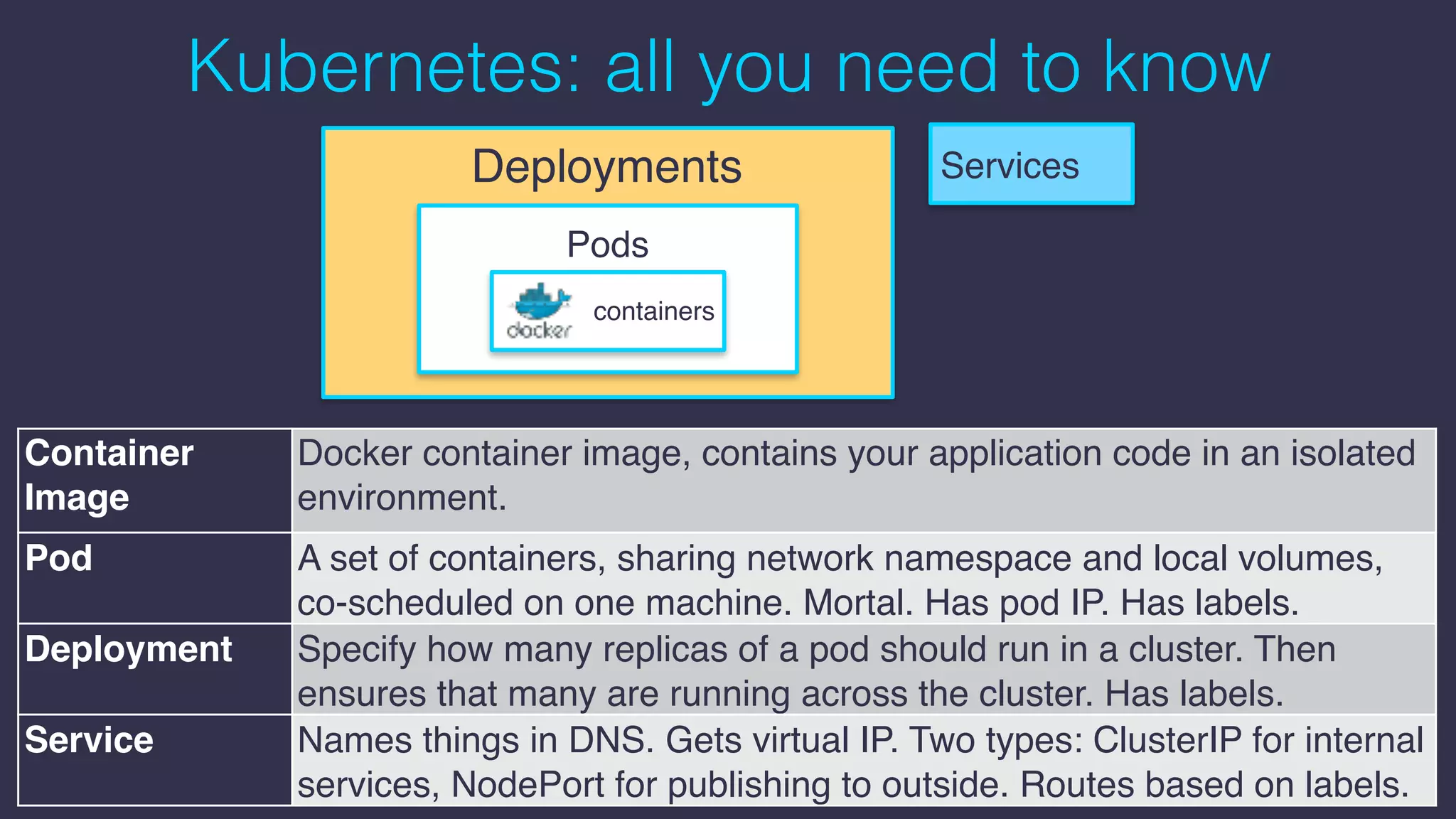
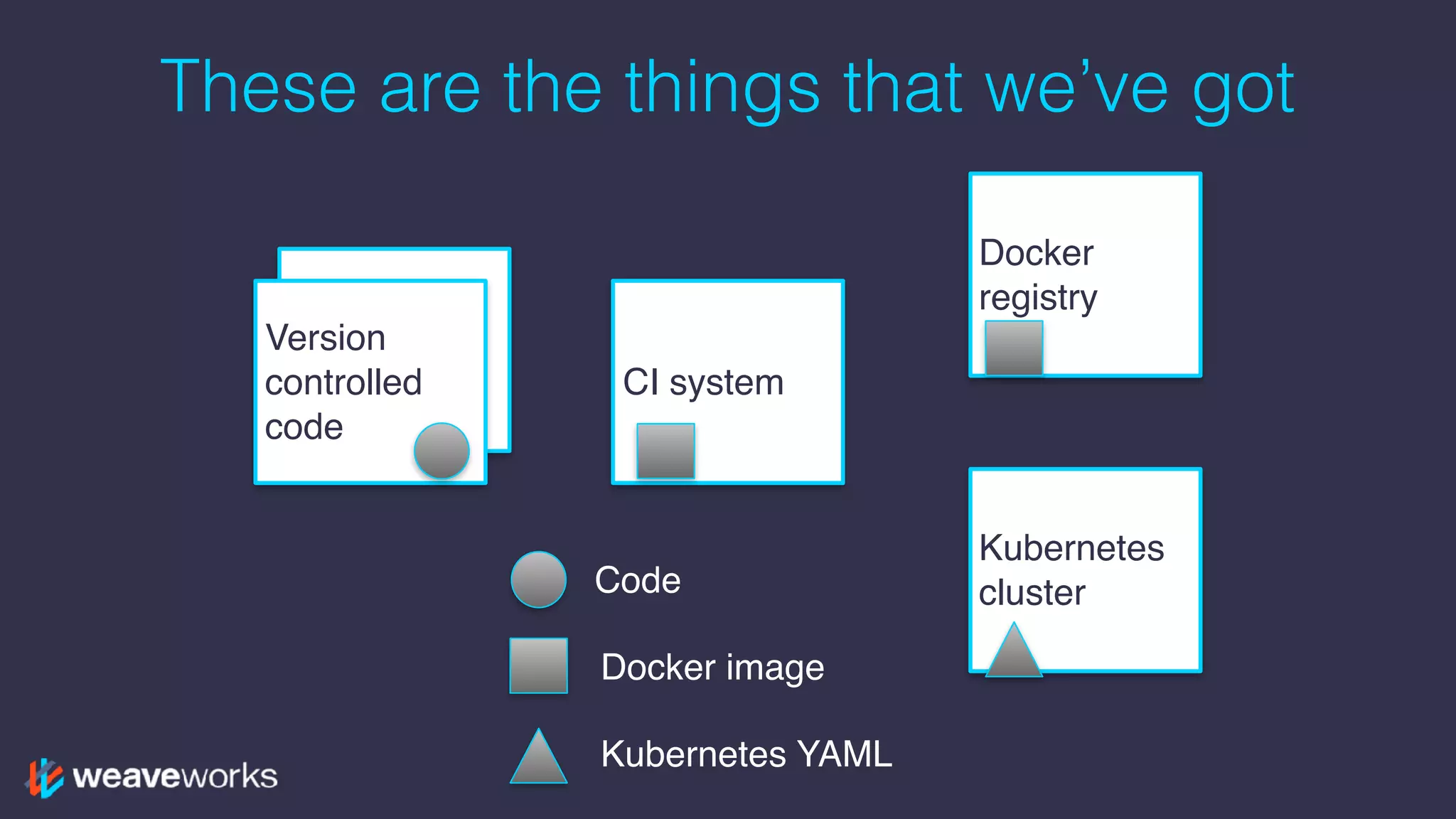
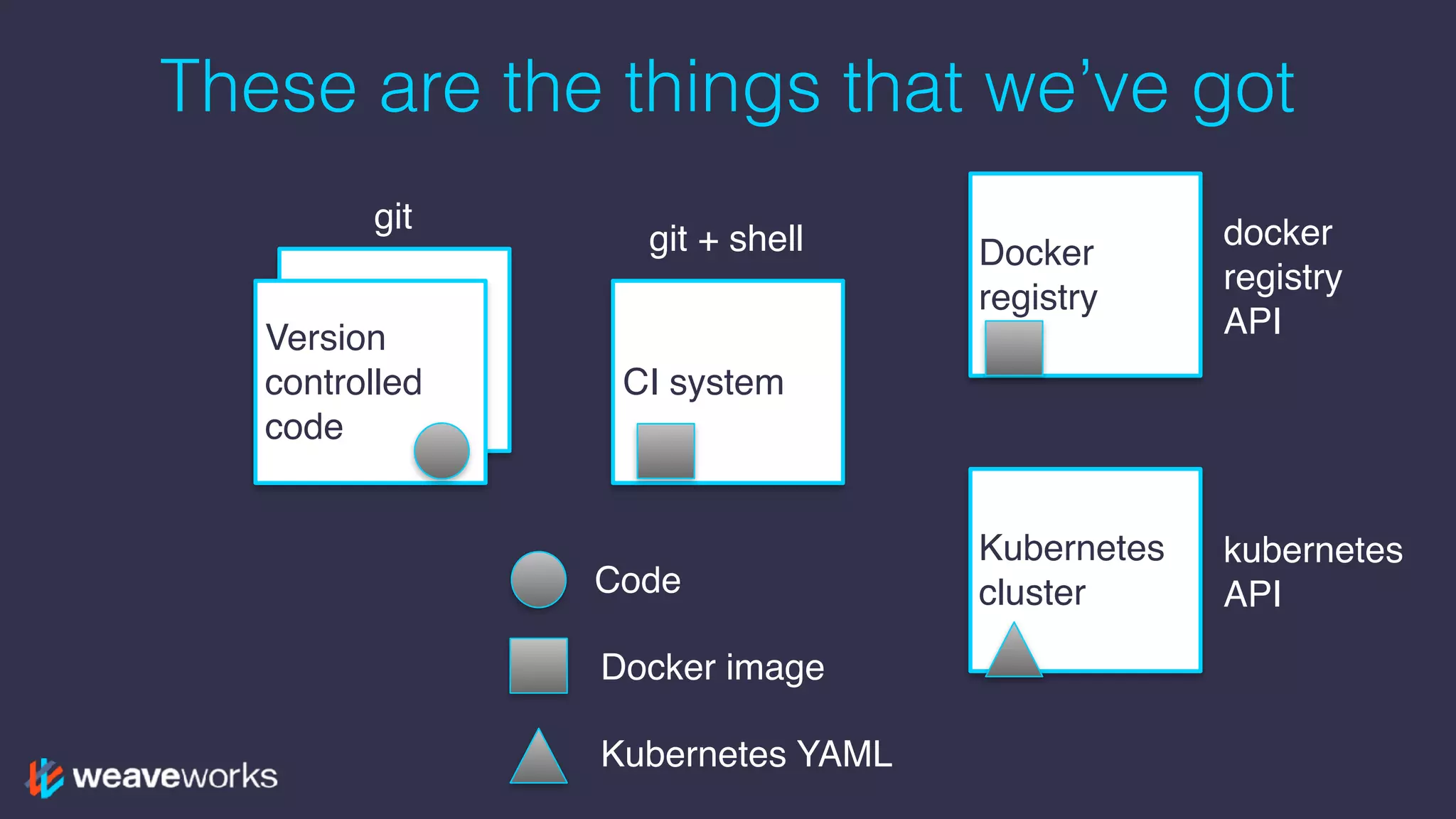
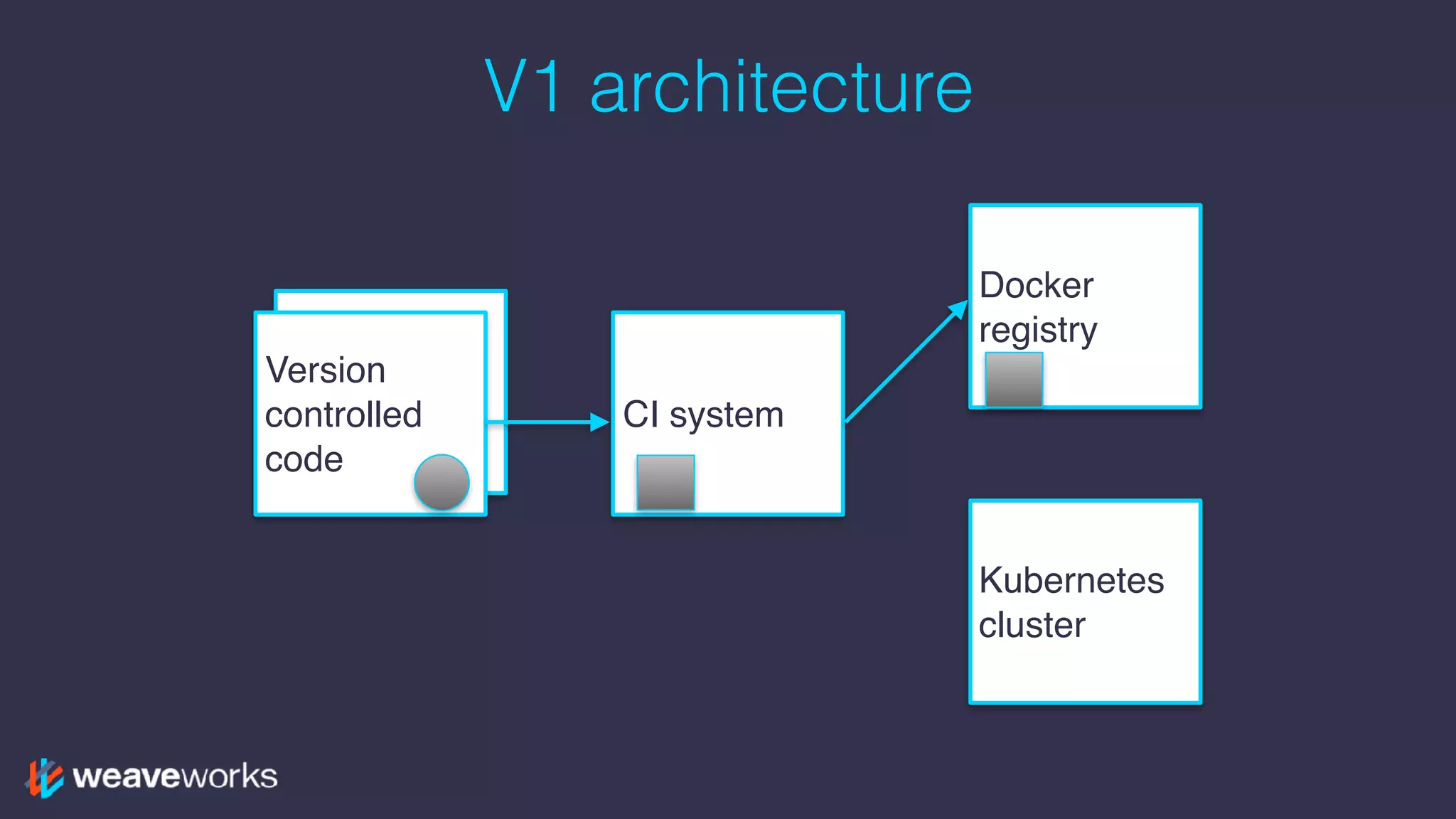
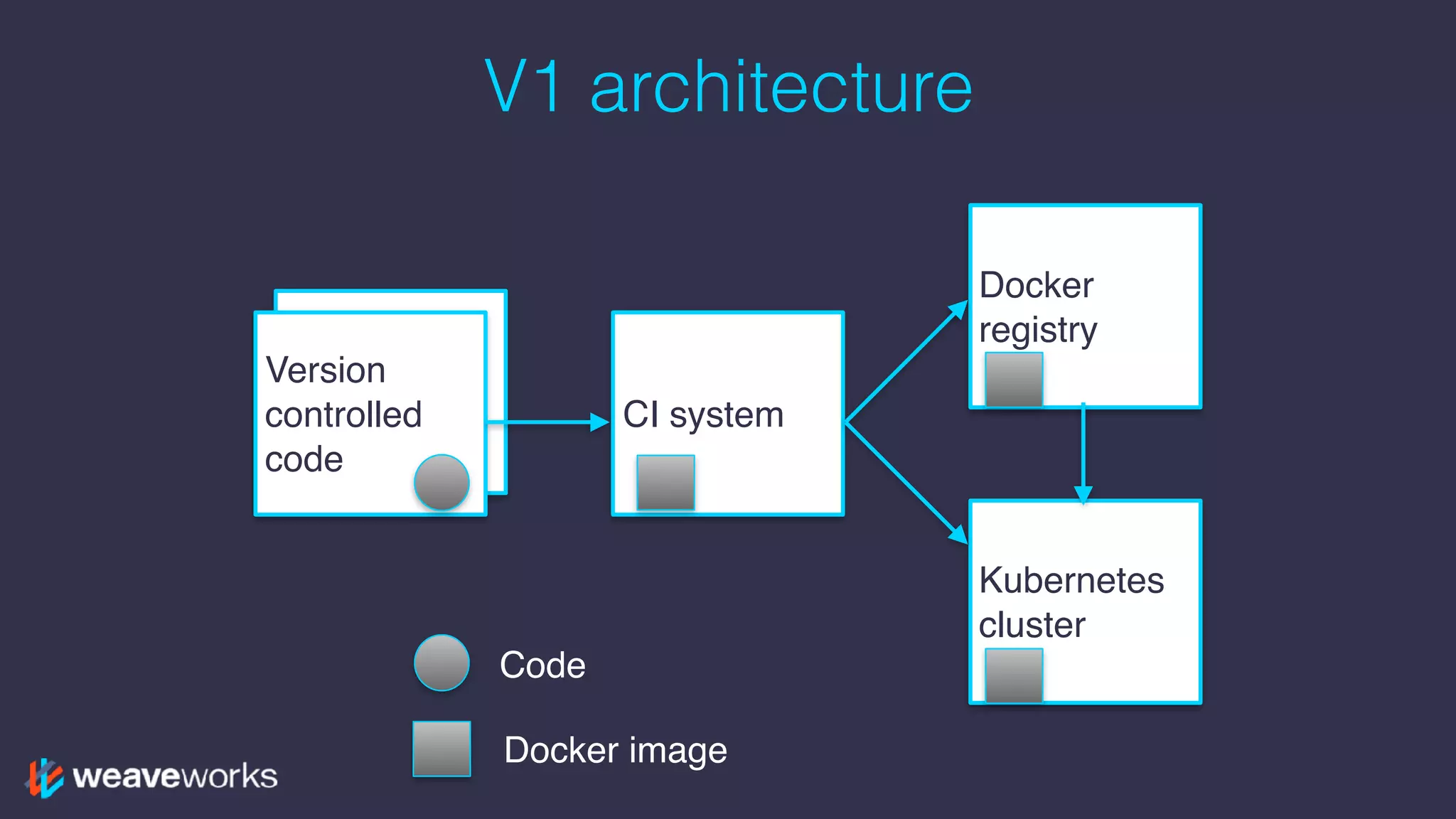
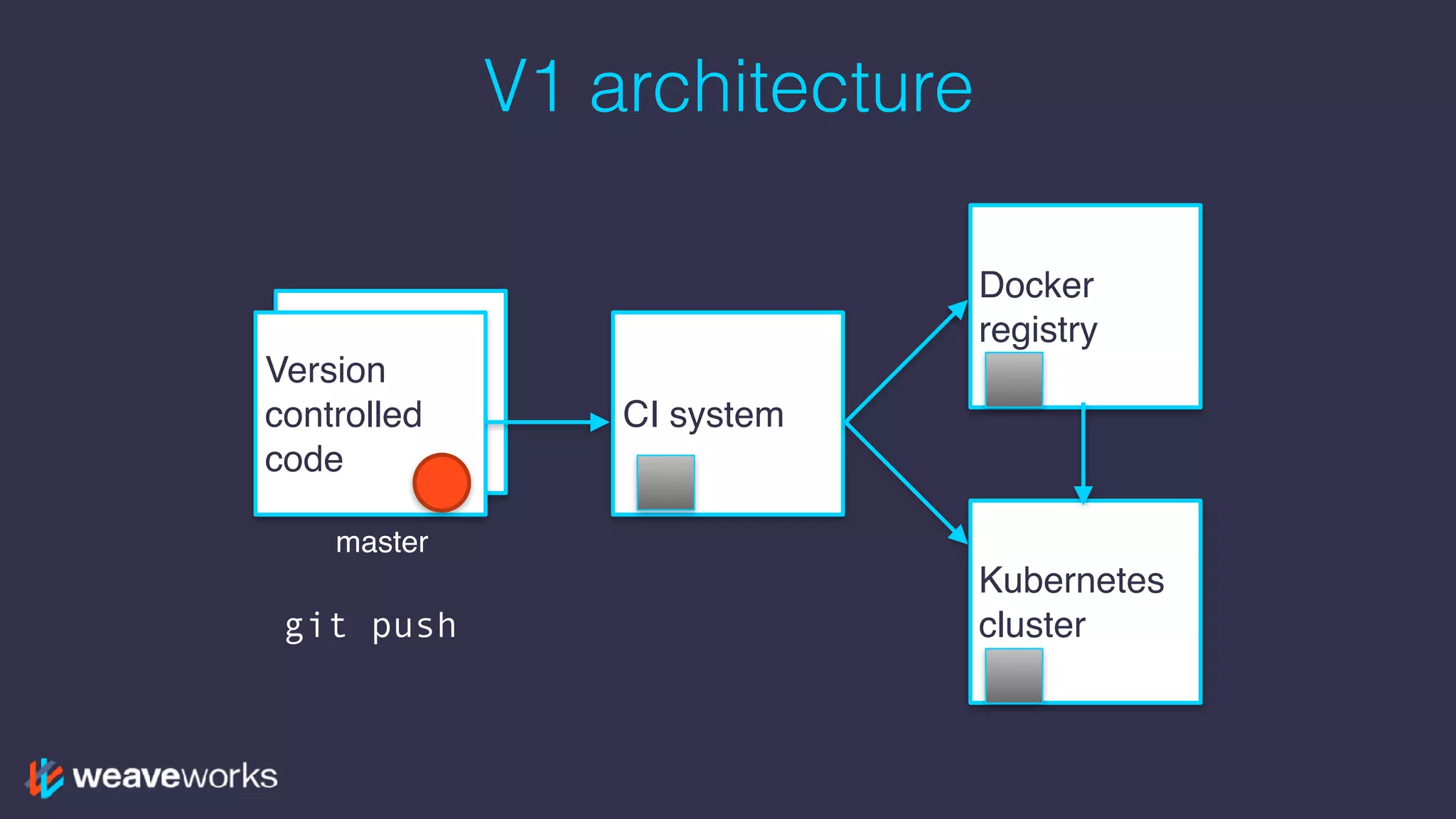
