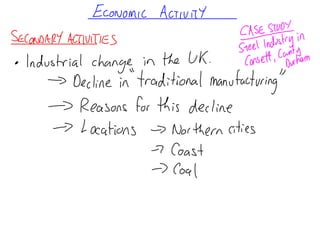
Economic Activity notes
•Download as PPT, PDF•
0 likes•527 views
Report
Share
Report
Share
Recommended
Javascript by Yahoo

The JavaScript programming language is a multi-paradigm language that is misunderstood due to its name, design errors in early implementations, and use in web browsers. It is a functional language that uses objects, prototypes, and closures. Values in JavaScript include numbers, strings, Booleans, objects, null, and undefined. All other values are objects.
Father's Day

Father's Day began as a church service in Fairmont, West Virginia in 1908 to honor fathers. Sonora Smart Dodd from Washington then campaigned for an official Father's Day after being inspired by Mother's Day. She chose the third Sunday of June, which became the first official Father's Day in 1910 celebrated in Spokane, Washington. Common gifts for Father's Day include ties, golf or restaurant gift certificates, and cologne.
A Process By Any Other Name...: Applying Information Architecture with bridge...

This is my presentation from the 2006 IA Summit in Vancouver, BC. The summary is that the practice of IA is not about artifacts but the thinking that goes into them and the way you assess which artifacts to use.
Applicare l'ISEE. Tra semplcità ed equità.

Come applicare l'ISEE tenendo conto dei vincoli della formulazione e delle discrezionalità concesse all'ente erogatore.
Arran Day 4

Today was our fourth day of the Arran fieldtrip. We started the day with a hike up Goatfell, the highest point on the island. After reaching the summit, the class stopped to have lunch and take in the panoramic views of the surrounding landscape. In the afternoon, we visited Brodick Castle and learned about the history of the estate and those who lived there.
Arran Day Part 3

The students continued their hike through the Scottish Highlands, passing through rocky terrain and open moorland. They stopped for lunch near a small loch, enjoying the scenic views of the surrounding hills and mountains. By late afternoon, the group had completed their 15 kilometer hike and arrived tired but satisfied back at the youth hostel.
Arram Day 3 Part 1

The students woke up early for their third day of the Arran fieldtrip. After packing up their tents and having a quick breakfast, they met their guide for a geology walk along the coastline to examine the various rock formations and learn about the geological history of the area. Along the way, the guide pointed out fossils and explained how the landscape was shaped by volcanic activity millions of years ago.
Recommended
Javascript by Yahoo

The JavaScript programming language is a multi-paradigm language that is misunderstood due to its name, design errors in early implementations, and use in web browsers. It is a functional language that uses objects, prototypes, and closures. Values in JavaScript include numbers, strings, Booleans, objects, null, and undefined. All other values are objects.
Father's Day

Father's Day began as a church service in Fairmont, West Virginia in 1908 to honor fathers. Sonora Smart Dodd from Washington then campaigned for an official Father's Day after being inspired by Mother's Day. She chose the third Sunday of June, which became the first official Father's Day in 1910 celebrated in Spokane, Washington. Common gifts for Father's Day include ties, golf or restaurant gift certificates, and cologne.
A Process By Any Other Name...: Applying Information Architecture with bridge...

This is my presentation from the 2006 IA Summit in Vancouver, BC. The summary is that the practice of IA is not about artifacts but the thinking that goes into them and the way you assess which artifacts to use.
Applicare l'ISEE. Tra semplcità ed equità.

Come applicare l'ISEE tenendo conto dei vincoli della formulazione e delle discrezionalità concesse all'ente erogatore.
Arran Day 4

Today was our fourth day of the Arran fieldtrip. We started the day with a hike up Goatfell, the highest point on the island. After reaching the summit, the class stopped to have lunch and take in the panoramic views of the surrounding landscape. In the afternoon, we visited Brodick Castle and learned about the history of the estate and those who lived there.
Arran Day Part 3

The students continued their hike through the Scottish Highlands, passing through rocky terrain and open moorland. They stopped for lunch near a small loch, enjoying the scenic views of the surrounding hills and mountains. By late afternoon, the group had completed their 15 kilometer hike and arrived tired but satisfied back at the youth hostel.
Arram Day 3 Part 1

