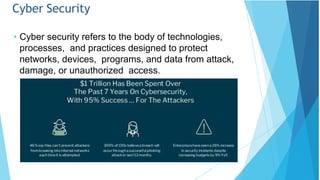
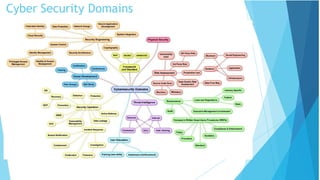
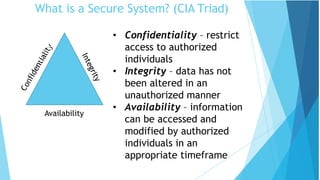
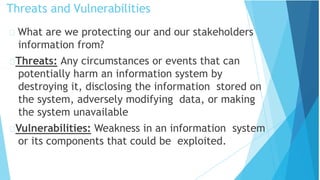
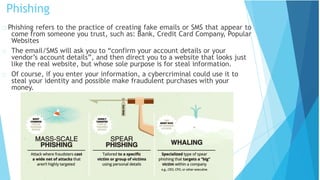
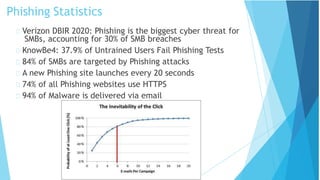
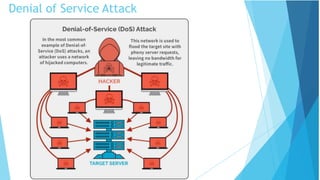
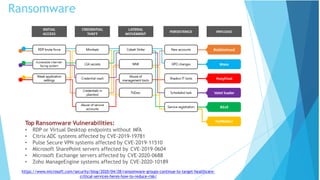
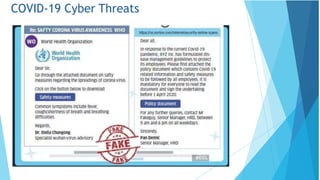
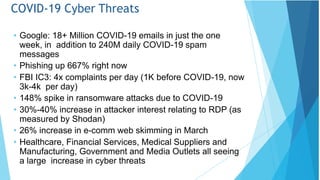
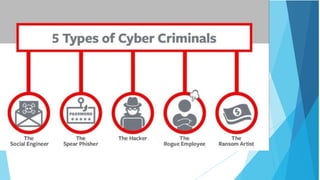
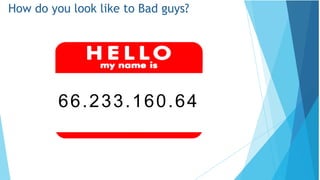
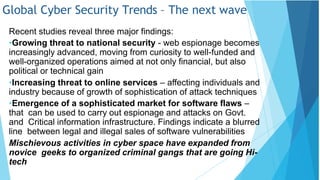
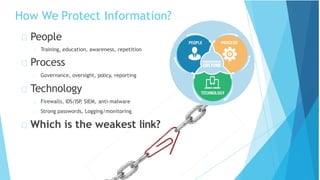
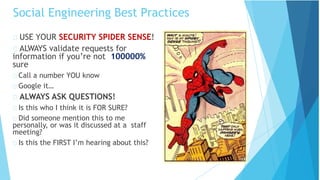
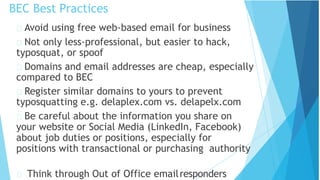
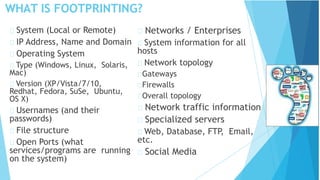
The document discusses various aspects of cyber security. It begins by highlighting the importance of cyber security and noting that the only truly secure system is one that is powered off, locked in a bunker, and guarded. It then discusses key concepts in cyber security including threats, vulnerabilities, and the CIA triad of confidentiality, integrity and availability. The document also covers specific cyber threats such as phishing, malware, ransomware, business email compromise, and COVID-19 related cyber threats. It discusses the roles and responsibilities of cyber security professionals and important best practices for security.