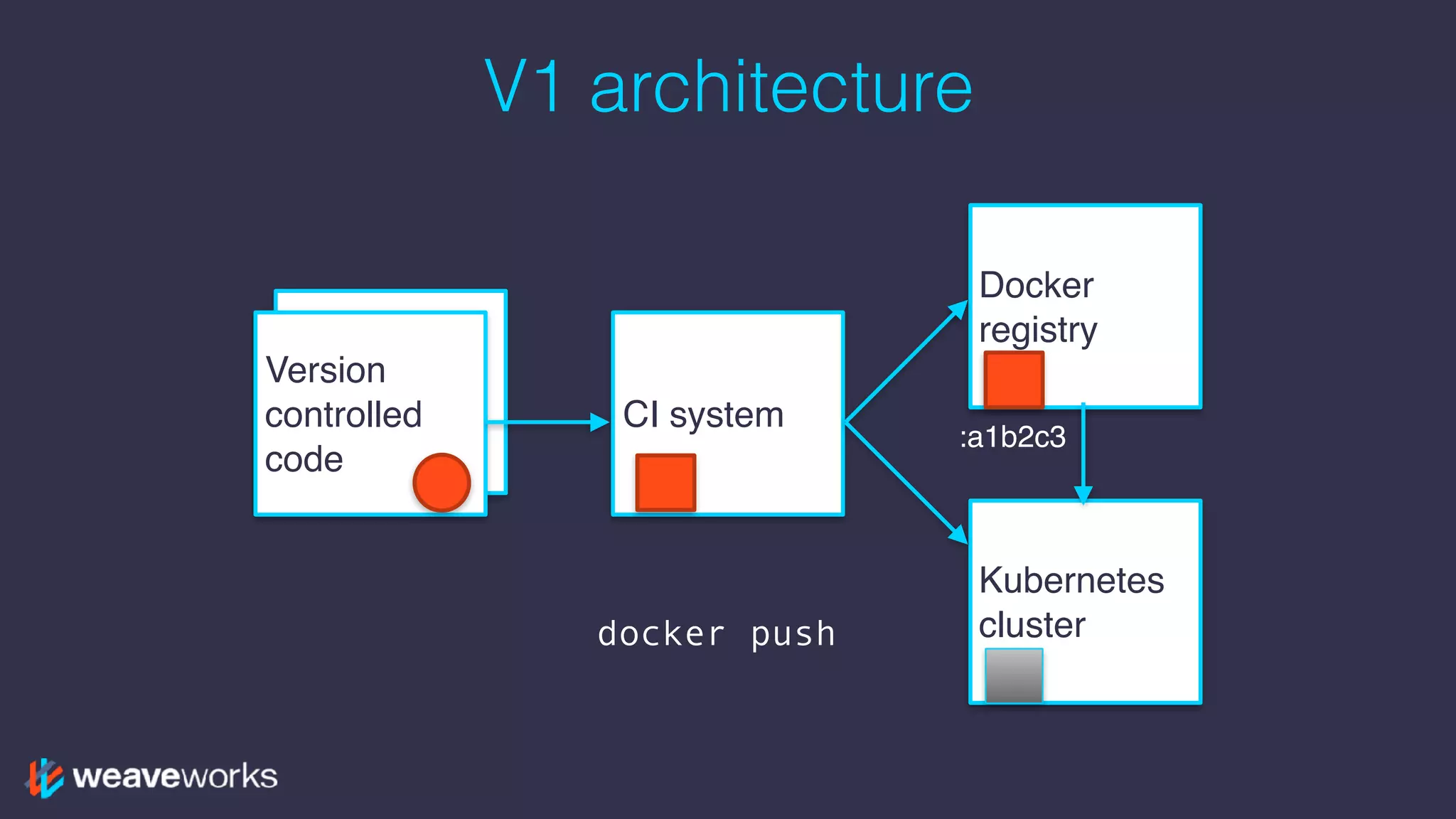
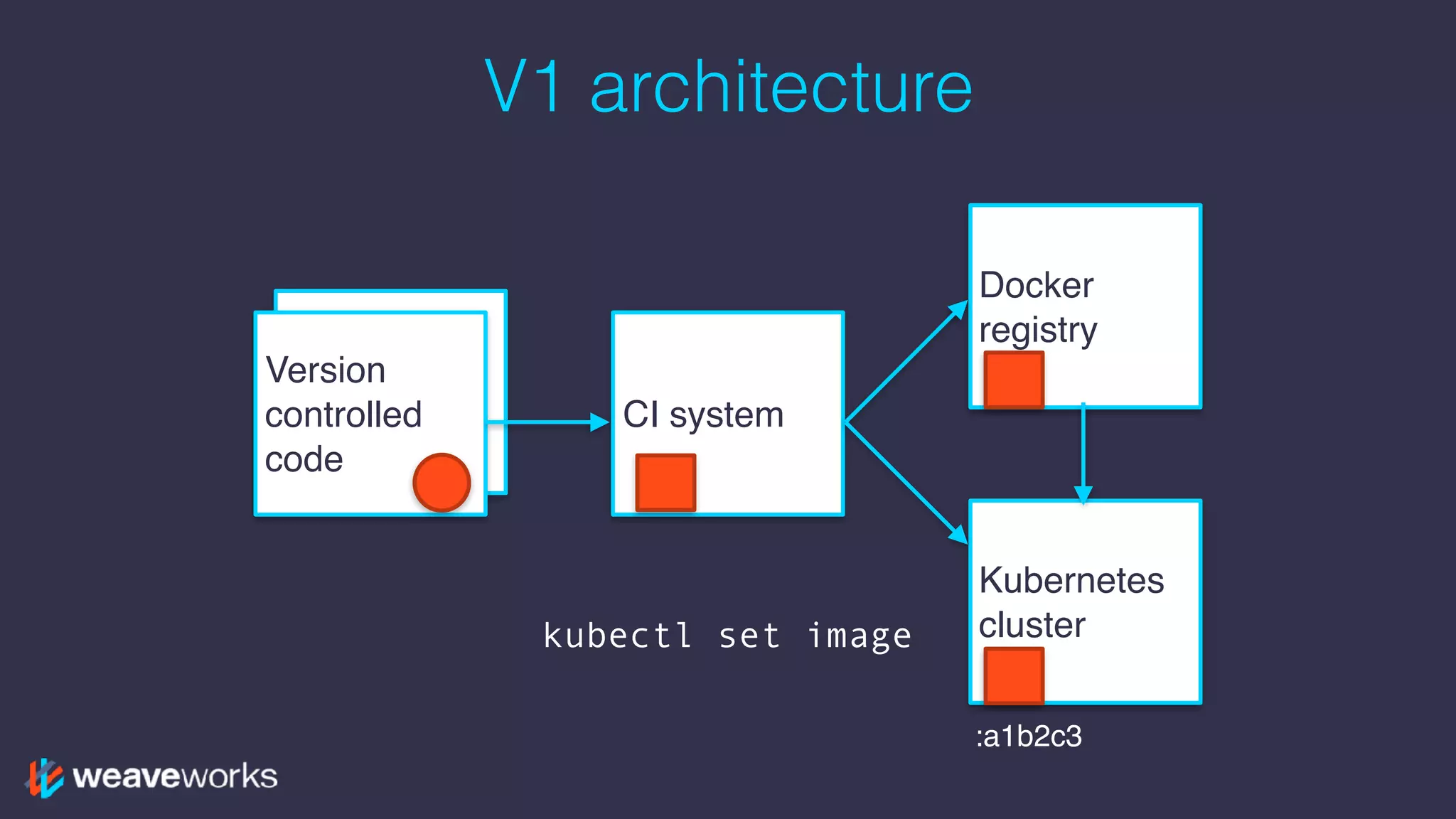
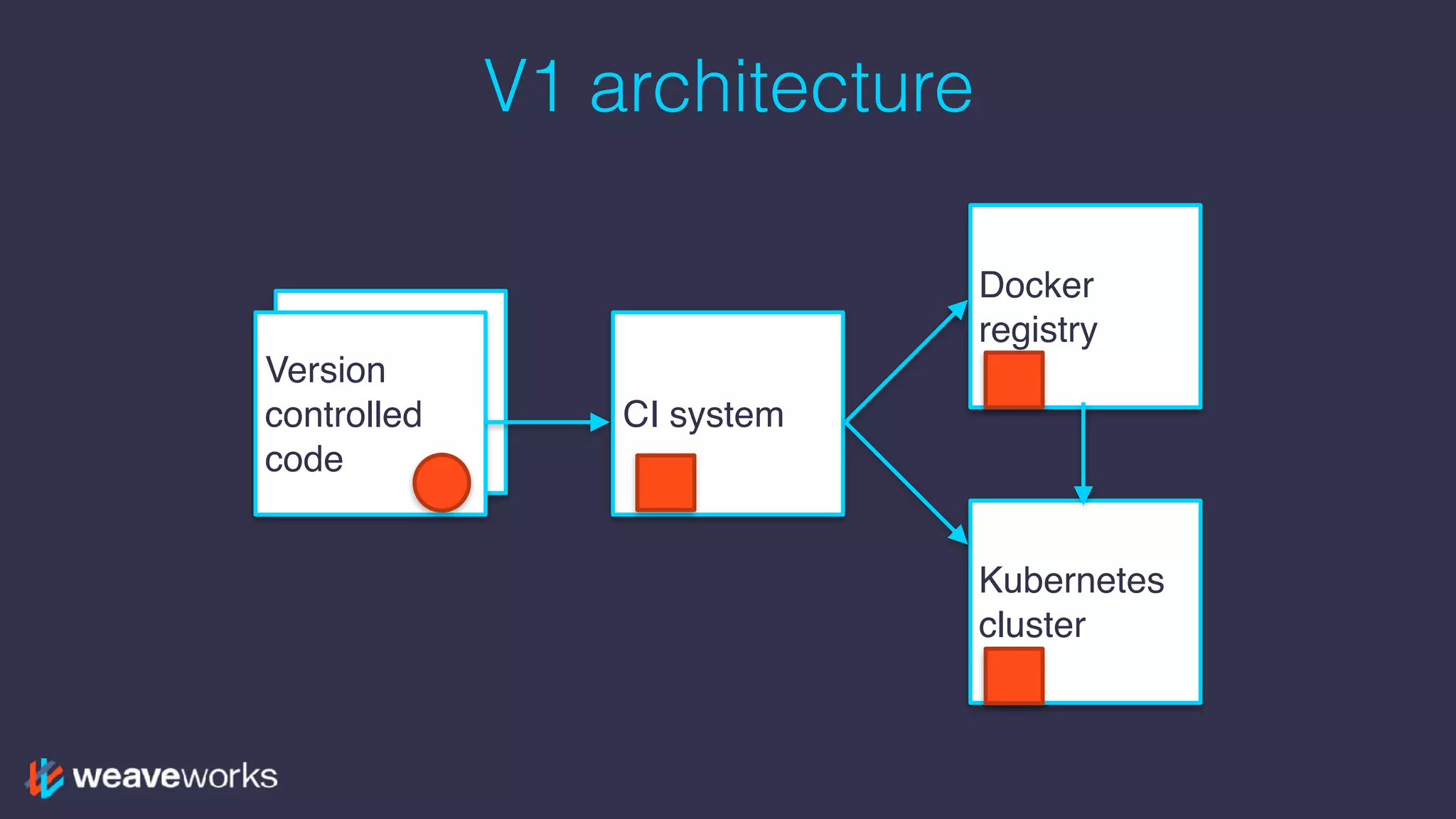
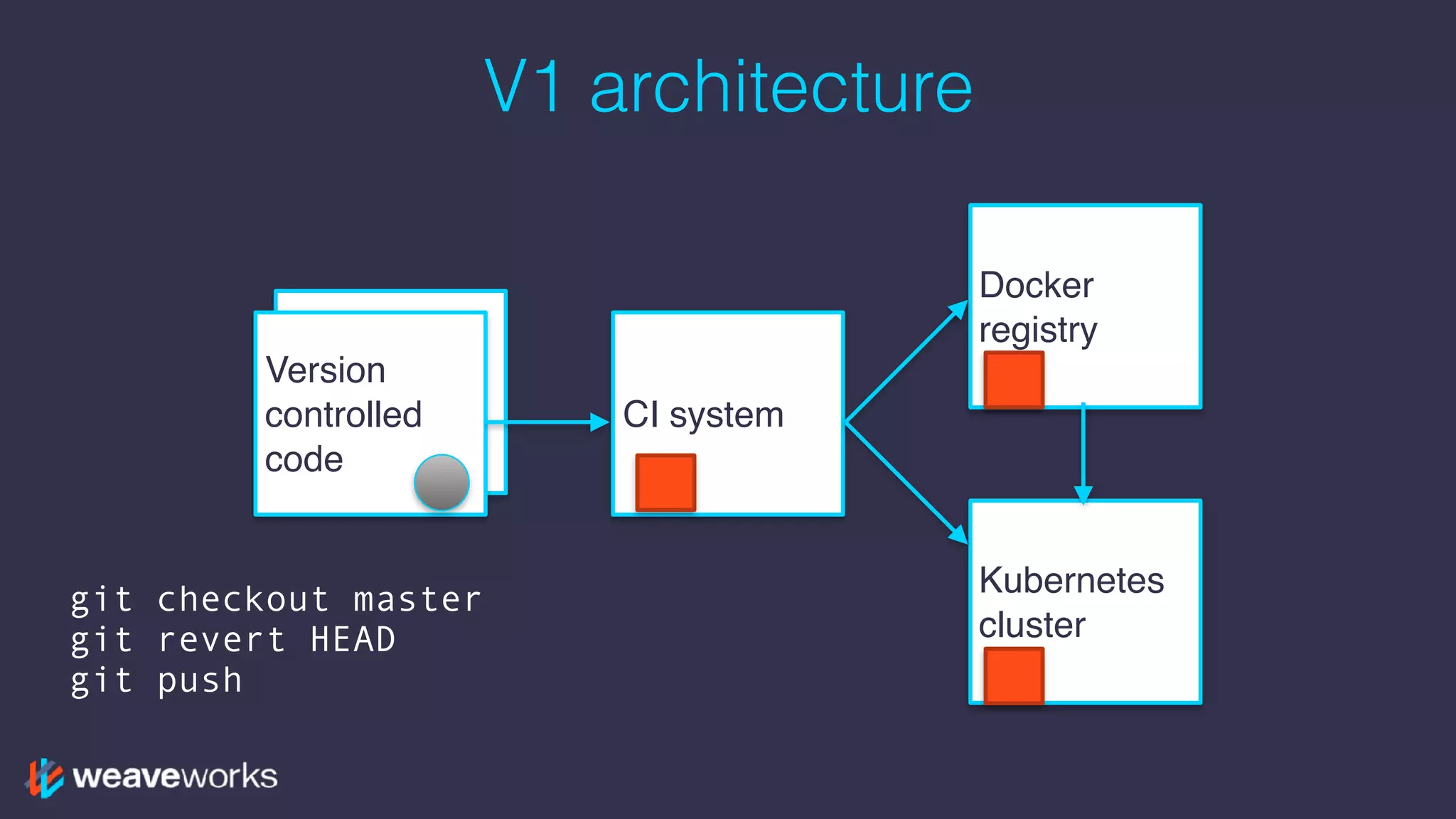
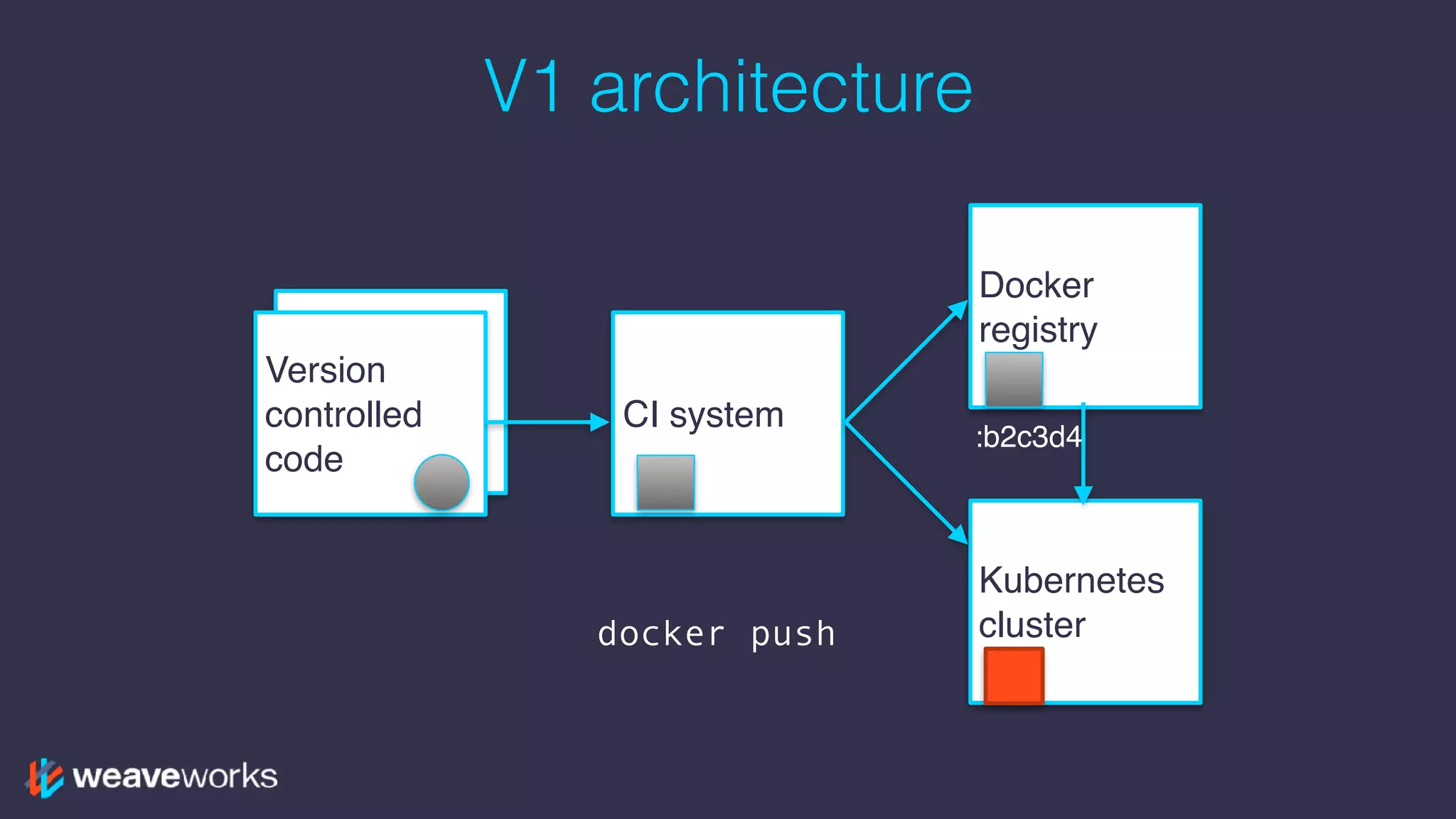
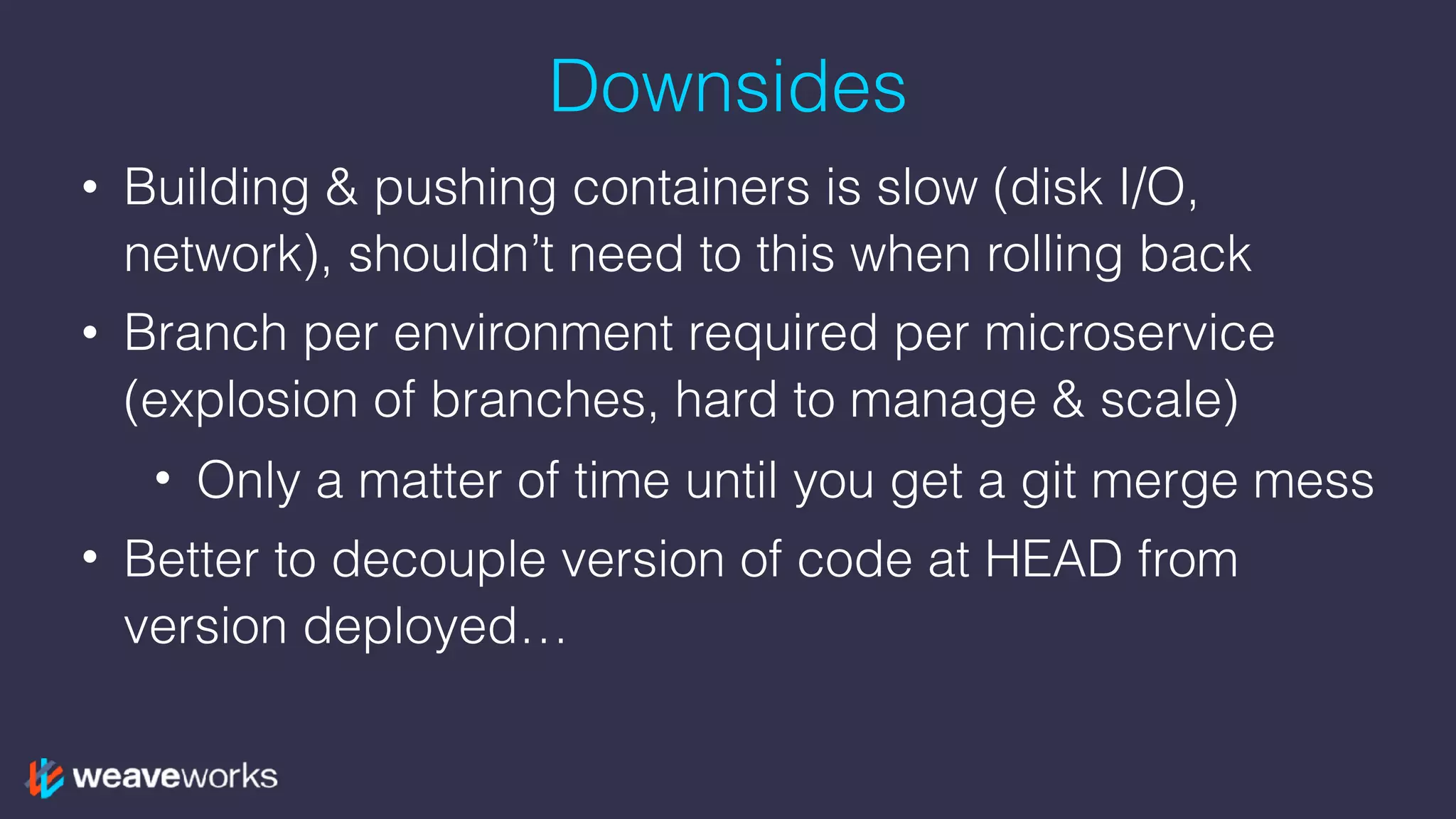