The students woke up early for their third day of the Arran fieldtrip. After packing up their tents and having a quick breakfast, they met their guide for a geology walk along the coastline to examine the various rock formations and learn about the geological history of the area. Along the way, the guide pointed out fossils and explained how the landscape was shaped by volcanic activity millions of years ago.
Arran Day 3 Part 2

The students continued their hike through the Scottish Highlands, passing lochs and mountains along the way. After a long day of walking, they stopped to set up camp for the night near Loch an Eilein. Exhausted but satisfied with their adventure, the group looked forward to relaxing by the campfire under the stars before getting some well-earned rest.
Arran Day Part 2

The students continued their exploration of the Arran coastline by hiking along the cliff trails. Along the way, they spotted many seabirds nesting in the cliffs and seals resting on the rocky shore. Their guide pointed out various geological features formed by the relentless pounding of ocean waves over millions of years.
Arran Day 2

Today the class went on several nature hikes through the forests and hills near Arran. They observed many local plant and animal species and discussed how humans have impacted the environment. The day ended with building a campfire and making s'mores before packing up to return home after an educational trip.
Arran Day 1

The students woke up early and boarded the bus for their field trip to Arran. After a long bus ride, they arrived at their first stop, the Brodick Castle gardens, where they explored the beautiful grounds and went on a guided tour of the castle. For lunch, the group ate sandwiches overlooking the sea before heading to their campsite for the night.
Environmental lack of development

Environmental hazards such as droughts, tropical storms, floods, earthquakes, and volcanoes negatively impact development in less economically developed countries (LEDCs). Climatic hazards like droughts and storms are more responsible for loss of life globally than tectonic events. Tropical areas where many LEDCs are located experience more frequent and severe climatic hazards compared to temperate regions. When hazards do occur, their impacts are worse in LEDCs due to factors like buildings not being constructed to withstand disasters and lack of emergency infrastructure.
Causes of the lack of development

This document discusses the factors that have contributed to the lack of economic development in less economically developed countries (LEDCs), which are concentrated in just three continents - South America, Africa, and Asia. It identifies human factors like historical legacies from colonialism, persistent colonial trade patterns, and issues like economic mismanagement, corruption, and wars as causes for the concentration of over 1 billion people living in absolute poverty across these three continents.
Aid

There are three main types of aid:
1) Political (bilateral) aid which is given directly from one government to another, often with conditions attached for the recipient country to buy goods from the donor country.
2) Multilateral aid which is given to international agencies like the UN to distribute as they see fit, often targeting large projects and not always meeting local needs.
3) Charitable aid from NGOs which works closely with local communities to target aid directly to those most in need, making it more effective.
Water availability and quality

The document discusses facts about water availability on Earth. It notes that while oceans hold the vast majority of the planet's water, only 3% is fresh water. Most of this fresh water is unavailable for human use, being locked up in ice sheets. The document then explains that fresh water availability is unevenly distributed among countries, with some experiencing water stress due to high consumption rates and populations. It concludes by noting that global water demand is rising faster than the population as developing countries industrialize and increase irrigation for food.
Water Quality

The majority of water stressed countries are located in Africa and Asia, where governments have less ability to implement measures to address water supply issues like pollution control, increased water efficiency, and population control. Access to clean water varies greatly between more economically developed countries (MEDC) which have near universal access, and less economically developed countries (LEDC) where the average access is 70% but ranges widely between and within countries, with sub-Saharan Africa having the lowest access at 51%. Rural areas generally have lower access to clean water and sanitation than urban areas.
Population and Development

The document compares the population characteristics of more economically developed countries (MEDC's) and less economically developed countries (LEDC's). It finds that MEDC's typically have lower birth rates and death rates, resulting in little or no natural population increase. Their population structures show fewer people under age 15. LEDC's have higher birth rates and natural increase, with more than 30-55% of their populations under age 15.
Measuring Development

The document discusses measuring development between less economically developed countries (LEDCs) and more economically developed countries (MEDC). It defines development as encompassing both economic and social factors like wealth, quality of life, health, literacy, and housing. The most widely used indicator is gross national product (GNP) per capita, which is a country's total output divided by population. However, GNP is a more reliable indicator for MEDCs than LEDCs because LEDC statistics are less available and accurate, and GNP does not account for subsistence farming common in LEDCs. Other development indicators include birth rate, energy consumption, doctors per person, and literacy rates.
Creating a weblog

