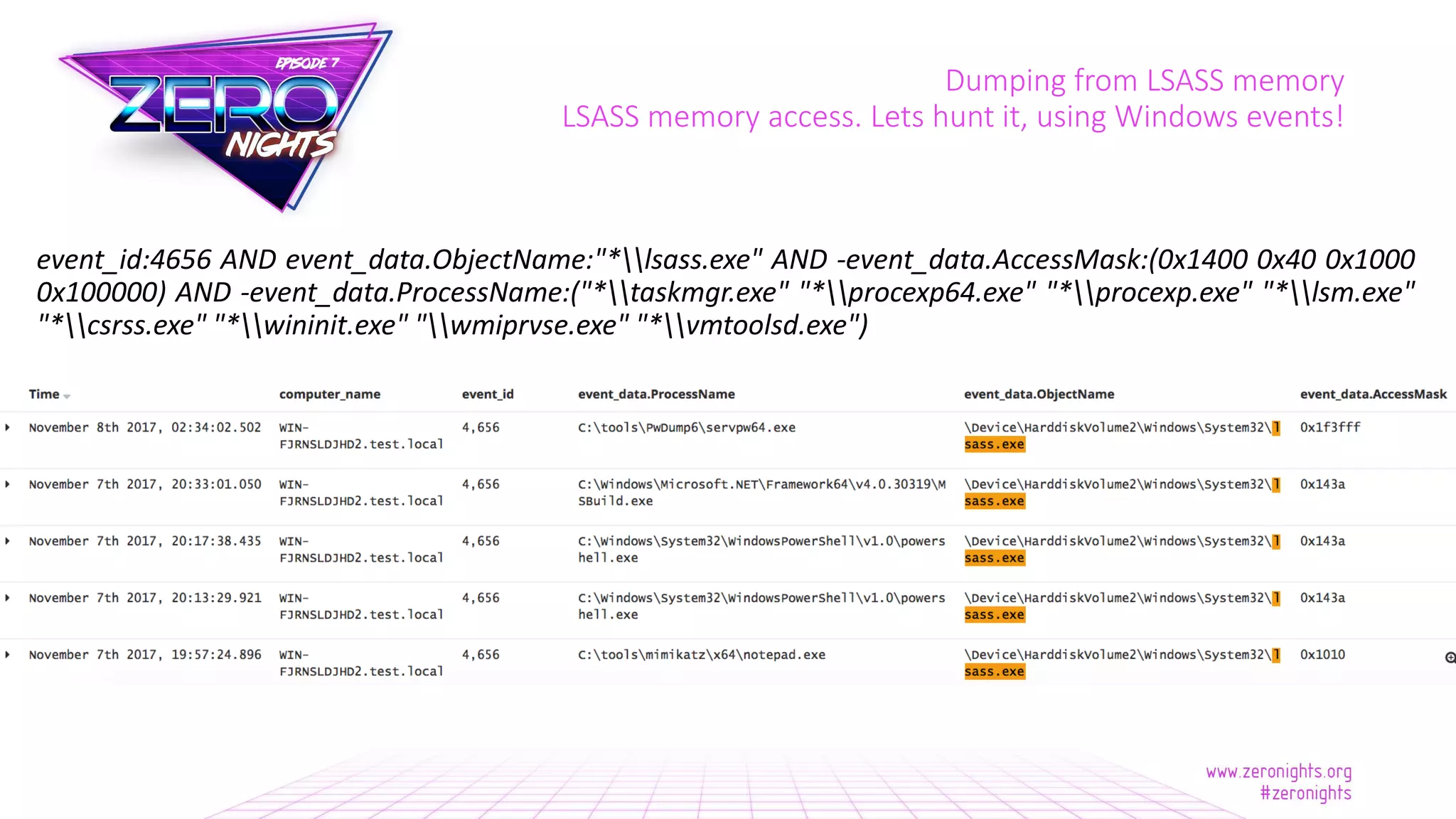
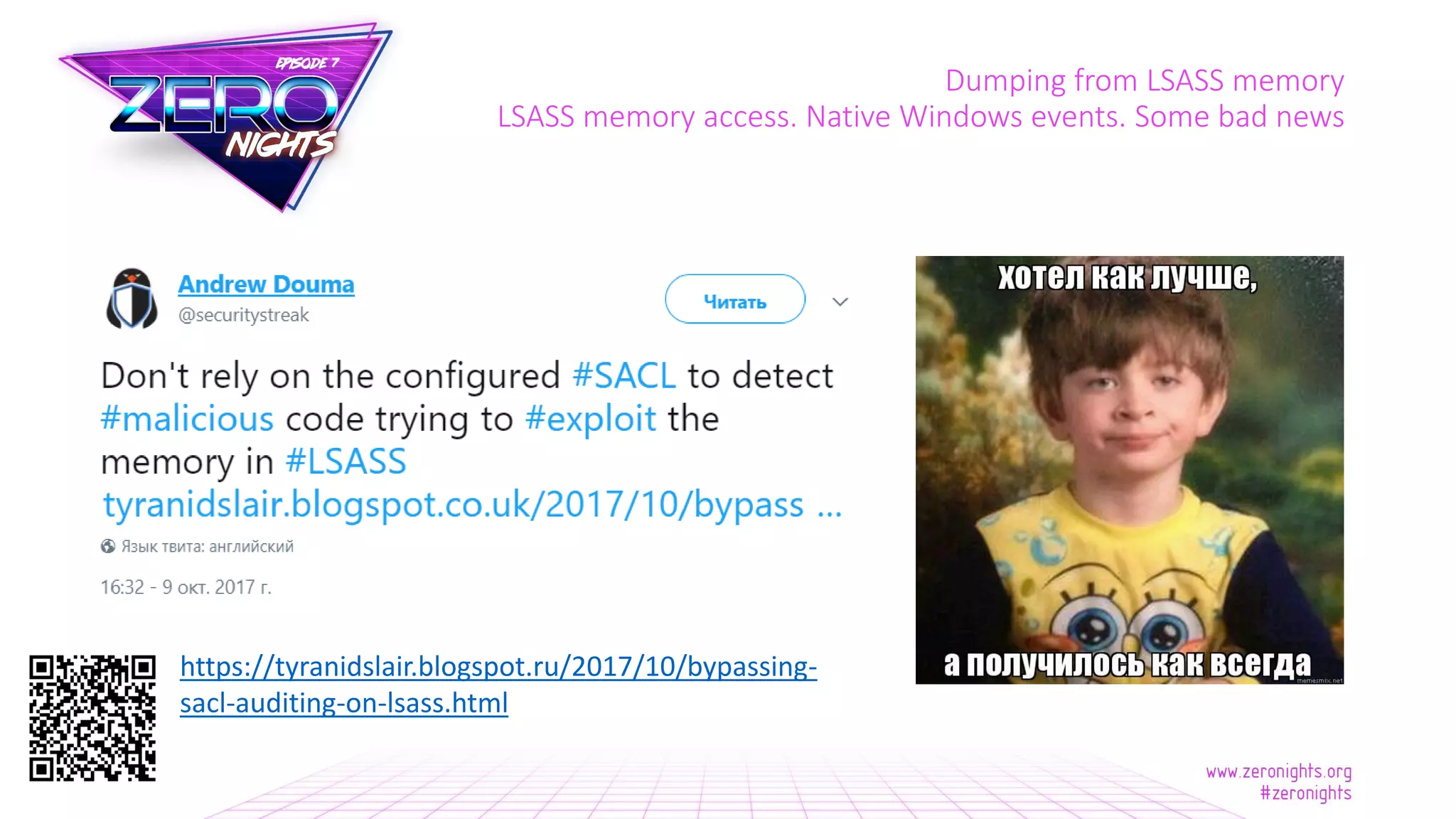
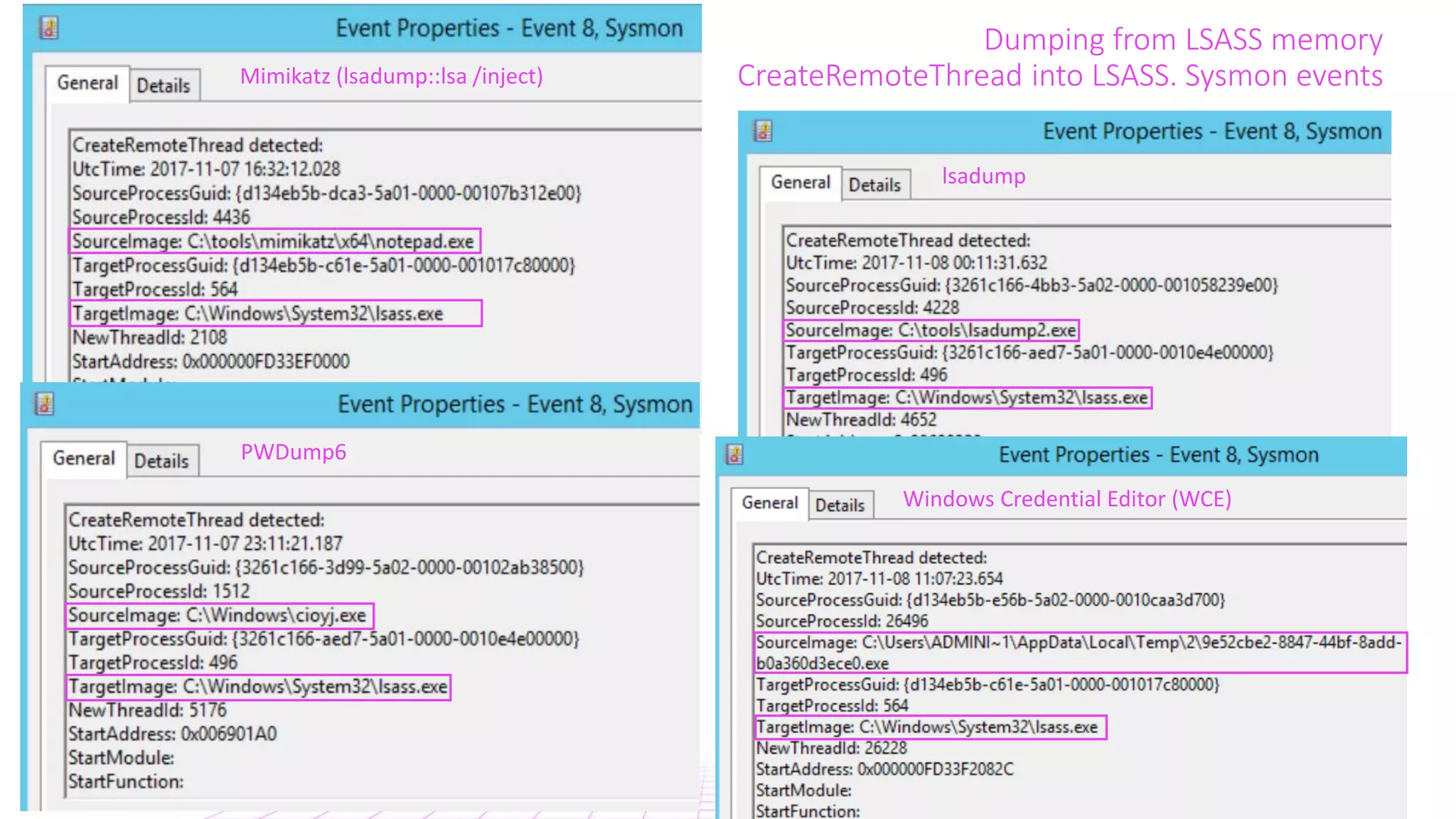
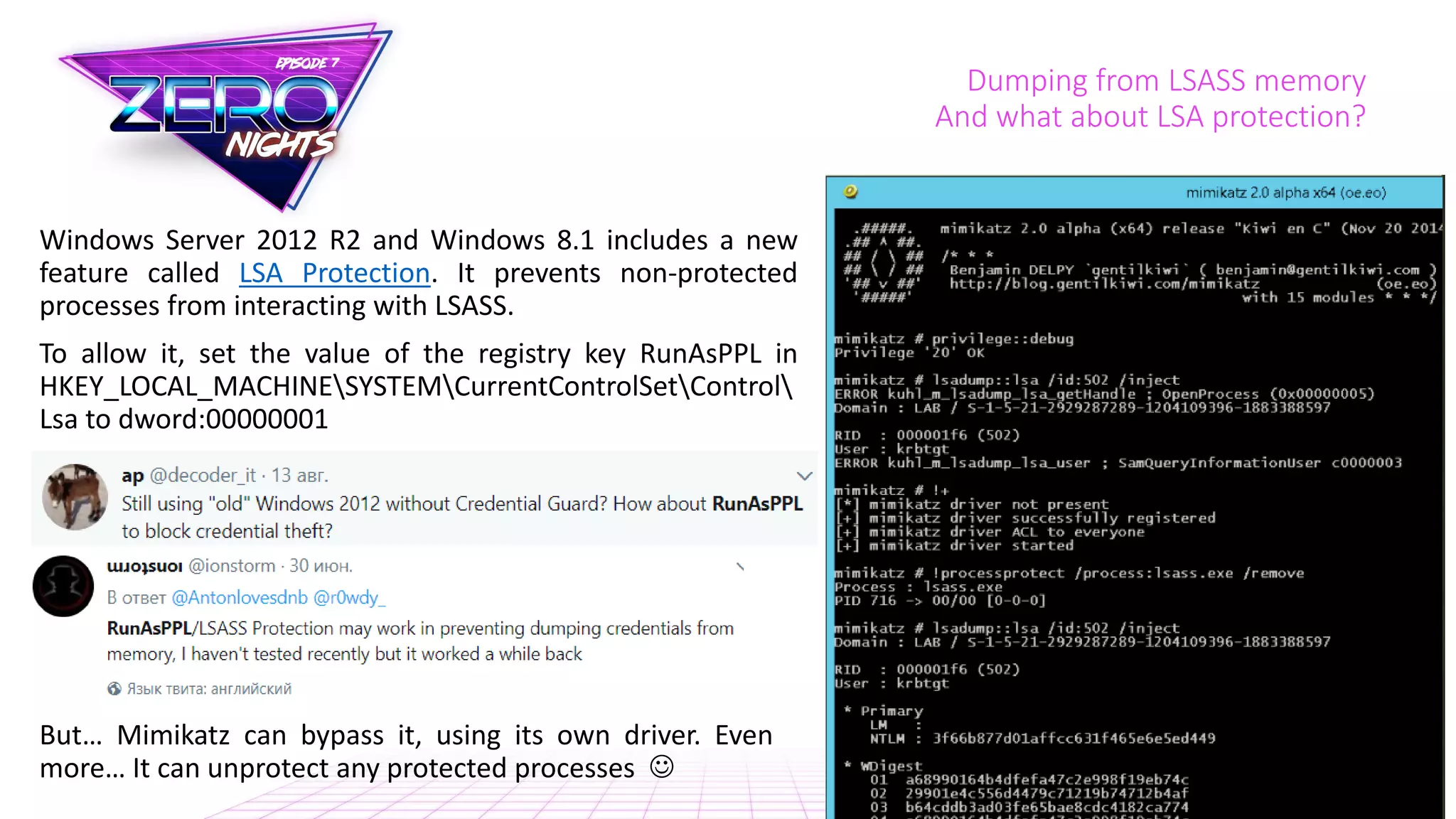
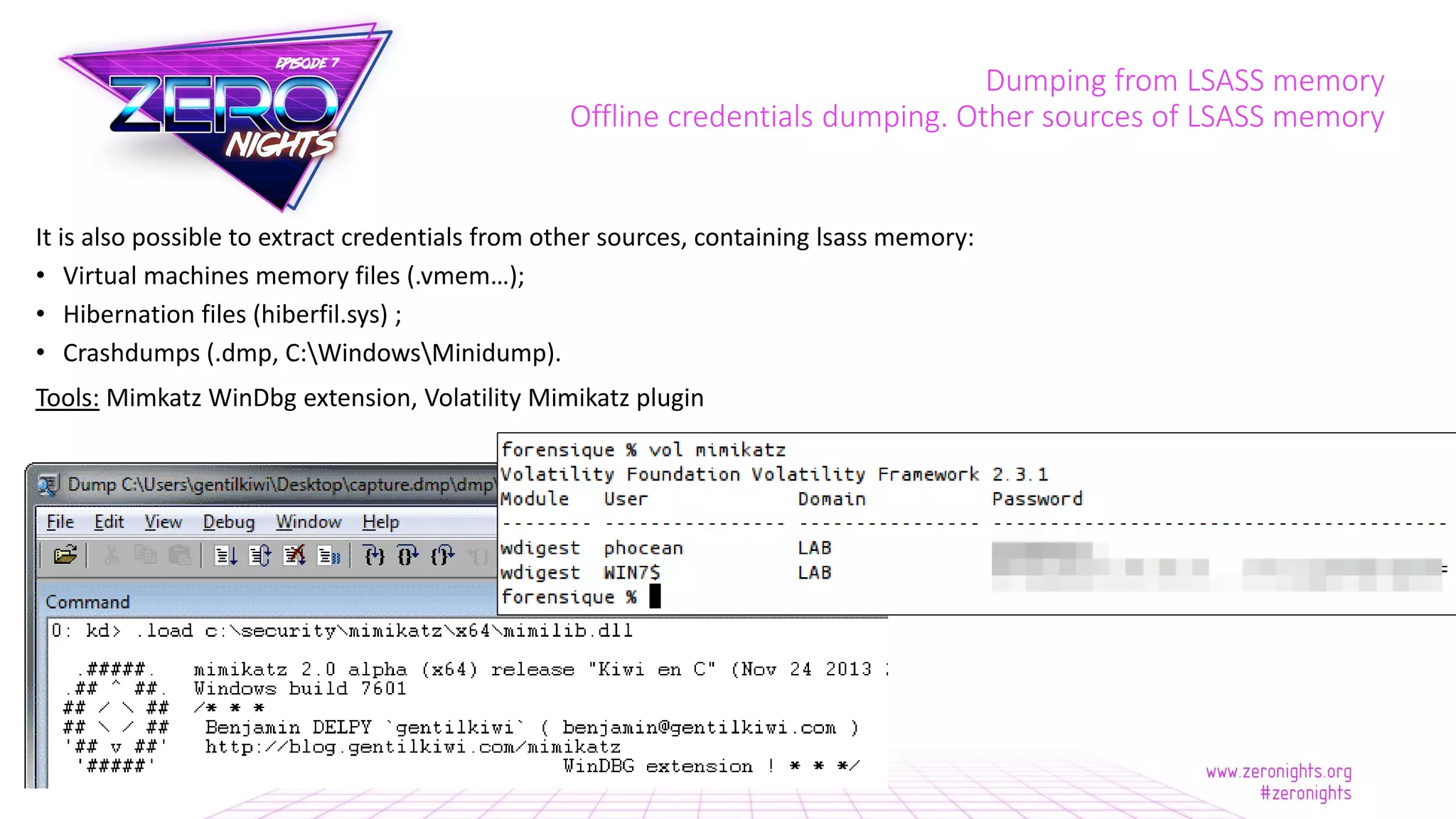
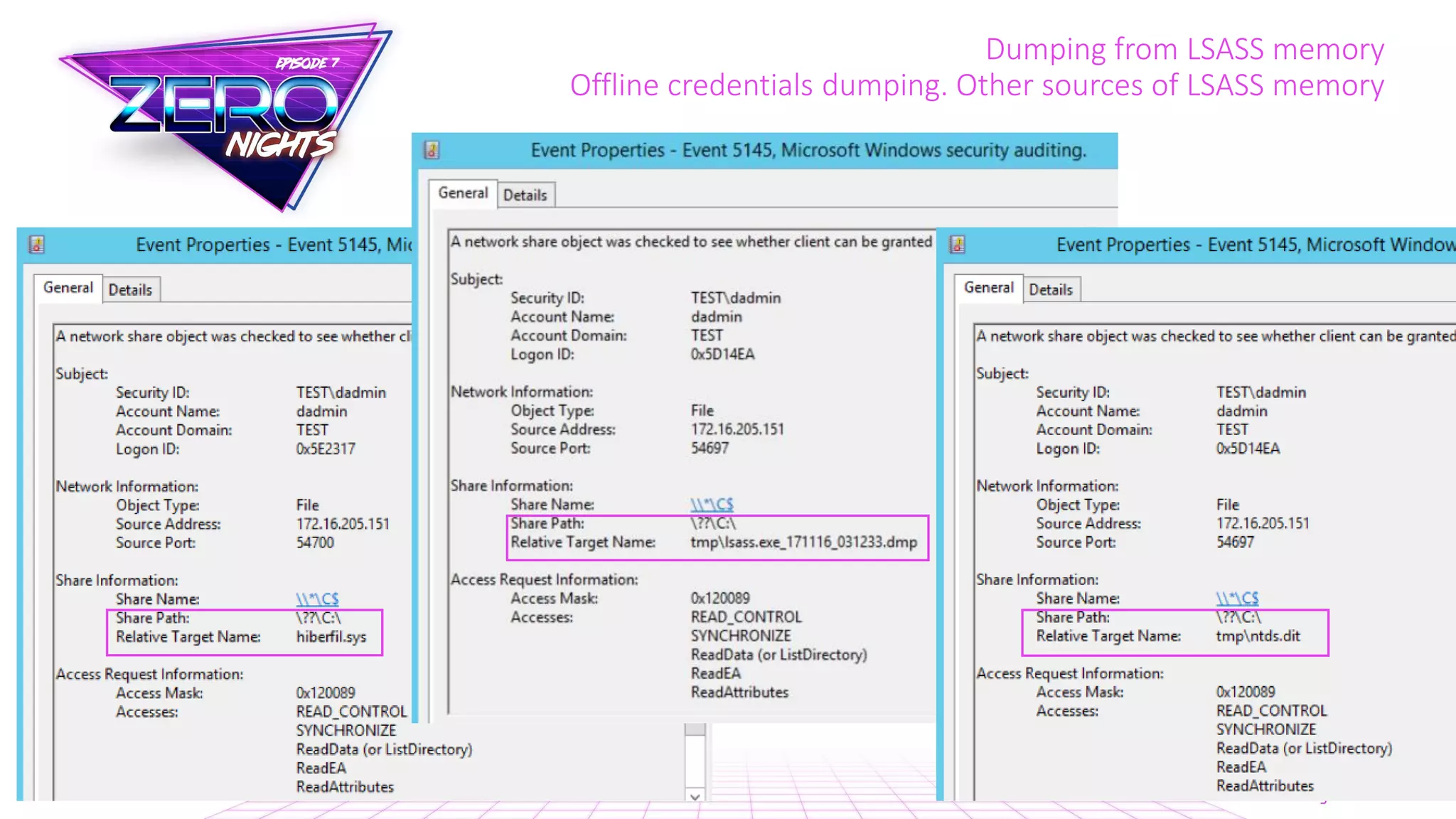