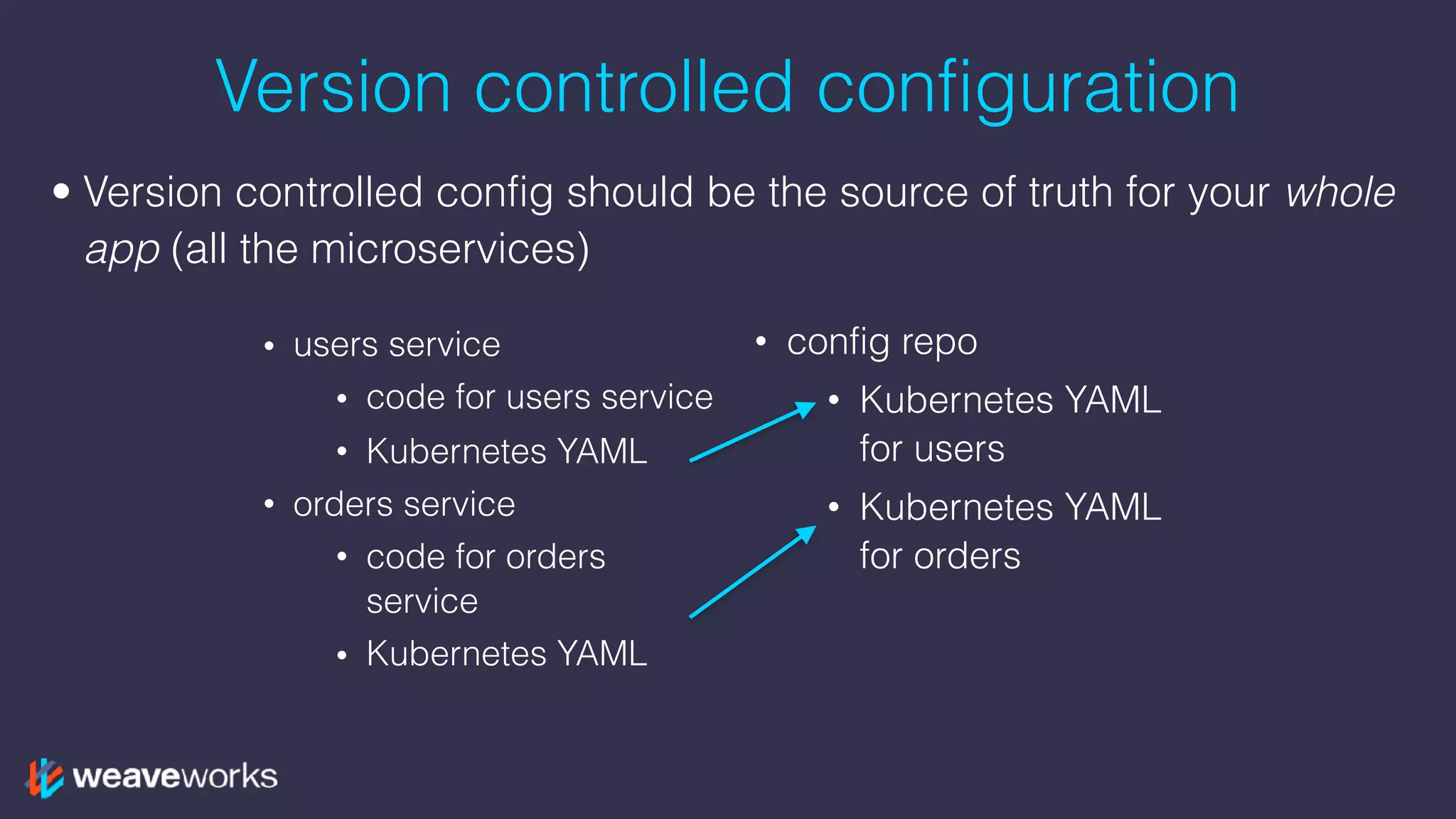
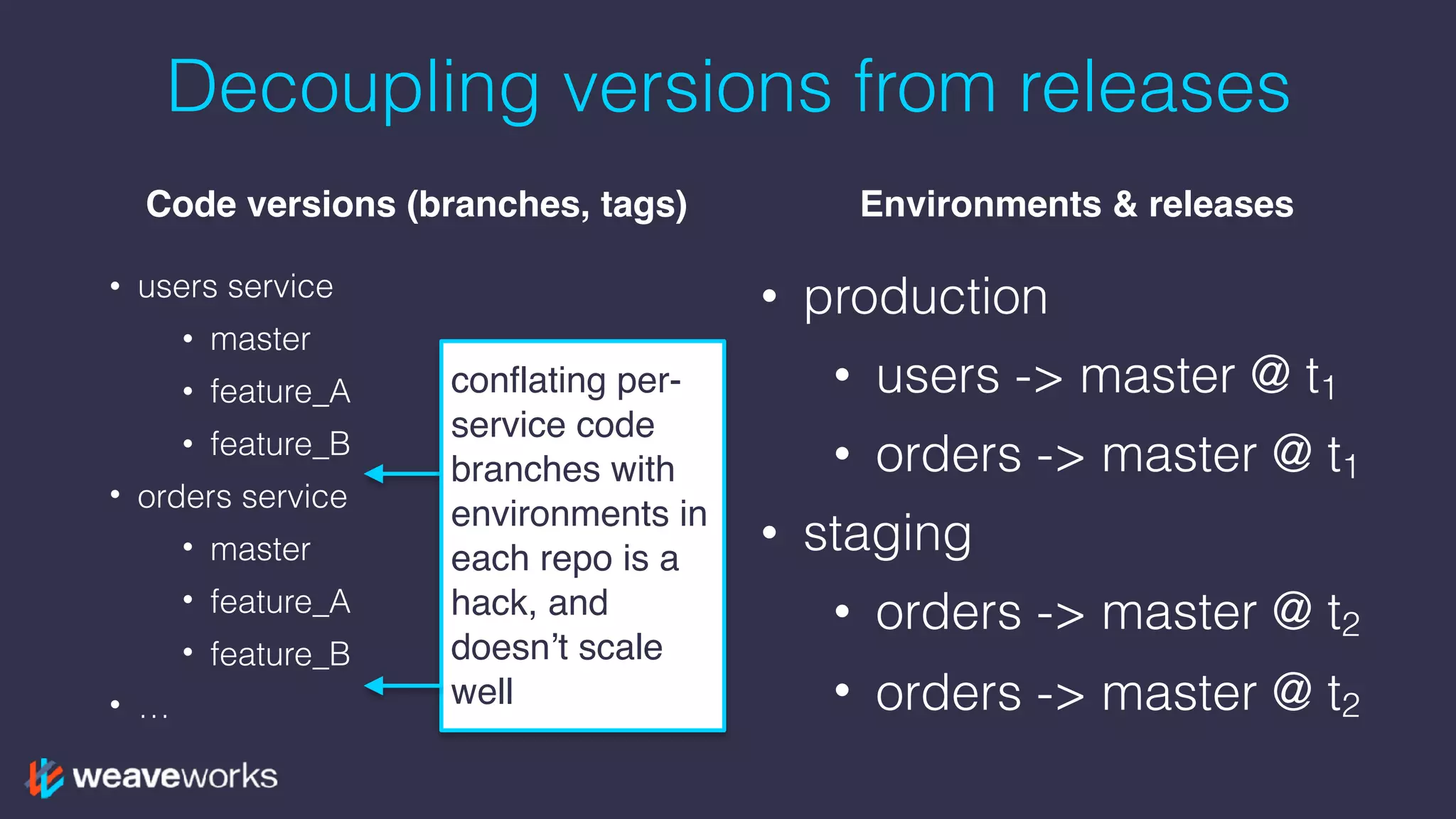
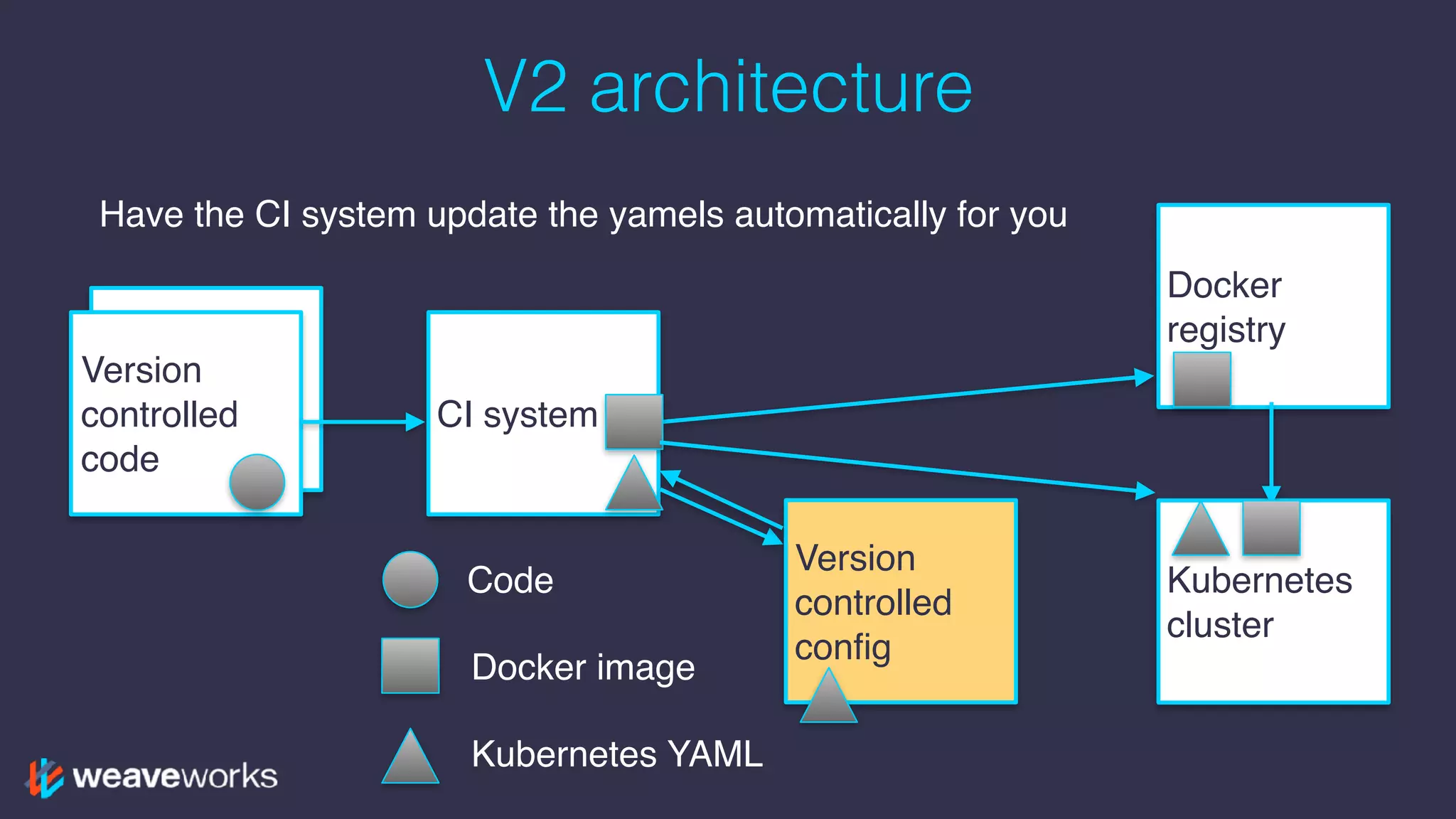
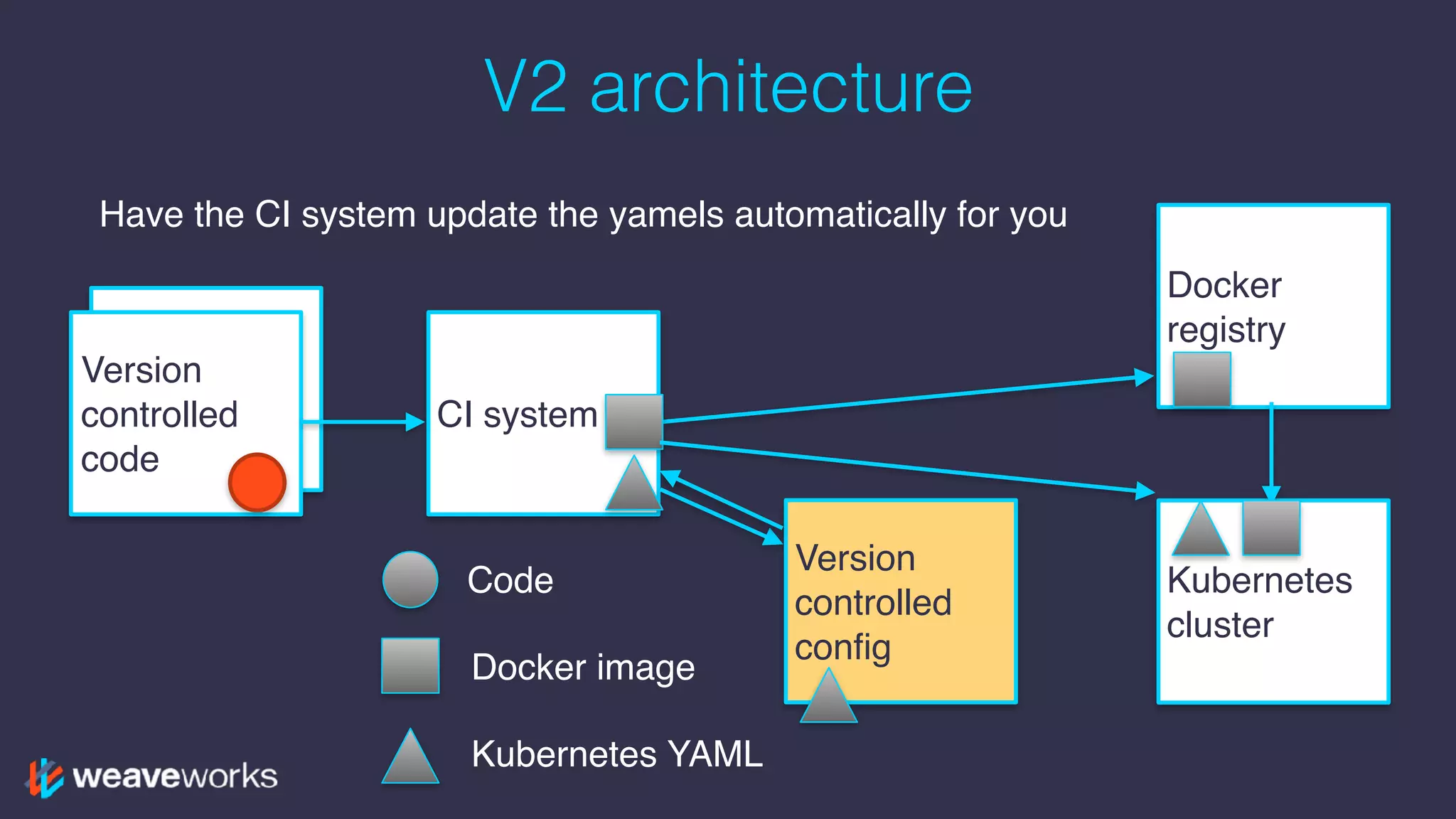
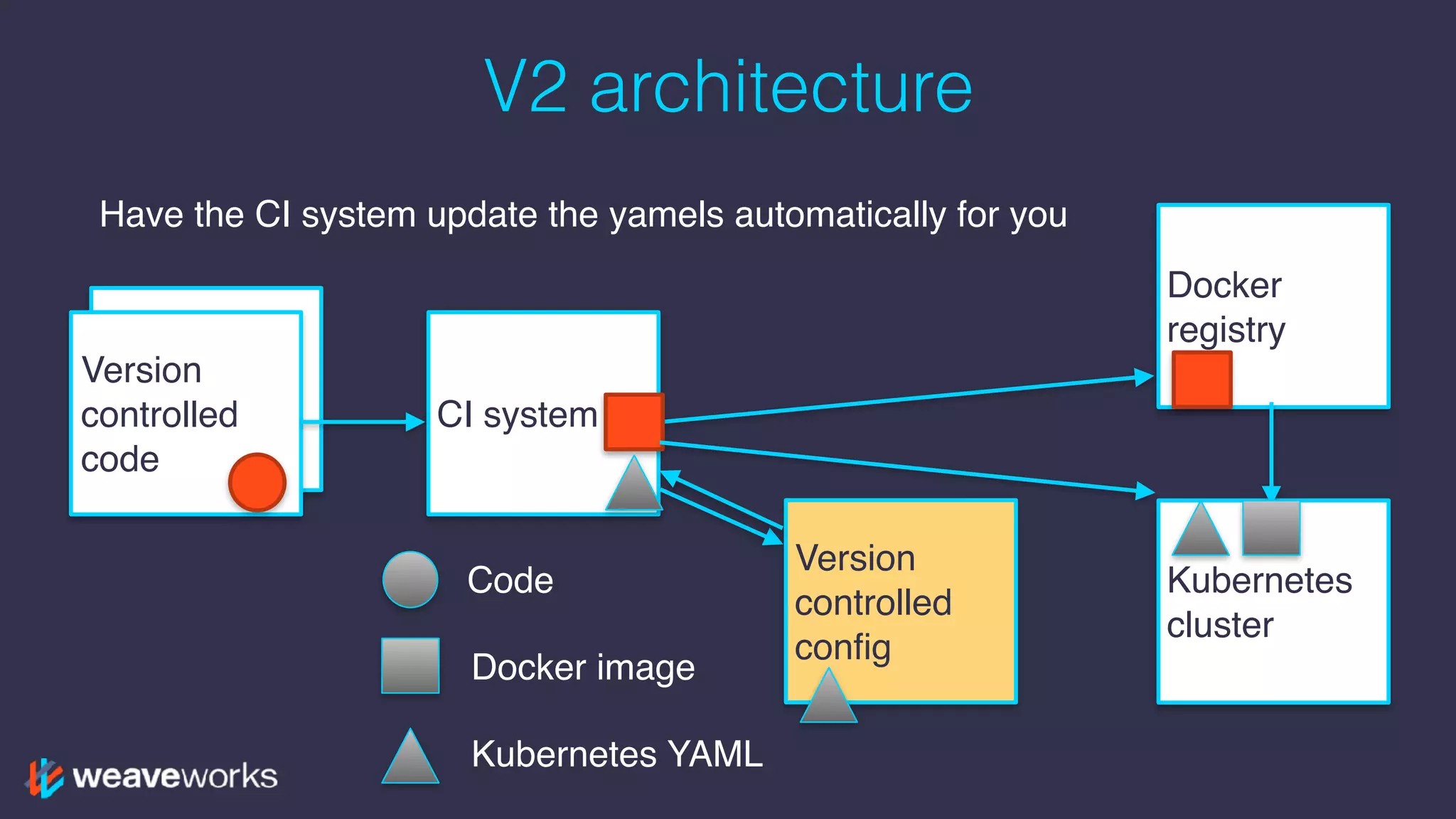
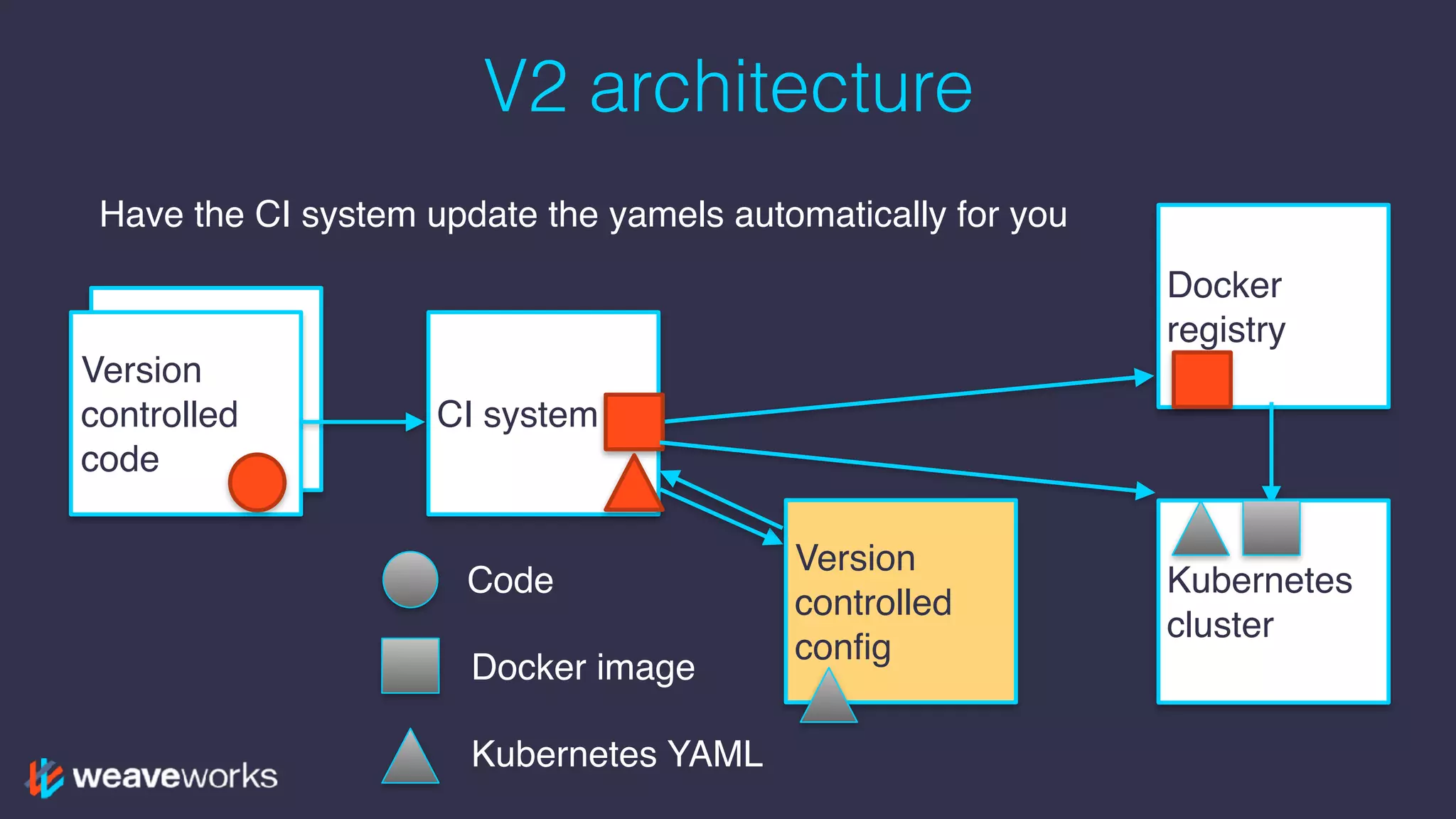