This document discusses creating a geography department blog to communicate information to students. It defines what a blog is, explains how a blog can be useful for following up on lessons, providing homework links and reminders. It also provides information on setting up a free blog using Blogger.com and including links to videos on YouTube, PowerPoints on SlideShare, and homework on Box.net.
OS Symbols Bingo Game

The document instructs the reader to choose 9 Ordnance Survey map symbols, draw a 3x3 grid, and place one map symbol in each square of the grid to create a bingo card.
Choosing The Best AWS Service For Your Website + API.pptx

Have you ever been confused by the myriad of choices offered by AWS for hosting a website or an API?
Lambda, Elastic Beanstalk, Lightsail, Amplify, S3 (and more!) can each host websites + APIs. But which one should we choose?
Which one is cheapest? Which one is fastest? Which one will scale to meet our needs?
Join me in this session as we dive into each AWS hosting service to determine which one is best for your scenario and explain why!
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

Direct losses from downtime in 1 minute = $5-$10 thousand dollars. Reputation is priceless.
As part of the talk, we will consider the architectural strategies necessary for the development of highly loaded fintech solutions. We will focus on using queues and streaming to efficiently work and manage large amounts of data in real-time and to minimize latency.
We will focus special attention on the architectural patterns used in the design of the fintech system, microservices and event-driven architecture, which ensure scalability, fault tolerance, and consistency of the entire system.
"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk

At this talk we will discuss DDoS protection tools and best practices, discuss network architectures and what AWS has to offer. Also, we will look into one of the largest DDoS attacks on Ukrainian infrastructure that happened in February 2022. We'll see, what techniques helped to keep the web resources available for Ukrainians and how AWS improved DDoS protection for all customers based on Ukraine experience
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The typical problem in product engineering is not bad strategy, so much as “no strategy”. This leads to confusion, lack of motivation, and incoherent action. The next time you look for a strategy and find an empty space, instead of waiting for it to be filled, I will show you how to fill it in yourself. If you’re wrong, it forces a correction. If you’re right, it helps create focus. I’ll share how I’ve approached this in the past, both what works and lessons for what didn’t work so well.
A Deep Dive into ScyllaDB's Architecture

This talk will cover ScyllaDB Architecture from the cluster-level view and zoom in on data distribution and internal node architecture. In the process, we will learn the secret sauce used to get ScyllaDB's high availability and superior performance. We will also touch on the upcoming changes to ScyllaDB architecture, moving to strongly consistent metadata and tablets.
JavaLand 2024: Application Development Green Masterplan

My presentation slides I used at JavaLand 2024
More Related Content
More from abblanchgeography
Arran Day 3 Part 2

The students continued their hike through the Scottish Highlands, passing lochs and mountains along the way. After a long day of walking, they stopped to set up camp for the night near Loch an Eilein. Exhausted but satisfied with their adventure, the group looked forward to relaxing by the campfire under the stars before getting some well-earned rest.
Arran Day Part 2

The students continued their exploration of the Arran coastline by hiking along the cliff trails. Along the way, they spotted many seabirds nesting in the cliffs and seals resting on the rocky shore. Their guide pointed out various geological features formed by the relentless pounding of ocean waves over millions of years.
Arran Day 2

Today the class went on several nature hikes through the forests and hills near Arran. They observed many local plant and animal species and discussed how humans have impacted the environment. The day ended with building a campfire and making s'mores before packing up to return home after an educational trip.
Arran Day 1

The students woke up early and boarded the bus for their field trip to Arran. After a long bus ride, they arrived at their first stop, the Brodick Castle gardens, where they explored the beautiful grounds and went on a guided tour of the castle. For lunch, the group ate sandwiches overlooking the sea before heading to their campsite for the night.
Environmental lack of development

Environmental hazards such as droughts, tropical storms, floods, earthquakes, and volcanoes negatively impact development in less economically developed countries (LEDCs). Climatic hazards like droughts and storms are more responsible for loss of life globally than tectonic events. Tropical areas where many LEDCs are located experience more frequent and severe climatic hazards compared to temperate regions. When hazards do occur, their impacts are worse in LEDCs due to factors like buildings not being constructed to withstand disasters and lack of emergency infrastructure.
Causes of the lack of development

This document discusses the factors that have contributed to the lack of economic development in less economically developed countries (LEDCs), which are concentrated in just three continents - South America, Africa, and Asia. It identifies human factors like historical legacies from colonialism, persistent colonial trade patterns, and issues like economic mismanagement, corruption, and wars as causes for the concentration of over 1 billion people living in absolute poverty across these three continents.
Aid

