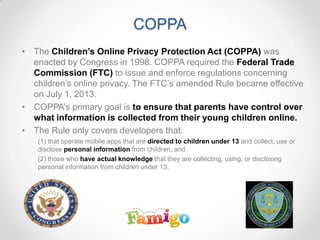
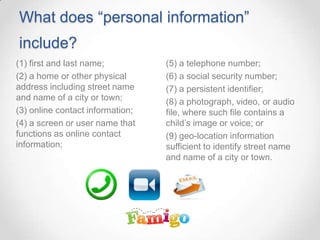
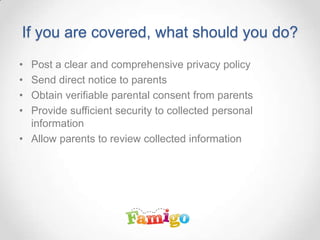
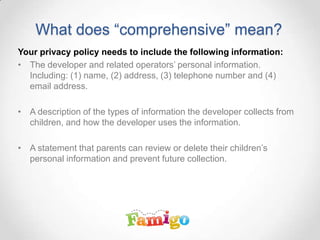
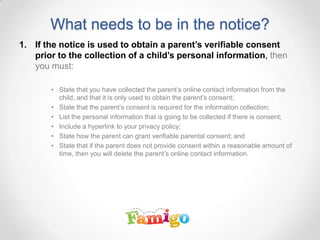
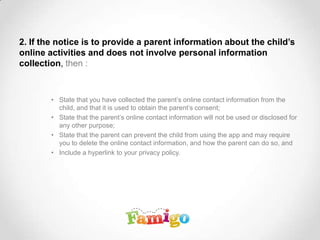
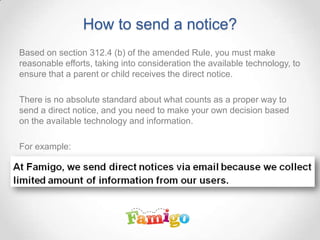
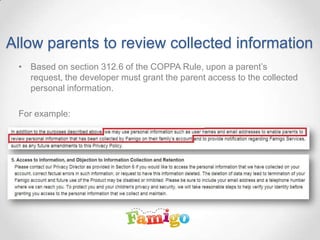
The document provides an overview of the Children's Online Privacy Protection Act (COPPA), detailing its purpose, which is to ensure parental control over the collection of personal information from children under 13. It outlines requirements for developers, including posting a comprehensive privacy policy, sending direct notices to parents, and obtaining verifiable parental consent. Additionally, it explains what constitutes personal information and how developers should manage security and access related to children's data.