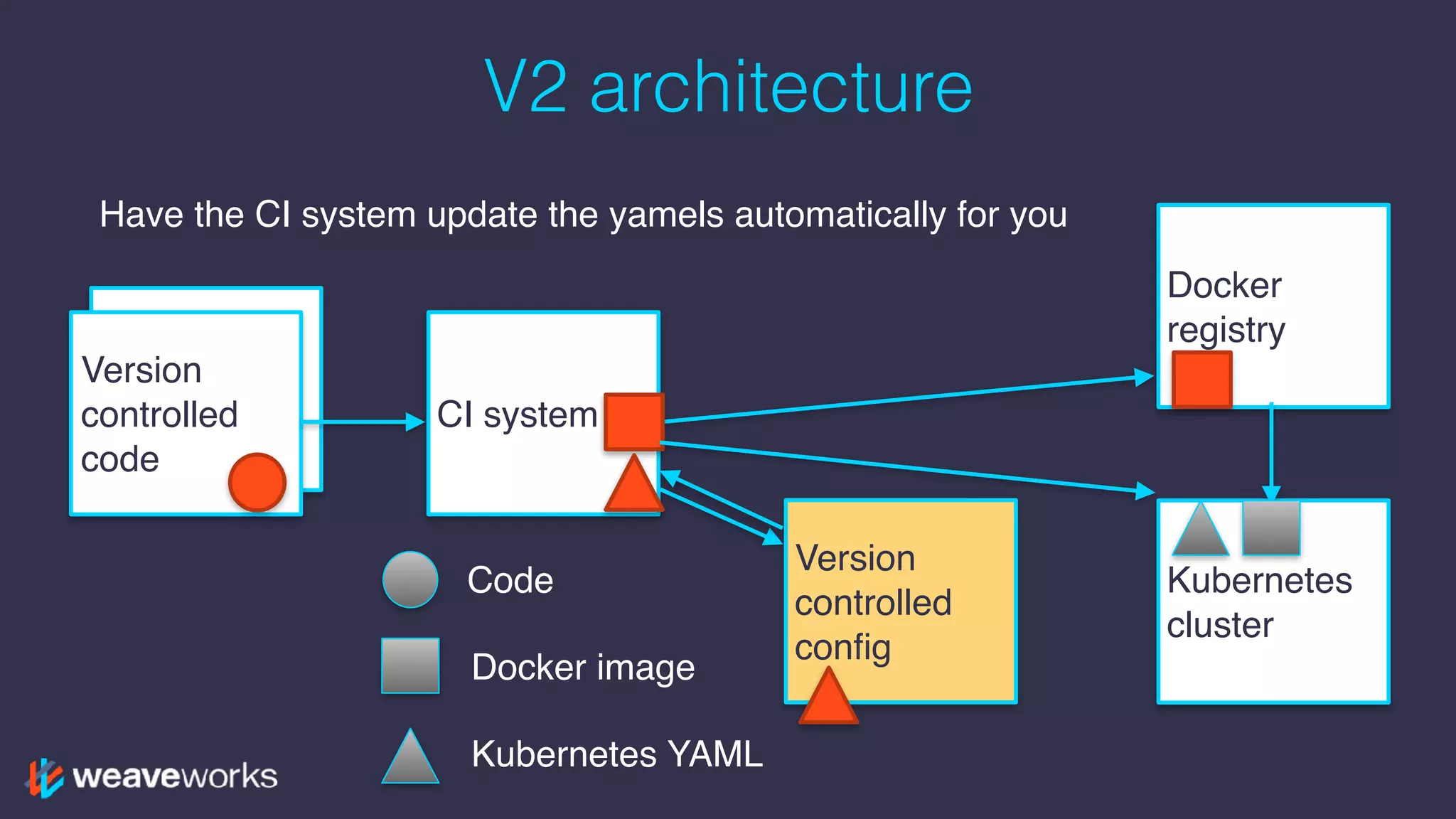
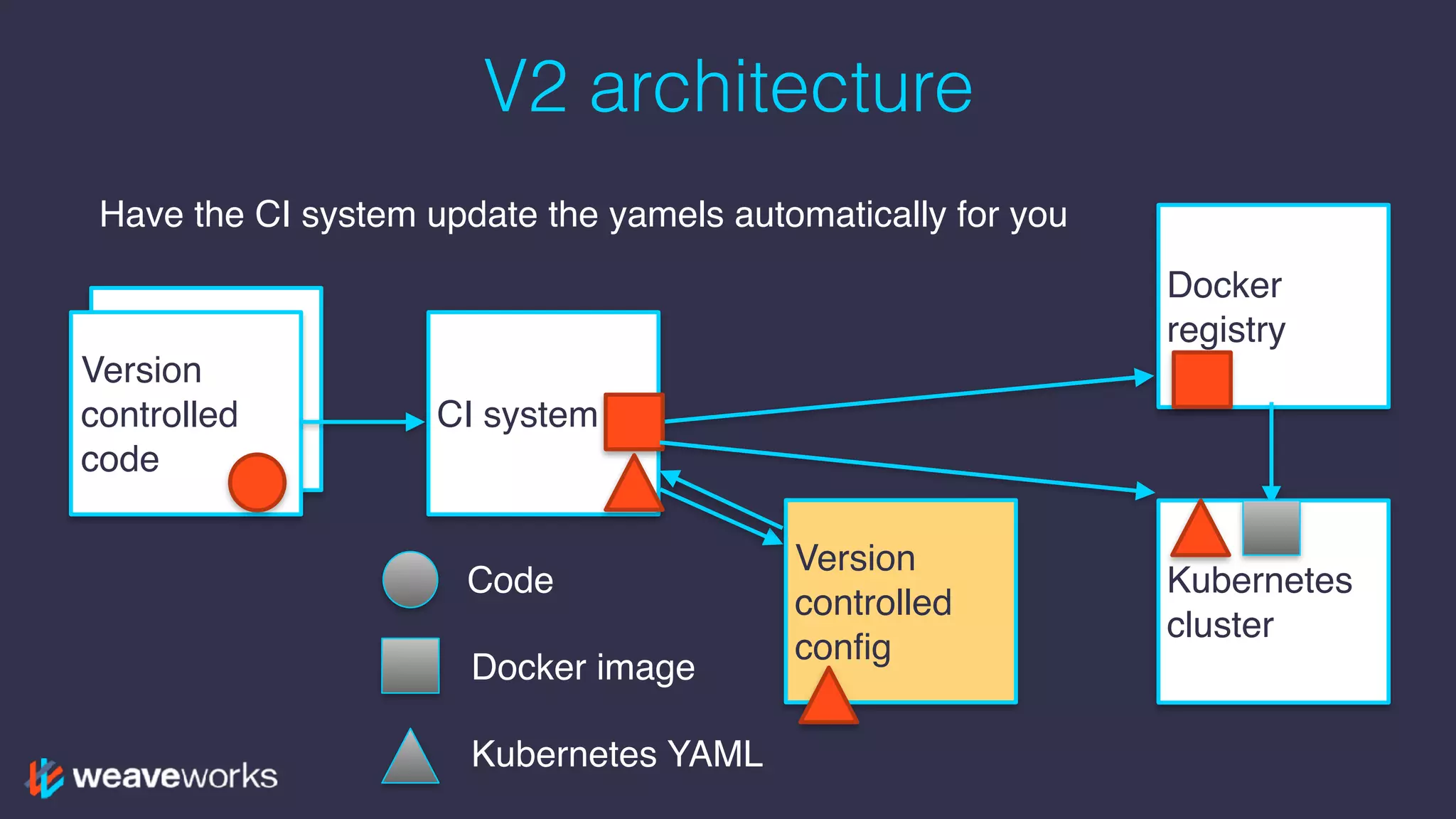
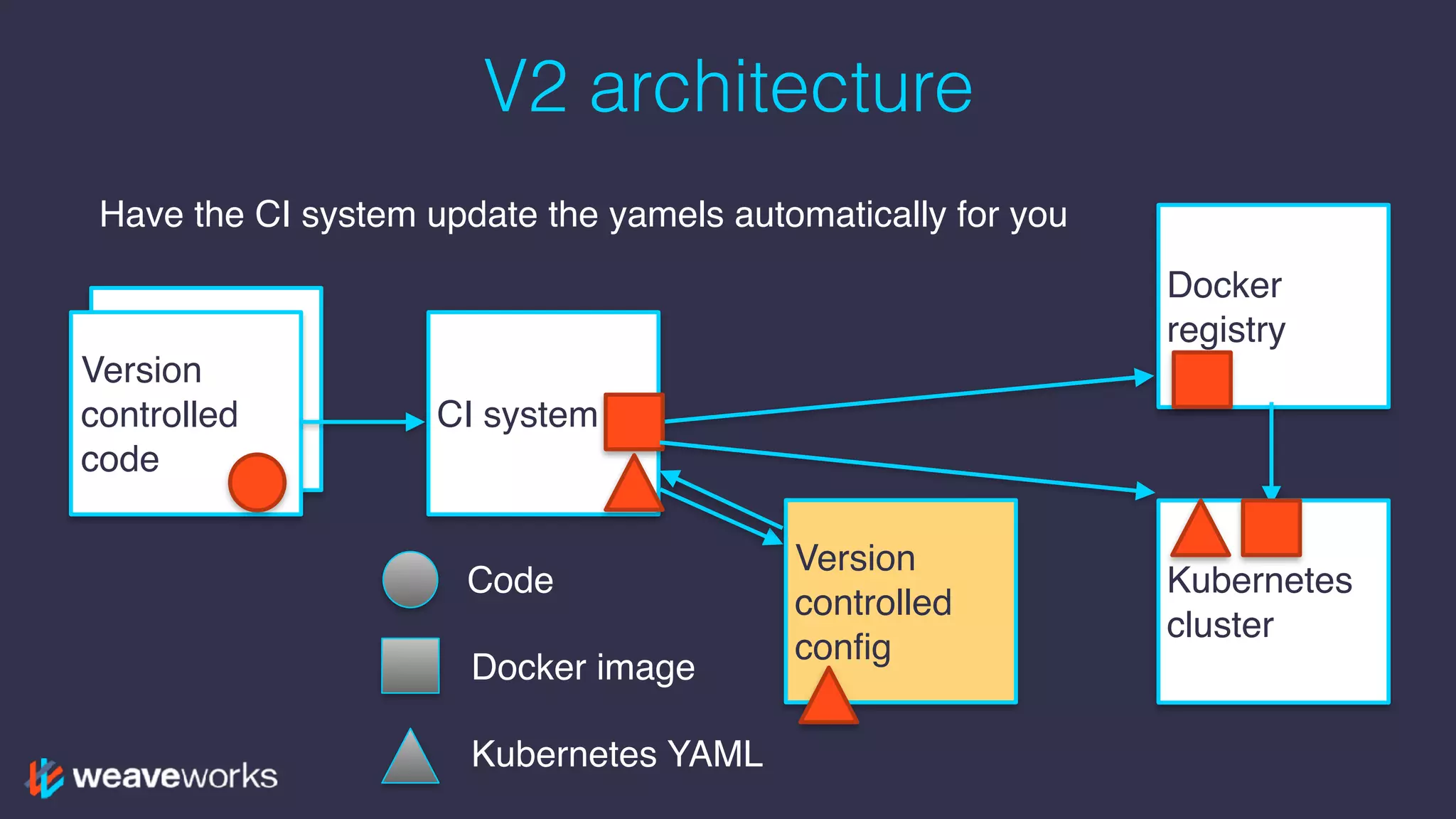
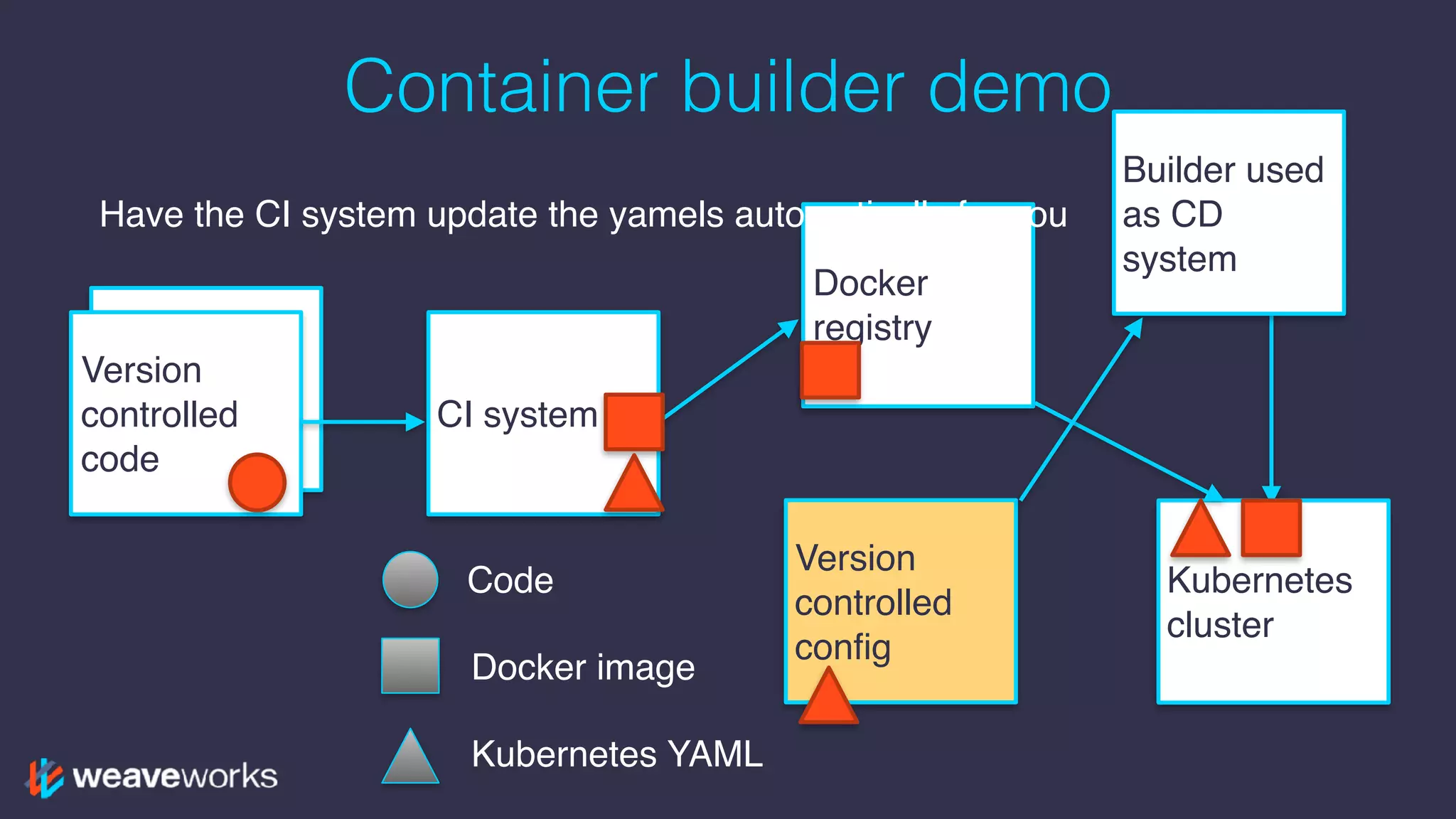
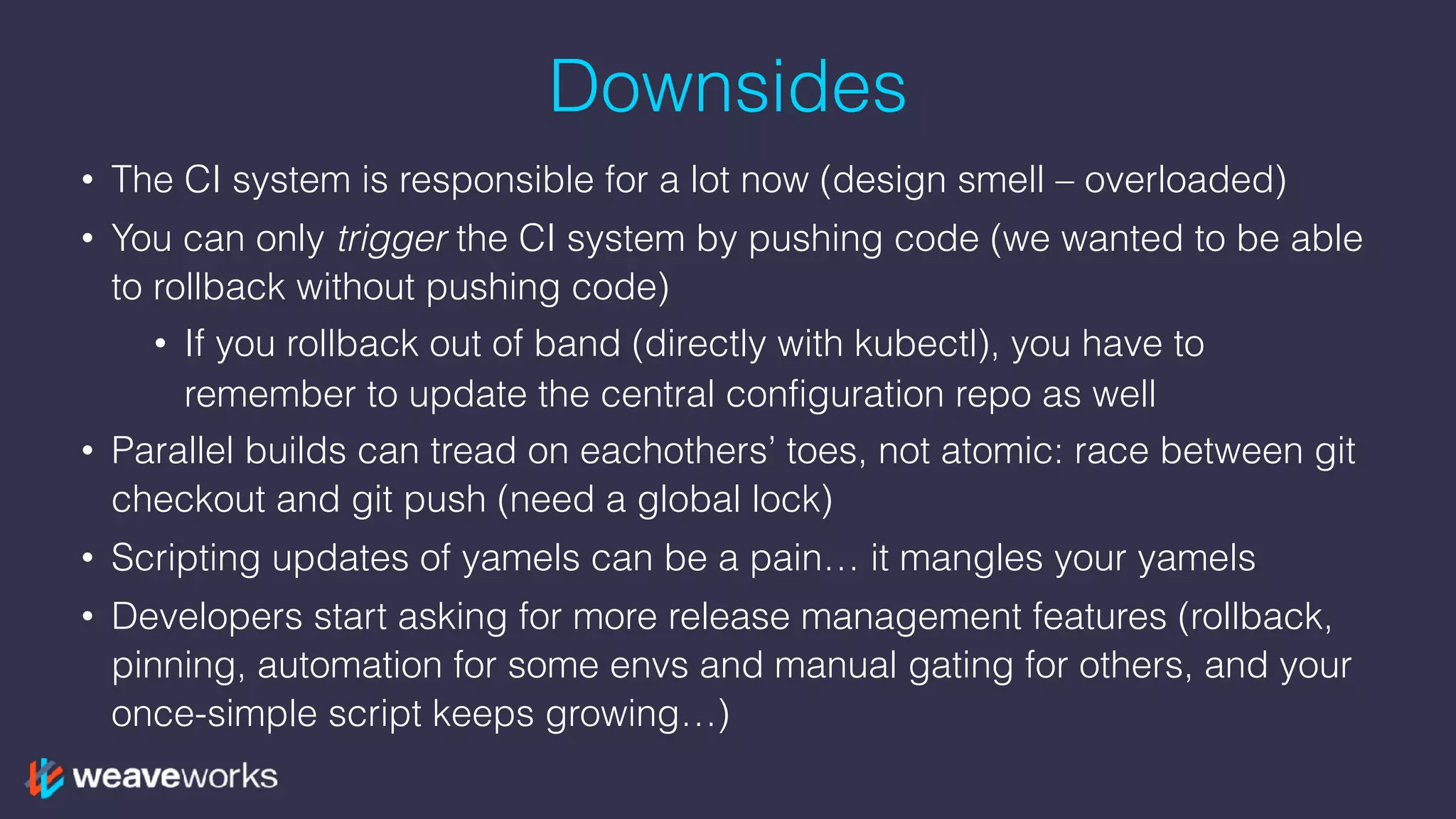
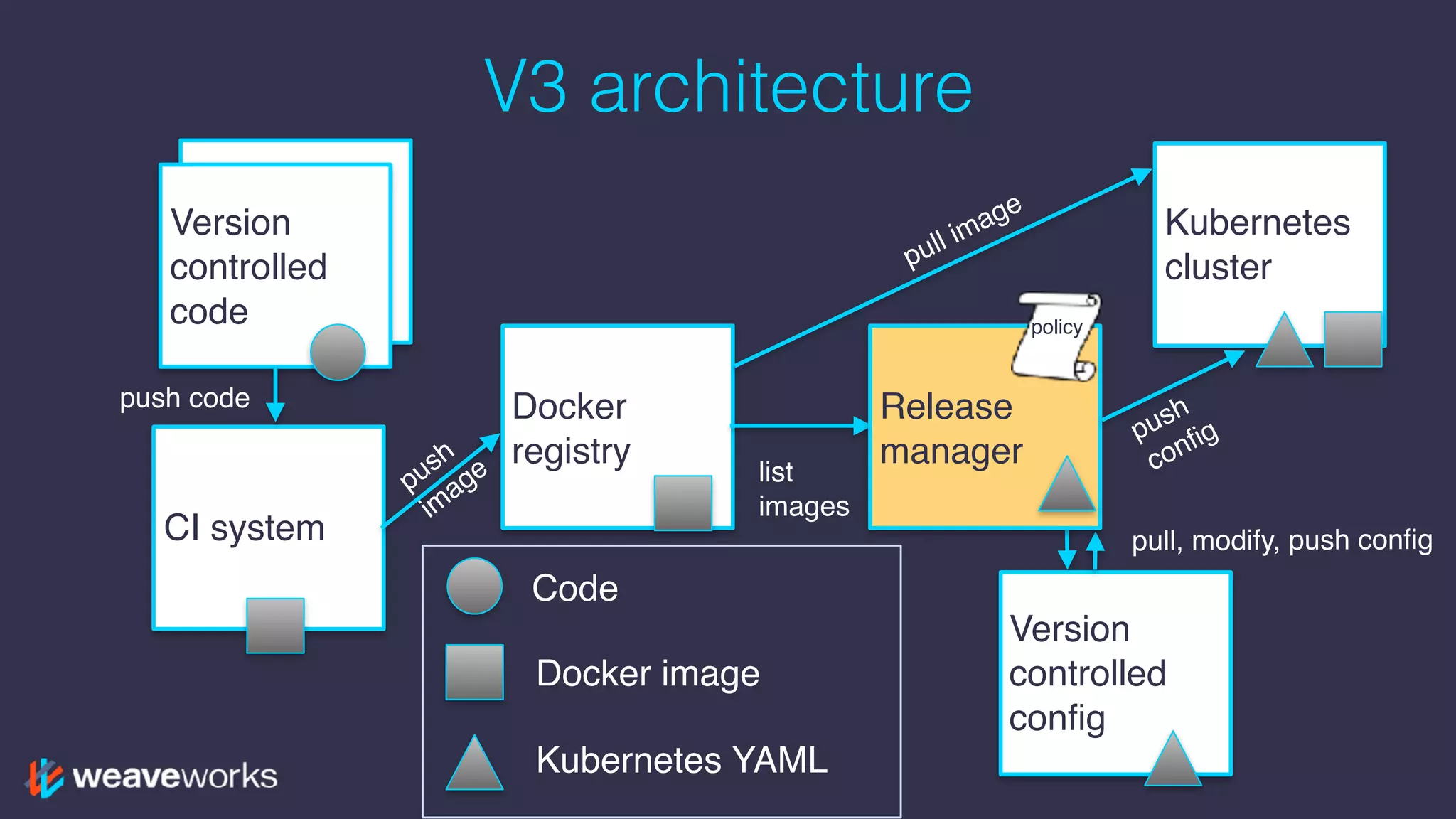
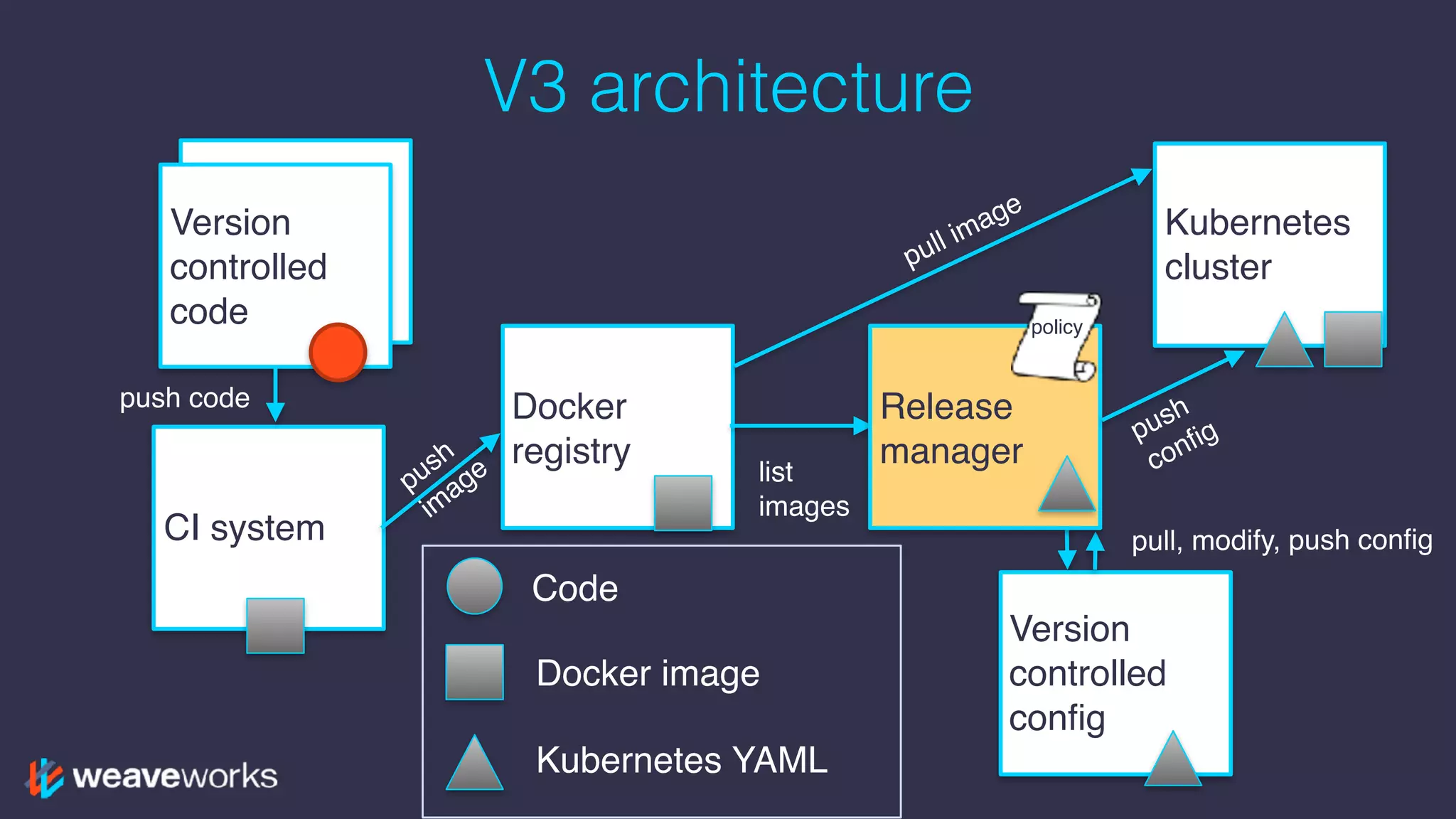
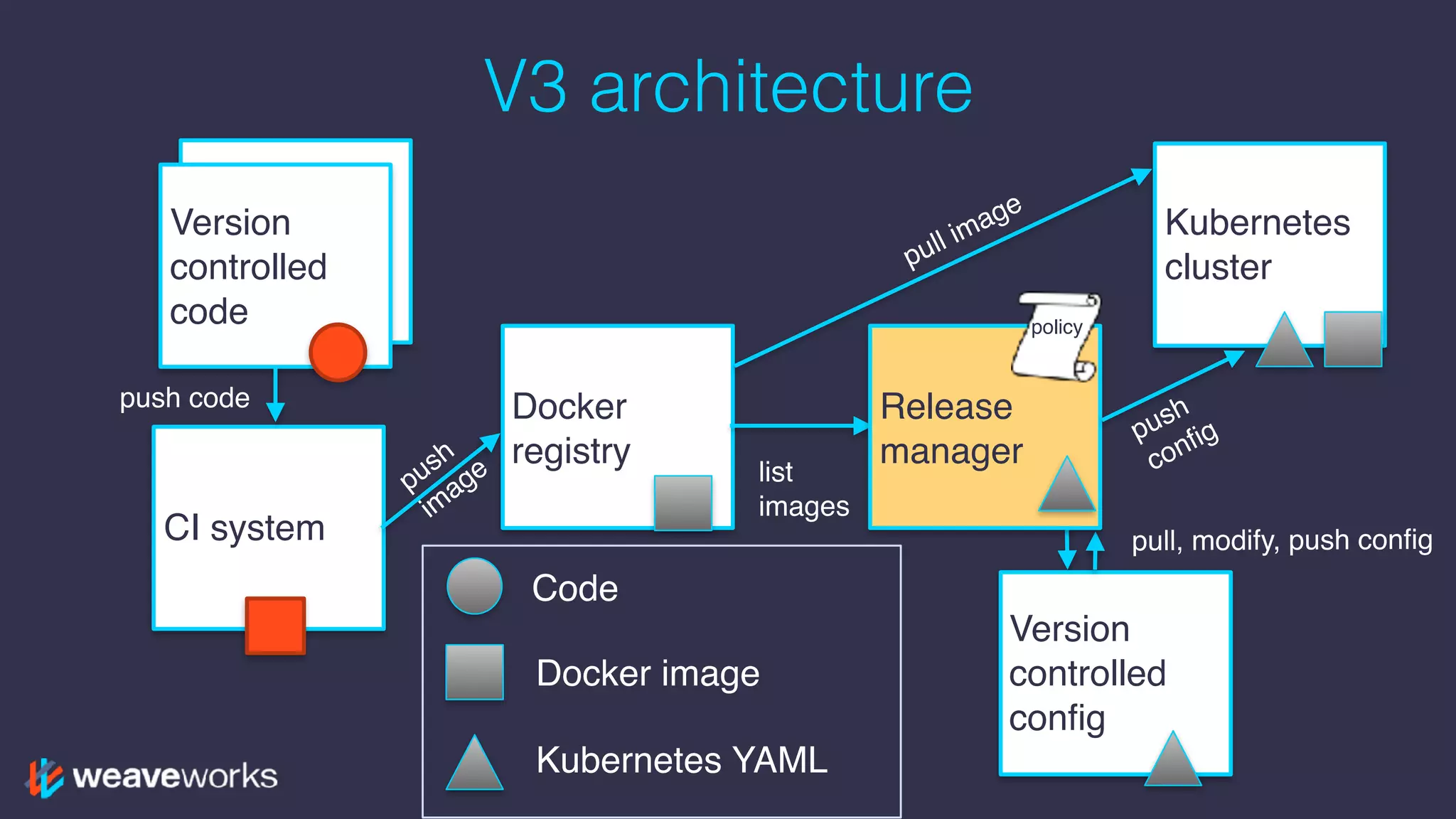
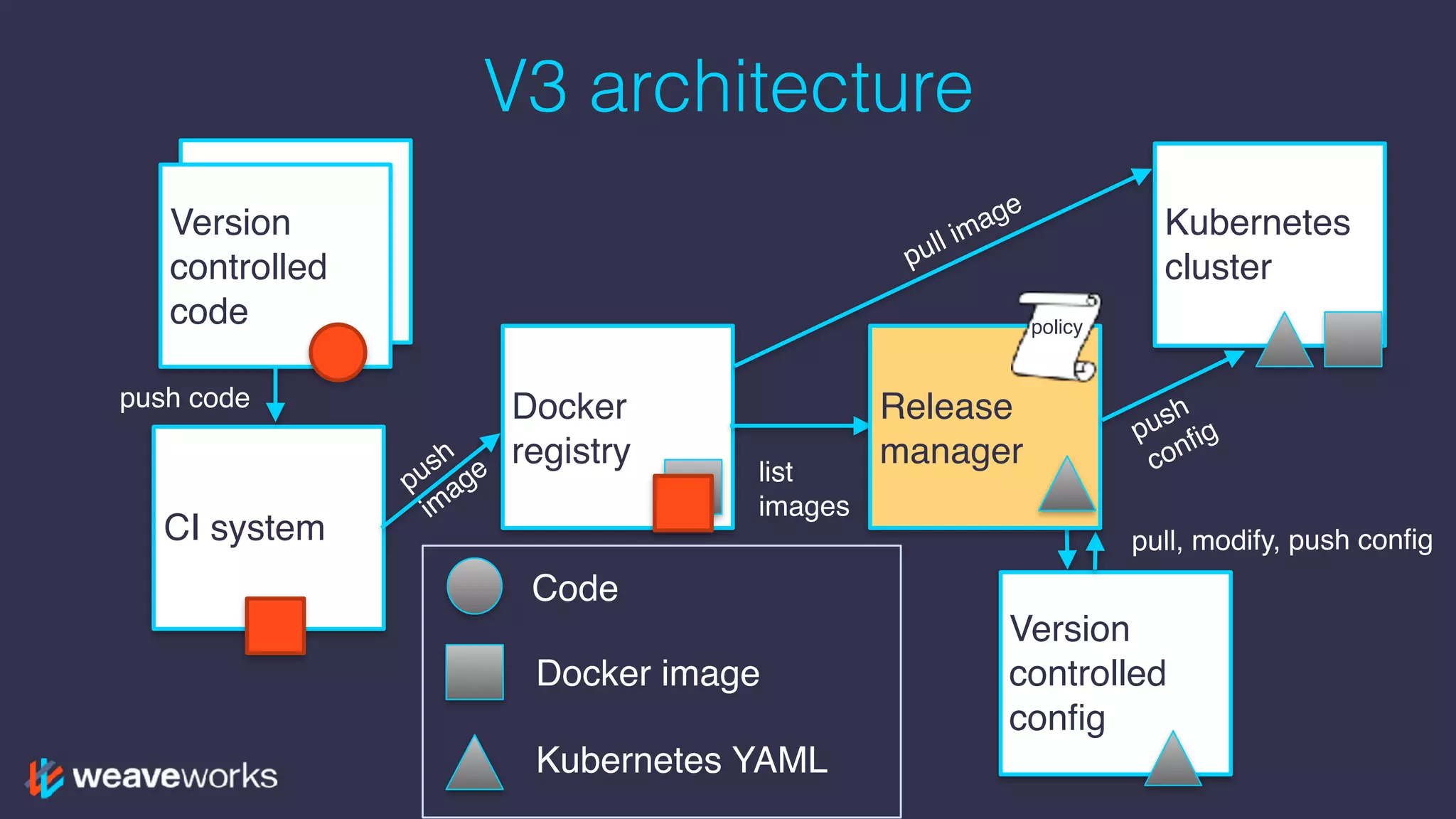
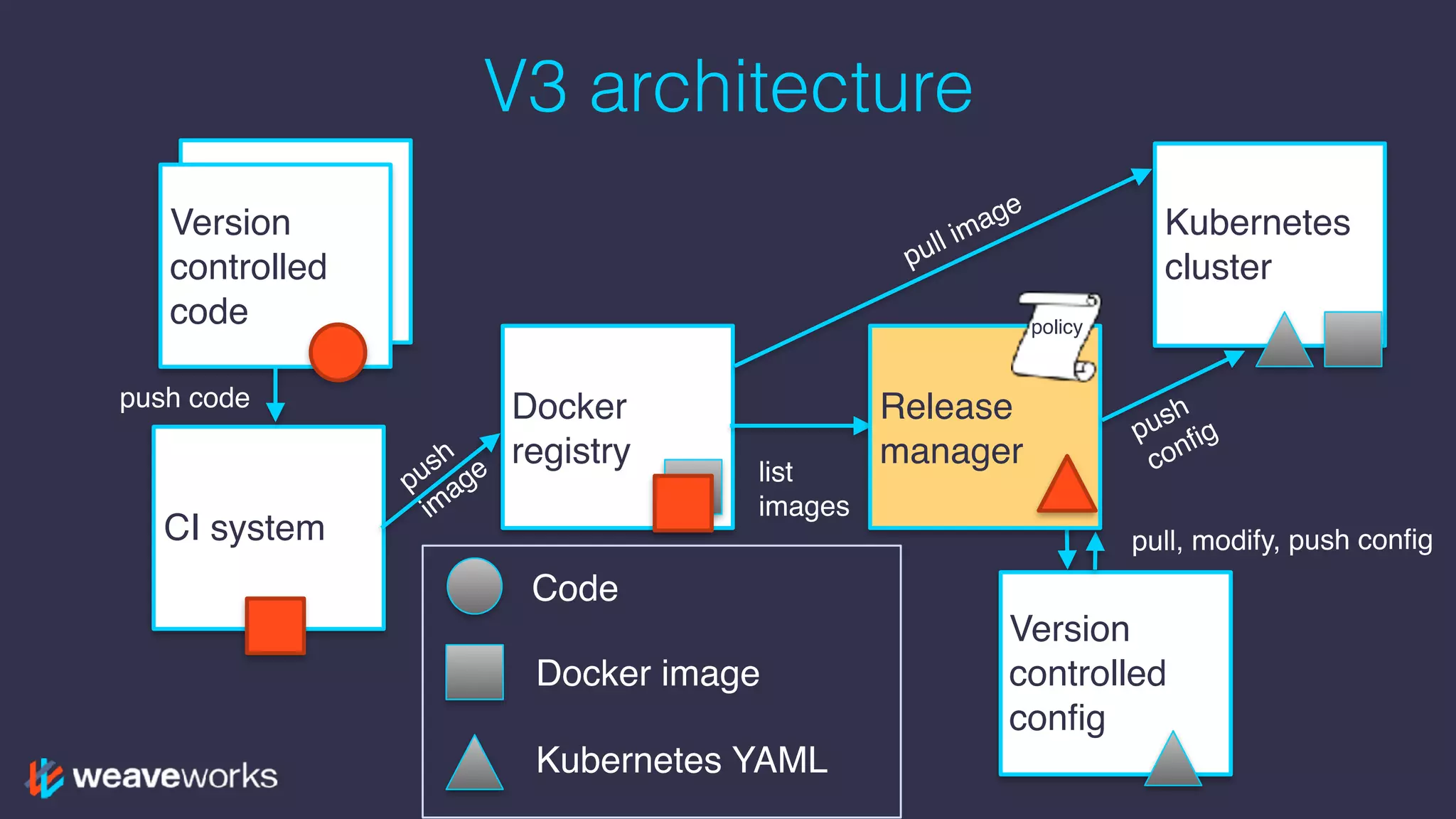
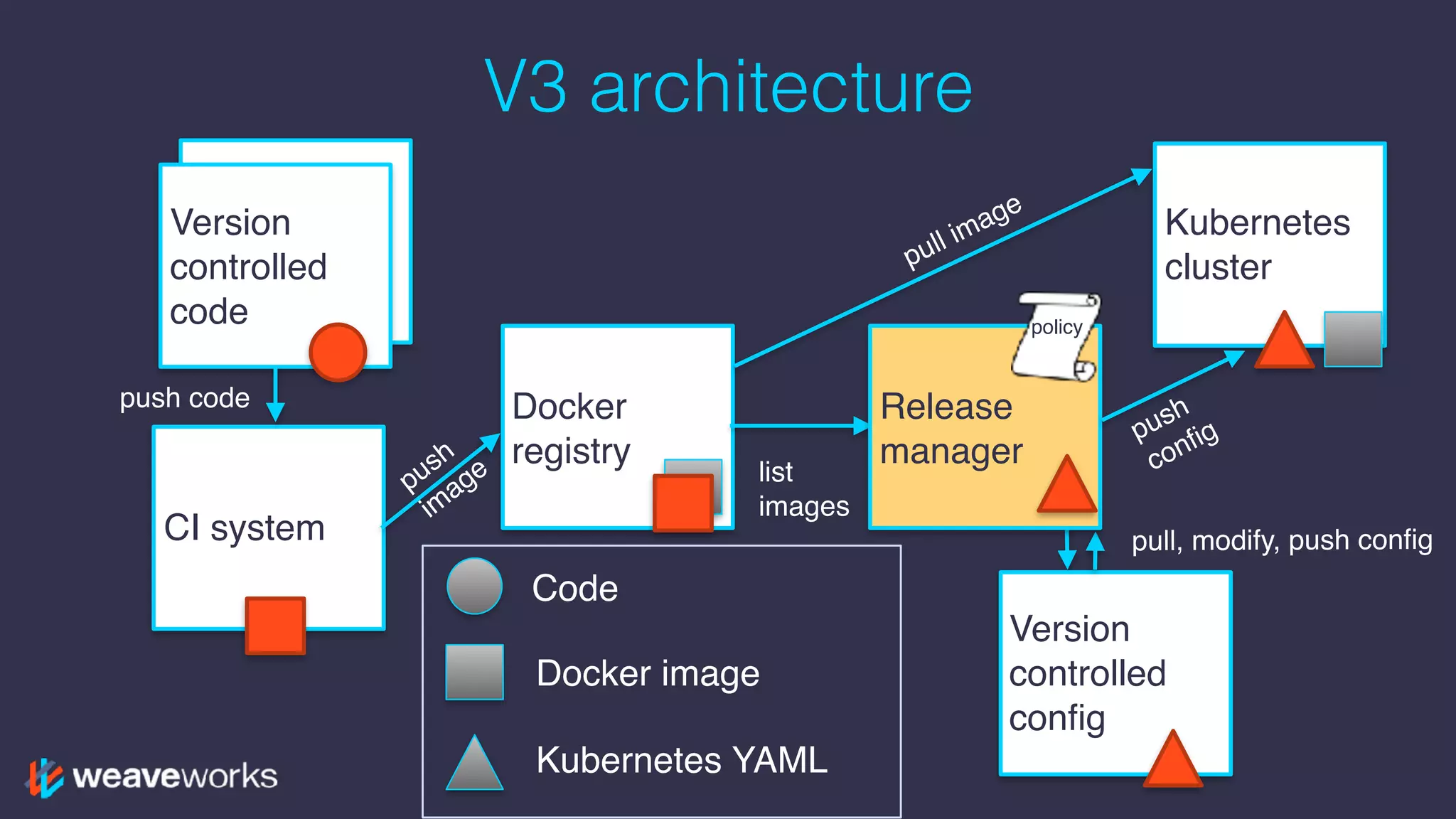
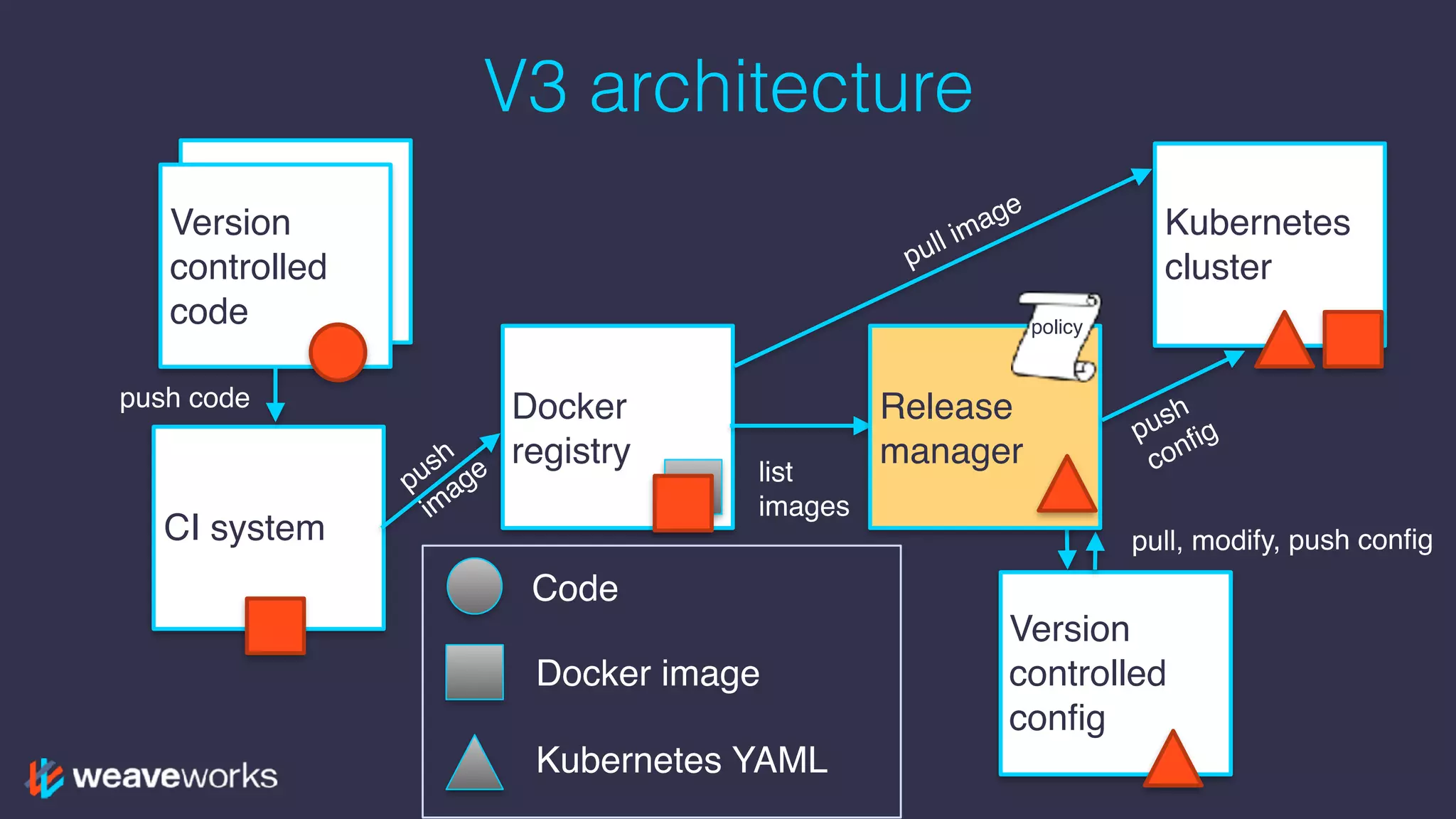