There are three main types of aid:
1) Political (bilateral) aid which is given directly from one government to another, often with conditions attached for the recipient country to buy goods from the donor country.
2) Multilateral aid which is given to international agencies like the UN to distribute as they see fit, often targeting large projects and not always meeting local needs.
3) Charitable aid from NGOs which works closely with local communities to target aid directly to those most in need, making it more effective.
Water availability and quality

The document discusses facts about water availability on Earth. It notes that while oceans hold the vast majority of the planet's water, only 3% is fresh water. Most of this fresh water is unavailable for human use, being locked up in ice sheets. The document then explains that fresh water availability is unevenly distributed among countries, with some experiencing water stress due to high consumption rates and populations. It concludes by noting that global water demand is rising faster than the population as developing countries industrialize and increase irrigation for food.
Water Quality

The majority of water stressed countries are located in Africa and Asia, where governments have less ability to implement measures to address water supply issues like pollution control, increased water efficiency, and population control. Access to clean water varies greatly between more economically developed countries (MEDC) which have near universal access, and less economically developed countries (LEDC) where the average access is 70% but ranges widely between and within countries, with sub-Saharan Africa having the lowest access at 51%. Rural areas generally have lower access to clean water and sanitation than urban areas.
Population and Development

The document compares the population characteristics of more economically developed countries (MEDC's) and less economically developed countries (LEDC's). It finds that MEDC's typically have lower birth rates and death rates, resulting in little or no natural population increase. Their population structures show fewer people under age 15. LEDC's have higher birth rates and natural increase, with more than 30-55% of their populations under age 15.
Measuring Development

The document discusses measuring development between less economically developed countries (LEDCs) and more economically developed countries (MEDC). It defines development as encompassing both economic and social factors like wealth, quality of life, health, literacy, and housing. The most widely used indicator is gross national product (GNP) per capita, which is a country's total output divided by population. However, GNP is a more reliable indicator for MEDCs than LEDCs because LEDC statistics are less available and accurate, and GNP does not account for subsistence farming common in LEDCs. Other development indicators include birth rate, energy consumption, doctors per person, and literacy rates.
Creating a weblog

This document discusses creating a geography department blog to communicate information to students. It defines what a blog is, explains how a blog can be useful for following up on lessons, providing homework links and reminders. It also provides information on setting up a free blog using Blogger.com and including links to videos on YouTube, PowerPoints on SlideShare, and homework on Box.net.
OS Symbols Bingo Game

The document instructs the reader to choose 9 Ordnance Survey map symbols, draw a 3x3 grid, and place one map symbol in each square of the grid to create a bingo card.
More from abblanchgeography (13)
Recently uploaded
Choosing The Best AWS Service For Your Website + API.pptx

Have you ever been confused by the myriad of choices offered by AWS for hosting a website or an API?
Lambda, Elastic Beanstalk, Lightsail, Amplify, S3 (and more!) can each host websites + APIs. But which one should we choose?
Which one is cheapest? Which one is fastest? Which one will scale to meet our needs?
Join me in this session as we dive into each AWS hosting service to determine which one is best for your scenario and explain why!
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

Direct losses from downtime in 1 minute = $5-$10 thousand dollars. Reputation is priceless.
As part of the talk, we will consider the architectural strategies necessary for the development of highly loaded fintech solutions. We will focus on using queues and streaming to efficiently work and manage large amounts of data in real-time and to minimize latency.
We will focus special attention on the architectural patterns used in the design of the fintech system, microservices and event-driven architecture, which ensure scalability, fault tolerance, and consistency of the entire system.
"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk

At this talk we will discuss DDoS protection tools and best practices, discuss network architectures and what AWS has to offer. Also, we will look into one of the largest DDoS attacks on Ukrainian infrastructure that happened in February 2022. We'll see, what techniques helped to keep the web resources available for Ukrainians and how AWS improved DDoS protection for all customers based on Ukraine experience
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The typical problem in product engineering is not bad strategy, so much as “no strategy”. This leads to confusion, lack of motivation, and incoherent action. The next time you look for a strategy and find an empty space, instead of waiting for it to be filled, I will show you how to fill it in yourself. If you’re wrong, it forces a correction. If you’re right, it helps create focus. I’ll share how I’ve approached this in the past, both what works and lessons for what didn’t work so well.
A Deep Dive into ScyllaDB's Architecture