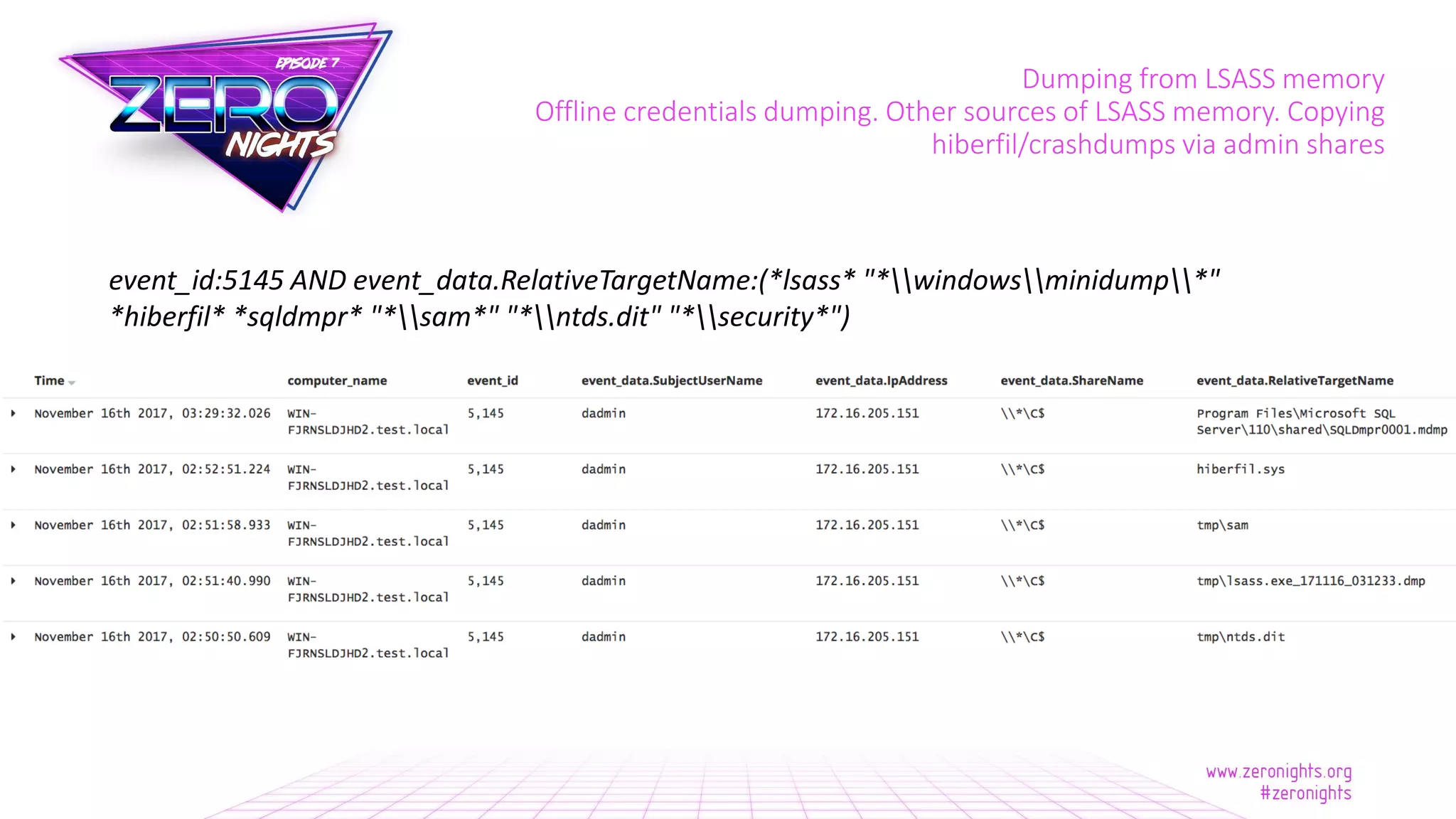
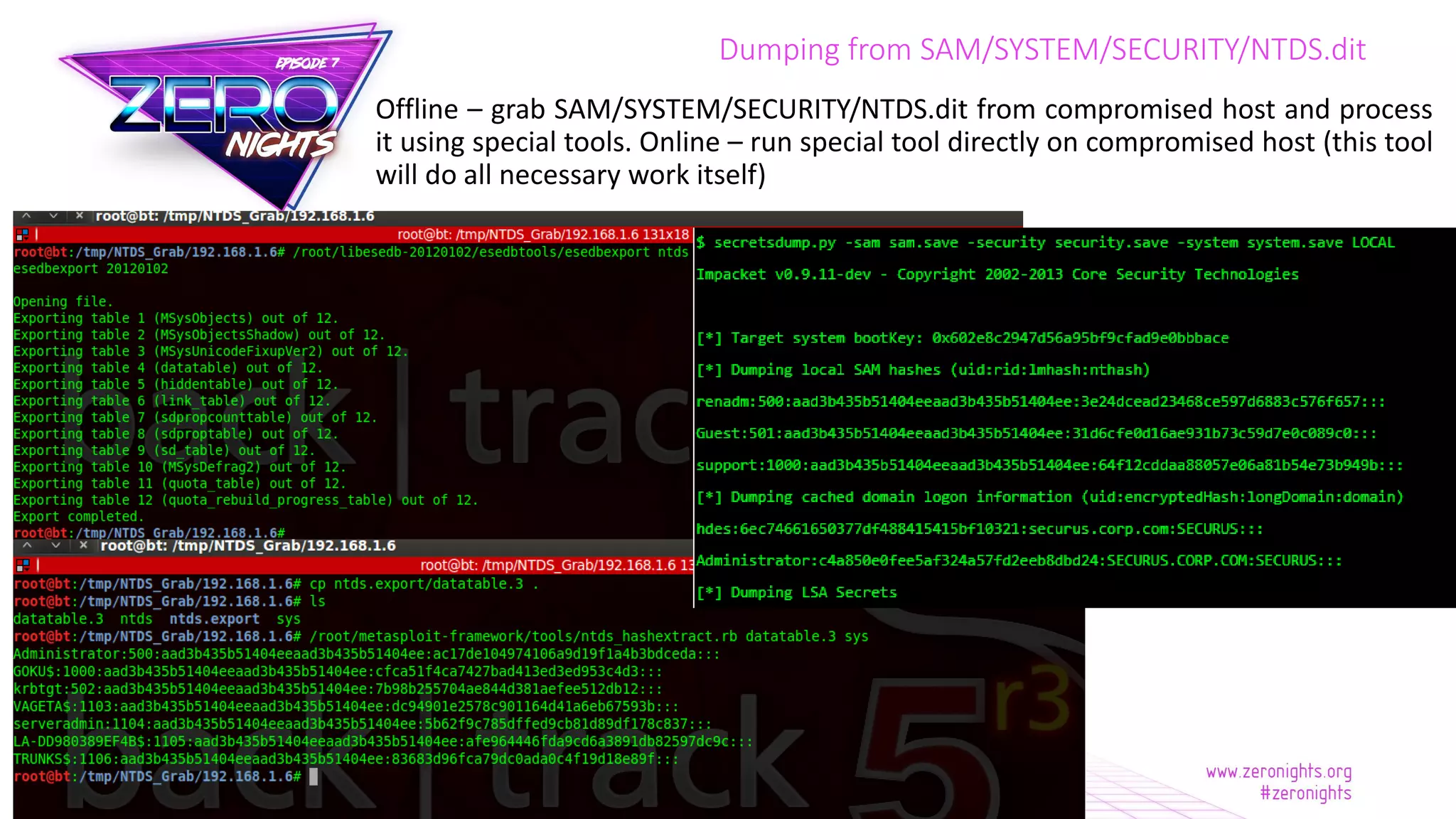
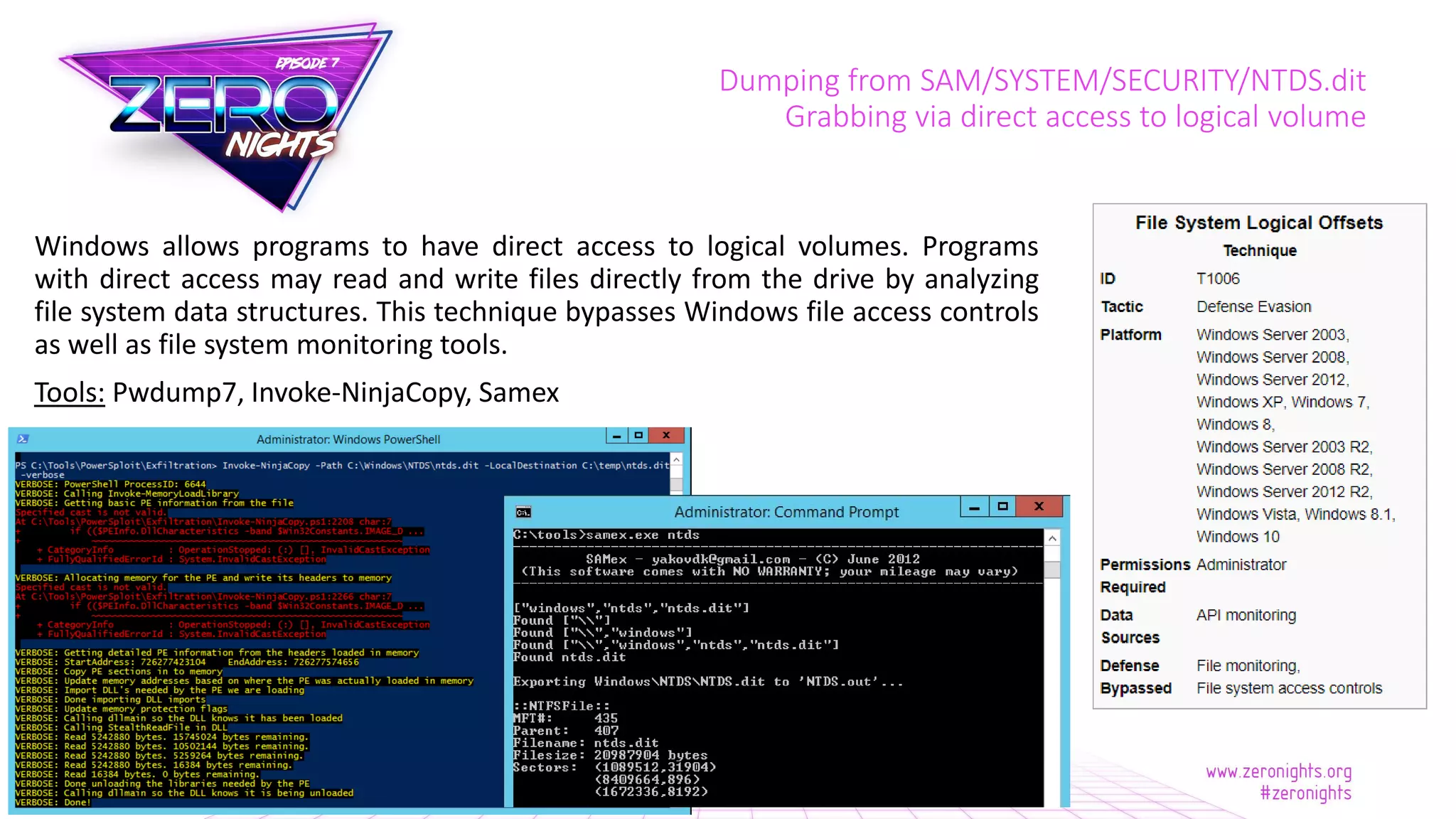
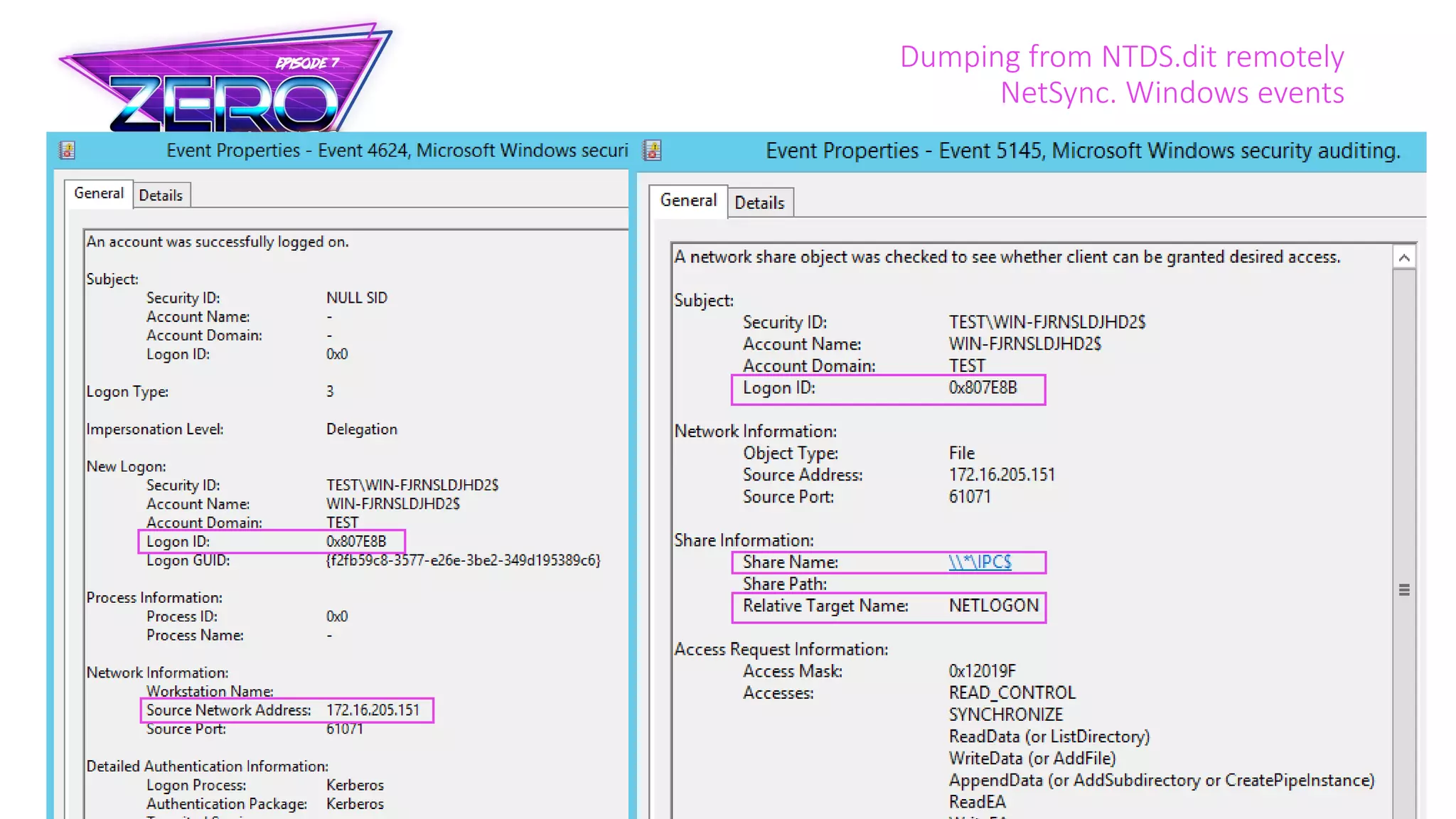
The document discusses credential dumping techniques in Windows environments, highlighting methods used by various threat actor groups to extract sensitive information from systems, including tools like Mimikatz and WCE. It emphasizes the importance of detecting such activities through system logs (Sysmon and Windows Event Logs) and outlines potential data sources such as LSASS memory, SAM registry hives, and other offline methods. Additionally, it touches on the use of native Windows features for monitoring and auditing access to sensitive data, providing practical guidance for detecting credential extraction attempts.


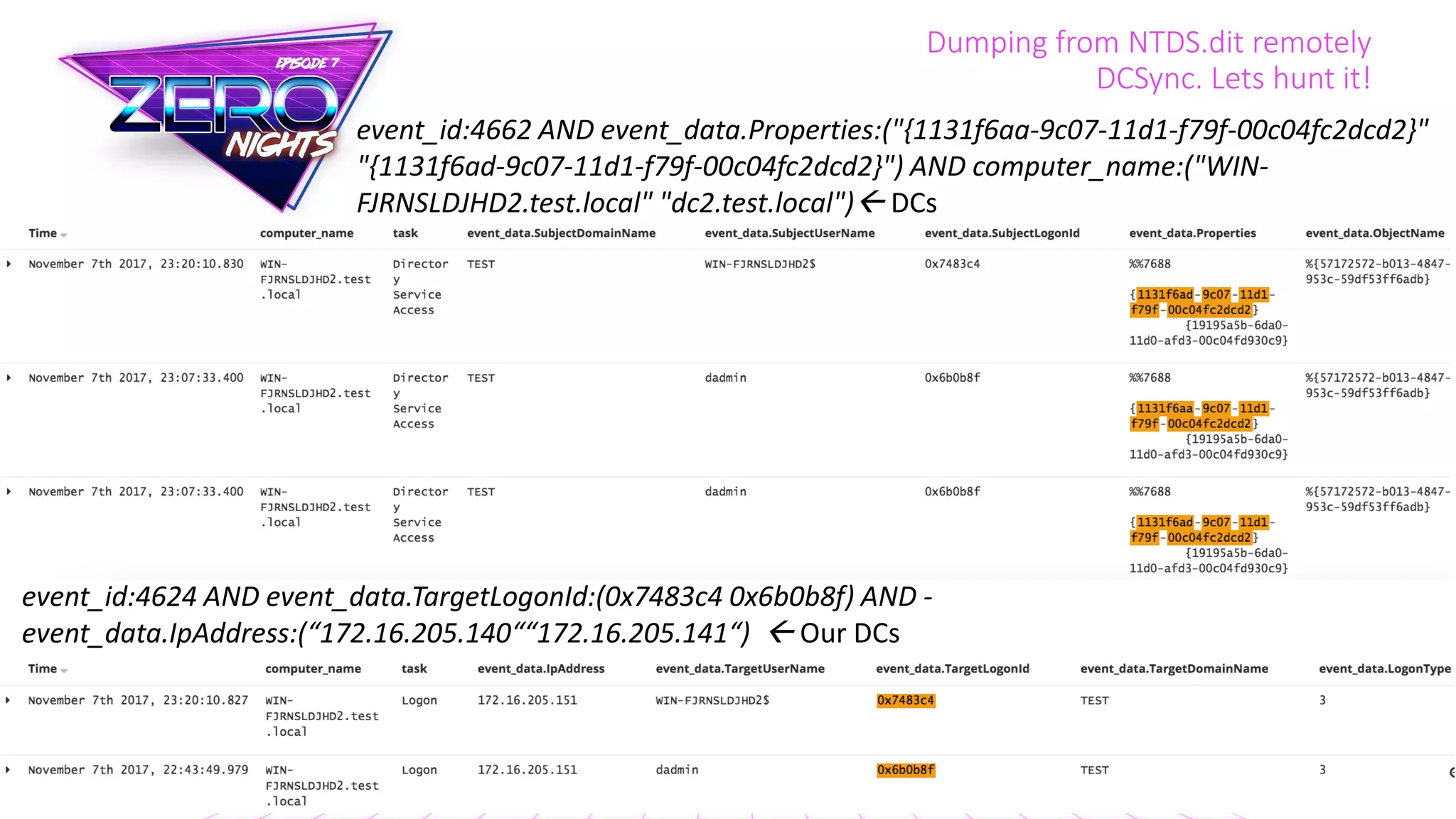
![Dumping from NTDS.dit remotely
NetSync
Based on [MS-NRPC] - Netlogon Remote Protocol
Tools: Mimikatz](https://image.slidesharecdn.com/zeronights2017kheirkhabarov-171118103000/