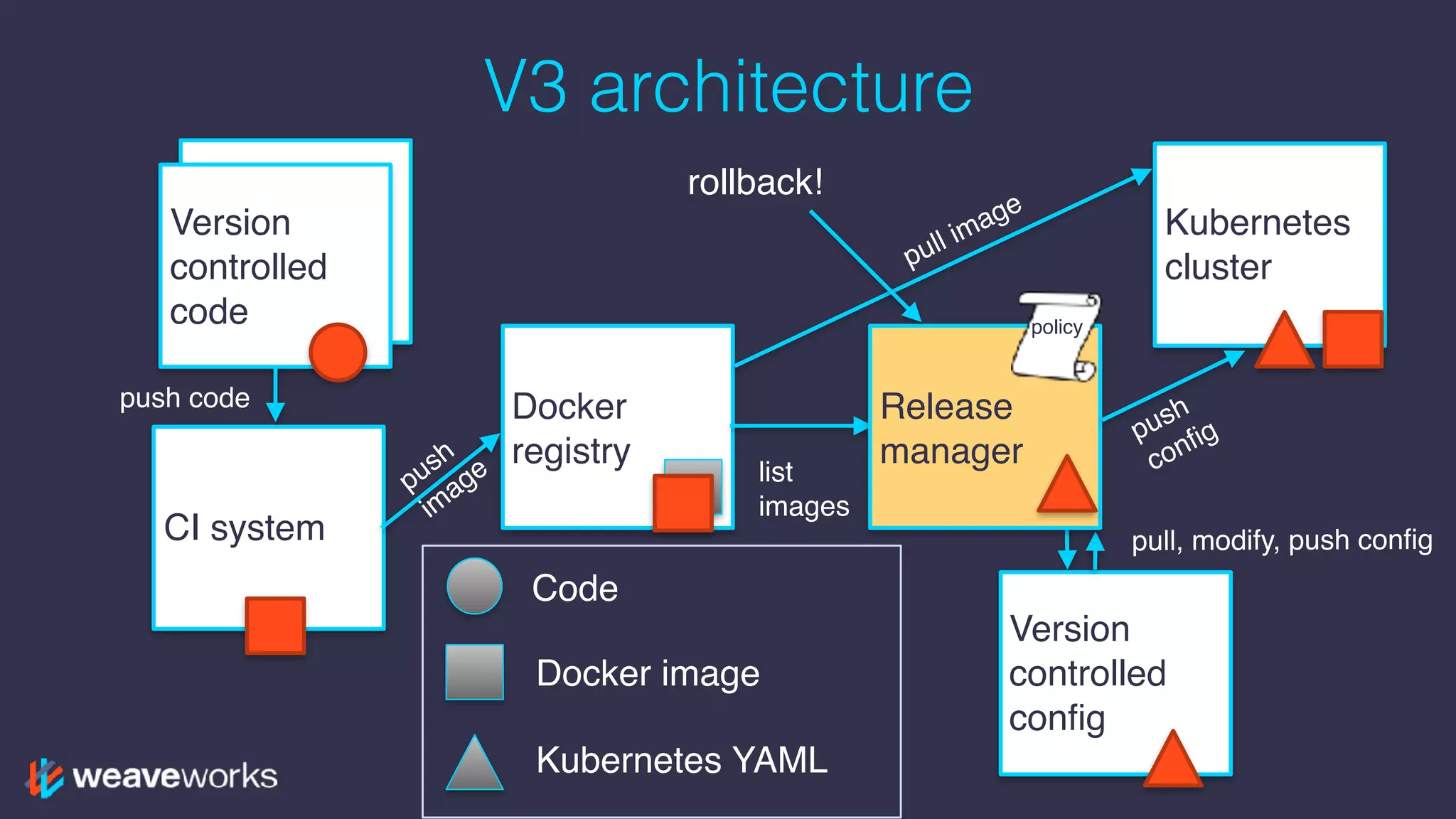
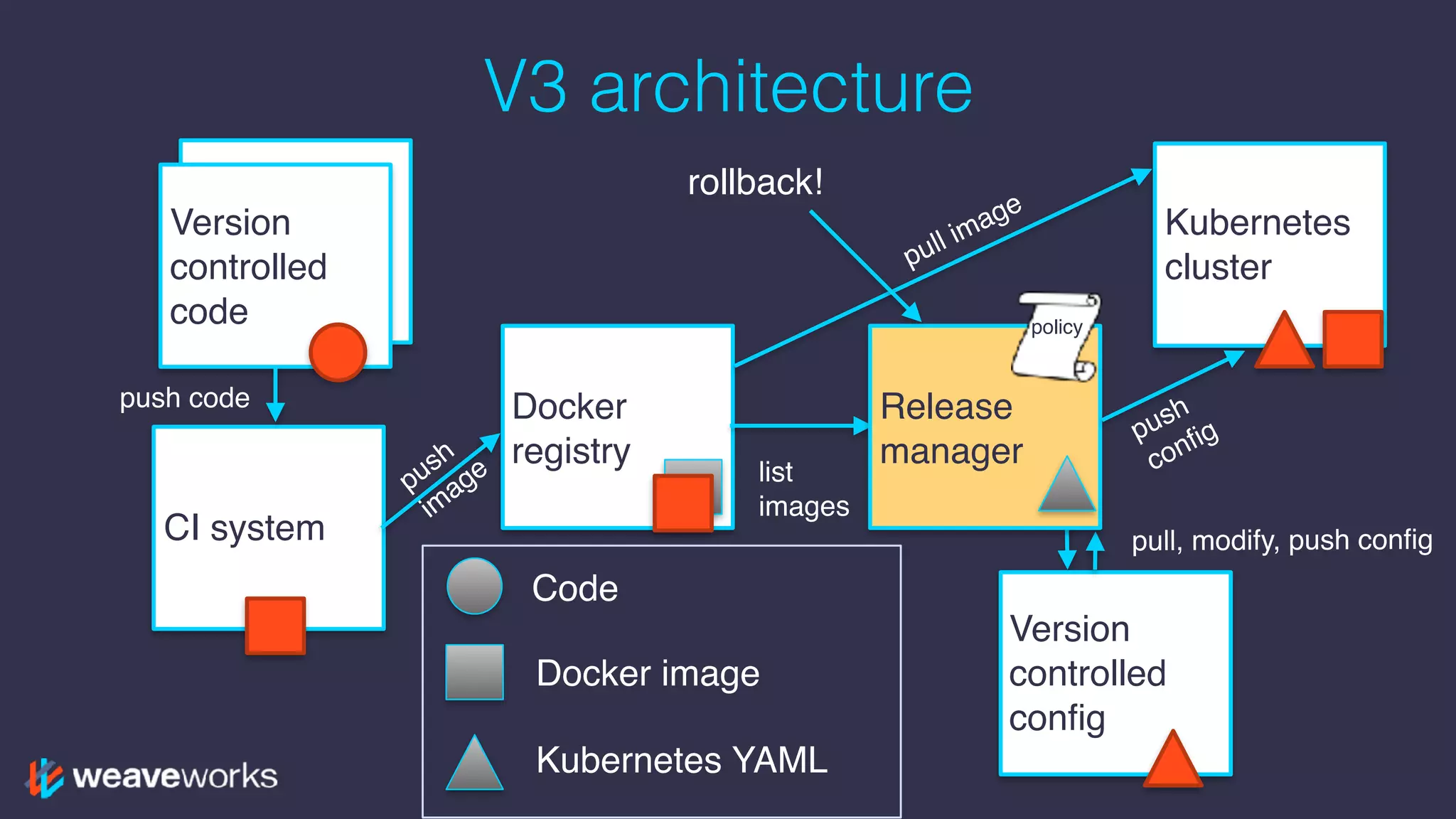
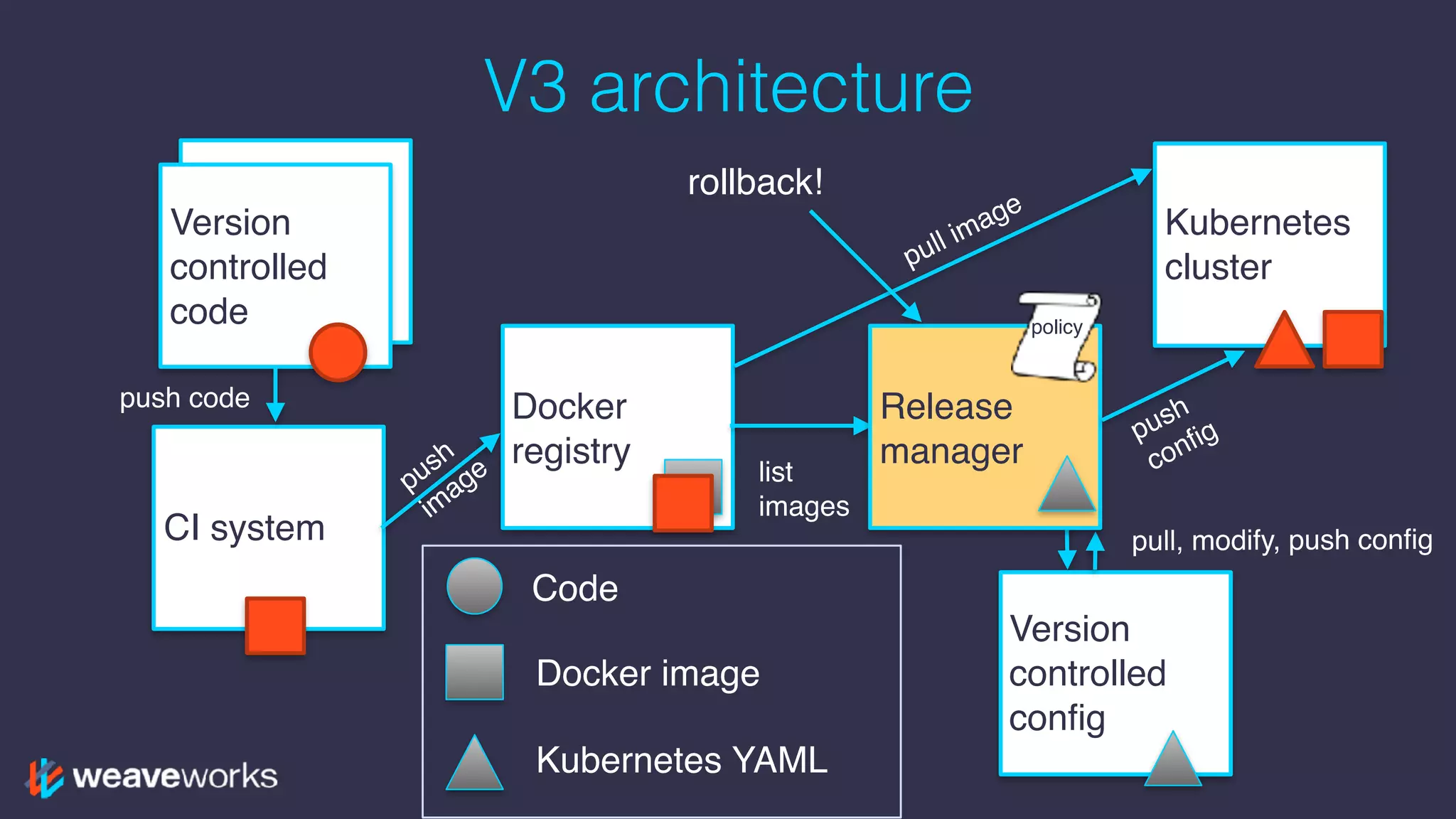
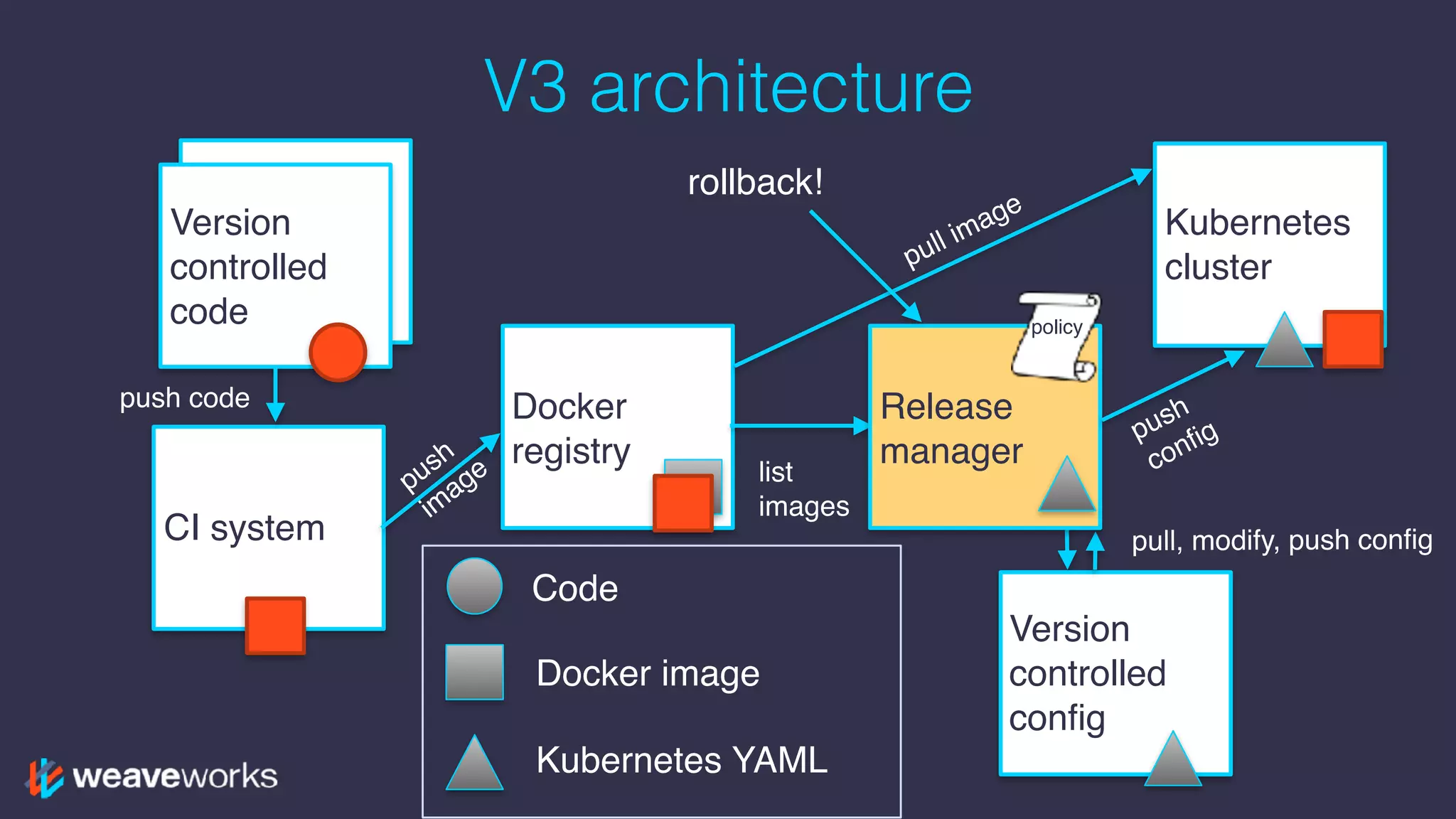
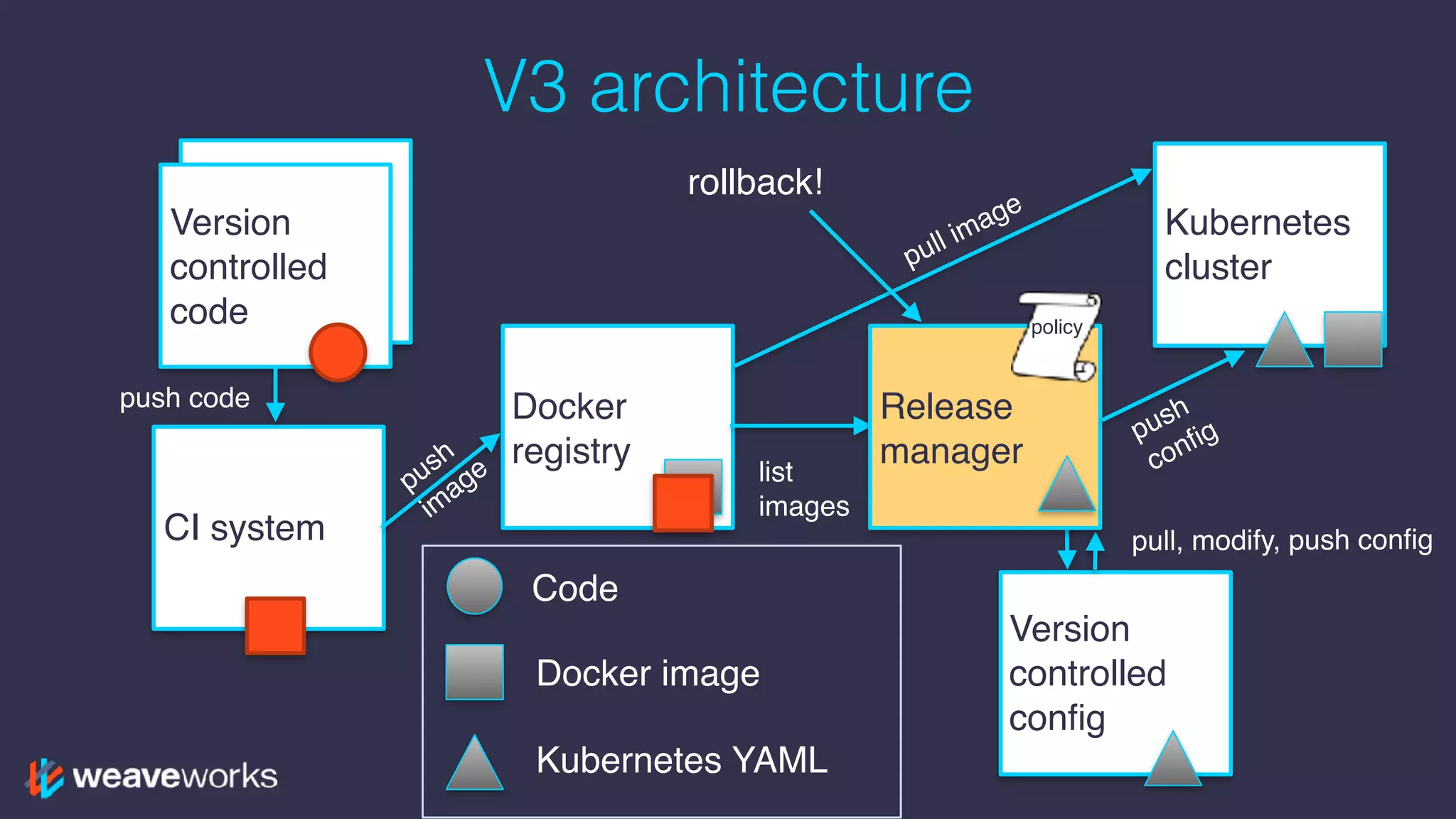
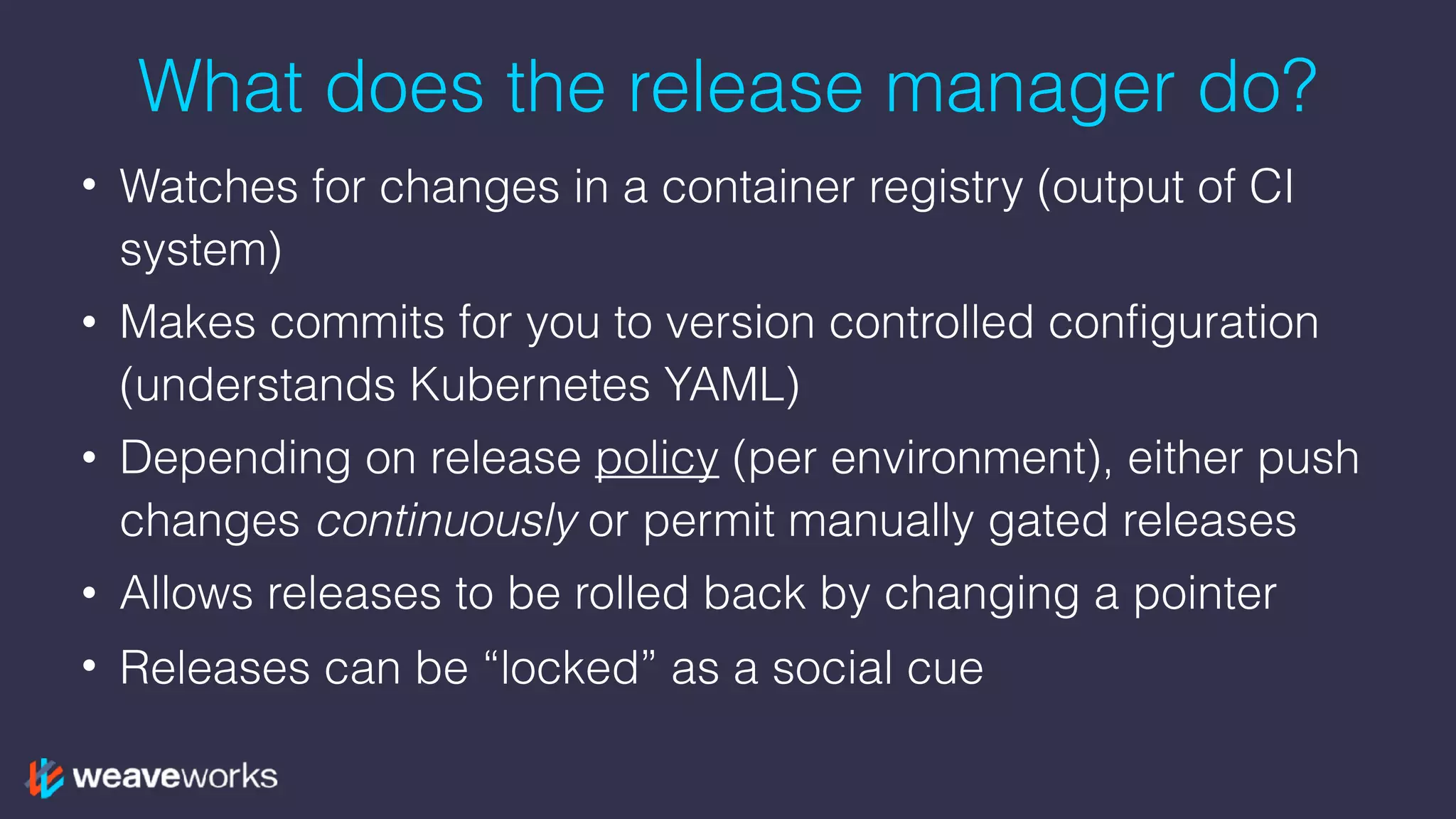
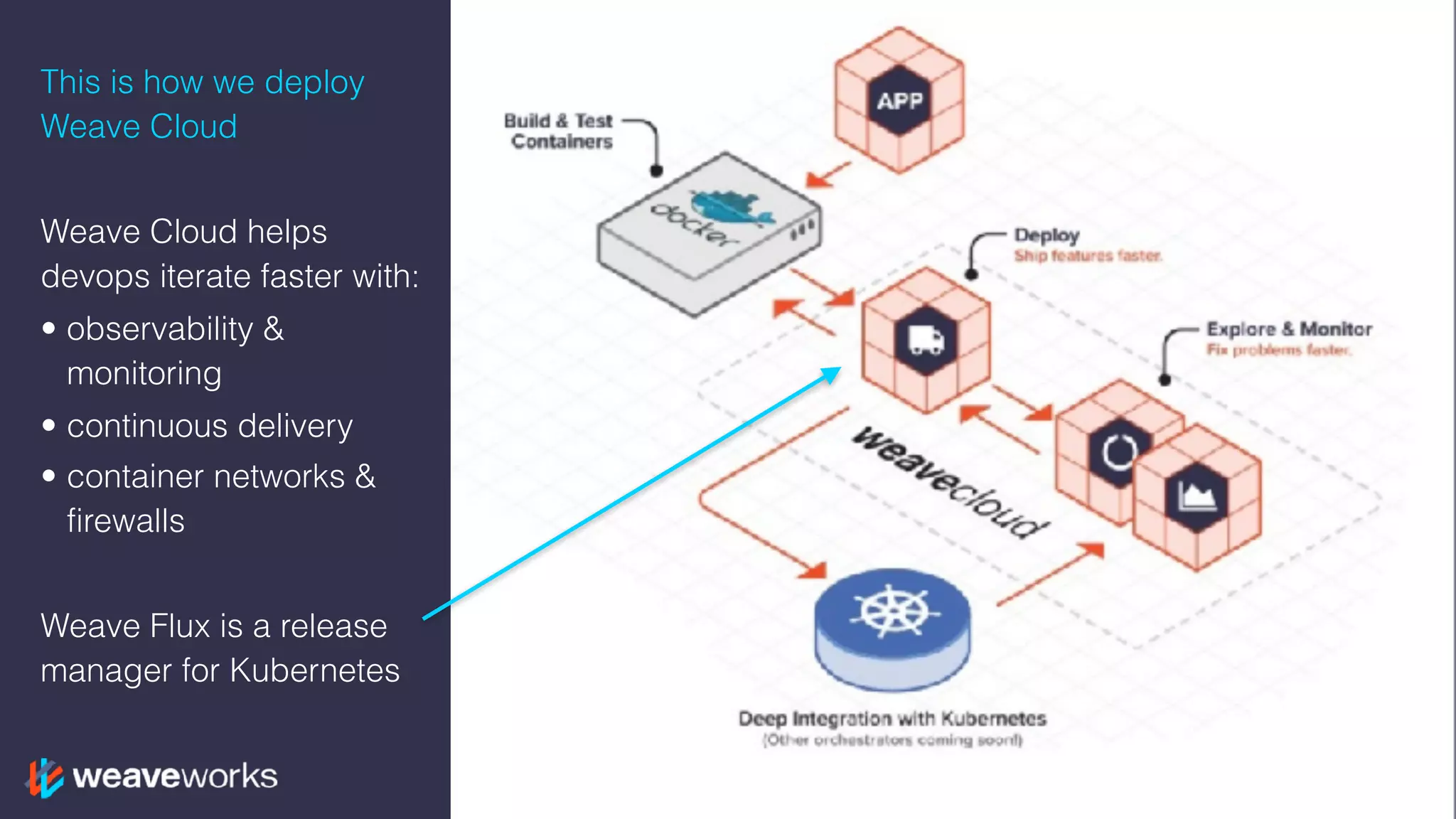
The document discusses continuous delivery using Kubernetes and GitLab, outlining the benefits, including improved team velocity and microservices scalability. It covers the fundamentals of Kubernetes components such as pods, services, and deployments, while also detailing a version-controlled configuration approach for managing deployments. Finally, it highlights the transition to a release manager architecture to enhance deployment processes and rollback capabilities.