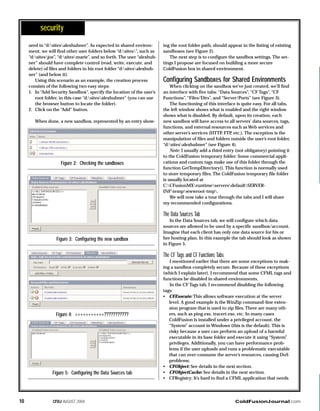
1) The document provides tips for securing a shared ColdFusion hosting environment, including enabling sandbox security and configuring individual sandboxes for each user.
2) It recommends disabling certain tags and functions like CFExecute, CFOBJECT, and CreateObject that could allow users to access system resources or other users' data.
3) The document explains that while sandboxes isolate users, shared hosting can never be 100% secure due to the possibility of users interfering with each other through things like denial of service attacks.