75/Hunting-for-Credentials-Dumping-in-Windows-Environment-50-2048.jpg)
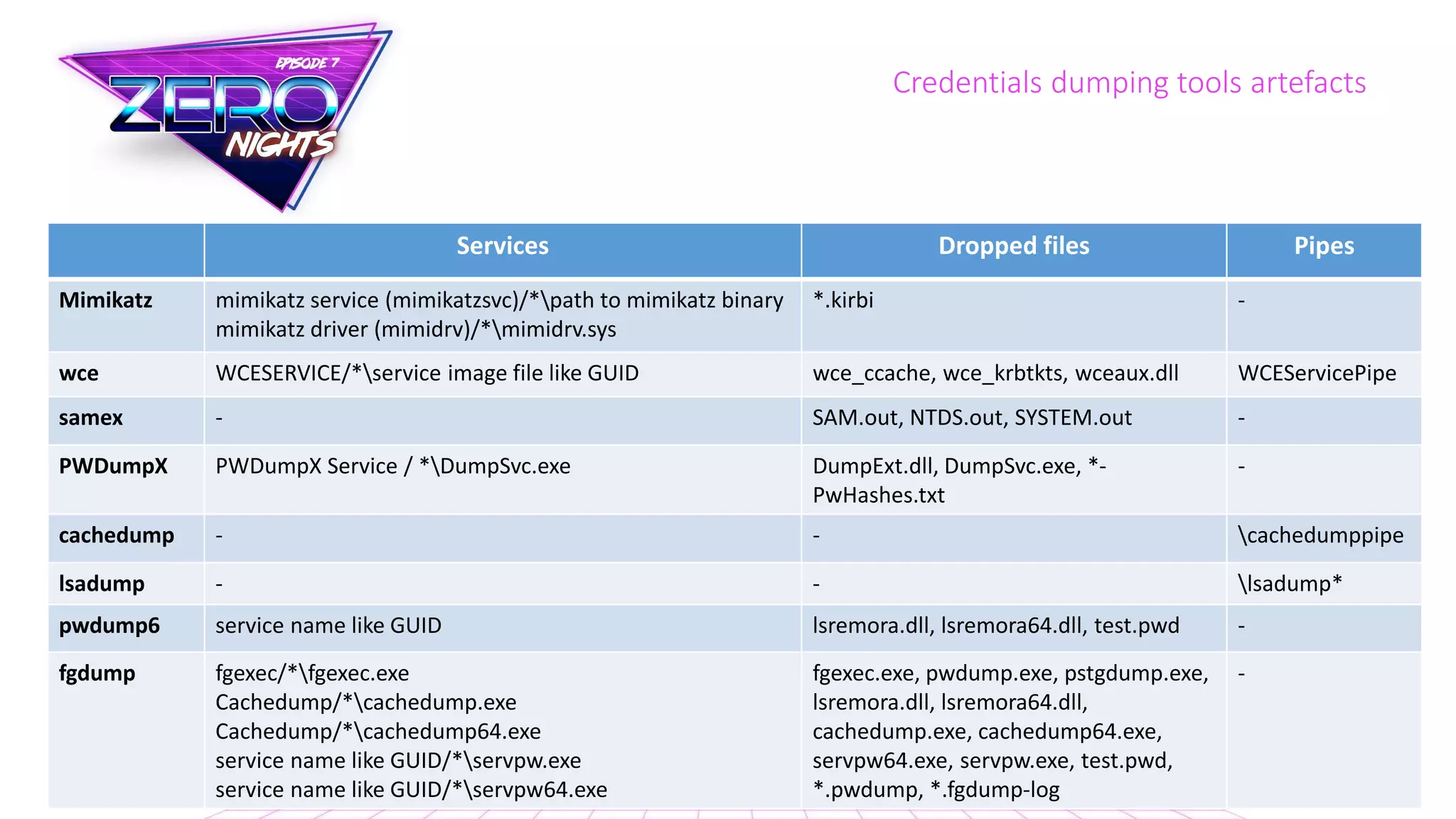
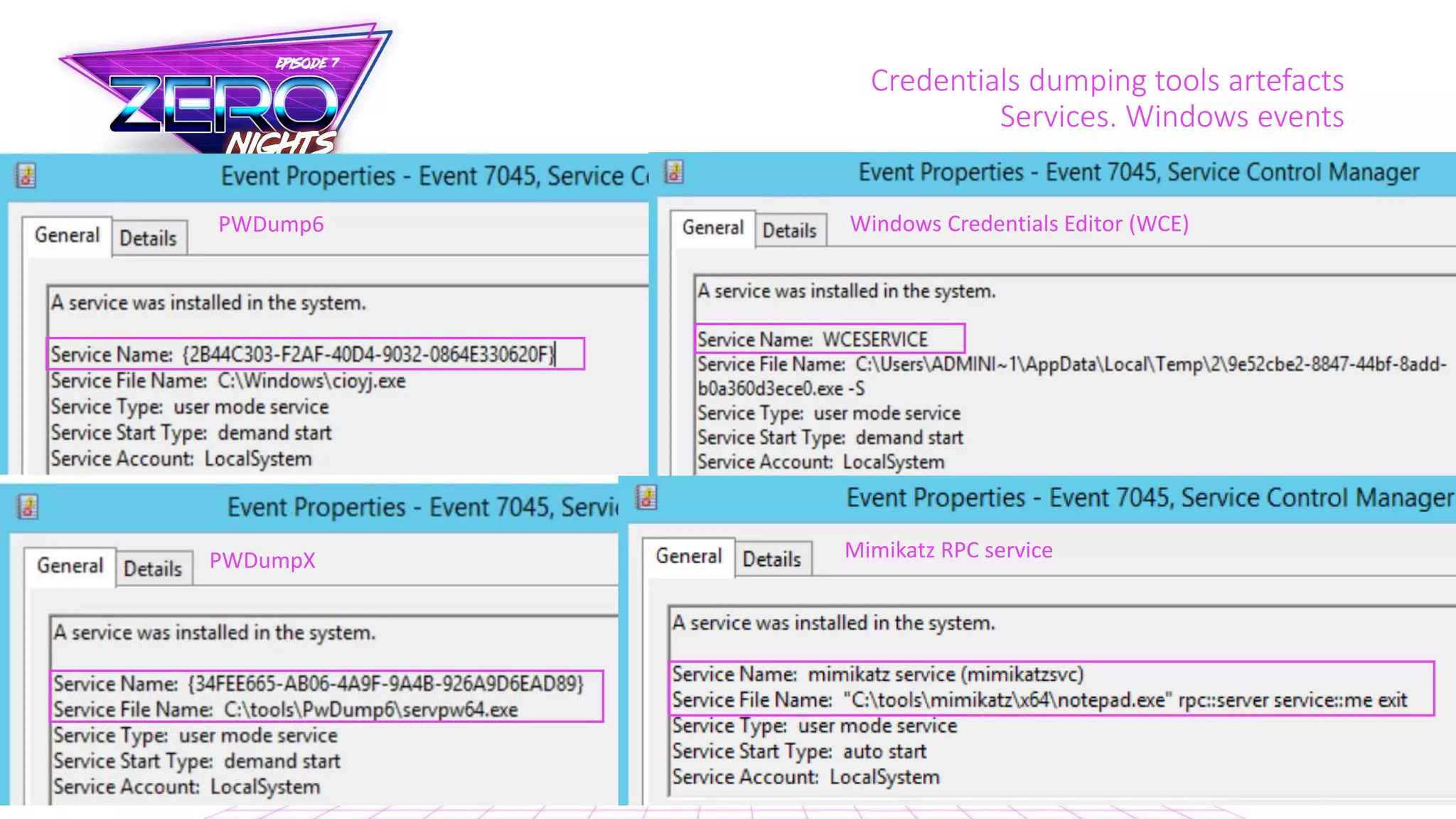
![Credentials dumping tools artefacts
Services. Lets hunt it!
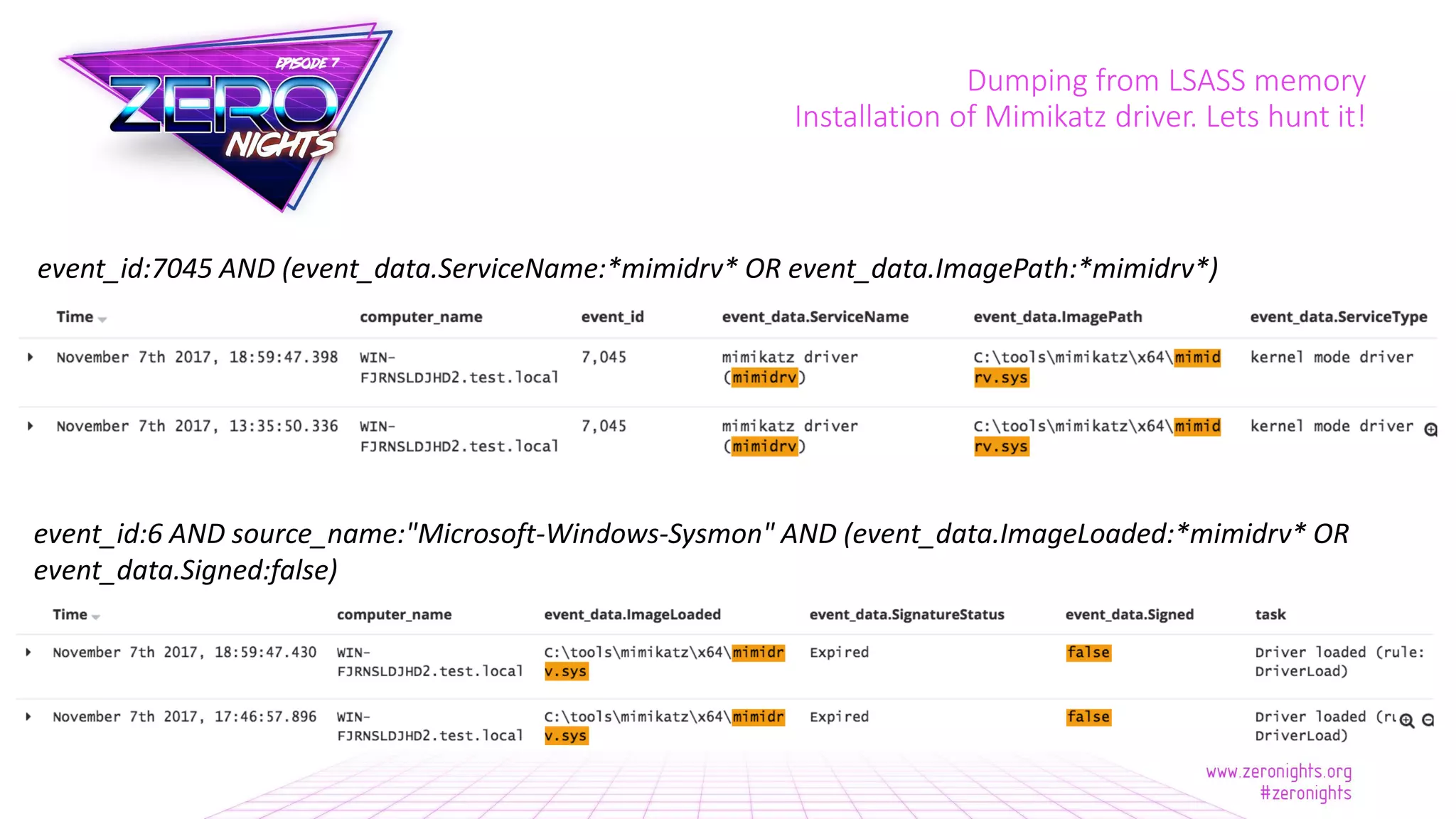
event_id:7045 AND (event_data.ServiceName:(fgexec cachedump *mimikatz*
*mimidrv* WCESERVICE *pwdump*) OR event_data.ImagePath:(*fgexec* *dumpsvc*
*mimidrv* *cachedump* *servpw* *gsecdump* *pwdump*) OR
event_data.ImagePath.raw:/(.*.*|.*[{]?[0-9A-Fa-f]{8}-[0-9A-Fa-f]{4}-[0-9A-Fa-
f]{4}-[0-9A-Fa-f]{4}-[0-9A-Fa-f]{12}[}]?.(exe|scr|cpl|bat|js|cmd|vbs).*)/)](https://image.slidesharecdn.com/zeronights2017kheirkhabarov-171118103000/75/Hunting-for-Credentials-Dumping-in-Windows-Environment-54-2048.jpg)