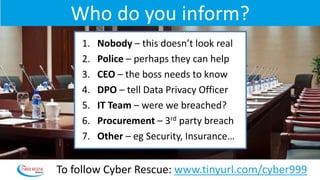
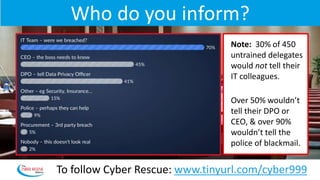
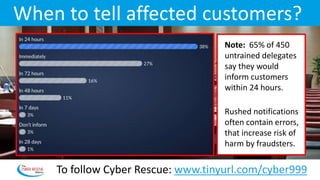
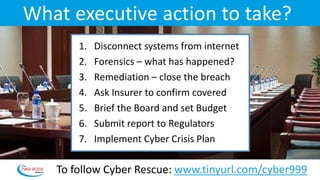
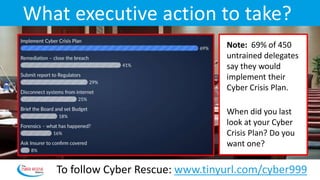
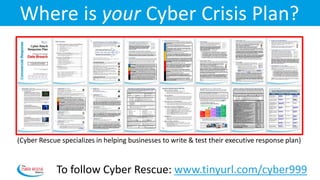
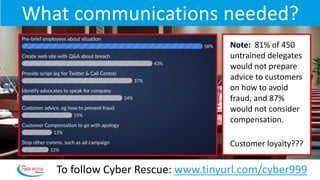
The document details a cyber attack executive simulation involving 450 delegates at a finance conference, highlighting how untrained executives often disagree on crucial responses during a crisis. Key findings include significant hesitance to inform IT and executives of a breach, and the necessity for structured communication strategies post-incident. The simulation underscores the importance of regular training for executive teams to effectively manage cyber incidents and their repercussions.