This talk will cover ScyllaDB Architecture from the cluster-level view and zoom in on data distribution and internal node architecture. In the process, we will learn the secret sauce used to get ScyllaDB's high availability and superior performance. We will also touch on the upcoming changes to ScyllaDB architecture, moving to strongly consistent metadata and tablets.
JavaLand 2024: Application Development Green Masterplan

My presentation slides I used at JavaLand 2024
High performance Serverless Java on AWS- GoTo Amsterdam 2024

Java is for many years one of the most popular programming languages, but it used to have hard times in the Serverless community. Java is known for its high cold start times and high memory footprint, comparing to other programming languages like Node.js and Python. In this talk I'll look at the general best practices and techniques we can use to decrease memory consumption, cold start times for Java Serverless development on AWS including GraalVM (Native Image) and AWS own offering SnapStart based on Firecracker microVM snapshot and restore and CRaC (Coordinated Restore at Checkpoint) runtime hooks. I'll also provide a lot of benchmarking on Lambda functions trying out various deployment package sizes, Lambda memory settings, Java compilation options and HTTP (a)synchronous clients and measure their impact on cold and warm start times.
Apps Break Data

How information systems are built or acquired puts information, which is what they should be about, in a secondary place. Our language adapted accordingly, and we no longer talk about information systems but applications. Applications evolved in a way to break data into diverse fragments, tightly coupled with applications and expensive to integrate. The result is technical debt, which is re-paid by taking even bigger "loans", resulting in an ever-increasing technical debt. Software engineering and procurement practices work in sync with market forces to maintain this trend. This talk demonstrates how natural this situation is. The question is: can something be done to reverse the trend?
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Northern Engraving | Nameplate Manufacturing Process - 2024

Manufacturing custom quality metal nameplates and badges involves several standard operations. Processes include sheet prep, lithography, screening, coating, punch press and inspection. All decoration is completed in the flat sheet with adhesive and tooling operations following. The possibilities for creating unique durable nameplates are endless. How will you create your brand identity? We can help!
Demystifying Knowledge Management through Storytelling

The Department of Veteran Affairs (VA) invited Taylor Paschal, Knowledge & Information Management Consultant at Enterprise Knowledge, to speak at a Knowledge Management Lunch and Learn hosted on June 12, 2024. All Office of Administration staff were invited to attend and received professional development credit for participating in the voluntary event.
The objectives of the Lunch and Learn presentation were to:
- Review what KM ‘is’ and ‘isn’t’
- Understand the value of KM and the benefits of engaging
- Define and reflect on your “what’s in it for me?”
- Share actionable ways you can participate in Knowledge - - Capture & Transfer
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors

Join us to learn how UiPath Apps can directly and easily interact with prebuilt connectors via Integration Service--including Salesforce, ServiceNow, Open GenAI, and more.
The best part is you can achieve this without building a custom workflow! Say goodbye to the hassle of using separate automations to call APIs. By seamlessly integrating within App Studio, you can now easily streamline your workflow, while gaining direct access to our Connector Catalog of popular applications.
We’ll discuss and demo the benefits of UiPath Apps and connectors including:
Creating a compelling user experience for any software, without the limitations of APIs.
Accelerating the app creation process, saving time and effort
Enjoying high-performance CRUD (create, read, update, delete) operations, for
seamless data management.
Speakers:
Russell Alfeche, Technology Leader, RPA at qBotic and UiPath MVP
Charlie Greenberg, host
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Recently uploaded (20)
Choosing The Best AWS Service For Your Website + API.pptx

Choosing The Best AWS Service For Your Website + API.pptx
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

"$10 thousand per minute of downtime: architecture, queues, streaming and fin...
"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk

"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk
9 CEO's who hit $100m ARR Share Their Top Growth Tactics Nathan Latka, Founde...

9 CEO's who hit $100m ARR Share Their Top Growth Tactics Nathan Latka, Founde...
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...
JavaLand 2024: Application Development Green Masterplan

JavaLand 2024: Application Development Green Masterplan
High performance Serverless Java on AWS- GoTo Amsterdam 2024

High performance Serverless Java on AWS- GoTo Amsterdam 2024
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
Northern Engraving | Nameplate Manufacturing Process - 2024

Northern Engraving | Nameplate Manufacturing Process - 2024
Demystifying Knowledge Management through Storytelling

Demystifying Knowledge Management through Storytelling
Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors

Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx